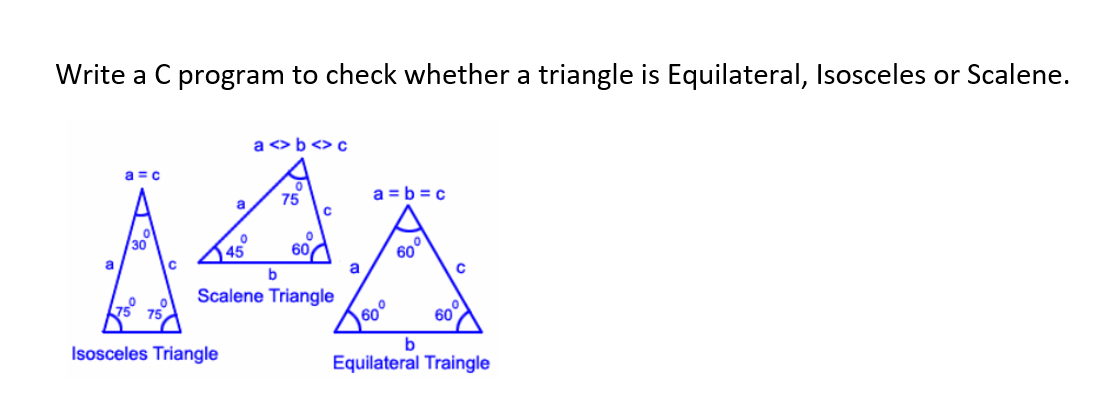
Write a C program to check whether a triangle is Equilateral, Isosceles or Scalene. a <> b <> c a = c 75 a = b =c a 30 45 60A 60 a b a Scalene Triangle 60 75 75 60° Isosceles Triangle b Equilateral Traingle
Q: Examine the two schools of thinking when it comes to the definition of "information technology."…
A: Data:- An information system is a collection of interconnected components that gather, store, and…
Q: (c) The process of fetching the next instruction when the present instruction is being executed is…
A: There are two ways to boost a CPU's performance:1) Introduce quicker circuits into the hardware.2)…
Q: Discuss the usage of tablet computers and smartphones for business purposes.
A: Introduction: Here we are required to explain the usage of tablet computers and smartphones for…
Q: 2b Illustrate the differences between CISC and RISC with an example and how they relate to…
A: The Answer is in given below steps
Q: How do you keep an office with shared resources, such as a printer and other PCs, safe while using…
A: Introduction: Shared resources are those that may be accessed by several computers connected through…
Q: What kinds of data structures are there?
A: INTRODUCTION: Data structures are ways of storing and arranging data in a computer system so that…
Q: Process Burst Time Arrival Time P1 12 P2 11 P3 13 10 P4 7 15 P5 14 20 P6 10 25 P7 8 30 P8 17 35 P9…
A: Find the required Gantt Chart and scheduling table for Round Robin given as below :
Q: Process Burst Time Arrival Time P1 12 P2 11 P3 13 10 P4 7 15 P5 14 20 P6 10 25 P7 8 30 P8 17 35
A: Note: Due to company policies I am compelled to solve only one question and that is the first…
Q: When do you think tacacs+ is a better option than RADIUS or Kerberos?
A: TACACS+ is more dependable than RADIUS or Kerberos as TACACS+ uses TCP. TACACS+ allows for…
Q: How can several systems share communication channels while avoiding signal collision?
A: Given: CSMA/CD is the progression of these older protocols with two new features added to CSMA. The…
Q: What is the value of numltems after the below code is executed? Iten jar new Iten(); Iten ball ne…
A: Here the variable numItems is a static variable. Thus it will be initialized only once and will be…
Q: In what ways are Firewall rules advantageous?
A: A firewall is a network security appliance that monitors and filters incoming and outgoing network…
Q: How do you maintain security while using shared resources like a printer?
A: Maintain security: Computer security, network security, or data innovation security (IT security) is…
Q: the mumber of otervations in the goups Car Milage Data
A: R Code------------------------ # Drawing the box plot (mtcars dataset, mpg and cyl)boxplot(mpg ~…
Q: Password assaults may take a variety of forms. System administrators need to know what they can do…
A: Empower encryption on your switch. In the event that your modem and switch can be gotten to by…
Q: Differentiate recognition versus recall, give a concrete scenario.
A:
Q: Write a program in python to get the lossing probability after taking the winning probability from…
A: The sum of probabilities of winning and loosing is 1 So here we use the same logic to find the…
Q: Many data centres have already migrated to cloud computing designs like Big Data Cluster.. According…
A: GIVEN: Many data centers have already begun to use cloud computing designs such as the Big Data…
Q: Explain how a company's information systems utilize databases, using any company as an example.
A: Improved data security and more significant data access are benefits of using a database in a…
Q: Enter the number of participants: 5 Enter their ages: 21 52 47 60 3 The following are the ages of…
A: Algorithm first declare the two variables of integer type. Ask the user to enter the total…
Q: (c) The process of fetching the next instruction when the present instruction is being executed is…
A: Solution:: The process of fetching the next instruction when the present instruction is being…
Q: #include using namespace std; int main() { int x = 1, n; cout>n; do { cout<<x<<"\t" <<x * x<<"\t"…
A: The do...while loop is a variant of the while loop with one important difference: the body of…
Q: What is the reason why ACK packets don't need to be sequentially numbered?
A: Given: We learned that the sender need sequence numbers so that the receiver can determine if a data…
Q: Big Data Cluster, a kind of cloud computing, is quickly overtaking all other types of data centre…
A: Capital expenditures (CAPEX) are not required: Significant data efforts demand massive investment in…
Q: For Big Data Clusters, cloud computing is already the most popular data centre infrastructure. Big…
A: Introduction: Big data refers to methods for analyzing, methodically extracting information from, or…
Q: Technology of information and communication How are server events categorised in Event Viewer?
A: Information and Communication Technology: When we talk about information and communication…
Q: Explain how information security policy and an information security strategy are related.
A: The most fundamental level is information security policy. The information security plan may be…
Q: Using a corporate data model has several advantages for Mercy. Mercy's considerable foray into big…
A: Data Model: The enterprise data model will benefit Mercy by streamlining the system and increasing…
Q: What are the many theories around cybercrime? Please offer references in response to this inquiry.
A: Despite being developed to describe crimes committed in the "real world," these concepts may…
Q: struct namerec{ char last[15]; char first[15]; char middle[15]; struct payrecord{ int id; struct…
A: Step 1 A struct is a user defined data type that contains variables of multiple data types. It is…
Q: How do cloud computing benefits stack up against those of on-premises computing systems? What are…
A: The solution to the given question is: An increased number of tasks can be handled without impacting…
Q: Considering the significance of networking in the field of information technology, should a paper be…
A: Given: Not only does it make it a simple for employees to exchange information, hence enhancing…
Q: nformative examples should be used to explain the foundations of information systems.
A: The goal of an information system is to convert raw data into meaningful information that can be…
Q: 2-Caches are important to providing a high-performance memory hierarchy to processors. Below is a…
A: Note mentioned weather memory is byte addressable or word addressable given address is word address…
Q: What are the distinctions between C++, assembler, and Python programming languages? To support your…
A: INTRODUCTION: Here we need to tell the differences between C++, assembler, and Python programming…
Q: #include using namespace std; int main() { int y, x=1, total =0; while (x <= 10) { y=x * x; cout <<…
A:
Q: Instructions for transferring the contents of the AX register to the BX register should be written…
A: Find the required instruction with explanation given as below :
Q: How should a company keep track of passwords?
A: INTRODUCTION The query is about how corporations manage password documentation, and the next step…
Q: Why would you want to use RAID 5? Which of the additional choices would be required if RAID 5 was to…
A: RAID 5: RAID 5 combines the best of both systems, allowing you to have high data throughput and…
Q: Define what the term "UNIX" means. What are the top five UNIX features, and how would you describe…
A:
Q: BootMgr is located on which partition? Is it on the system or boot partition?
A: Answer : There are two types of partitions in the hard drive. system partition and boot partition .…
Q: Which of the following statements is FALSE? The intricacy of time requires additional CPU cycles.…
A: The statement that space complexity necessitates less memory is incorrect in this case. The overall…
Q: Instructions for transferring the contents of the AX register to the BX register should be written…
A: Statement: In order to deal with diverse activities, each set of processors has its own arrangement…
Q: Suppose we could separate the class definitions and class implementation in two different files from…
A: The answer to the following question:-
Q: What advantages does having a separate hard drive for the paging file give the user?
A: Advantages of having separate hard drives for the paging files. Answer in Step 2
Q: Give an example of the learning process for a switch table with five nodes linked to a single switch…
A: In networking, make a switch: Switching is used in networking to forward packets and filter traffic.…
Q: Write a brief note about the output device?
A: In this question we have to discuss about the note about the output devices Let's understand
Q: How can several systems share communication channels while avoiding signal collision?
A: Definition: The progression of these older protocols, as well as the addition of two features to…
Q: System development methodology is defined in this section.
A: Software development is a lengthy and typical process and should be done with all procedures…
Step by step
Solved in 2 steps with 1 images

- Write a C# program to check whether the given number is armstrong number or not. Armstrong Number in C#: A positive number is called armstrong number if it is equal to the sum of cubes of its digits for example 0, 1, 153, 370, 371, 407 etc.write a program in C++ that A user needs to determine the size of squares (let say delta) in a grid, the center of the circle (does not have to lie on a grid but it can!) and the radius. (for example use "cin>>" ) Then you need to plot a circle using parametric equations of circle (you need to increase angle and plot these (in my picture black) points). First plot the first point of the circle and determine in which square of grid it is. (in my picture it is an orange square) and plot the left bottom vertex of this square (in my picture it is a blue point). Then increase an angle and plot next point of circle - check if it lies in different square. -If it is not in different square, you need to increase angle and check again. (because an angle was too small) -If it is the different square, then check, if this square has THE COMMON EDGE with the previous one -> if it has the common edge, then print new left bottom vertex of this square (if does not have common edge,…In C++, write a program that inputs three integers from the keyboard and prints the sum, average, product, smallest and largest of these numbers. The screen dialog should appear as follows: Input three different integers: 13 27 14 Sum is 54 Average is 18 Product is 4914 Smallest is 13 Largest is 27
- Write a C++ program that asks the user to enter the radius of the circle and then find the Circumference and area of the circle. Cir= 2* pi *R Area= pi*R*RWrite a program in C++ to print all those natural numbers whose cube is less than or equal to 1000.Write a C++ program that reads student scores, determines the best score, and assigns grades using the following scheme: If your score is 7 = best - 10, you'll get an A;if your score is 7 = best - 20, you'll get a B;if your score is 7 = best - 30, you'll get a C;if your score is 7 = best - 40, you'll get a D; and if your score is 7 = best - 40, you'll get an F. The program asks the user to enter the total number of students, then all of the scores, and finally displays the grades.
- In this c++ program you are asked to design a 2 x 2 x 2 Rubik's cube that is filled with numbers instead of colors. The cube, naturally, has six sides that are identified as follows: The front side is side 0 The right side is side 1 The backside side is side 2 The left side is side 3 The Up side is side 4 The bottom side is side 5 The squares on every side are initially filled with the same side index. This means that the four squares on the front side are filled with 0's, the four squares on the right side are filled with 1's, etc. You are allowed to move the cube in two directions only: Horizental move (H or h): The first row moves one step in four sides in this order (0 -> 1 -> 2 -> 3 -> 0) Vertical move (V or v): The left column moves one step in four sides in this order ( 0 -> 5 -> 2 -> 4 -> 0) The program accepts from the the user the number of moves he/she wants to make, accepts the sequence of desired moves as shown in the sample case below.…Write a C++ program to check whether the triangle is equilateral, isosceles or scalene triangle.(using c++ only)write a program in c++ Type equal to 'G', If classification is equal to 5 then set the character variable and print a message saying "graduate student"; otherwise set Type equal to 'U' and print a message saying "undergraduate" using for and dowhile loop
- Write a C++ program that accepts the rectangular coordinates of two points (x1,y1) and (x2,y2), calculates the distance of each point from the origin, and calculates the distance between two points.Write a c program that calculates the potential energy of 3 charges q1=1, q2=2, q3=3 located at points (1,2,3), (3,−4,−5), and (−4,2,−6) respectively. The units are coulombs forcharge and meters for coordinates. The energy is given by the expression; U=k(q1q2/r12+q2q3/r23+q1q3/r13) where rij is the distance between the charges qi and qj, and k= 9×109in SI units.Your program should print the result on the screen.Write a program that translates a letter grade into a number grade. Letter grades are A, B, C, D, and E, possibly followed by + or -. Their numeric values are 4, 3, 2, 1, and 0. There is no F+ or F-. A + increases the numeric value by O.3, a – decreases it by 0.3. However, an A+ has value 4.0. Enter a letter grade: B- The numeric value is 2.7. (in C++ language)

