Which of the following statements about OpenCL is FALSE? Select one: a. OpenCL lets programmers run kernels on CPU and GPU devices b. OpenCL programs are portable and can run on heterogeneous computer systems c. Device and platform information can be obtained at runtime d. Data parallelism is not supported by OpenCL e. OpenCL is used to write parallel programs
Which of the following statements about OpenCL is FALSE? Select one: a. OpenCL lets programmers run kernels on CPU and GPU devices b. OpenCL programs are portable and can run on heterogeneous computer systems c. Device and platform information can be obtained at runtime d. Data parallelism is not supported by OpenCL e. OpenCL is used to write parallel programs
Chapter1: Introduction To Linux
Section: Chapter Questions
Problem 5RQ: Which of the following kernels are developmental kernels? (Choose all that apply.) a. 2.3.4 b. 3.5.5...
Related questions
Question
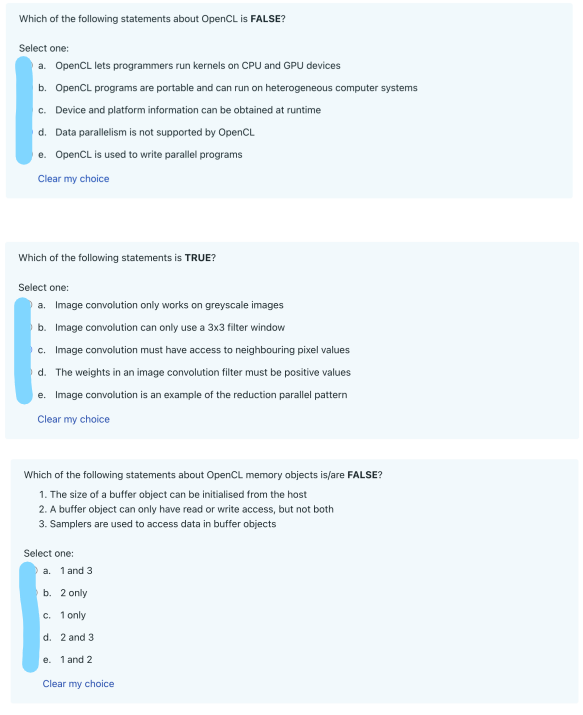
Transcribed Image Text:Which of the following statements about OpenCL is FALSE?
Select one:
a. OpenCL lets programmers run kernels on CPU and GPU devices
b. OpenCL programs are portable and can run on heterogeneous computer systems
c. Device and platform information can be obtained at runtime
d. Data parallelism is not supported by OpenCL
e. OpenCL is used to write parallel programs
Clear my choice
Which of the following statements is TRUE?
Select one:
a. Image convolution only works on greyscale images
b. Image convolution can only use a 3x3 filter window
c. Image convolution must have access to neighbouring pixel values
d. The weights in an image convolution filter must be positive values
e. Image convolution is an example of the reduction parallel pattern
Clear my choice
Which of the following statements about OpenCL memory objects is/are FALSE?
1. The size of a buffer object can be initialised from the host
2. A buffer object can only have read or write access, but not both
3. Samplers are used to access data in buffer objects
Select one:
a. 1 and 3
b. 2 only
c. 1 only
d. 2 and 3
e. 1 and 2
Clear my choice
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

CompTIA Linux+ Guide to Linux Certification (Mind…
Computer Science
ISBN:
9781305107168
Author:
Jason Eckert
Publisher:
Cengage Learning

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

CompTIA Linux+ Guide to Linux Certification (Mind…
Computer Science
ISBN:
9781305107168
Author:
Jason Eckert
Publisher:
Cengage Learning