why output is exit status 1?
Q: What exactly is the purpose of wireless networks in 3rd world countries? If wired LANs and cabling…
A: Networks don't always utilise cabling. Wireless networks, which link networking components by…
Q: A time diagram for Direct Memory Access (DMA) that synchronizes with the clock?
A: Memory on a computer: It is the location where information and methods for carrying out tasks are…
Q: What precisely are these things called triggers? Why is it vital to have them? In Access 2016, how…
A: Triggers are database management system objects that automatically respond to an event (such as data…
Q: Is it feasible to provide more explanation on the four primary advantages that continuous event…
A: Yes it's feasible to provide on the four primary advantages that continuous event simulation offers.
Q: The Traveling Salesman Problem in Paris - An Optimal Tour Considering a Multimodal Transportation…
A: A solid public transportation infrastructure is critical in the development of smart cities,…
Q: why can't output?
A: In this question we will code and check for the output which not working for you Let's code and…
Q: Fix the following method printEvenIndex so that it will print out the Integers at even indices of…
A: Algorithm of the code: 1. Instantiate an empty ArrayList called values2. Create an array of integers…
Q: Do not exceed three lines in length while writing your synopses for each of the following subjects:…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: The definition of inherited wealth has been unclear. Look at it in all its forms.
A: The ability of one class to inherit attributes and behaviours from another class is referred to as…
Q: Do you have a primary issue with regards to the development of software?
A: Software Development: The process of building software applications in computer science as a whole…
Q: ling the challe
A: Introduction: The main piece of software that controls a computer's hardware and software resources…
Q: EXPERIMENT: Watching the Image Loader using e global flags to enable a debugging feature Write all…
A: The experiment is about modifying the source code for Image Loader software to enable a debugging…
Q: List and discuss the pros and cons of the various online communication methods, keeping in mind how…
A: Globalization and the rise of business collaboration worldwide mean that online communication is no…
Q: Look at Linux's server features and costs, then compare them to those of the most popular…
A: Windows by Microsoft Portrayal: A collection of Microsoft's operating systems is known as Microsoft…
Q: For what reasons does Microsoft see Linux as a competitive threat in China and elsewhere? Where…
A: Introduction: Why does Microsoft think Linux threatens the global IT sector as a whole, not just in…
Q: The meaning of the word "transitive" What is the rule for converting tables from the second normal…
A: Let A -> B and B-> C are two functional dependencies, then A-> C is known as a transitive…
Q: Just how long it takes to complete an insertion sort depends on a variety of factors, including the…
A: Complete software testing: Software testers do testing after individually testing and integrating…
Q: What is the Big-O running time of the following section of code? for i=1 to 1000 for j = 1 to 2000…
A: This code contains nested loop. Outer loop runs 1000 times while the inner loop runs 2000 times for…
Q: Do you, as an analyst, have any experience with computer system design strategies?
A: What is a Good System Design Strategy? A system design approach in software engineering often refers…
Q: Write this in Java: (Geography: estimate areas) Use the GPS locations for Atlanta, Georgia; Orlando,…
A: Write this in Java: (Geography: estimate areas) Use the GPS locations for Atlanta, Georgia;Orlando,…
Q: Create an Algorithm to Test Semiregularity Input: a set S of nontransitive group G generators acting…
A: Dear Student, The required algorithm along with explanation is given below -
Q: In your perspective, what function, if any, might screencasting potentially play in the field of…
A: Screencasting has the potential to play a significant role in the field of technical writing by…
Q: can u show the graph with all the fuctions lines r showing ?
A: In this question we will plot all the function visible in the graph using python Let's code.
Q: When analyzing data sets, such as data for human heights or for human weights, a common step is to…
A: The question asks for a program to analyze data sets by normalizing the values. The goal is to read…
Q: Which of the three below employs "definite event simulation?"
A: Discrete event simulation (DES) is a technique used to represent real-world systems that may be…
Q: It is essential to do research on wireless network infrastructure in developing nations. Due to the…
A: Reduce the number of devices sharing your home Wi-Fi network.serves as a central point for…
Q: Exist within the realm of software engineering any subfields that you think may be interesting…
A: Introduction: The following are the primary categories of our research interests in the field of…
Q: Provide an explanation of the relationship between dependability and availability as it relates to…
A: Reliability indicates that the computer performs as intended. In a network, reliability is…
Q: What sets software engineering different from other technical specializations?
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: If we can assume that the keys in the list have been arranged in order (for example, numerical or…
A: The practical testing of the generated functions provides a suitable counterpoint to the theoretical…
Q: An Optimal Tour Considering a Multimodal Transportation System – The Traveling Salesman Problem…
A: The Traveling Salesman Problem (TSP) is a classic optimization problem where a salesperson wants to…
Q: There are three parts to the von Neumann architecture, and they should all be defined in depth. How…
A: From one gadget to the next, the fundamental elements and how they are seen are different. A…
Q: There are two major advantages of electronic mail over conventional mail for modern communication.…
A: Email isn't just for text messages. Any type of multimedia can be sent within mail, also helps in…
Q: There are a number of benefits to using electronic methods of communication. Did you know there were…
A: Communication through technological means may take many different forms. Every every day, the use of…
Q: The steps of digital forensics may be broken down into two categories: ad hoc and enterprise
A: Digital forensic phases: The Ad Hoc phase lacked structure, objectives, tools, processes, and…
Q: Are the following two IP addresses in the same subnet? Answer either 'yes' or 'no'.…
A: Given: Two IP addresses: 2001:69a0:75:60c9:6a10::1/64 2001:69A0:7500:60C9:632e:d456:3c95:72c2/64…
Q: Provide a brief background on the evolution of computing.
A: Introduction: The background of computers goes back 200 years. Mechanical computing devices were…
Q: Do you, as an analyst, have any experience with computer system design strategies?
A: A system analyst is a person who is thoroughly aware of the system and leads the system development…
Q: Consider above contingency table listing counts of Spam and NoSpam email with or without "Free" word…
A: - We have to work on the contingency table and find the probability.
Q: Assignment for Computer Architecture You are to write a program in MIPS that computes N! using a…
A: Introduction Computer Architecture:: computer Architecture refers to the fundamental design and…
Q: 4.11 LAB: Number pattern Write a recursive function called print_num_pattern() to output the…
A: Number pattern using recursive function using the python programming language see the below code
Q: Could two network interfaces theoretically have the same MAC address? Can you explain this? Is…
A: Introduction: When a computer connects to a network, whether it be public or private, this is known…
Q: How can cloud processing and storage enhance our lives?
A: Given: Cloud computing is the process of storing and accessing data and computer resources through…
Q: The three components that make up a computer's von Neumann architecture. A wide range of…
A: Neumann Architecture is characterised by the fact that the key components, as well as the visibility…
Q: Windows 8 improves upon earlier versions when used on a gaming PC with integrated video and a free…
A: Introduction: A graphics card, also known as a video card, display card, graphics adapter, or…
Q: Easter Sunday is the first Sunday after the first full moon of spring. To compute the date, you can…
A: The JAVA code is given below with output screenshot
Q: When it comes to efficient communication, is today's technology being used to its fullest potential?
A: Introduction Efficient communication is the ability to clearly and quickly convey information from…
Q: Is it your opinion that the effect of good customer service on repeat business makes organizations…
A: Client Retention: In marketing, customer retention is the act of persuading current consumers to…
Q: When two machines on the same network have the same MAC address, what should you do? Totally…
A: Is it possible for two computers to have a MAC address conflict?Yes, it is possible. One of the…
Q: Suppose we are performing a binary search on a sorted vector initialized as follows: // index Ø 1…
A: Given: vector <int> numbers (-5, -1,0, 3, 9, 14, 19, 24, 33, 41, 56, 62, 70, 88, 99);int index…
why output is exit status 1?
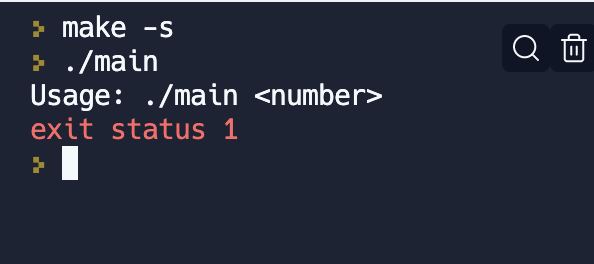
Step by step
Solved in 3 steps with 4 images

- rvalue expression identifies a non-temporary object, points to a specific memory location and lives a longer life. true or falseGive Authentic And Relevant Answer. Write a detail use case for “Search a Cab” function. For searching a cab, the passenger would enter his/her source and destination information and the application would list down all the available cabs in a 1km radius. If application unable to find cab within 1km radius passenger can increase the radius up to 3 km. The passenger would send pickup request to the driver and the driver would come to pick the passenger from the source address. ‘Get a Cab’ is a Smartphone application. It will search cabs for the passenger, provide them with security by reminding them about their luggage and it will also allow the user to inform the police with the help of a one-click button. This application facilitates the guardians to trace the location of their loved ones. It also lets passengers locate a driver at any instance to overcome all time related issues. If the passenger wants to avail the services of the same driver in future, he/she can add the driver to…Cookie Calories A bag of cookies holds 40 cookies. The calorie information on the bag claims that there are 10 servings in the bag and that a serving equals 300 calories. Create an application that lets the user enter the number of cookies he or she actually ate and then reports the number of total calories consumed.
- When debugging an application, why would you not want to single-step throughevery procedure or function?C# (Login User Control) Create a UserControl called LoginPasswordUserControl that contains a Label (loginLabel) that displays string "Login:", a TextBox (loginTextBox), where the user inputs a login name, a Label (passwordLabel) that displays the string "Password:" and, finally, a TextBox (passwordTextBox), where a user inputs a password (set property PasswordChar to "*" in the TextBox’s Properties window). LoginPasswordUserControl must provide public read-only properties Login and Password that allow an app to retrieve the user input from loginTextBox and passwordTextBox. The UserControl must be exported to an app that displays the values input by the user in LoginPasswordUserControl.Most of the memory locations declared in an application should be class-level variables. a. True b. False
- Access keys are assigned in a control’s __________property. a. Access b. Caption c. Key d. TextTrue or False To close an application’s form in code, you use the statement Close.This();Program Description: PasswordGenerator.java You have to implement a program that creates three buttons to display the digits of a password a button to generate a password a button to reset the password Additional Requirements: The top three digit buttons are not interactive as they are only used to display numbers from 0 to 9. The text size of the buttons should be 30 pixels and font should be Arial. There should be 5 pixels distance between the buttons.
- In C++ language (OOP), Two different authorization levels... Create program When the program is started, there should be two different authorization levels: Admin and Customer. If admin logs in, "*" character must be entered. If the customer logs in, only enter should be pressed. Admin should have authority to update product information. A menu should be displayed for this. In the menu, the relevant operation should be performed by asking which operation admin wants to do. When the customer is log in, a special menu should be displayed for the customer. In this menu, there should be view cart, select category and log out options.Which concept in access control places restrictions on a user's access to the particular data that is necessary for him or her to complete the task that has been given to him or her?Book Club PointsSerendipity Booksellers has a book club that awards points to its customers based onthe number of books purchased each month. The points are awarded as follows:• If a customer purchases 0 books, he or she earns 0 points.• If a customer purchases 1 book, he or she earns 5 points.• If a customer purchases 2 books, he or she earns 15 points.• If a customer purchases 3 books, he or she earns 30 points.• If a customer purchases 4 or more books, he or she earns 60 points.Write a program that asks the user to enter the number of books that he or she haspurchased this month and then displays the number of points awarded.



