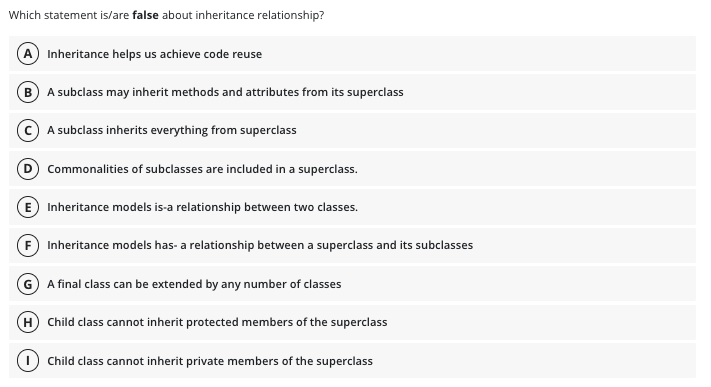
Which statement is/are false about inheritance relationship? A) Inheritance helps us achieve code reuse B A subclass may inherit methods and attributes from its superclass (C) A subclass inherits everything from superclass Commonalities of subclasses are included in a superclass. E Inheritance models is-a relationship between two classes. Inheritance models has- a relationship between a superclass and its subclasses G A final class can be extended by any number of classes (H) Child class cannot inherit protected members of the superclass Child class cannot inherit private members of the superclass
Q: Write a Perl program that passes by reference a literal to a subprogram, which attempts to change…
A: Perl which refers to the one it is a high-level, interpreted, general-purpose programming language…
Q: Please solve all part 1. List and explain few data mining techniques to answer business questions.…
A: Introduction: In order to find patterns and associations that may be used to address business…
Q: The internet is regarded as a successful example of information and communications technology.…
A: Introduction: ICT is information and communication technology (ICT) ICT uses modern communication…
Q: Q.3 Write AVR instructions to MULTIPLY the content of the register R20 by 0.125. Since the…
A: Here is the explanation of the above problem. See below steps.
Q: In the U.S. fuel efficiency of cars is specified in miles per gallon (mpg). In Europe it is often…
A:
Q: To answer this question, let's first consider why it makes sense to move away from using servers…
A: Using the infrastructure as a service (Ia As) deployment paradigm, charity management maintains the…
Q: Given the following sorted list of numbers: [ -5, -2, -1, 0, 3, 6, 12, 13, 14, 23, 30 ] Explain…
A: Explain the process for performing a Binary Search for the key -5. You must state the low, mid and…
Q: Based on Amdahl's law, with multi-core and parallel computing capability, the maximum speedup is…
A: Dear Student, The answer to your question is given below -
Q: Question Analyse the following demand information and use a chase production strategy and a level…
A: Given: Analyse the following demand information and use a chase production strategy and a level…
Q: 6. You have received the following 7+4 bit Hamming encoded messages (the Hamming bits are…
A: Definition: In 1950, Hamming introduced the [7,4] Hamming code. It encodes four data bits into seven…
Q: Create a General Tree with an insert function. You have to code your own tree. Test the tree by…
A: Introduction: A non-linear data structure called a tree organizes data elements according to their…
Q: The goal of the algorithm is to maximise the sum of the contiguous subarrays
A: introduction; The goal of the algorithm is to maximize the sum of the contiguous subarrays.
Q: Please explain the major flaws of a two-tiered system. How about a multi-tiered client-server…
A: What is the primary drawback of a two-tier architecture? A multitier client-server approach would be…
Q: When it comes to cloud computing, what are some of the pros and cons of having users all over the…
A: Cloud computing enables enterprises to provide clients with storage, database, networking, and…
Q: When and why do we employ the Binomial, Poisson, and Proportional models of regression?
A: Regression is defined as the statistical technique which is relating to a dependent variable of one…
Q: Write a C# program that passes by reference a literal to a subprogram, which attempts to change the…
A: Here is how the program works:- An array consisting of values from 0 to 10 is defined. Further,…
Q: Regarding computer architecture, could you differentiate between the Harvard and von Neumann…
A: Architecture of computers: Computer architectures depict the connections between a computer's…
Q: List and discuss the many methods of online communication, as well as their relative advantages and…
A: Online communication is one of the cutting-edge methods of communication. Online communication…
Q: Provide some concrete examples to clarify the idea of a real-time operating system. Is there…
A: Introduction: Real-time operating systems (RTOS) provide real-time applications specific…
Q: What is one reason why the lack of “typical” security incident information is a barrier to improving…
A: Take a people-centric approach to security.Peoplecan be your biggest security risk or your strongest…
Q: In what ways are all Agile frameworks similar? Please enter your information and then hit the…
A: Introduction: The agile approach is a common strategy that promotes the use of continuous iteration…
Q: Type Direct Mapped Two-way Set Associative Four-way Set Associative Fully Associative Tag Index/Set…
A: SOLUTION- Given, => 32-bit computer =>byte addressable memory =>Number of blocks in the…
Q: Write a program in LC-3 that subtract two numbers from the keyboard and prints the results to the…
A: Start. Load the numbers on register. Subtract them. Print the result. End.
Q: What is SOA? How does it operate?
A: The problem stems from the service-oriented design that is used in the process of developing…
Q: Think you can remember the difference between active and passive transformations from a few quick…
A: Either an active or a passive change may take place:It is possible for an active transformation to…
Q: What is a typical Web application?
A: Introduction In this question we are asked about the web application
Q: QUESTION 4: Consider the following graph. Starting from vertex a, what is the result of? (a)…
A: BFS- A vertex-based method for locating the shortest path in a graph is called breadth-first search.…
Q: Explain Principles, Merits and Demerits of Time of Flight (TOF) separation. Please answer at your…
A: Introduction: In many different contexts, time-of-flight mass analyzers provide considerable…
Q: The formal communication system of a company should be described. In what ways does the…
A: Introduction: A formal communication network is built by executives and shown with a hierarchical…
Q: Given Triangle struct (in files Triangle.h and Triangle.c), complete main() to read and set the base…
A: Solution: I have solve the problem in C++ code with comments and screenshot for easy…
Q: Define semaphores in Ada and use them to provide both cooperation and competition synchronization in…
A: Semaphore is defined as the technique to manage the concurrent process by using simple integer…
Q: PYTHON PROGRAMMING Create 2 simple programs that uses: if, else, and for loop. note: don't…
A: Introduction: The use of the else statement has been restricted due to the if conditional…
Q: Users are able to interact with computers through the use of input devices. Reply:
A: Input Device definition Any hardware that connects a user to a computer is referred to as an input…
Q: What are the many facets of a network's ability to communicate effectively that may be impacted by a…
A: Dear Student, The answer to your question is given below -
Q: PLAIN TEXT: ALIVE KEY: YOU CIPHER SYSTEM: VIGENERE The resulting cipher text is
A: #include<stdio.h>#include<string.h>int main(){ char mat[27][27],str[29],key[29];…
Q: Can you distinguish between the most significant and least significant bits?
A: In this question we need to explain the differences between Most Significant Bit (MSB) and Least…
Q: Exactly what is meant by the phrase "operating system"? What are the OS's two most important roles?
A: Solution: Given, what is meant by the phrase "operating system"? What are the OS's two most…
Q: Explain what virtualization is and how it works in the context of cloud computing
A: An "Cloud" which refers to servers that are accessing over the Internet, and the software databases…
Q: Identify Many of the most disastrous software crashes in the annals of computing have identifiable…
A: IMPORTANT SOFTWARE BREACHES: Some of the most noteworthy software failures in computer science…
Q: How does a web application come to have so many components?
A: Let's see the answer:
Q: Describe one specific application of virtual servers in the classroom.
A: Virtual server In contrast to dedicated servers, a virtual server shares hardware and software…
Q: Is it possible to utilize the internet in such a way that it would be to the individual's advantage…
A: Patients' knowledge of, competency with, and engagement in health decision-making processes can all…
Q: What do the a) processing unit and b) programme counter do in the von Neumann paradigm?
A: The notion of the stored-program computer, in which instruction data and program data are kept in…
Q: Can you explain the distinction between network architecture and application architecture?
A: These question answer is as follows,
Q: “You search information on internet to become informed” – this statement relates to which…
A: The solution is given in the next step with explanation
Q: Main (Required) In addition to the above classes, students will have a sudoku.py file, where the…
A: def drawlines(): for i in range (9): for j in range (9): if defaultgrid[i][j]!=…
Q: Many individuals use programming languages to create software for usage on the internet. Give…
A: Programming languages are the languages which are used to interact with the computer and these…
Q: What kind of governance concerns should be taken into account when moving from in-house servers to…
A: Introduction: The charity administration maintains the infrastructure of the charity information. We…
Q: ISO 9126 is the superior standard when compared to competing standards.
A: McCall's Quality Model vs ISO 9126 Quality Model Comparison Given that both the ISO 9126 Quality…
Q: Explain the functionality of the boots using only bullet points.
A: How the computer boots: When a computer is switched on, the booting startup grouping starts the…
Computer Science help
Step by step
Solved in 2 steps

- Answer in your words , no plagiarism please. I will downvote. Thankyou . Generalization is the relationship between a superclass and one or more subclasses.The superclass is more general and it holds common attributes, operations and associations. Whereas the subclass is more specific. It uses the common attributes, operations and association of superclass but adds its specific attributes, operations and associations.Generalization is also called as is-a relationship. This is because, each instance of subclass is an instance of the superclass.Generalization relationship can be represented using an arrow having hollow arrowhead. The arrowhead points to the superclass. Explain the use of Generalization.Question 30 Which of the following description is TRUE? Inheritance allows us to define a class based on another class. Child classes receive all the features from the parent class but can NOT have their own additional features. Abstraction means that a method in a parent class can have a number of different implementations in child classes. An interface is a completely abstract class, which contains abstract properties, methods, and variables. The private access modifier makes members accessible only from within the class and hides them from the outside.QUESTION 8 Which of the following statements is wrong about inheritance? A. The inheriting class is called a subclass B. Inheritance is one of the features of OOP C. Protected members of a class can be inherited D. Private members of a class can be inherited and accessed
- What is a delegate object? Group of answer choices 1. It is a way to unit test your code, by delegating certain tests to one object, and other tests to another. This makes each test clear and puts all related tests in a single object. 2. It’s a way to reuse code through composition. We delegate certain responsibilities to an object that can handle those responsibilities. 3. It’s a way to reuse code through inheritance. The parent class is the delegate object because the child delegates certain responsibilities to the parent class by using the inherited methods without overriding. 4. A delegate object is when you create multiple instances of the same class. One object is created for certain purposes, while the other is delegated to take care of similar purposes. While both objects are from the same class they have different specific purposes.Which of the following are not true about inheritance? (Multiple choice can be selected) A It is the pillar of the OOP paradigm that states that a class' variables and methods can be duplicated by its child classes by inheriting them. B It is done to avoid duplication of codes. C It is used to conceal the implementation of codes. D It is used to protect the integrity of data. E None of the other choices are correct.C++ please help me answer this question I will give you a good rating Thank you! Choose the correct answer to the question. A derived class... a. Can contain more attributes (data members) and behaviors (methods) than its base class. b. Can be the base class for other derived classes.c. Object can access all data members with the dot operator. d. Object can be assigned to a reference of the base class. a, b only.a,b,d only.All of the above. Choose the correct answer to the question. Which of the following can be changed when overloading an operator? The precedence of the operator.The associativity of the operatorThe arity (number of operands) of the operator. All of the aboveNone of the above
- C++ please help me answer this question I will give you a good rating Thank you! 1. True or False? Explain your answer. Explain why? _____ Two classes that exist in the same program can have functions with the same name or variables with the same name. Explain your answer above. Explain why? _____ When using inheritance, the derived objects are constructed first and the base class object at the top of the hierarchy is constructed last. True False _____ Default constructors are inherited from the base class, thereby eliminating the need for derived classes to define their own default constructors. _____The extraction operator>> and the insertion operator<< returns a istream and ostream reference respectively so that input and output operations can be chained. _____ Once a constructor is used for an individual object, you cannot use a constructor with that object again. True False 19. Explain your answer above. Explain why?JAVA PROGRAMMING (TRUE OR FALSE) No further explaination needed. Classes in the java·lang package may be used directly if they are imported first using an import statement(True/False) The fields and methods of a child/sub class are only those inherited from the parent/super class.(True/False) A reference/object of super class type can hold/assume any object of its sub class type.(True/False) An import statement is necessary to use/access a classin the same package.(True/False) A private data field is accessible only by other classes via the exposed methods of its class.(True/False)Part-2 (Encapsulation, Inheritance, Polymorphism) ____________________________________________________________________________ Create a Java project that demonstrates various object oriented concepts you have learned so far in this course (encapsulation, inheritance and polymorphism). To do this, create a super class and at least 2 subclasses. You can either do multilevel inheritance or hierarchical inheritance in this to complete this part-2 task. The super class will have following properties/functionalities:a) Create a total of 3 member variables for the class, selecting the appropriate data types for each field. b) Include an argument constructor in this Class, that will initialize all data fields. c) Encapsulate this Class.The two subclasses will have below properties/functionalities:a) One of the subclasses will have at least one member variable and other subclass with at least two member variables. b) Have two constructors in each subclass:• One constructor for initializing only…
- Part-2 (Encapsulation, Inheritance, Polymorphism) Create a Java project that demonstrates various object oriented concepts you have learned so far in this course (encapsulation, inheritance and polymorphism). To do this, create a super class and at least 2 subclasses. You can either do multilevel inheritance or hierarchical inheritance in this to complete this part-2 task. The super class will have following properties/functionalities: a) Create a total of 3 member variables for the class, selecting the appropriate data types for each field. b) Include an argument constructor in this Class, that will initialize all data fields. c) Encapsulate this Class. The two subclasses will have below properties/functionalities: a) One of the subclasses will have at least one member variable and other subclass with at least two member variables. b) Have two constructors in each subclass: • One constructor for initializing only super class data • Another constructor will initialize both super and…Create a Java project that demonstrates various object oriented concepts you have learned so far in this course (encapsulation, inheritance and polymorphism). To do this, create a super class and at least 2 subclasses. You can either do multilevel inheritance or hierarchical inheritance in this to complete this part-2 task. The super class will have following properties/functionalities: a) Create a total of 3 member variables for the class, selecting the appropriate data types for each field. b) Include an argument constructor in this Class, that will initialize all data fields. c) Encapsulate this Class. The two subclasses will have the below properties/functionalities: a) One of the subclasses will have at least one member variable and other subclass with at least two member variables. b) Have two constructors in each subclass: • One constructor for initializing only super class data • Another constructor will initialize both super and subclass data. c) Encapsulate the…1)In the C++ code segment below, which of the following are valid reasons for making vUnit a member of myClass2? class myClass1 { //other details omitted}; Class myClass2 { myClass1 vUnit; //other details omitted}; A)It allows for polymorphism. It models a has-a relationship in myClass2 to myClass1. B)It uses less memory that inheritance. C)It is a short-hand notation for inheritance. D)It gives myClass2 faster access to myClass1 than could be achieved via inheritance. 2)which of the following represent valid use cases of the ANSI C register storage class specifier? A)A for loop in which the loop index is declared in the initialization. B)A short int inside a block which will be passed by pointer to another function. C)An unsigned short defined inside a function combined with other quantities as a bitmask. D)A parameter list of an external function declared in a header file. E)A char array declare at file…

