Write a C program that asked the user to enter an integer MAX where 101000. The program then produces the following table of y=x/n where x=1 ..MAX; n=1 ..5 TABLE OF DIVISION 1 | 1 3 4 | Y.yyy | 2 | Y.yyy | Y.yyy | | Y.yyy | | | MAX | Y.yyy 2 | 3 Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Note: Y.yyy are values of y=x/n displayed with 3 decimals. 4 | 5 | Y.yyy | Y.yyy Y.yyy | Y.yyy Y.yyy | Y.yyy | Y.yyy Y.yyy Y.yyy | Y.yyy
Write a C program that asked the user to enter an integer MAX where 101000. The program then produces the following table of y=x/n where x=1 ..MAX; n=1 ..5 TABLE OF DIVISION 1 | 1 3 4 | Y.yyy | 2 | Y.yyy | Y.yyy | | Y.yyy | | | MAX | Y.yyy 2 | 3 Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Y.yyy | Note: Y.yyy are values of y=x/n displayed with 3 decimals. 4 | 5 | Y.yyy | Y.yyy Y.yyy | Y.yyy Y.yyy | Y.yyy | Y.yyy Y.yyy Y.yyy | Y.yyy
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter6: Arrays
Section: Chapter Questions
Problem 7RQ
Related questions
Question
100%
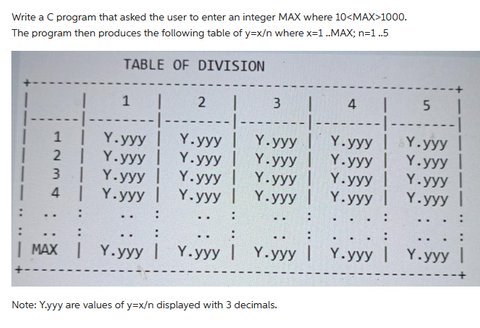
Transcribed Image Text:Write a C program that asked the user to enter an integer MAX where 10<MAX>1000.
The program then produces the following table of y=x/n where x=1 ..MAX; n=1 ..5
TABLE OF DIVISION
1 |
1
| Y.yyy |
2 | Y.yyy |
| Y.yyy |
4 | Y.yyy |
3
| MAX | Y.yyy
2 | 3
Y.yyy |
Y.yyy |
Y.yyy |
Y.yyy |
Y.yyy |
Y.yyy |
Y.yyy |
Y.yyy |
Y.yyy |
Y.yyy |
Note: Y.yyy are values of y=x/n displayed with 3 decimals.
4 | 5 |
Y.yyy | Y.yyy
Y.yyy |
Y.yyy
Y.yyy |
Y.yyy |
Y.yyy
Y.yyy
Y.yyy | Y.yyy
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT