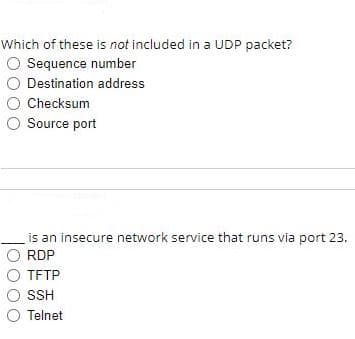
Which of these is not included in a UDP packet? O Sequence number Destination address Checksum O Source port is an insecure network service that runs via port 23. RDP O TFTP SSH
Q: installer executes 'ipconfig' to see what the IP addres is but it comes up with a 169.254.254.10…
A: Question 7: Answer is APIPA(automatic Private IP Addressing) Explanation: computer need a valid IP…
Q: All UDP datagrams leaving a local network via a NAT box must have the same: A source IP address B…
A:
Q: A network administrator is configuring DHCP snooping on a switch. Which configuration command should…
A: Q. A network administrator is configuring DHCP snooping on a switch. Which configuration command…
Q: What does a cybersecurity analyst know about their target if they receive a RST packet back from a…
A: 1. The target is active but the port is closed if you get an RST (reset) packet back from it. If no…
Q: Q) Which authentication method stores usernames and passwords in the routerand is ideal for small…
A: The right answer is Option(b) local AAA Explanation:- local AAA authentication, authorization and…
Q: Which of the following command is used to manipulate network routing table? a. Route Print O b.…
A: a.) Route print command Route command is useful to view and to manipulate the IP network routing…
Q: Which application protocol is used between two mail servers? Group of answer options SMTP POP…
A: A computer network is a collection of computers connected by digital linkages and using a set of…
Q: hich of the following are the identification fields for a UDP socket? destination IP, destination…
A: A socket is a unique identifier for a process on a system. A system can have connections with more…
Q: Which Scopes is used to assign IPV4 address pools for Class A, B, and C networks in a DHCP Server,…
A: Normal Scope - Allows A, B and C Class IP address ranges to be specified including subnet masks,…
Q: To add the IP address 204.168.8.100 with the MAC address 00-14-22-01-23- 45, what command will you…
A: The solution to the given problem is below.
Q: While troubleshooting a recurring problem on your network, you will want to examine the TCP messages…
A: For examining the TCP messages exchanged from server to client or client to server , Wireshark…
Q: Which Scopes in a DHCP Server is used to offer IPV4 address pools for Class A, B, and C networks and…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. With a DHCP…
Q: Which of the following port scans attempts to establish a communication channel via TCP three-way…
A: TCP basically stands for Transmission control protocol.It controls all transmission of data in…
Q: Write the appropriate commands on paper to configure a DHCPV4 Server and EtherChannel…
A: Answer: I have written command and also I have attached command as well as command screenshot.
Q: To test DNS configuration by resolving a host name to an IP address, which commandor commands can…
A: To test DNS configuration by resolving a hostname to an IP address, the following command can be…
Q: * For this IPV4 address 10.440.0/17 the broadcast IP Is: O 10.4.122.255 O 10.4.128.255 O 10.4.127254…
A: As per the above question or the first question answer will bvbe option A: 10.4.127.255 Calculation…
Q: 22. Checksum, as used in the transport layer, can detect all errors. a. True b. False
A: Note: As per the bartleby policy we can answer single question at a time if you want the solution of…
Q: Which of the following commands on a router is true about the command "service password- encryption?…
A: Encryption
Q: In linux, what is the iptables command that allows inbound UDP packets to the server ports 10001 to…
A: iptables command in Linux: iptables is a command line interface used to set up and maintain…
Q: Which of the following is used by hosts and routers to report errors? (A) ICMP (в) NAT CIDR DHCP
A: A distributed denial of service attack is attacked by the attackers which tries to avert allowable…
Q: Which of the following is a method of mitigating NTP attacks? False Update Prevention O Router…
A: All the choices are correct but the most appropriate choice is option D, NTP Authentication.
Q: A smurf attack occurs when an oversized ICMP packet is sent the host is the recipient of repeated…
A: 1} A Smurf attack occurs when _____________ Ans) an oversized ICMP packet is sent. (Option1) An…
Q: Dualipa get a message 'unusual traffic detected' from Google, although she had not performed any…
A: answers are given below with explanation
Q: While setting up a computer on the network, you use 'ipconfig' and see that the IP address is…
A: We are given current ip as 10.24.16.160 with subnet mask 255.255.255.192. Gateway is a device which…
Q: When a fresh IP configuration is required, DHCP clients issue a DHCPREQUEST packet. Is this true or…
A: DHCP Dynamic Host Configuration Protocol is a network management protocol. It is used on Internet…
Q: During the process of redistributing a route into EIGRP, which parameter has to be specified? Exit…
A: Introduction: Redistribution is the use of a routing system to promote routes that have been learnt…
Q: A system administrator at a SOHO remote site would like to modify the range of…
A: The DHCP configuration of a SOHO router can be configured with the beginning and ending DHCP address…
Q: Which one of the following protocols is used to resolve IP addresses to Domain name? O a. DHCP O b.…
A: Here in this question we have asked about the protocol which is used to resolve IP address to domain…
Q: An IT administrator wants to assure that a client PC always acquires the same IP address from a DHCP…
A: 1) A DHCP Server is a network server that automatically provides and assigns IP addresses, default…
Q: What is a characteristic of an IPv4 loopback interface on a Cisco IOS router? O a. It is a logical…
A: The Answer is given below step.
Q: All UDP datagrams leaving a local network via a NAT box must have the same: (A) source IP address B…
A: All UDP Datagrams leaving a local network via a NAT box must have the same. Correct option is…
Q: Which Scopes is used to assign IPv4 address pools for Class A, B, and C networks in a DHCP Server,…
A: Multicast Scope - Used to assign IP address ranges for Class D networks. Multicast scopes do not…
Q: he following is a dump of a UDP header in hexadecimal format. CB840045001C001C a. What is the source…
A: GIVEN: The following is a dump of a UDP header in hexadecimal format.CB840045001C001Ca. What is the…
Q: Which of these would NOT be a valid Internet Control Message Protocol error message? Destination…
A: The Answer is in step2
Q: Which of the following layer 2 attack will result to not allow the legitimate user to get the valid…
A: DHCP Starvation: In this type of attack is based on the fact that each DHCP server has a fixed…
Q: q12
A: Answer: You receive a compliant that some of the web-servers are no longer accessible. You attempted…
Q: ***** When the load is greater than the capacity, the delay.. b. Increases linearly c. Goes to…
A: 1) C option is correct that is: Goes to infinity Explanation: Packets become blocked at nodes when…
Q: Write command-set that could configure a switch’s IP address 192.168.1.5 255.255.255.0 on vlan1
A: if multiple questions are posted, then as per company guidelines only first question need to be…
Q: Which file stores the TCP/IP addresses of the DNS servers used to resolve host names ifno DNS…
A: The transmission Control Protocol/ Internet Protocol is the protocol for communication between two…
Q: workstation
A: According to the question, everything mentioned there is only one glitch we can identify and it's…
Q: Deliver packet to higher layer (eg. TCP, UDP) Process (AH/ESP) Match found ВYРASS Not No match…
A: When the regular IP packets are received thens search is performed by an IPSEC to match with the…
Q: Which type of IPV6 address is used to send a single IPV6 packet to multiple destinations? a.…
A: Question from basics of IPv6, we have different types of addresses in Ipv6 like Multicast, Unicast…
Q: The command below illustrates the configuration of static route. Router(config)# ip route…
A: Dear Student, The function of the parameter distance is to set an administrative distance(AD) whose…
Step by step
Solved in 2 steps

- On the receiver's return, I want all TCP traffic from my internal network to pass via the firewall. This traffic is allowed by what rule? Port 80/HTTP Standard Established ICMP115. Which one of the following is a cryptographic protocol used to secure http connection ? a) Stream Control Transmission Protocol (SCTP) b) Transport Layer Security (TLS) c) Explicit Congestion Notification (FCN) d) Resource Reservation Protocol (RRP)To test DNS configuration by resolving a host name to an IP address, which commandor commands can you use? (Choose all that apply.)a. nslookup hostnameb. dig hostnamec. host hostnamed. resolve hostname
- A system administrator at a SOHO remote site would like to modify the range of automatically-assigned IP addresses. Which of the following should be modified on the SOHO wireless router?WPA2 security modePrimary and secondary DNSDMZ interfaceMAC filteringDHCP ending addressFrom your laptop, you need to remote into a switch to make some configuration changes.Which Transport layer protocol and TCP/IP port should you open in Windows Firewall tomake this work using Telnet?a. UDP, port 23b. TCP, port 23c. UDP, port 22d. TCP, port 22e. UDP, port 2122. Checksum, as used in the transport layer, can detect all errors.a. Trueb. False 23. Which of the following protocols cannot be used by a user agent to retrieve email messages fromits SMTP server?a. POP3b. SMTPc. IMAPd. HTTPe. All of the above
- Which file stores the TCP/IP addresses of the DNS servers used to resolve host names ifno DNS servers are specified within the network configuration file for the NIC?a. /etc/hostsb. /etc/host.confc. /etc/resolved. /etc/resolv.confWhich tunneling protocol is acomponent of the IPsec protocol suite?a. L2TPb. OpenVPNc. PPTPd. IKEv2How long did it take from when the HTTP GET message was sent from your browser navigating to http://<your-DSL-IP-Address>ntil the HTTP OK reply was received? More than a second More than a minute Less than a second Less then a minute
- Locate the packets in the capture utilizing the UDP transport protocol that AREN'T DNS packets. Which application protocol is represented by those packets? You may have to performa little research (Google, etc.) A Ethernet B Internet Protocol C Hot Standby Router Protocol D Hyper Text Transfer ProtocolWhich Scopes in a DHCP Server is used to offer IPV4 address pools for Class A, B, and C networks and contains an IP address range assignment that includes the subnet mask, exclusions, and reservations? * Standard Opinions Scopes for Failover Greetings Multicast Scopes, Super ScopesWhich of the following ports maintain a database of the NetBIOS names for hosts and the corresponding IP address : TCP 53 TCP 137 UDP 389 UDP 137

