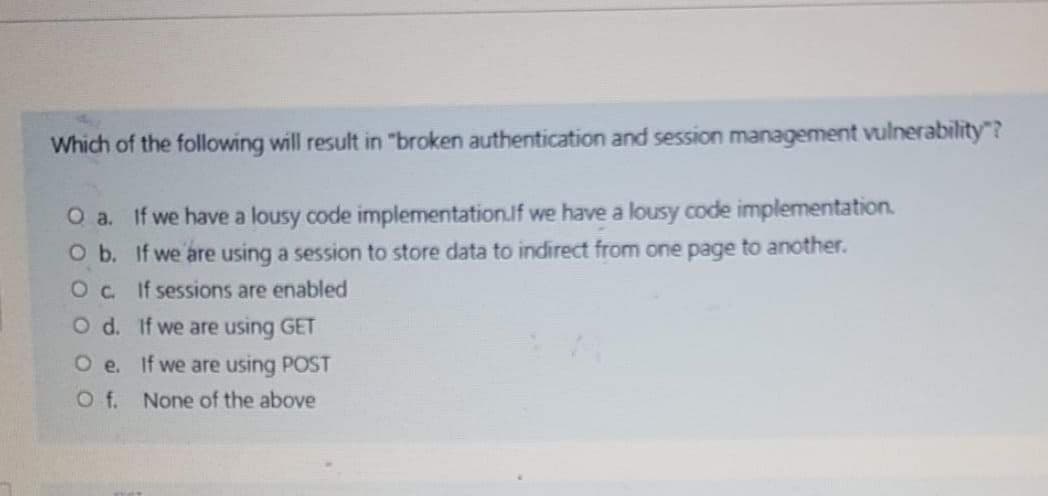
Which of the following will result in "broken authentication and session management vulnerability"? O a. If we have a lousy code implementation.if we have a lousy code implementation. O b. If we are using a session to store data to indirect from one page to another. Oc If sessions are enabled O d. If we are using GET O e. If we are using POST O f. None of the above
Q: send many requests to multiple servers with spoofed source, response can flood target and the…
A: DDoS attacks come from multiple locations, often spoofed. DDos is accomplished by flooding the…
Q: Under which condition is using the trial-and-error approach not advisable? (Choose all that apply.)…
A: Under which condition is using the trial-and-error approach not advisable? (Choose all that apply.)…
Q: The marks for the final exam have been shared with specific people on a web server. The files are…
A: GIVEN QUESTION IS The marks for the final exam have been shared with specific people on a web…
Q: Which of the following statements is incorrect concerning HTTP cookies? O a. HTTP cookies are stored…
A: Lets see the solution.
Q: Let the file size be 5 x 10° Bytes. Let the upload bandwidth at the sever be = 5 x 10 Bytes/second…
A: Let the file size be 5 x 109 Bytes. Let the upload bandwidth at the sever be = 5 x 106Bytes/second…
Q: cali duckburg mcduckcorp Figure 1: DNS name tree for Duckburg
A: The answer is
Q: A DoS attack that exhausts the capacity of a system or network is called ___________. Volumetric…
A: Networks is the one which refers to the set of the computer that are interconnected in order to…
Q: The netstat programme, available for Linux and Windows, provides a list of active network…
A: Given: "Netstat" is a command that displays information about the network. "Network statistics" is…
Q: Clients are reporting slowness when attempting to access a series of load-balanced APIs that do not…
A: To use OAuth 2.0 to protect an API so that an application can access it on behalf of a user The flow…
Q: Which of the following is correct about passive attack? a. Involve modification of the data stream O…
A: Passive Attacks are in the nature of eavesdropping on or monitoring of transmission.
Q: What is a reverse shell?
A: A reverse shell is a type of session cyber attackers commonly use to open communication ports…
Q: On servers with Linux operating system, access logs are kept under which of the following…
A: As per our policy, "Since you have asked multiple questions, we will solve the first question for…
Q: APPLICATION LAYER S: blah blah S: .. S: . ... . .blah ? c. Suppose you have configured your POP mail…
A: Post Office Protocol version 3 (POP3) is an mail protocol used to retrieve mail from a remote server…
Q: Write a small program/script to resolve all DNS hostnames of Southeastern's ranging from 0 to 255…
A: Given address : 147.174.$i.$j/16 16 bits, that is first and second octet are network ids. Last 16…
Q: Which of the following mechanisms offers slowest performance compared to others? O a. Digitally…
A: All the processes are of same service, so they have equal performances.
Q: What’s the difference between session.save() and session.saveOrUpdate() methods in hibernate
A: SUMMARY: - hence we discussed all the points.
Q: How to remove the item from the cart if the quantity is 0? I have included my code below that I am…
A: //here, it remove the product from card which has 0 quantity$product_id = $_SESSION['product_id'];
Q: When using a Stream Cipher, which of the following will most weaken your encryption? O Using a nonce…
A: When using a Stream Cipher ,which of the following will most weaken your encryption: 1.using a nonce…
Q: setAttribute(PDO::ATTR_ERRMODE, PDO::ERRMODE_EXCEPTION);} ?> Assume a user has logged in…
A: Shopping cart is an online shopping site where the customer buy an item and add them into cart to…
Q: When the session will be timed out? HTTP response: host: localhost:8084 user-agent: Mozilla/5.0…
A: It is defined as the response sent by a server to the client. The response is used to provide the…
Q: Linux - Ubuntu Create a file named .db in /etc/bind/, this file will contain all the resource…
A: If your domain uses nameservers, one can add a subdomain record to the DNS zone file. Subdomains…
Q: A new application will be deployed on EC2 instances in private subnets. The application will…
A: A new application will be deployed on EC2 instances in private subnets. The application will…
Q: 2. Group each four integers and create an InetAddress object using them (in the same order they…
A: The ask is to write a Java program to do the following: - Read the input file "ipnumbers.out" -…
Q: Which of the following methods was used to share these files?
A: The answer for the above question is: d. The files were hashed using SHA-1 hashing algorithm
Q: Which of the following actions should you first take to secure your Linux computeragainst network…
A: First Action to Secure Linux Computer: To overcome the network attack, only the necessary network…
Q: $script = $_GET["script"]; eval("/$script;");
A: Given: $script = $_GET["script"];eval("/$script;"); We need to chose the answer: Which of the…
Q: ALICE Yes Message (m) Hash MD Function Alice public-key Alice private-key Hash Same? Function…
A: Explain Two weaknesses of Digital Signature Scheme that can be solved using the MAC scheme. Answer:…
Q: What’s the use of session.lock() in hibernate?
A: Introduction : If the attacker has obtained the session ID, the client's identity must be verified.…
Q: Which statement is true about Staged Payload? O Instructs the target machine to open a shell command…
A: It is a payload of type staged type windows/shell/reverse_tcp. In the whole process string sent to…
Q: Which one of the following statements is NOT correct about HTTP cookies? a. A cookies is a piece of…
A: a) A cookie is a piece of code that has the potential to compromise the security of an internet…
Q: using Linux/Unix, please Suppose that you want to block everyone (except you) at the main door…
A: Actually, given information: Suppose that you want to block everyone (except you) at the main door…
Q: Assume that you are trying to control the access to a file on your web server. Which of the…
A: The file should be encrypted using the AES encryption algorithm, since this algorithm works fine…
Q: Which of the following is not a function of the session layer in the OSI model? O a. Establish,…
A: Communication between the processes is not a function of the session layer.
Q: Consider the following simple authentication dialogue: C → AS: IDc II Pc II IDv AS → C: Ticket C…
A: ANSWER : Simple Authentication Dialogue : A Simple Authentication Dialoguethe user logs on…
Q: Provide one real-world example where a session would be more appropriate to use (do not provide…
A: The session is defined as the form of the information that happens to be interactive between the…
Q: Which of the following events demonstrates an example of cross-site request forgery vulnerability? O…
A: Vulnerabilities refer to the weak points that provide chances to attackers to enter into the…
Q: Write a complete bash script that monitors who logs in and logs out of the current CSELinux machine…
A: print out the current date and time and report the number of users loggedin,even if there are no…
Q: Write a complete bash script that monitors who logs in and logs out of the current CSELinux machine…
A: the solution is given below :
Q: Write a complete bash script that monitors who logs in and logs out of the current CSELinux machine…
A: complete bash script that monitors who logs in and logs out of the current CSELinux machine (e.g.,…
Q: You have successfully configured Windows Server 2019 as a VPN server using SSTP tunnel type. You…
A: The VPN profile is has "UseWinlogonCredential" parameter enabled. Explanation: Correct answer The…
Q: If we want to run Snort in Network Intrusion Detection System (NIDS) mode so that we don't record…
A: Solution: Given,
Q: Which of the following will work when trying to hack a login screen? O Try a list of commonly used…
A: Hacking: It is the process of attacking the computer and software to steal the information of the…
Q: In practice, we do not usually sign a document by 'encrypting' (I'm using the word loosely, here)…
A: Explanation: Message digest is also one of the types of encryption technique. It uses a fixed size…
Q: hijack a session, an attacker is observing and monitoring the session’s traffic of the victim which…
A: Here have to determine which is from option is vest for , hijack a session, an attacker is observing…
Q: #find all IP addresses for invalid logins, then see which IPs are also used for scanning def…
A: # importing the module import re # opening and reading the file with…
Step by step
Solved in 2 steps

- MCQ: To hijack a session, an attacker is observing and monitoring the session’s traffic of the victim which is known as ________________. a. Command injection b. Passive attack c. Active attack d. Brute forcingWhich one of the following statements is NOT correct about HTTP cookies? a. A cookies is a piece of code that has the potential to compromise the security of an Internet user b. A cookie gains entry to the user’s work area through an HTTP header c. A cookie has an expiry date and time d. Cookies can be used to track the browsing pattern of a user at a particular siteA new application will be deployed on EC2 instances in private subnets. The application will copy/write some sensitive data from/to an S3 bucket. Company compliance policy requires that the data must not traverse the public internet. Which solution meets the compliance requirement? A.Access the S3 bucket through an VPC end point for S3 B.Access the S3 bucket through a proxy server C.Access the S3 bucket through a NAT Gateway D.Access the S3 bucket through the SSL protected S3 internet endpoint
- Once the attacker gained access to the victim's machine, what executable did they first use to run commands on the host? Cite evidence from 'splunk-exec.csv'. [Example]: The attacker used 'zsh', which is a type of shell. We see this command executing at 05:26:93 PM from the host logs. Answer:What’s the difference between session.save() and session.saveOrUpdate() methods in hibernate?In snort, what does the "-W" switch do? Group of answer choices "Watches" the network, .ie. goes into sniffer mode Dumps all system interfaces by Index Number Dumps all packets into a log file Dumps all rules to the console
- Some students are starting a newspaper called 352times, they have the following security goals: Anyone should be able to read the paper with minimal effort, without doing anything more than sending a request to the newspaper’s server and reading the request in plaintext, ignoring any part of it that is not plaintext Those who care should be able to put in a bit more effort to verify that the newspaper was written by the true authors, without any additional communication with the newspaper Any unauthorized changes in the newspaper should be detected by the group of people who care Write a protocol for the newspaper to publish its news. Write the protocol that the people who want to verify the authorship and detect any unauthorized changes would use.Write a complete bash script that monitors who logs in and logs out of the current CSELinux machine (e.g., cse01, cse02, etc.) where the script is running. In particular, youwill check the status of who is logged in every 10 seconds and report each user ID thatlogs in or logs out during that time frame. Note that there may be more than one userthat logs in or out duringthis interval. You must include the host name when reportingthe user ID information. In addition, you will install a custom signal handler to trap theSIGINT(i.e.,^C)onetimebeforeyouareabletoterminatethescriptwiththeSIGINT.You will also print out the current date and time and report the number of users loggedin,even if there are no changes (i.e.,no one logged in or out during the interval). HOW TO DO THIS? PLEASE EXPLAIN WITH ANSWER!!Write a complete bash script that monitors who logs in and logs out of the current CSELinux machine (e.g., cse01, cse02, etc.) where the script is running. In particular, youwill check the status of who is logged in every 10 seconds and report each user ID thatlogs in or logs out during that time frame. Note that there may be more than one userthat logs in or out duringthis interval. You must include the host name when reportingthe user ID information. In addition, you will install a custom signal handler to trap the SIGINT(i.e.,^C) one time before you are able to terminate the script with the SIGINT. You will also print out the current date and time and report the number of users loggedin,even if there are no changes (i.e.,no one logged in or out during the interval). HOW TO DO THIS? PLEASE EXPLAIN WITH ANSWER!!
- Write a complete bash script that monitors who logs in and logs out of the current CSELinux machine (e.g., cse01, cse02, etc.) where the script is running. In particular, youwill check the status of who is logged in every 10 seconds and report each user ID thatlogs in or logs out during that time frame. Note that there may be more than one userthat logs in or out duringthis interval. You must include the host name when reportingthe user ID information. In addition, you will install a custom signal handler to trap the SIGINT(i.e.,^C) one time before you are able to terminate the script with the SIGINT. You will also print out the current date and time and report the number of users loggedin,even if there are no changes (i.e.,no one logged in or out during the interval). What should the script.h file have inside it? Please show screenshot of output if possible ,what is the answer?a. Which of the following can be used for both encryption and digital signatures? 3DES AES RSA MD5 b. Digital Signatures provide which of the following? Confidentiality Authorization Integrity Authentication Availability c. The difference between a hash and a digital signature is: Hashes are used to verify message authenticity, digital signatures are used to verify message integrity. Hashes are used to verify message integrity and authenticity, digital signatures are used to verify message authenticity only. Hashes are used to verify the message integrity only, digital signatures are used to verify message authenticity and message integrity. There is no functional difference. d.Which asymmetric algorithm is used for establishing a shared key?A.Elliptic CurveB. PGPC. Diffie-HellmanD. RSA e.What is used to create a message digest that will be attached to data at rest or in transit? Asymmetric algorithm Symmetric algorithm Encryption Hashing Non-repudiation Authentication…Clients are reporting slowness when attempting to access a series of load-balanced APIs that do not require authentication. The servers that host the APIs are showing heavy CPU utilization. No alerts are found on the WAFs sitting in front of the APIs. Which of the following should a security engineer recommend to BEST remedy the performance issues in a timely manner? Options: A Implement rate limiting on the API. B Implement geoblocking on the WAF. C Implement OAuth 2.0 on the API. D Implement input validation on the API. if you could explain why you chose that correct choice, Id appreciate it. Thank you!



