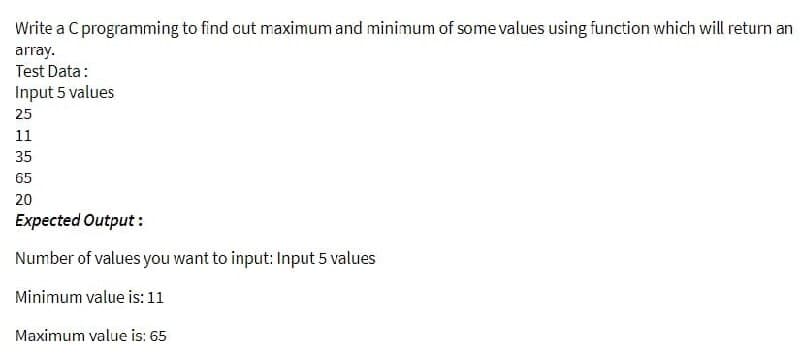
Write a C programming to find out maximum and minimum of some values using function which will return an array. Test Data: Input 5 values 25 11 35 65 20 Expected Output: Number of values you want to input: Input 5 values Minimum value is: 11 Maximum value is: 65
Q: AMMING OOP1 - Objects, Classes, and Encapsulation Create a program that has the following method…
A: Introduction: Below the C# program compute the area of the circle with Objects, Classes, and…
Q: The counting concept underpins the operation of a digital computer. why?
A: Introduction: A concise explanation of the logic that underpins the operation of a digital computer…
Q: It is common practice in wireless networks to make use of the following two types of technology: Ad…
A: Wireless networks are the networks which can connected with the wireless connectivity, and it is not…
Q: hat are a few of the key distinctions between PaaS and IaaS?
A: PaaS stands for Platform as a Service. It is a cloud delivery model used in applications that are…
Q: 5.25 Consider the Nim game: There are n number of tokens. Each player is required to divide the pile…
A:
Q: Describe the importance of technical documentation in any engineering field.
A: Introduction: Technical documentation is used to reduce customer tickets raised by customers when…
Q: f you dont mind me asking what exactly was wrong iun my code
A: - We have to talk about the error in the original code of the student.
Q: In the instance of cybercrime, what assumptions are made?
A: Defending against cyber-attacks is a never-ending and ever-changing challenge. The assumption that a…
Q: File Name: Surname_MP8.m Problem Statement: Based on an automobile's model year and weight the state…
A: ANSWER;-
Q: MCQ3102: The physical layer is concerned with the movement of which of the following over the…
A: This mcq is related to physical layers.
Q: Determine the time complexity function of the program snippet below, int f1(int n) { if (n <= 1)…
A: These re recursive functions and we have to find their time complexity by recurrence relation. We…
Q: How does capacity analysis react when multiple processes are running at the same time?
A: Introduction: Multiprocessor: It is referred to as a multiprocessor when there are two or more…
Q: construct a programming-based version of the factorial function, and prove the time compexity
A: Factorial is the product of all the integers below a given number; for example, factorial four (4!)…
Q: 1] Explain the MOVE command with syntax and example? 2] Explain the XCOPY command with syntax and…
A: To explain: 1] MOVE command 2] XCOPY command 3] CHKDSK command
Q: computer science - Define the risks. Discuss the various types of threats and their sources.
A: Introduction: A computer security risk is something on your computer that can harm or steal your…
Q: Give an example of the differences between an embedded computer and a general-purpose computer.
A: Embedded computers are designed for a specific task. General purpose computer are designed to…
Q: Write a python program to get the binary of a user entered number without using loops, recursion and…
A: Step-1: Start Step-2: Declare a variable number and take input from user Step-3: Using format…
Q: Develop a jupyter notebook in Colab using all of the data processing criteria shown in the class.…
A: To create a new notebook, go to Colab and click on New Notebook (select either Python 2 or 3). It…
Q: In this problem you are provided with a CFG/BNF and you are to determine which of the following…
A:
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: The correct answer for the above mentioned question was given in the following steps.
Q: The problem states that there are five philosophers sitting around a circular table. The…
A: The code is given below as:
Q: Pearson Charity: Donation Form Please complete the form. Mandatory fields are marked with a*…
A: Output
Q: Area code processing In US, long distance phone call is made by dialing the three digits area code…
A: Here is the approach : Create and initialize the array in java . Add all the elements inside the…
Q: Talk about how important system administration is to an organisation.
A: Introduction: The term "system administrator" refers to the person in charge of configuring and…
Q: "Rabenstein code was used to send a message with 4 information bits, you receive 100110001, if y…
A: The answer is
Q: The following Java code is poorly structured. Rewrite it so that it has a better structure and…
A: Please refer to the following steps for the complete solution to the problem above.
Q: “The size of the keyspace is the most important consideration for the security of an encryption…
A: A keyspace is the set of all valid or distinct keys of a given encryption algorithm. The encryption…
Q: write a study report about the database system. The mimimum length is 5 pages.
A: DATABASE SYSTEMS: A database is a logically ordered collection of structured data kept…
Q: Please provide a brief outline of the benefits and drawbacks of connectionless protocols as a…
A: In connection-less protocols, no channel/connection is established for sending packets from sender…
Q: Ques. 13 Demonstrate a code use of structure in c# a powerfull addition to c# struct to define…
A: According to the information given:- We have to follow the instruction in order to create structure…
Q: Java Program Create student class with attributes(states) and methods (behaviors) as shown in the…
A: In this question it is asked to provide a class called student with some specific attributes: name…
Q: Write a program to draw a beautiful artboard
A: Actually, program is an executable software that runs on a computer
Q: Assuming the kid is connected to the school's LAN, what happens when they access the internet and…
A: LAN(Local Area Network): A LAN is a group of computers connected devices that are contained inside…
Q: It is common practice in wireless networks to make use of the following two types of technology: Ad…
A: It self organizes the network. Multiple hop networks. Connectiond are dynamic.
Q: Q1- Convert the following: a-1011 1100B to hexadecimal b- 173D to binary c- 4 1.6875 to binary d- If…
A: As per Bartleby's policy, only the first 3 parts can be solved for the multi-part questions. Please…
Q: Explain what is meant by the zone routing protocol for advanced routing ?
A: Zone Routing Protocol, or ZRP, is a hybrid Wireless Networking routing protocol that sends data over…
Q: Initialize the fields in the object
A: Given :- In the above question, the term constructor in programming language is mention in the above…
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: Here we are expected to respond to the three inquiries posed to above about network foundation for…
Q: Assuming the kid is connected to the school's LAN, what happens when they access the internet and…
A: Introduction A local area network-LAN, is a gathering of associated gadgets in a solitary actual…
Q: Asymmetric algorithms can be used to create public key encryption and key agreement schemes. Discuss…
A: Key agreement scheme enable two or more parties to establish a shared encryption key that they can…
Q: Python 3.10.5 (v3.10.5:f377153967, Jun 6 2022, 12:36:10) [Clang 13.0.0 (clang-1300.0.29.30)] on…
A: - We have to correct the code with the warning.
Q: Which of the following statements could potentially change the value of number 2? O number1= number…
A: Dear Student, number1 = number2; , will allocate the value of number2 to number1 and thus will…
Q: The study of computers -What exactly is a prototype, and what does it serve?
A: Introduction: A pre-production sample, model, or release of a product is referred to as a prototype.…
Q: In one of convolutional layers a ConvNet, the input has the size of 68x62x32, and you convolve it…
A: ANSWER:
Q: C# Password Generator: The program depicts a simple application of a password generator that…
A: It is defined as a general-purpose, object-oriented programming language. It is one of the most…
Q: What impact does hierarchy have on organisational development and administrative autonomy, and how…
A: Intro Hierarchy provides efficient organization. We've all heard the phrase "too many cooks spoil…
Q: Explain how Transnet could respond to the above - mentioned risk by making use of the ' risk…
A: Please find the detailed answer in the following steps.
Q: Q) BEZIER CURVE PRODUCED BY BERSTEIN BASES FUNCTION HAS LIMITED FLEXIBILITY. JUSTIFY THE STATEMENT.
A:
Q: Write a C++ program to generate a random vehicle registration number that is a string of length 10…
A: Write a C++ program to generate a random vehicle registration number that is a string of length 10…
Q: Dont copy & paste form other side Proof of optimality the Huffman tree can now be proved by…
A: Lemma: For any Huffman tree constructed by function buildHuff that contains at least two letters,…
Step by step
Solved in 4 steps with 2 images

- write a c++ program in which function drawLine(int x, int y) in the above code. this function should return length of lines in main i.e subtracting y from x.Write a program in C++ to input two integer numbers (X and Y), the program should contain two functions. function1 (ones) to find the ones of these two numbers, and function2 (sum) to find the summation of these ones then print the summation. Example: X= 25 Y= 34 Summation = 5+4 =9Write a C++ function that accepts a double typed number and return back the fractional part of the number. For example, if the number is 789.123, the number 0.123 should be returned.
- Write a function in c that would return single digit sum of a number. Ex. Given: 195 the function returns 6 -> 1+9+5=15 then 1+5=6 Given: 711 the function returns 9 -> 7+1+1=9write a program in c++ to find the value of x: x=2y+5Z where y=r^2+7 HINT : using functionWrite a C program that reads a double value (x) from the user and then uses it to compute the value of the mathematical constant e to the power of x (ex) and print it in main using the following infinite series: ex =1+x/1!+x2/2!+x3/3!+x4/4!+... Your program should include the following three functions: 1- function called powerOfNumber which takes two parameters: x (double) and y (integer) and returns the value of xy . Function PowerOfNumber MUST use a while loop. ( Not allowed to use the predefined function pow in math.h). 2- function called factorialOfNumber which takes one parameter x (integer) and returns its factorial. Function factoriaOfNumberl MUST use a for loop. 3- function called computeExpo which receives one parameter x (double) and returns the value of ex for the given x using the series above as well as functions powerOfNumber and factorialOfNumber ( 1 and 2 above) . Function computer_ex MUST use a do/while loop. The loop should stop 1 when the new term…
- Write a C program to determine whether a number is a prime number or not using a function. *The function prototype should look like int isPrime(int n) that returns 1 if n is prime and 0 if otherwise.*The use of Flag or bool is not allowed.Write a function called multiplyMe in c programming which has a variable number of integers as arguments and returns the product of the integers ie input | output (3, 2, 3, 4)) 24Write a function that computes the value of e which can be approximated using the following expression: 2 + (1/2!) + (1/3!) + . . . + (1/n!) where n is a positive integer. Write a C++ program that uses this formula to approximate the value of e.
- Write a C++ function that returns true if any of the two integer parameters passed as input is 20, or their sum is 20. Prototype: bool check2(int,int);Write a c++ program that contains a “main” and 4 functions: In the main function declare 4 integer variables x, y, z and m and call the following functions: The first function is to initialize the 4 variables using the last 4 digits of your university ID number. For example, if your ID number is 43956789 then you x=6, y=7, z=8, and m =9. The second function should calculate and print the average of the 4 variables. The third function is to find the largest number of the 3 variables. The last function should double the values of the 4 variables. For example if x = 6 then x will become 12.Write a C++ function that returns how many digits in a string. For example, if youenter “This is an easy quiz, and I should get 10 out of 10”, the function returns 4.Write a C++ program to test your function. Prevent the user from changing the string inside the function. You are allowed to use materials that is not covered in our lectures

