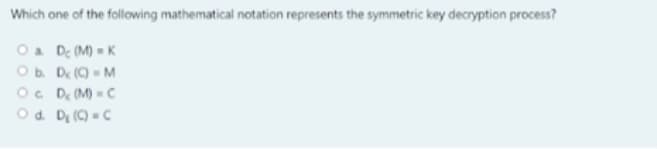
Which one of the following mathematical notation represents the symmetric key decryption process? Oa De (M) = K Ob De (9 - M Oc D M) C Od. D, () =C
Q: D D Question 23 Which one is used as a "computational infeasible barrier"? Firewall IDS O Access…
A: Computer Networks which refers to the set of the computer which is the connected by the transmission…
Q: Which of the following is NOT a functionality that encryption algorithms can provide? Lütfen birini…
A: Answer : - Option (E) is correct . i,e. None of the above is correct option . Explaination :- A…
Q: Which of the following statements are correct? Group of answer choices In the symmetric key crypto,…
A: The following statements are correct 1. In the symmetric key crypto, we need to share a secret with…
Q: 16. Which one of the following cannot be taken as a primary key ? a. Id b. Register number c.…
A: Here is the solution which is mentioned below:
Q: 1. Which of the following public key cryptosystem application can be used by RSA? O a. Key exchange…
A: RSA: It is a public key cryptosystem used for secure data transmission. It is asymmetric…
Q: In the case of Public Key Authority It is necessary to make a request for B's public key, and the…
A: Introduction: In a key exchange, one party generates the secret key and encrypts it using the…
Q: Refer to Cybersecurity.ipynb, the cc_encrypt_character(char, key) function applies the value of cc_n…
A: here is the correct answer to this question:-
Q: 5. Which of the following application is not one of the public key encryption categories? a. Digital…
A: Cryptography: Cryptography is the process of securing a message or information by encrypting it…
Q: Kerberos relies exclusively on __________ . A. symmetric encryption B. asymmetric encryption C.…
A: Asymmetric encryption: Asymmetric encryption is a public key encryption. It is a form of data…
Q: Which of the following modes of Symmetric Key Block Ciphers is relatively less secure compared to…
A: 1.electronics code book is not more secure in symmetric key block cipher compare to other In…
Q: Q2: Based on Data Encryption Standard (DES), if the shared key is "Informed" and the output of Round…
A: Data encryption standard (DES) has been found vulnerable against very powerful attacks and…
Q: q13) Which key combination the Sender should apply in order to achieve confidentiality in public…
A: a. Receiver Private Key b. Senders Private Key
Q: If each user in a group of 12 people wants to communicate secretly and bidirectionally with each…
A: Asymmetric Encryption consists of two cryptographic keys known as Public Key and Private Key. The…
Q: Which of the following identifies the disadvantage of symmetric encryption?
A: Sharing the Key is the biggest problem with symmetric key encryption is that you need to have a way…
Q: Your first and last names as a plaintext, please perform encryption using the following…
A: The Playfair cypher was the first digraph substitution cypher to be used in practise. The cypher was…
Q: Based on the following scheme. Answer the following questions. E PRa E(PRa, M) PU, E(PU, E(PRa, M))…
A: It is defined as the process of verifying the identity of a person or device. A common example is…
Q: Consider the following AES cipher key: 34 22 2a 3e 00 11 33 ff fe ab 22 11 3e e4 2c 55 What is the…
A: Consider the following AES cipher key: 34 22 2a 3e 00 11 33 ff fe ab 22 11 3e e4 2c 55 What is the…
Q: Signed by same ephimeral key Key ? long 1. How cam 2 Messages m.,m2 Mecoven the torm
A: Given question:-
Q: Which of the following is TRUE? R CFB is MORE efficient than CBC for encryption the same size of…
A: The, answer has given below:
Q: Public Key Authority is one example of this. Before sending a message to A, the Public Key Authority…
A: Authority in Charge of Public Keys: It's comparable to the directory, but it adds security by…
Q: Provide any 5 differences between private key encryption (symmetric encryption) and public key…
A: This question comes from Cryptography in Cybersecurity which is a paper of Computer Science. Let's…
Q: In Public Key Authority A request for B's public key and Public Key authority prepares the message…
A: Below is the answer:
Q: QUESTION 5 Choose the correct answer: one key used for encrypting (public key) and another for…
A: Note: we are only allowed to solve one question in one post. I am solving the first on here. To get…
Q: Which of the following passwords is the most secure? 87654321 changeme p63lmhZ passwOrd
A: Please find the solution below:
Q: Vigenere Cipher By finding the key length in worksheet 7 .doc, you can use frequency analysis for…
A: F 46 8.534 % E 37 6.865 % U 34 6.308 % P 33 6.122 % T 32 5.937 % C 29 5.380 %…
Q: In Public Key Authority A request for B's public key and Public Key authority prepares the message…
A: what is public key encryption: I is a asymmetric crypto system in which public key and private key…
Q: he public key encryption is explained in detail here.
A: USE OF A PUBLIC KEY FOR DESCRATCHING: Cryptographical encryption is the technique of encrypting data…
Q: Which of the following is not one of the encryption functions? A. Hash Coding B. Asymmetric…
A: Encryption Function: Encryption is a way of translating data from plaintext(unencrypted) to…
Q: OP_DUP OP_HASH160 OP_EQUALVERIFY OP_CHECKSIG
A: The Scripting language used in Bitcoin is stack based, which means each data, input or output is put…
Q: Which of the following are symmetric key ciphers? Select all that apply. DES RSA Diffie-Hellman OAES…
A: According to question i give you all correct answer in step 2
Q: One disadvantage of symmetric cryptography is Select one it is not scalable Ob. tis not efficient…
A: This question is comes from Cryptography which is a paper of Computer Science. Note: "As we have…
Q: How long is the sub-key that is used in each round of DES? 32 56 48…
A: Lets see the solution.
Q: In brute force attack, on average half of all possible keys must be tried to achieve success. i)…
A: Question. In brute force attack, on average half of all possible keys must be tried to achieve…
Q: hich key combination the Sender should apply in order to achieve confidentiality in public key…
A: Public Key Cryptography Public Key Cryptography uses two different keys to perform encryption and…
Q: Which of the following symmetric key encryption ciphers provides the strongest protections O DES AES…
A: Given:
Q: Which of the following statements about Anonymity is CORRECT:
A: The correct"The Anonymity set of your transaction is the set of transactions without real…
Q: Which of the following categories of cipher no quality control? а. Substitution ciphers b. Product…
A: The quality control ensures that the end product developed fulfills all criteria. Substitution…
Q: 2. Which of the following is an example of substitution cipher? O a. AES O b. Rail Fence cipher O c.…
A: c) Caesar cipher The correct option is c)
Q: No plagarism please! Correct and detailed answer will be Upvoted else downvoted. Thank you!…
A: In this answer I will be discussing about polygram substitution ciphers.
Q: Given the following: • Plaintext: HARDWIRED • Key: FUNK • Blocksize: 4 What is the ECB ciphertext? O…
A: Answer : Given Data - Plaintext : HARDWIRED Key : FUNK Blocksize : 4
Q: What type of cipher has a weakness when we have large amounts of repetitive data? O Recoded ciphers…
A: The problem is based on the basics of cyber security.
Q: QUESTION 8 Which of the following is true if the Maxirmum-Age of a cookie is omitted: O This gives…
A: This indicates that the cookie will expire at the end of the current session (when the browser…
Q: Which of the following statements related to DES is correct? O a. It is an asymmetric key cipher O…
A: Explanation: The DES is a symmetric-key block cipher. it is an implementation of a Feistel Cipher.
Q: a. K = 3 b. Ciphertext: SVFPDQOODHAXHBHUXWDOHHVGDVB plaintext: PSCMANLLEAUEBERUTALEESDASB 2.…
A: Every cipher you mentioned is a cipher based on a letter, meaning that you exchange one letter for…
Q: Which one of the following cipher is an example for symmetric-key algorithm? O a. DSA Ob. RC4 O. RSA…
A: Answer: symmetric-key algorithm is the simplest kind of encryption that involves only one secret key…
Q: Which of the following statements regarding a CA is not correct? a. CA publishes expired digital…
A: In this answer I will be discussing about the Certificate authority.
Step by step
Solved in 3 steps

- If an RSA system, the public key of a given user is e = 31, n = 3599. What is the privet key of this user? If x = 3 mod 7, and x = 5 mod 13, and x = 8 mod 11, what value is x? Show all the steps. If code was used to solve this question then attach the code snippet with the answer. If any online-service or reference were used then clearly state so and provide the reference.Consider the following AES cipher key: 34 22 2a 3e 00 11 33 ff fe ab 22 11 3e e4 2c 55 What is the first round key generated from the above cipher key based on the AES key scheduling algorithm?Suppose p=5 and q=11. Which of the following is the private key of an RSA cryptosystem with public key (n,e)=(55,7)? a. (55, 23) b. (55, 15) c. (55, 39) d. None of the Above
- Her public key certificate is valid from 1000 hours on the 9th November 2013 to 1000 hours on the 9th November 2014, according to Alice's certificate. As of the 15th of March 2014, the certificate was cancelled. This list is published every day at midnight by the CA. Dates are determined by the following:As soon as Alice's certificate arrives in the CRL and as soon as it departs from the CRL, respectivelyPlease describe the solution in detail.Which of the following is the number of secret keys required for 6 people to message via symmetric encryption? a) 6 B) 11 C) 15 D 21In the case of Public Key Authority It is necessary to make a request for B's public key, and the Public Key Authority must prepare a message (E(PRauth[PUB] || Request || Time1]) before sending it to A. What key A should use to decipher the message is up for debate.
- What precisely is the difference between stream ciphers and block ciphers? Stream ciphers and block ciphers both encrypt data. Please offer an explanation for each of the following: three separate differencesAlice owns public key certificate valid from 1000 hours of 9TH November 2013 to 1000 hours of 9TH November 2014.The certificate was revoked at 1700 hours on 15th March 2014. The CA publishes the CRL daily at 0000 hours. Determines the dates:a) When the Alice’s certificate appears in the CRL andb) When it disappears from the CRL.please provide steps to explain solution.Which of these encryption techniques does NOT rely on a key? a. Polyalphabetic substitution-based cipher b. Data Encryption Standard c. Monoalphabetic substitution-based cipher d. Transposition-based cipher No hand written and fast answer with explanation

