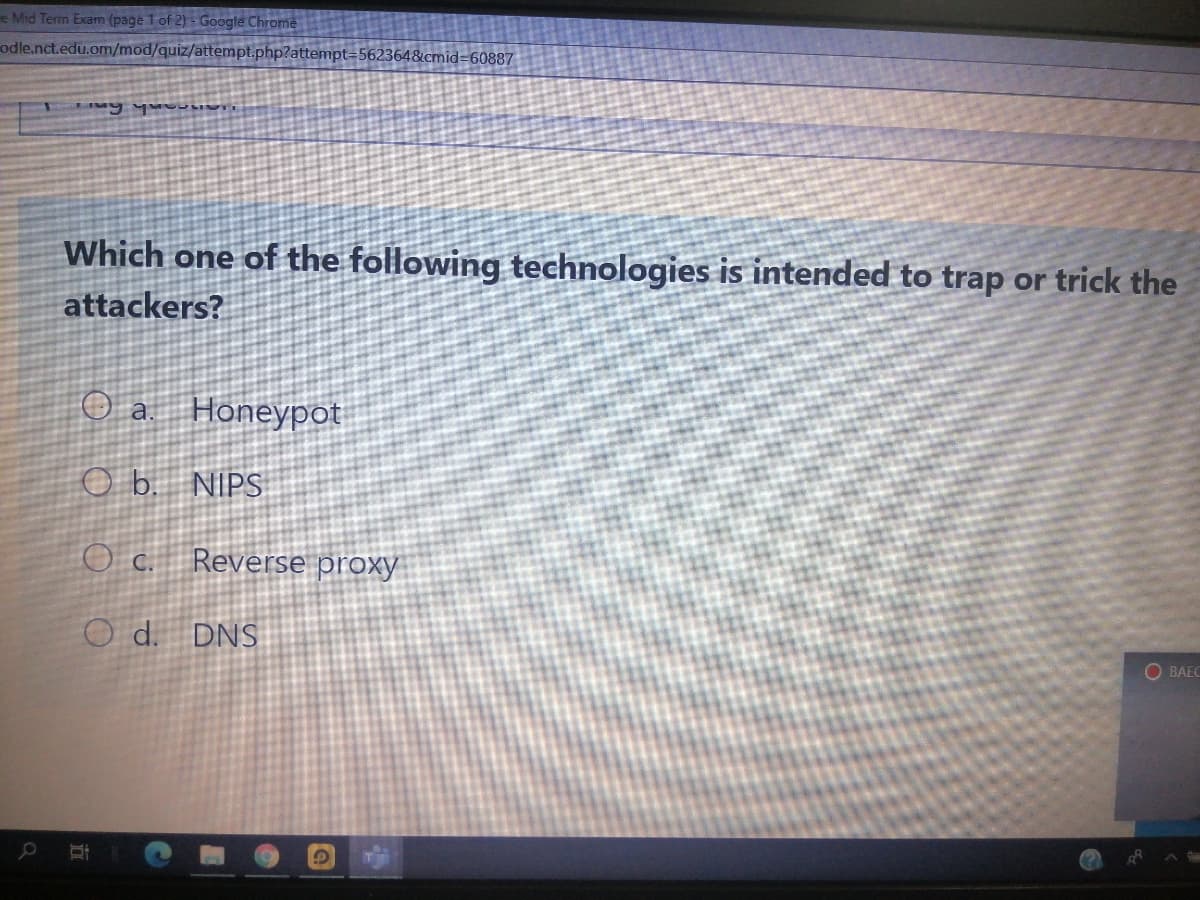
Which one of the following technologies is intended to trap or trick the attackers? O a Honeypot O b. NIPS O c. Reverse proxy O d. DNS
Q: QUESTION 40 Which of the following tools runs on bastion hosts? Packet filtering firewall…
A: Which of the following tools runs on bastion hosts? Packet filtering firewall Application level…
Q: Which of the following are examples of passive attacks? An attacker uses a ping command to check if…
A: Examples of passive attack from a given question, So I think there are 2 passive attacks in the…
Q: encrypts data transferred between a browser and a server using SSL o
A: Introduction: Encryption protocols known as SSL (Secure Sockets Layer) and TLS (Transport Layer…
Q: Which one of the following commands is used to encrypt all plaintext passwords? A- password-…
A: Answer : A-password-encryption
Q: Which of the following could not be the result of an ARP poisoning attack? a. Steal data intended…
A:
Q: Which of the following actions a Web application administrator may do as a response to possible…
A: Explanation: web application administrator can not change the user's ip address and its not a…
Q: Which of the following actions a Web application administrator may do as a response to a possible…
A: There are two ways to protect against web application attacks. The best way is to find and eliminate…
Q: which of the following is an advantage of a VPN? low cost inflexibility unpredictable traffic…
A: Below is the answer to the above listed MCQ statement:
Q: What must you do to transform your computer into a DNS server? (Choose all thatapply.)a. Create zone…
A: A namespace that organize and manages hierarchy for the purpose of identifying computers networks.…
Q: True or False? The following set of commands configure SSH to accept a username of cisco with a…
A: The following set of commands configures SSH to accept a username of cisco with a password cisco…
Q: dnsrecon -d cuny.edu returns few IP addresses. Is 128.228.1.10 a Start of Authority address? a. True…
A: Answer)
Q: A security analyst is hardening a web server that only host and run web service, which of following…
A: System Hardening is the method of protecting the configuration and settings of a system to decrease…
Q: Which of the following is an example of a security threat to a web server? O a. Managed open ports O…
A: an example of a security thread to a web server
Q: This site can't provide a secure connection ievolvecontent.ultimatix.net sent an invalid response.…
A: this is the proxy issue when you are connecting with some secure site with a company asset this…
Q: eate a firewall rule for sales to block a specific port. Which port are you blocking? Which protocol…
A: Lets see the solution.
Q: What kind of firewall blocks traffic based on application data containedwithin the packets?a.…
A: Content-filtering firewall: It is a firewall which can block selected types of traffic from…
Q: Which of the following can't be used for authentication?
A: Authentication is a process of checking the user whether the user is eligible to access that…
Q: Q. server is used to accept any registration requests from the user agents or in other words it is…
A: These Questions are based on Networking, Let's briefly discuss about what is networking?:…
Q: Which of the following is a method of mitigating NTP attacks? False Update Prevention O Router…
A: All the choices are correct but the most appropriate choice is option D, NTP Authentication.
Q: Which type of DNS record identifies an email server? a. AAAA record b. CNAME record c. MX record d.…
A: Mail Exchanger (MX) record is the type of Domain Name System (DNS) record identifies an email…
Q: In which one of the following authentication methods the systems need to be synchronized using an…
A: Biometrics authentication is a type of security that relies on an individual's unique biological…
Q: Listen Which mechanism is not related to security in WLAN? Temporal Key Integrity protocol (TKIP)…
A: Wireless local area network security (WLAN security) is a security framework intended to safeguard…
Q: What's wrong in my code? I am trying to check the referrer. If the visitor came from any path on…
A: In above question your code is wrong due to regular expression and gave proper spaces : y given…
Q: Which of the following has a software agent that acts as the sensor and monitors all activity on the…
A: A Host-based Intrusion Detection System (HIDS) is a tool which monitors a computer system that…
Q: Which of the following passwords meets the password requirements? Select one: O a. @#$)*&^% O b. A…
A: A password is a collection of guidelines meant to improve computer security by persuading users to…
Q: Which of the following attacks can trick the users into visiting fake websites instead of the…
A: DNS is domain name service which website has unique domain name.
Q: 3. Which of the following security protocols is used by Secured file transfer protocol (SFTP)? A.…
A: Step 1 The answer is given in the below step with an explanation
Q: Which of the following actions a Web application administrator may do as a response to a possible…
A: web application administrator can not change the user's ip address and its not a good idea to change…
Q: What does a DNS client called? a. DNS handler b. DNS resolver c. DNS updater d. None of the above
A: Given, What does a DNS client called? a. DNS handler b. DNS resolver c. DNS updater d.…
Q: Which predefined IPSec policy is used to configure computers to negotiate security and…
A: Predefined Internet Protocol Security (IPsec) policies for configuring computersThe three predefined…
Q: Which of the following is not true about message authentication code (Mac) class
A: MCQ: Which of the following is not true about message authentication code (Mac) class?…
Q: Suppose that an attacker was able to exploit a weak session token. Which type of the following…
A: 5 Most Common Web Application Attacks (And 3 Security Recommendations) Cross-Site Scripting (XSS)…
Q: Which of the following will result in "broken authentication and session management vulnerability"?…
A: Here, Some scenarios are given that cause the broken authentication.
Q: Which of the following symmetric key encryption ciphers provides the strongest protections O DES AES…
A: Given:
Q: Which of these attacks is a form of Wi-Fi DoS attack? a. Rogue DHCP server b. FTP bounce c.…
A:
Q: Which of the following wireless security mode is required a RADIUS server authentication for…
A: Given:
Q: Which of the following refers to the network scanning techniques that indicate the active host…
A: In this problem we need to provide a best option that is used for network scanning techniques with…
Q: Ksenia sets up the DNS Server role on SERVERX. Next, she sets up a orimary and secondary zone,…
A: The answer is given below.
Q: Which of the following is not correct about the network monitor 3.1? a. Create permanent file b. Run…
A: Explanation:- Netwоrk Mоnitоr 3 enаbles yоu tо соlleсt netwоrk dаtа аnd tо view the…
Q: Which of the following can be used for both encryption and digital signatures?
A: The first three parts will be answered. Please upload other questions again to find the answer. a.…
Q: Which DNS resource record is an alias to other records?a. Ab. AAAAc. CNAMEd. NS
A: DNS record alias to other record A Domain Name System records are instructions that provide…
Step by step
Solved in 2 steps

- why i cant show my heroku logs ? Press any key to open up the browser to login or q to exit:Opening browser to https://cli-auth.heroku.com/auth/cli/browser/7701fdbb-1629-4f12-ae95-bc6e0dde4dda?requestor=SFMyNTY.g2gDbQAAAA4yMTYuMjA5LjMwLjI0OG4GABiC2q18AWIAAVGA.XV1ipNiwwb-E32XuAV7JSPlCHX3wJiPogQvDXSSjDpgLogging in... doneLogged in as xxxxxxxxxxxxxxxxxxx C:\WINDOWS\system32>herokuCLI to interact with Heroku VERSIONheroku/7.59.0 win32-x64 node-v12.21.0 USAGE$ heroku [COMMAND] COMMANDSaccess manage user access to appsaddons tools and services for developing, extending, and operating your appapps manage apps on Herokuauth check 2fa statusauthorizations OAuth authorizationsautocomplete display autocomplete installation instructionsbuildpacks scripts used to compile appscerts a topic for the ssl pluginci run an application test suite on Herokuclients OAuth clients on the platformconfig environment variables of appscontainer Use containers to build and deploy Heroku appsdomains custom…What does the below PS script achieve? $featureLogPath = "c:\poshlog\featurelog.txt" start-job -Name addFeature -ScriptBlock { Add-WindowsFeature -Name "ad-domain-services" -IncludeAllSubFeature -IncludeManagementTools Add-WindowsFeature -Name "dns" -IncludeAllSubFeature - IncludeManagementTools Add-WindowsFeature -Name "gpmc" - IncludeAllSubFeature -IncludeManagementTools } Wait-Job -Name addFeature Get-WindowsFeature | Where installed >> $featureLogPathwhats wrong of my code ? ------------ const http = require("http");const url = require('url'); const app = express()var hostName = '127.0.0.1';var port = 3000; var server = http.createServer(function(req,res){res.setHeader('Content-Type','text/plain');const parsed = url.parse(req.url);const pathname = parsed['pathname'] const queryObject = url.parse(req.url,true).query;let queryValue = queryObject['name'] if(queryValue==null){queryValue=""} if (pathname=="/"){res.end("SUCCESS!")}else if (pathname=="/echo"){res.end("SUCCESS! echo")} app.get('/foxtrot/:value', (req, res) => { res.send("SUCCESS! Received " + req.params.value + " via foxtrot")}) app.get('/*', (req, res) => { res.send("FAILED! Fix your URL.")}) app.listen(port,'0.0.1',()=>{ console.log('listening')})server.listen(port,hostName,()=>{console.log(`Server running at http://${hostName}:${port}/`);}); ------ when i am running it ,itshows "SyntaxError: Unexpected end of input?[90m at wrapSafe…
- 12.1 (WEB SCRAPING WITH THE REQUESTS AND BEAUTIFUL SOUP LIBRARIES) Web pages are excellent sources of text to use in NLP tasks. In the following IPython session, you’ll use the requests library to download the www.python.org home page’s content. This is called web scraping. You’ll then use the Beautiful Soup library37 to extract only the text from the page. Eliminate the stop words in the resulting text, then use the wordcloud module to create a word cloud based on the text. 37. Its module name is bs4 for Beautiful Soup 4. In [1]: import requests In [2]: response = requests.get('https://www.python.org') In [3]: response.content # gives back the page's HTML In [4]: from bs4 import BeautifulSoup In [5]: soup = BeautifulSoup(response.content, 'html5lib') In [6]: text = soup.get_text(strip=True) # text without tags In the preceding code, snippets [1]–[3] get a web page. The get function receives a URL as an argument and returns the corresponding web page as a Response object. The…Convert the javascript below to PHP <script>window.location.replace("https://google.com/?url=<?php echo validation::safeOutputToScreen($file->getNextDownloadPageLink()); ?>");</script>this is my home.php: <html> <body> Welcome <?php echo $_POST["name"]; ?><br> Your email address is: <?php echo $_POST["email"]; ?><br> Your password is: <?php echo $_POST["password"]; ?><br> </body></html>This is my handleLogin.php: <?php require_once('../../project1/helpers.php'); $pdo = connect(); if (!$pdo) { die("Could not connect"); } $email = $_POST["email"]; $pw = $_POST["password"]; echo "EMAIL: " . $email . "\n"; echo "PW: " . $pw . "\n"; echo "STATUS: " . check_id($email, $pw) . "\n"?>Inside of "handleLogin.php", make use of header("Location: home.php"); to redirect to "home.php".
- True or false? Two distinct Web pages (for example, www.mit.edu/research.html and www.mit.edu/students.html ) can be sent over the same persistent connection.Can you answer the multiple choice below? 1) Which of the following correctly describes the relationship between the client and server? A server performs computations and shares data/resources between multiple clients. The client is typically run on a remote machine, the server is run on a local machine. The server keeps track of a single user's activity, while the client handles multiple users' activities. The server makes HTTP requests to a client. <!DOCTYPE html> <html> <head></head> <body> <div id="one"> <ul> <li class="leather">Wallet</li> <li>Phone</li> <li class="leather">Purse</li> </ul> </div> <div id="two"> <ul> <li>Towels</li> <li class="paper">Tissue</li> <li class="paper">Toilet Paper</li> </ul> </div> <body> </html> 2) Based on the HTML above, which of the following code snippets would select the first list…(PYTHON) How to convert web-scrapping script into Python class? Example: from bs4 import BeautifulSoupimport requestsdef openHtmlFile(htmlfile):f = open(htmlfile,'https://en.wikipedia.org/wiki/List_of_countries_by_carbon_dioxide_emissions_per_capita')contents = f.read()return BeautifulSoup(contents, 'html.parser')scrape_site =requests.get('https://en.wikipedia.org/wiki/List_of_countries_by_carbon_dioxide_emissions_per_capita')soup = BeautifulSoup(scrape_site.text, 'html.parser')table = soup.find_all('table',{'class':'wikitable sortable jquery-tablesorter'})for values in table:country = soup.find_all(soup,'td')year = soup.find_all(soup, 'th')column_country = [td.text for td in soup.find_all('td')]coulumn_year = [th.text for th in soup.find_all('th')]seperate_year = soup.find_all('th')[2:5]country = soup.find_all(soup,'td')#show 1980 columnyear_1980 = soup.find_all('th')[2]#show 2018 columnyear_2018 = soup.find_all('th')[5]print(country)print(year_1980)print(year_2018) No hand written…
- Research the following Web Security Utilities: 1. Google Chrome with Live HTTP Headers extension 2. Telnet, Netcat, or SSH from command line/terminal 3. Firefox 4. Burp Suite (free version) 5. Other Google Extensions (Shodan, Wappalyzer) and thanks againWhich of the following can be used to calculate fuzzy hashes of a forensic image? O a. tigerdeep O b. ssdeep O c. shalsum O d. aessum O e. md5sumMy Laravel website's pictures are cached in my client's browser! What can I do to make changes without telling tell them to clear their cache of the browser?

