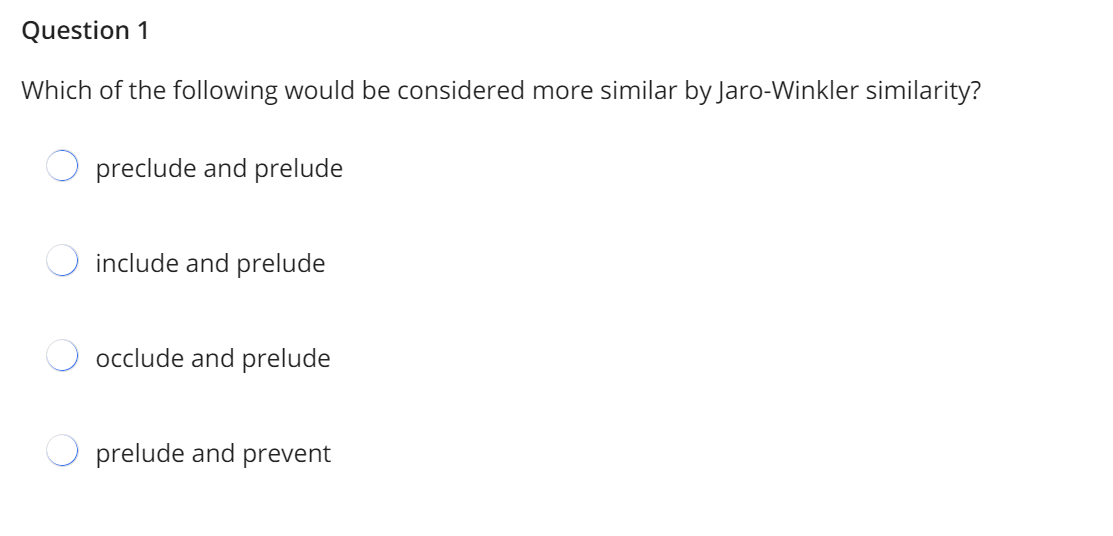
Which of the following would be considered more similar by Jaro-Winkler similarity?
Q: Computer science Which distinctions between physical location exchanges and computer/telephone netw...
A: Please refer below for your reference: The distinctions between physical location exchanges and comp...
Q: What is the distinction between optimistic and pessimistic locking?
A: Optimistic Locking strategy where you read the record, note the version number (other ways to do thi...
Q: Make a C program using a C project that will create an array of 10 scores. Create functions to comp...
A: Please refer to the following steps for the complete solution to the problem above.
Q: A computer forensic expert is called to the scene of a crime. What is the first thing the investigat...
A: The correct answer is Examination of Storage.
Q: le: 15, 20, 35, 10 *1/5 Out R
A: in rule: 15, 20, 35, 10 *1/5 Out Rule?
Q: In what ways does cloud computing differ from other types of computing?
A: Introduction: Cloud computing is a term that refers to the omnipotent and omniscient, as well as the...
Q: On Linux, how can a user work with prior Microsoft Office files?
A: Since, Microsoft Office is not directly supported by Linux it needs to installed using third party a...
Q: PROBLEM: Write a C++ program that will allow the user to input the First Name, Last name, Middle In...
A: 1)Read the input from the user first name, last name, middle initial and Grade 2)Display the first...
Q: Q1a) If a new application is built by a mobile platform, can it be created with web design? What's t...
A: Due to company policies I am compelled to solve only one question and that is the first question. Pl...
Q: Two significant breakthroughs in the history of computers should be described in a few sentences.
A: In the history of a computers, there have been two major breakthroughs: The first was John Ambrose F...
Q: Why and when should implicit heap-dynamic variables be used; when, how, and why should they not be u...
A: Answer the above questions are as follows:
Q: What are transaction isolation levels used for?
A: Transaction isolation levels The transaction specifies the level of separation that describes the l...
Q: 1.Classify the following IP addresses as A, B, or C and label the network and host parts of the IP a...
A: As per answering guidelines solving the first part and solving first three sub question of first que...
Q: What are the limitations on the use of Rumack-Matthew nomogram
A: The answer is given below.
Q: ompany SuperCrypto has invented a new superfast PKE algorithm whose security is based on the computa...
A: Lets see the solution.
Q: What are the various file stream classes? Explain the syntax for opening a file in both read and wri...
A: Different file stream classes There are 2 file stream classes and are as follows: ifstream ofstrea...
Q: xplain why NoSQL systems became popular in the 2000s and draw a quick comparison between their chara...
A: The answer is given below.
Q: cloud -What does IaaS (Infrastructure as a Service) mean?
A: Introduction: IaaS emerged as part of a bigger transition away from traditional hardware-oriented da...
Q: Consider the following scenario: you are the database administrator for the iTunes store. When it co...
A: Introduction: A database is a data storage center where we may store whatever information we desire ...
Q: Write a recursive method called sumDigits that finds the sum of all of the digits in an integer para...
A: We are going to write a recursive function which will return sum of digits of a number. I am provid...
Q: PROBLEM: Write a C++ program that will accept 3 strings (these should be of different sizes) then so...
A: I have provided C++ CODE along with CODE SCREENSHOT and TWO OUTPUT SCREENSHOTS------------...
Q: In the code editor, you are provided with the definition of a struct Dog. This struct needs a charac...
A: Use a for loop to iterate from 0 till size Then print the index of dog incremented by 1 and respecti...
Q: rio: you are asked to create a Java class MetaDisplay that contains a static void printTable(String ...
A: given - Consider the following scenario: you are asked to create a Java class MetaDisplay that conta...
Q: What does the superparamagnetic limit imply for disk drives and how does it affect them?
A: A form of magnetism that appears in small ferromagnetic or ferromagnetic nanoparticles called as Sup...
Q: SELinux is an example of what kind of Access Control? RBAC O DAC МАС O Rule-based Access Contral
A: SELinux stands for Security Enhanced Linux and this is a security architecture for Linux system that...
Q: Distinguish between the many forms of Semantics, when and how they are used, and what the pros and d...
A: Introduction: Semantics is one of the primary fields of linguistics, and it deals with the comprehen...
Q: 1. The simplicity of using the system is one of the key features that developers should consider whe...
A: The answer as given below:
Q: Design a class that attempts to determine the relative frequency of each letter by reading a file an...
A: Save file as with "txt" I have saved my file as "n.txt" And my file contains below data: i amtejas
Q: 2. Which of the following uses add to insert values? Check Box Text Box Combo Box Radio Button
A: Correct answer is Text box. Text box can be used to add to insert values.
Q: Represent the number 1.01011010101 x 2-19 in IEEE Standard 754 single precision floating point binar...
A: stating that as per our guidelines we are supposed to answer only one question. Kindly repost other ...
Q: These are values or sets of values. O Data Object O Data O Data object
A: The data is information that has been translated into a form that is efficient for movement or proce...
Q: What are the critical haptic display parameters?
A: Answer: Haptic Display: Haptic display represents a promising interface for human-computer interacti...
Q: Mobile application developement Q1 Evaluate the areas where mobile applications are applied and u...
A: Mobile application development
Q: . Describe the characteristics of the link-state and the distance-vector routing protocols and their...
A: Lets see the solution.
Q: What is the purpose of c# programming using the Datagrid Control?
A: Introduction: The Datagrid control allows you to show a collection of data in rows and columns in a ...
Q: Using a flowchart, describe white box testing.
A: White box testing means a scenario where the tester deeply understands the inner workings of the sys...
Q: Do not copy from other websites Q. You are in charge managing the performance of your organisation’...
A: This report will acquaint the peruser with the idea of execution estimation and matrix as applied to...
Q: for c++ A set is a collection of distinct elements of the same type. Design the class unorderedS...
A: Answer: Program #include <iostream>#include "unorderedSetType.h" using namespace std; int main...
Q: An organization has issued metal keys to its employees and has recently suffered some after hours em...
A: A keycard is defined as a security token which will grant access through electrically-powered doors....
Q: When it comes to data types, what are the pros and downsides of using user-defined ordinal kinds? An...
A: Introduction: An ordinal data type is one in which the potential values are related to the set of po...
Q: A network can be explained by its architecture. That is, it can either be Peer-to-Peer (P2P) or Clie...
A: As per our guidelines we are suppose to answer one question.Kindly repost other question as a separa...
Q: Write a program that prompts the user to input three positive angle values in degrees to determine w...
A: PROGRAM INTRODUCTION: Import the required libraries. Start the definition of the main function. Cre...
Q: 21. what is at put f this logic gati? A F=?
A: Here in this question we have given a a circuit and we have asked to find the output of this .
Q: How can businesses use cloud services in a secure manner?
A: Introduction: A VPN makes use of the general public web to simulate private, secure connections on a...
Q: Computer science Why is it necessary for a systems analyst to serve as a translator? Who may be a p...
A: Introduction: System analysts are responsible for ensuring that a firm's network and computer system...
Q: What are the most critical steps to improving data quality in a database?
A: Introduction: There are four methods for improving the quality of your data:
Q: This is the branch of law that involves two parties that have a grievance that needs to be settled. ...
A: Criminal is a popular term used for a person who has committed a crime or has been legally convicted...
Q: Computer science What are the approaches for creating a programme?
A: Introduction: The programming design process consists of the following steps: - Understanding the pr...
Q: Write a program that prompts the user to input coefficients A, B, and C of a quadratic equation in g...
A: The nature of roots depends on the value of discriminant So first calculate the discriminant and the...
Q: How to answer this? MODULE 1- NETWORKS TODAY1.0.5 Packet Tracer - Logical and Physical Mode Explorat...
A: The answer as given below:
Step by step
Solved in 2 steps

- Show how there might be a conflict between the First Amendment's protection of free speech and a business's ability to use a trademark. In what ways might these assertions, which seem to be at odds with one another, be reconciled?Present a relationship with the domain some subset of the integers that is to be proven via Mathematical Induction. Prove your relationship with the domain some subset of the integers via Mathematical Induction. Note you must detail each of the four steps and show all of the work.what are the the tradeoffs in this situtation ie, (each outcome with respect to principles that are in conflict)
- Which of the followingdecisions require knowledge based on collaboration andinteraction?7. For each of the following relations on the set of all real numbers, solve all of the subparts as they are all connected rightly on a word processing document to determine whether it is reflexive, symmetric, antisymmetric, transitive. Here xRy if and only if: (a) x + 2y = 0 (b) x = 2y(c) x − y is a rational number (d) xy = 0(e) xy ≥ 0 (f) x = 1 or y = 1 (f) x = 1 or y = 1(g)x is a multiple of y (h) xy = 1Prove your relationship with the domain some subset of the integers via Mathematical Induction. Note you must detail each of the four steps and show all of the work. Step 1: Show true for the first element of the Domain. Step 2: Assume true for arbitrary even integer: Step 3: Show true for next element of the Domain
- Artificial Intelligence Assuming that an arrow (X ->Y) in Figure Above depicts a parent relation from X to Y, in other words, X is parent of Y. Answer the following: - Enlist the various facts in terms of clauses. Is Zahidparent of Nabeel? Is Sabirparent of Amna? Is Nabeel parent of Naila? Find all children of Adil. Enlist all parent-child relations. Who is grandparent of Nabeel? Who are grandchildren of Nasir? Are Zahidand Amna siblings? What are the results of the following prolog statements? ? - parent (X,Zahid). ? - parent (Amna, X). ? - parent (X, Y). ? - parent (Naila, X). ? -parent (Y, Kashif).Consider the effect that the proliferation of personal computers and the Internet have had on the design of computer systems to put this into perspective. Make sure that your claims are supported with proof, if that is at all feasible.C.W. Churchman once said that "Mathematics...tends to lull the unsuspecting that he who thinks elaborately thinks well." Do you think that the best QA Models are the ones that are most elaborate and complex Mathematically? Why?

