Write a program that reads in five integers and determines and prints the largest and the smallest integers in the group. Use C language and in C++
Q: Summarize the top three virtualization software products. Compare and contrast to understand.
A: Virtualization software lets users construct several virtual machines (VMs) on one physical…
Q: Please provide us with three compelling arguments as to why the incremental development approach is…
A: What is software development: Software development is the process of creating computer programs and…
Q: When transitioning from serial to batch processing, where exactly should one concentrate their…
A: When transitioning from serial to batch processing, focus on analyzing the existing process,…
Q: Give some background information on the concept of "cybersecurity" and the significance of putting…
A: Cybersecurity is the practice of safeguarding electronic devices, systems, and networks against…
Q: When using solid modeling, a designer may create an object not by combining lines but rather by…
A: In computer-aided design (CAD), solid modelling is a method for developing three-dimensional models…
Q: The OSI model, on the other hand, calls for a greater number of layers than are often seen in…
A: The OSI (Open Systems Interconnection) model and TCP/IP (Transmission Control Protocol/Internet…
Q: Each potential enhancement to the structure need to include a description of the challenges that may…
A: When suggesting enhancements to a framework, it is vital to analyse the possible challenges that may…
Q: What steps should a user take in the event that an email service provider examines their…
A: Email service providers routinely review communications acquired through their systems to ensure…
Q: Does the design of network applications vary considerably from that of other kinds of apps in any…
A: Network applications are software programs that enable communication between multiple devices over a…
Q: Describe the operating system's services and their three delivery methods.
A: An operating system provides a wide range of services to applications and users that run on it.…
Q: There are a number different situations in which a denial of service attack might potentially cause…
A: Denial of service (DoS) attacks threaten email systems, interrupting communication and productivity.…
Q: When transitioning from serial to batch processing, where exactly should one concentrate their…
A: Batch processing: The term "batch processing" refers to the operation in which a computer performs a…
Q: What several phases make up the waterfall method to the development of software? It would be quite…
A: According to the information given:- We have to define several phases make up the waterfall method…
Q: Within a distributed system, several individual bits of software are sent around between the many…
A: In a distributed system, software components may be shared across multiple locations, which may have…
Q: What steps should a user take in the event that an email service provider examines their…
A: Email provider: Email service providers frequently review communications acquired through their…
Q: After all has been said and done the most pressing question is: how exactly does the concept
A: Ubiquitous computing, also known as pervasive computing, refers to the idea of embedding computing…
Q: Sentiment analysis accuracy? Please tell me the normal method.
A: Sentiment analysis is a technique used in Natural Language Processing (NLP) to identify and extract…
Q: Recursive Exercises ALL PROGRAMS LISTED BELOW MUST USE RECURSION 1. Write a program that asks the…
A: NOTE: This is a multiple questions based problem. As per company guidelines only first question is…
Q: Read how other customers solved PC and mobile app issues. Consider strategies to comfort customers…
A: There are a variety of PC and mobile app issues that customers may face, but some common ones…
Q: How do we decide the data type to employ in Microsoft Access tables?
A: To ensure that data is saved properly and effectively when building tables in Microsoft Access, it…
Q: Do present safeguards allow under-16s to access the internet safely? Is it? If not, what more…
A: The Children's Online Privacy Protection Act (COPPA) in the United States and the General Data…
Q: What several phases make up the waterfall method to the development of software? It would be quite…
A: Software development is the process of designing, creating, testing, and maintaining software…
Q: DMA may improve system concurrency. How does this affect hardware design?
A: In computer systems , Direct Memory Access (DMA) is employed to enhance data transfer efficiency by…
Q: How can we make it less difficult for people from different countries to utilise the websites of…
A: In this question we have to understand How can we make it less difficult for people from different…
Q: In Design View of the DirectorSeptember query, add criteria using wildcard characters to select all…
A: Design View in access is a view that are used to create tables, installation table relationships,…
Q: You know the essentials of utilising social media. Why cloud computing beats autonomous systems?…
A: Compared to autonomous systems, cloud computing has some benefits, particularly in terms of…
Q: Can computers and the internet's moral minefields be navigated?
A: Yes , the moral minefields of computers and internet can be navigated.They can be navigated with…
Q: As you progress, it is important to think about the challenges that lie ahead of you and the…
A: As technology continues to evolve, businesses and individuals are faced with new challenges and…
Q: When children younger than 16 years old go online, are they secure owing to the precautions that are…
A: Children under the age of 16 who use the Internet may be exposed to a variety of online threats,…
Q: In today's developing countries, having a wireless internet connection that is both dependable and…
A: Having dependable and fast wireless internet in developing countries can provide benefits such as…
Q: When we claim that Direct Memory Access (DMA) has the ability to boost concurrency in the system,…
A: Direct Memory Access (DMA) is a technique for transmitting data between a device and memory without…
Q: What are some ways that you may protect your gadget from possible hazards such as power surges?
A: The Answer is in given below steps
Q: Learn how the introduction of wireless technology has altered life in developing nations. Wireless…
A: Introduction: Wireless technology has brought changes in the lives of people in developing…
Q: Each potential enhancement to the structure needs to include a description of the challenges that…
A: In today's digital age, businesses face many challenges in optimizing their structure for maximum…
Q: For reasons of safety, any and all electronic documents should be encrypted; nevertheless, the law…
A: While it is true that encrypting electronic documents can significantly enhance data security, not…
Q: in Java: Create a class LukcyNumber which checks if the input is a lucky number. A lucky number is a…
A: Define a public static boolean method called "isLucky" that takes an integer "number" as input.…
Q: 1. What is the (big-O) complexity of one add method call? How difficult is it to make n calls to…
A: The big-O complexity of one add method call depends on the data structure used to implement the…
Q: The issue that has to be answered is why these tendencies in cybercrime have evolved at this moment.…
A: Cybercrime has become a significant threat in recent years, with new trends and tactics emerging…
Q: Separate data groups are represented by each individual element of the table that lists the…
A: Interrupt vectors are an essential part of a computer system that help manage and respond to…
Q: Answer the given question with a proper explanation and step-by-step solution. Programming the Pico…
A: from machine import Pin, PWMimport time # set up pins for LEDsled_pins = [Pin(2, Pin.OUT), Pin(3,…
Q: Consider the potential issues with each approach to better prepare for framework design issues.…
A: Cloud computing offers scalable resources, quick prototype and deployment, and lower infrastructure…
Q: What language is accepted by the machine M = ({q0, q1, q2, q3}, {a, b}, {a, b,},, q0, B, {q3]
A: Answer is explained below
Q: You know the essentials of utilizing social media. Why does cloud computing beat autonomous systems?…
A: The core concept behind autonomous computing is the usage of computer hardware and software systems…
Q: What should a user do if their email service provider detects errors in their correspondence?
A: The kind of action that an email service provider takes may be determined by the nature and severity…
Q: Several Unix and Linux commands are identical. What's going on, anyway?
A: Unix is an OS developed by AT&T Bell Labs. Its main principles were to be simple, modular, and…
Q: Think about your own project in light of the example that is shown in the article, and then assess…
A: Typically, the Waterfall project management method oversees the software development process. Each…
Q: Why is it hazardous for email service companies to read their customers' messages?
A: Email service companies have access to their customers' messages, as they are responsible for…
Q: Find a written guide on using devices hands-free while driving. Hands-free devices are illegal…
A: A hands-free device is a technology that allows you to perform certain actions or communicate…
Q: Write a program in c to detect if the system will face any deadlock in the future. If a deadlock is…
A: Deadlock is a critical issue in computer systems where multiple processes compete for limited…
Q: 12.7 The BinaryTree class is a recursive data structure, unlike the List class. Describe how the…
A: Because its components are kept in a sequence and are only accessible by an index, the List class as…
Write a
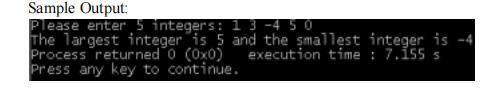
Step by step
Solved in 4 steps with 5 images

- #include <stdio.h> void(main) { char name; int num, i; printf("Enter User Name: "\n); scanf("%c", &name); printf("Enter Number of time fork() must be executed: "\n); scanf("%d", &num); for(i=0; i<num; i++) { fork(); printf("The user name is: ", char); } } Correct the code.import randomdef heads_or_tails(n): i=0 n = 'n' while i<n: num = random.randint(0,1) if num==0: print('heads') else: print('tails') i+=1 if __name__ == '__main__': random.seed(1) number_of_flips = int(input()) heads_or_tails(number_of_flips) it says Traceback (most recent call last): File "main.py", line 16, in <module> heads_or_tails(number_of_flips) File "main.py", line 5, in heads_or_tails while i<n: TypeError: '<' not supported between instances of 'int' and 'str'Your answer could not be processed because it contains errors: line 23: invalid preprocessing directive #Prompt
- Find errors Compilation Is need Code is incomplete Else downvote for incorrect solutionPSEUDO CODE MAKE CODE COMPLETE. 1024: OUTPUT getNumber: Read Base Read Exponent NumExponent(Base, Exponent); NumExponent(Base, Exponent): If Exponent=0 Return 1 Else Return Base*NumExponent(Base, Exponent-1).please code in pythonthe below code has alot of errors .. please make it error free import numpy as np import randomimport sys import osfrom datetime import datetimeimport string import subprocess from subprocess import callfrom subprocess import check_output if len(sys.argv) < 3: print('Usage: maintest.py Nm Ns R \n') exit() Ns = sys.argv[1] #sort size R = sys.argv[2] #number of repetitions w = open('BubbleSortResult.txt', 'w')#BubbleSort1: No Split Input = np.random.rand(Ns) Itmp = list (Input) def sort (numbers): sorted = False while not sorted: sorted = True for i in range (len (numbers)-1): if numbers [1] > numbers [i + 1]: sorted = False numbers [i + 1], numbers [i] = numbers[i], numbers [ i + 1]Te = datetime. now () for i in range (R): #Run R-time Itmp = list (Input) # Get fresh Input #print (Itmp) sort (Itmp) # This is in-place sort. Input will be altered. Te = datetime. now () - Te Totalus…
- Question 5 Write a program that reads 10 characters from the keyboard and then print the characters to the screen in reverse order. Use a loop, the keyboard interrupt 21h, the console interrupt 10h and the svstem stack to Implement your solution Full explain this question and text typing work only thanksAL= 53 CL=29 ADD AL, CL DAA What is the value of AL after execution? A) 39 B) None C) 7CH D) 35HAnswer only if you know the answer how many read/write operations are in this line of code int a = i + i Note :-Don't copy paste or give me proper answer with full explanation If you copy paste or give wrong answer I will downvote multiple time
- Modify below program to include response timeProgram: #include<stdio.h>#include<conio.h>using namespace std; int main(){int p[20],bt[20], su[20], wt[20],tat[20],i, k, n, temp; float wtavg, tatavg;printf("Enter the number of processes---"); scanf("%d",&n);for(i=0;i<n;i++){p[i] = i;printf("Enter the Burst Time of Process %d---", i); scanf("%d",&bt[i]);printf("System/User Process (0/1) ?---"); scanf("%d", &su[i]);}for(i=0;i<n;i++)for(k=i+1;k<n;k++)if(su[i] > su[k]){temp=p[i];p[i]=p[k];p[k]=temp;temp=bt[i];bt[i]=bt[k];bt[k]=temp;temp=su[i];su[i]=su[k];su[k]=temp;}wtavg = wt[0] = 0; tatavg = tat[0] = bt[0];for(i=1;i<n;i++){wt[i] =wt[i-1]+bt[i-1];tat[i] =tat[i-1]+ bt[i];wtavg = wtavg + wt[i]; tatavg = tatavg + tat[i];}printf("\nPROCESS\t SYSTEM/USER PROCESS \tBURST TIME\tWAITING TIME\tTURNAROUND TIME"); for(i=0;i<n;i++)printf("\n%d \t\t %d \t\t %d \t\t %d \t\t %d ",p[i],su[i],bt[i],wt[i],tat[i]);printf("\nAverage Waiting Time…Note:- Study this program and follow the given instruction and type execute the code and also give output for this java program as soon as possible. Modify example six to read file tooutfile2.txt compute and display the total. Then write the total to a file named tooutfile2A.txt exampleSix This program creates file tooutfile2.txt and stores 10 integers in it Please verify that the file was created along with the content package pwriter2; import java.util.Scanner; import java.io.*; public class Pwriter2 { public static void main(String[] args) throws IOException { PrintWriter tofile2 = new PrintWriter( "tooutfile2.txt" ); int i = 0; while (i < 10){ tofile2.println( i ); i = i + 1; } tofile2.close(); } }Study the block of codes below: (see attached photo) Which line of code will cause an error/problem when compiled/executed? (Indicate only the line number. If you think there will be no errors/problems, type NA as your answer.)







