which of the following statements about information security risks is most correct regarding he use of collaborative workspace tools and platforms?
which of the following statements about information security risks is most correct regarding he use of collaborative workspace tools and platforms?
Principles of Information Systems (MindTap Course List)
13th Edition
ISBN:9781305971776
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter14: Ethical, Legal, And Social Issues Of Information Systems
Section: Chapter Questions
Problem 2CE
Related questions
Question
which of the following statements about
Transcribed Image Text:A
O
B O
с O
D O
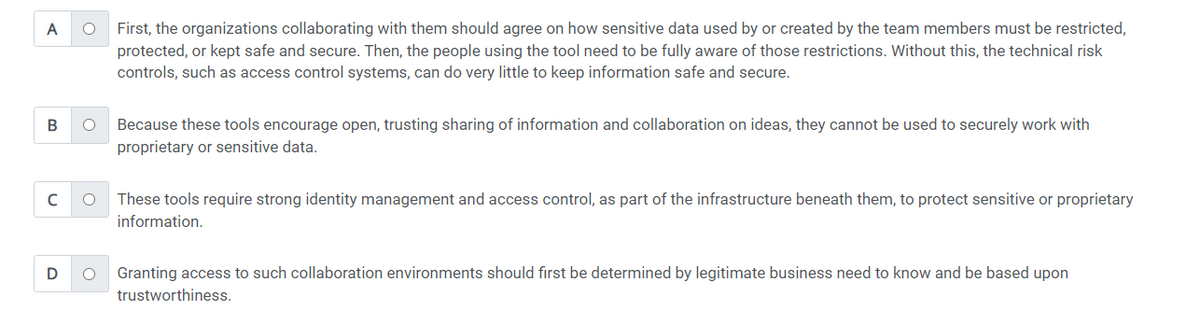
First, the organizations collaborating with them should agree on how sensitive data used by or created by the team members must be restricted,
protected, or kept safe and secure. Then, the people using the tool need to be fully aware of those restrictions. Without this, the technical risk
controls, such as access control systems, can do very little to keep information safe and secure.
Because these tools encourage open, trusting sharing of information and collaboration on ideas, they cannot be used to securely work with
proprietary or sensitive data.
These tools require strong identity management and access control, as part of the infrastructure beneath them, to protect sensitive or proprietary
information.
Granting access to such collaboration environments should first be determined by legitimate business need to know and be based upon
trustworthiness.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning