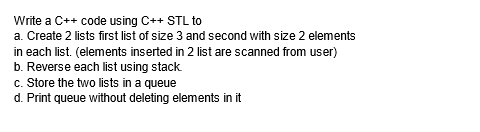
Write a C++ code using C++ STL to a. Create 2 lists first list of size 3 and second with size 2 elements in each list. (elements inserted in 2 list are scanned from user) b. Reverse each list using stack c. Store the two lists in a queue d. Print queue without deleting elements in it
Q: Who is familiar with Ada Lovelace's contributions to computer science?
A: Let's discuss who was Ada lovelace's and what was their contribution in Computer science.
Q: Which of the following are obstacles to the adoption of IoT?
A: The network of physical items, or "things," that are implanted with sensors, software, and other…
Q: Which part of a client/server architecture is responsible for storage?
A: The client-server architecture, architecture of a computer network in which many clients request and…
Q: ng HC19) What are the various phases of SDLC?
A: Software development Life Cycle is the use of standard strategic approaches to building programming…
Q: What advantages does MVC provide their firm in terms of web applications? How may the MVC…
A: Framework for web MVC: Requests are directed to handlers using a Dispatcher Servlet in the Spring…
Q: What governance factors should be taken into account while shifting from on-premises servers to an…
A: Introduction: The cause the board utilizes the sending model as an infrastructure as a software…
Q: What are the four fundamental capabilities of a computer system? employ an example to illustrate
A: The identifiability of a computer system is based on four primary characteristics.
Q: Operating system abstraction has several benefits. What are the most significant ones?
A: Introduction: The user and the hardware are connected through an operating system. Explanation: Some…
Q: How does MVC fit into the broader web application framework? What are the advantages of an MVC…
A: MVC is made up of three components: model, view, and controller. The Model component of the MVC, as…
Q: Exists a substantial drawback to a two-tier architecture? How can a client–server design with many…
A: Two-tier client-server architecture: The Client-Server concept is the basis for the two-tier…
Q: Is it necessary to emphasize the relevance of data backup and cloud storage in corporate…
A: Information is vital; after all, it describes everything from individual identities to financial…
Q: What advantages does MVC provide their firm in terms of web applications? How may the MVC…
A: Answer: What is MVCMVC, short for Model, View, and Controller, is a methodology or architectural…
Q: Discuss and evaluate at least five (5) unique data backup strategies, emphasizing their relative…
A: Introduction: Discuss backups and evaluate at least five different backup techniques, including each…
Q: Given the capability of contemporary computers, this is a difficult situation. How can we show that…
A: Computers have provided countless learning materials and increased the accessibility and flexibility…
Q: Compare and contrast secondary solid-state storage technologies with secondary magnetic storage…
A: Solid-State Storage : Data storage that uses integrated circuit devices rather than moving magnetic…
Q: Define XLAT instruction used in 8086.
A: Introduction: 8086 Microprocessor is an upgraded variant of 8085Microprocessor that was planned by…
Q: How does MVC fit into the broader web application framework? Which of the following are advantages…
A: Introduction Model, View, and Controller (MVC): This architectural design pattern divides an…
Q: Operating system abstraction has several benefits. What are the most significant ones?
A: The purpose of an operating system is to abstract hardware resources, such that the user may…
Q: Problem. Create a truth table for the expression p V ( q ^ ¬ r ), by filling in the indicated…
A: Answer: Here given three variable so total eight 8 combination are possible So we have create a…
Q: Define XLAT instruction used in 8086.
A: In 8086, 8 general purpose registers exist such as - AX (AH, AL) - Accumulator BX (BH, BL) - Used…
Q: Which are the most significant drawbacks of a two-tier system? What about a client–server design…
A: Client Tier and Database are the two layers that make up a two-tier architecture (Data Tier). It is…
Q: This is due to the fact that computers have gotten so advanced. How can we demonstrate that…
A: Beginning: Since their invention, computers have shown to be dependable, but they are also…
Q: What connects all Agile frameworks? Following that, click Submit. A set number of cycles…
A: Given: Work may be planned, managed, and carried out according to a certain methodology known as an…
Q: Write a class with name intlist. This class will have an integer array arr (for simplicity define it…
A: As language is not defined doing it in C++ programing language:
Q: What governance factors should be considered while shifting from on-premises servers to an IaaS…
A: When moving from servers hosted: On-premise to those hosted in an IaaS architecture, what are some…
Q: As a result of the brilliance of modern computers, Describe how computers have grown so prevalent in…
A: let us see the answer:- Introduction:-Development has long been a top priority in people's lives.…
Q: Provide a short explanation of each kernel component before listing the components.
A: An operating system's kernel is its beating heart. The OS exercises control over the computer system…
Q: What language is used to create PHP websites?
A: When creating websites, PHP is utilised with a variety of other languages.
Q: Describe the functionality of the boots using bullet points.
A: How the computer starts up: When a computer is turned on, a startup process known as booting begins…
Q: Flynn's taxonomy
A: Michael J. Flynn proposed Flynn's taxonomy, a classification of computer architectures, in 1966 and…
Q: What is Unpacked BCD Format?
A: BCD(binary coded decimal) Binary coded decimal or BCD is the system of writing the numerals that…
Q: Operating system abstraction has several benefits. What are the most significant ones?
A: The reasons why Operating system uses abstraction , are discusses as below.
Q: Which part of a client/server architecture is responsible for storage?
A: The answer is given below step.
Q: Which port is utilized to provide electricity to the Raspberry Pi
A: in the following section we will be discussing about the port utilized to provide electricity to the…
Q: Provide a list of bullet points describing the computer's boot procedure.
A: Introduction: A computer's operating system is launched during the booting process when it is…
Q: Write three functions to code for the following three sorting algorithms in C++. Make your own…
A: The C++ code is given below with code and output screenshot Happy to help ?
Q: A U-N flip-flip works as follows: If UN-00 the next state of the flip-flop is 1. UN 01 the next…
A: I have given complete solution in the below steps.
Q: Exist classroom or educational institution deployments of virtual servers?
A: We can see this as classroom learning and online learning. Exist classroom here is representing…
Q: What
A: Let's know about some special 10 capabilities of computer. Speed Accuracy Automation Versatility…
Q: How can I prevent being a victim of phishing?
A: Phishing attacks are some of the most common cybercrimes and frauds that impact many people…
Q: As a result of the brilliance of modern computers, Describe how computers have grown so prevalent in…
A: Introduction Computers are very powerful for a multitude of reasons. They operate with astonishing…
Q: What differences exist between time-sharing and distributed operating systems? In what ways do they…
A: OS: The computer is controlled by the operating system. An operating system makes user-computer…
Q: An example of c acode showing how nodes can be inserted at a doubly linked list, how the list can…
A: An example of code showing how nodes can be inserted at a doubly linked list, how the list can…
Q: What governance factors should be considered while shifting from on-premises servers to an laaS…
A: What governance considerations should be made when shifting from on-premise servers to an IaaS…
Q: Analyse, why many developing nations continue to face challenges in accessing humanitarianrelief,…
A: Answer:-
Q: Define XLAT instruction used in 8086.
A: Define XLAT instruction used in 8086 answer in below step.
Q: Which port is utilized to provide electricity to the Raspberry Pi? Is it an HDMI port, a Macro USB…
A: Answer:-
Q: If the sequence number space is k bits long, the Go-Back-N and selective-repeat algorithms should be…
A: Data is given by :- The Number of bit use for sequence number = k bits Protocols used : 1)…
Q: What is Distributed Training Orchestrator Pattern?The pattern is composed of which building blocks?
A: The distributed training orchestrator pattern automates the process of model train‐ ing. The goal is…
Q: How do network architecture and application architecture differ?
A: The phrase "network architecture" refers to the process of communication being segmented into…
Step by step
Solved in 4 steps with 4 images

- Write a program in c++ and make sure it works, that reads a list of students (first names only) from a file. It is possible for the names to be in unsorted order in the file but they have to be placed in sorted order within the linked list.The program should use a doubly linked list.Each node in the doubly linked list should have the student’s name, a pointer to the next student, and a pointer to the previous student. Here is a sample visual. The head points to the beginning of the list. The tail points to the end of the list. When inserting consider all the following conditions:if(!head){ //no other nodes}else if (strcmp(data, head->name)<0){ //smaller than head}else if (strcmp(data, tail->name)>0){ //larger than tail}else{ //somewhere in the middle} When deleting a student consider all the following conditions:student may be at the head, the tail or in the middleBelow, you will find a sample of what the file looks like. Notice the names are in…Write a program where 2 linked lists have ben create and now the main task is to merge the linked lists and display the merged list. For example, merging lists {1, 2, 3} and {7, 13, 1} should yield {1, 7, 2, 13, 3, 1} Note: the above mentioned task is to be performed using doubly linked list and in C++Question : Write a program to remove duplicates from a doubly linked list. e.g (1,2,3,4,5,2) (you will remove the 2nd duplicate) and then swap two data items in a doubly linked list. swap address of node 2 with node 4.
- write a c++ code that will do the adding a node to a doubly-linked list in the three cases (insert a node at the beginning-middle-end). A separate function is required for each case.python programming Write a function that will insert a new value into the middle of a Linked List. INPUT: The head of the Linked List, the value to insert OUTPUT: Nothing is output RETURNED: Nothing is returnedQuestion : Write a c++ program which creates a Linked List having maximum sum out of two Sorted Linked Lists. Use this : LinkedList finalMaxSumList(LinkedList List1, LinkedList List2); For eg: You have two sorted linked lists, create a linked list that contains data with maximum sum. The resulting list with maximum sum will contain nodes with data from both input sorted lists. While creating the resulting list with maximum sum, we may switch to the other input list only at the point of intersection (which mean the two nodes with the same value in the lists). You are only allowed to use O(1) extra space. Note: You have to returned Linked List which contain finalMaxSumList and you are not allowed to change in data type and prototype of the Function. Input:List1 = 1->3->30->90->120->240->511List2 = 0->3->12->32->90->125->240->249 Returned LinkedList: Following is resulting linked list out of two sorted listsResultingList =…
- Task:implement a function that reverses a list of elements by pushing them onto a stack in one order and writing them back to the list in reversed order P.S:Answer must be in pythonIn C++, how do I read a file with numbers Such as 1,2 3,4 5,6 and place it into a linked list with x,y values Without stringstream or sstream and vectorsfor C++ how do you cosntruct a stack using a linked list?
- Write a program in c++ to remove duplication if exists in the linked list. Write 2 separate functions to perform search and other to perform the duplication removal. Note: the above mentioned task is to be performed using singly linked list and in c++In SML write a function posLL to count a number of positive values in an int list list. One function only. posLL[nil,[~2,3], [5], [~7,11]] > 3Which of the following statement is not true about the doubly linked list? A. We can traverse in both the directions. B. It requires extra space C. Implementation of doubly linked list is easier than the singly linked list D. It stores the addresses of the next and the previous node

