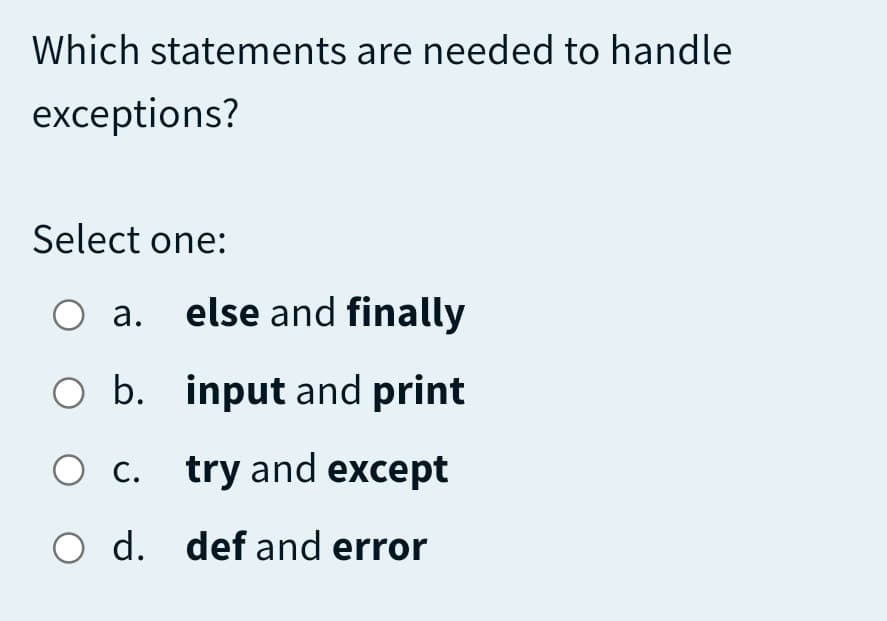
Which statements are needed to handle exceptions?
Q: What are some of the most prevalent sorts of error messages, and what do they indicate
A: "401 Unauthorized" First on our rundown of HTTP mistake codes is 401. A 401 message implies the serv...
Q: . Why Cyclomatic Complexity is used? Draw the flow graph and calculate the cyclomatic complexity for...
A: Cyclomatic complexity is a software metric used to measure the complexity of a program. Thomas J. Mc...
Q: write a JAVA program to input a positive integer from the user and print true in the output if the n...
A: - We need to code for the number program with digits and palindrome functionality. - We have to use ...
Q: Explain various types of addresses supported in IPv6 with their reserved bits.
A: A small part of the monstrous IPv6 address space has been set aside for special addresses.
Q: Simplify the following Boolean expressions to a minimum number of literals: (a + b+ c')(a'b' + c) (a...
A:
Q: Explain the advantages and disadvantages of each of the following firewall deployment scenarios in t...
A: 1 At the network's edge, there's a firewall. Advantages 1. Speed Each millisecond in an organization...
Q: A prime number is a number that is only evenly divisible by itself and 1. For example, the number 5...
A: The pseudo code (not any specific programming language) is given in the next steps
Q: void delFront(); // Remove the "next" item from the heap, however "next" // is defined... in this as...
A: Since we don't have Heap that it implements, we will write a complete solution for deletion on a min...
Q: Assume the designer of an online banking system created a secret function that gives him account inf...
A: Intro Due to the fact that the application was disguised and triggered only when the account balance...
Q: Write down the MATLAB expressions that will correctly compute the following: a. cot(t) 2 b.sec (t) +...
A: Answer the above questions are as follows:
Q: Question 3 The order-of-growth performance of most typical algorithms can be described by a small se...
A: Solution: The order of the growth of the running time of the algorithm gives the efficiency of the a...
Q: State a non-linear classifier that performs no worse than the linear classifier
A: Linear classifiers misclassify the area, while a nonlinear classifier like kNN will be highly exact ...
Q: In what capacity does a router function?
A: Capacity: A home router might theoretically have 254 devices connected to it. This is due to the IP ...
Q: services for many customers to order many products from anies. All Customers, products and companies...
A: Lets see the solution.
Q: What are the ideal QoS settings for real-time network traffic-generating applications?
A: Intro QoS stands for quality of service. QoS refers to technology that work on a network by managing...
Q: A - np. array ( (1, 2, 31, (4, 5, 6), [7, 8, 9] B - np.array ( (1, 2, 31, [4, 5, 61, [7, 8, 91 1) C ...
A: flow chart for 3D array
Q: Programto compute the average of seven degree, and d if the student success, then print "pass" word,...
A: Here assume that if average is greater than or equal to 35, student is assumed to be pass. If averag...
Q: Is it possible to buy software? If so, what are the various methods of obtaining software?
A: Introduction: A corporation may either create or buy software. In certain circumstances, acquired s...
Q: at is the normal relationship between an untrusted network, a firewall, and a trusted network, and h...
A: Lets see the solution.
Q: MACHINE LEARNING QUESTION: What are the main motivations for dimensionality reduction and what are ...
A: NOTE :- Below i explain the answer in my own words by which you understand it well.
Q: What is open source software and how does it differ from proprietary software? What is the differenc...
A: Proprietary software is software that is owned by the person or firm who created it. The term "open ...
Q: Discuss the major differences between symmetric-key and public-key systems in terms of encryption, a...
A: Introduction: To encrypt and decode an encrypted email, symmetric encryption needs a private key. Th...
Q: What exactly is Assembler?
A: Introduction: Assembler: An assembler is a type of computer program that interprets software program...
Q: In javascript define a function that takes a numeric argument, increments that argument, and then re...
A: We need to create a Javascript function that takes a numeric argument and increments that value. The...
Q: What type of sci-fi programme should be created that will appeal to both male and female audiences b...
A: Introduction SciFi shows create a lot of buzz among the generation which connects to scientific pri...
Q: 4: Write C++ program to find the sum of all integer between 100 and 200 which are divisible by 9.
A: The answer of this question is as follows:
Q: What is the definition of hand tracing?
A: Introduction Hand tracing: In the hand tracing the program is debug on pen and paper. There is no ...
Q: What role does the MAC address play in a TLS exchange utilising the change cypher specification?
A: Introduction What role does the MAC address play in a TLS exchange utilizing the change cipher spe...
Q: Given the below graph data, implement a python program for the following steps. Import this graph to...
A: By considering the graph data, the solution for this is
Q: Linux Bulid System: If I create a makefile target like this, list the targets that will be built in...
A: let us see the answer: Introduction:- A makefile is a set of instructions used to guide makepp on ho...
Q: Make a mental image of a virtual machine.
A: Intro EXPLANATION : VIRTUAL MACHINE: A software-based system with its operating system on a host se...
Q: Select all of true statements about the interface of merge (the main helper of the mergesort algorit...
A: _merger is a helper function of mergesort algorithm so lets check given statements are true of false...
Q: write a JAVA program to input a positive integer from the user and print true in the output if the n...
A: Write a JAVA program to input a positive integer from the user and print true in the output if the n...
Q: Was there anything in the field of computer science that could be done to avoid unethical and crimin...
A: Cybercriminals are individuals of people who use technology to commit malicious activities on digita...
Q: When it comes to iOS, what is the difference between the IPA and.am extensions?
A: In this question we have to discuss about the IPA and .am extensions First we will look into what bo...
Q: Create a programme to compute the sum of the numbers from 5 to 15.
A: Introduction Create a program to compute the sum of the numbers from 5 to 15.
Q: Suppose the two prime numbers p = 23 and q = 37 are used for an RSA encryption scheme. What are the ...
A: Below is the answer to above question. I hope this will meet your requirements...
Q: Write a C++ program to take an array of ints, print true if the sequence of numbers 1, 2, 3 appears ...
A: Required:- Write a C++ program to take an array of ints, print true if the sequence of numbers 1, 2,...
Q: I have a code for an assignment, but the code isn't working please help me. The code of the resourc...
A: The exception shown in the picture occurs when we try to access the file which is not available in t...
Q: Write the pseudocode for two modules which could be incorporated into the application planned for Lu...
A: # defining the first moduledef module1(): # declaring the lists to store the description and ...
Q: For this exercise you are going to write a program that will allow you to accept and load different ...
A: import csv from datetime import datetime from matplotlib import pyplot as plt def get_weather_data(f...
Q: What are the main procedures you should take if you want the computer to search for operating system...
A: Introduction: The process of a computer's operating system starting when it is switched on is known ...
Q: Consider the following array: int[] a = { 1, 2, 3, 4, 5, 4, 3, 2, 1, 0 }; What are the contents of ...
A: 1) We have an array a initialize with values { 1, 2, 3, 4, 5, 4, 3, 2, 1, 0 }; 2) Now have for loo...
Q: So, what is the distinction between a static and a dynamic website?
A: Intro Dear student we need to explain about what is exactly difference between a static and a dynami...
Q: How to setup and code google cloud speech api into java
A: The answer is
Q: Give two advantages of using virtualization as a networking technique on a network.
A: Intro Give two advantages of using virtualization as a networking technique on a network.
Q: A six-person project team has how many separate communication channels? How many more channels of...
A: Intro The communication channel specifies the way to flow the information between people in a proje...
Q: When should a network designer use static or dynamic VLAN?
A: Introduction When should a network designer utilize static VLAN and dynamic VLAN?
Q: Home:Woark Programtocompute the average of seven degree, and if the student success, then print "pas...
A: Hello student Greetings Hope you are doing great Thank You!!!
Q: please fast answer
A: ANSWER ANS 1. The er 1 and er 2 is given below :-
Step by step
Solved in 2 steps

- Which of the following statements are true? A) When you open a file for reading, if the file does not exist, an error occurs. B) When you open a file for writing, if the file does not exist, a new file is created. C) When you open a file for reading, if the file does not exist, the program will open an empty file. D) When you open a file for writing, if the file exists, the existing file is overwritten with the new file. E) When you open a file for writing, if the file does not exist, an error occurs. ======================================================================================= A, B, and D only A, and E B, and D only A and B onlyC++ Complete printmessage.cpp which uses escape sequences to print the following message on the screen. output: "Several backslashes are sometimes seen," Said Sally. "I've said so." See? \/\\//\\\///Write a few statements that open a file called "words" and writes the last word in the file to a file called "lastword".
- In Python, which of the following opens read_it.txt for writing or reading data text_file variable. a. text_file = open("read_it.txt", "wr") b. text_file = open("read_it.txt", "rw") c. text_file = open("read_it.txt", "aw") d. text_file = open("read_it.txt", "w+") which one is correct?Create a program that run again and again and if the user enter 0 it is ended? Use C++Write the negation of each statement.a. The processor is fast but the printer is slow.b. The processor is fast or else the printer is slow.c. If the processor is fast, then the printer is slow.d. Either the processor is fast and the printer is slow, or else the file is damaged.e. If the file is not damaged and the processor is fast, then the printer is slow.f. The printer is slow only if the file is damaged.
- In Python, which of the following opens read_it.txt for reading in data text_file varible. a. text_file = open("read_it.txt", "r") b. text_file = open("read_it.txt", "w") c. text_file = open("read_it.txt", "a") d. text_file = open("read_it.txt", "rd") which one is correct?What will be output to the screen when the following code is executed:def PrintMe(x): try: return s * 5 except: print("Error has occured") finally: print("Doing some cleanup")The following code contains which kind of error? system.out.println("What "Character" does this // print?") a. Runtime error b. Logic error c. Spelling error d. Syntax error
- Which of the following statements is correct? Application software includes operating systems such as Windows, Linux, UNIX, and Mac OS.193. Which of the following does not affects the execution of the program? a. Arguments b. Environment c. Control d. I/oIn python, which of the following opens read_it.txt for appending or reading in data test_file variable. a. text_file = open("read_it.txt", "ar") b. text_file = open("read_it.txt", "wr") c. text_file = open("read_it.txt", "a+") d. text_file = open("read_it.txt", "ra") Which one is correct? help!





