Write a program that reads words from a text file and displays all the words (duplicates allowed) in ascending alphabetical order. The words must start with a letter. The text file is passed as command-line argument (you can assume that the text file is in the same directory as the executable, i.e. bin).
Write a program that reads words from a text file and displays all the words (duplicates allowed) in ascending alphabetical order. The words must start with a letter. The text file is passed as command-line argument (you can assume that the text file is in the same directory as the executable, i.e. bin).
Database System Concepts
7th Edition
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Chapter1: Introduction
Section: Chapter Questions
Problem 1PE
Related questions
Question
Can you help/guide me on this assignment, here are the directions:
Write a program that reads words from a text file and displays all the words (duplicates allowed) in ascending alphabetical order. The words must start with a letter. The text file is passed as command-line argument (you can assume that the text file is in the same directory as the executable, i.e. bin).
I think the code is correct but I believe what I'm doing wrong is the Command line argument where I'm placing the text file. Which I think is in the right place, apparently not.
Here's my work:
![Package Explorer X
Display TickTack Toe
>
> javaFx
I▶ IION 3.3.232!
BS!
T
GenericStack.java
1 package application;
2 import java.io.File;
10
11
3 import java.util.ArrayList;
4 import java.util.Scanner;
5 import java.util.Collections;
6
7
public class Programkit20 {
8
90
public static void main(String[] args) {
if (args.length != 1) {
System.out.println("Usage: java Programkit20 fullfilename");
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
}
}
}
Program kit20.java X Kit20.java
System.exit(1);
}
String filename = args[0];
ArrayList<String>words= new ArrayList<>();
}
try {
Scanner in = new Scanner (new File(filename));
while(in.hasNext()) {
}
String word = in.next();
if (word.matches ("[a-zA-Z].*")) {
words.add(word. to LowerCase());
♡
Collections.sort (words);
for (String word:words) {
System.out.println (word);
}
in.close();
} catch (Exception ex) {
System.err.println("Error reading file:" + ex.getMessage());
Problems @ Javadoc Declaration Console X Properties Debug
*
<terminated > Programkit20 [Java Application] C:\Program Files\Java\jdk-19\bin\javaw.exe (Mar 16, 2023, 1:25:44 AM – 1:25:45 AM) [pid: 1400]
Usage: java Programkit20 fullfilename](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2Fbdc33a51-efff-4610-b226-be7150e1db8b%2F21d833f7-0d81-4ac7-9e22-31f8d6354d7f%2Fcfk7a07_processed.png&w=3840&q=75)
Transcribed Image Text:Package Explorer X
Display TickTack Toe
>
> javaFx
I▶ IION 3.3.232!
BS!
T
GenericStack.java
1 package application;
2 import java.io.File;
10
11
3 import java.util.ArrayList;
4 import java.util.Scanner;
5 import java.util.Collections;
6
7
public class Programkit20 {
8
90
public static void main(String[] args) {
if (args.length != 1) {
System.out.println("Usage: java Programkit20 fullfilename");
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
}
}
}
Program kit20.java X Kit20.java
System.exit(1);
}
String filename = args[0];
ArrayList<String>words= new ArrayList<>();
}
try {
Scanner in = new Scanner (new File(filename));
while(in.hasNext()) {
}
String word = in.next();
if (word.matches ("[a-zA-Z].*")) {
words.add(word. to LowerCase());
♡
Collections.sort (words);
for (String word:words) {
System.out.println (word);
}
in.close();
} catch (Exception ex) {
System.err.println("Error reading file:" + ex.getMessage());
Problems @ Javadoc Declaration Console X Properties Debug
*
<terminated > Programkit20 [Java Application] C:\Program Files\Java\jdk-19\bin\javaw.exe (Mar 16, 2023, 1:25:44 AM – 1:25:45 AM) [pid: 1400]
Usage: java Programkit20 fullfilename
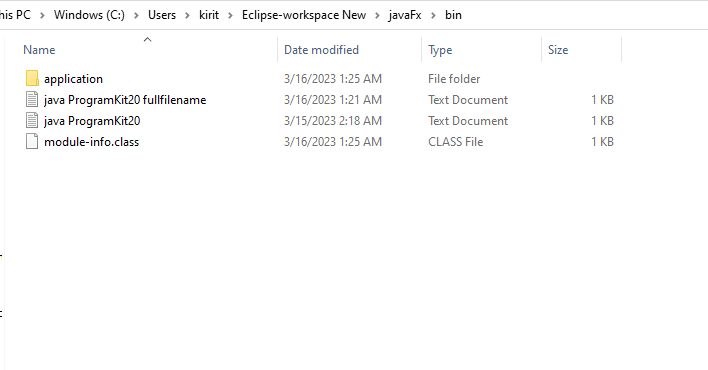
Transcribed Image Text:mis PC Windows (C:) > Users kirit > Eclipse-workspace New > javaFx > bin
Type
File folder
Text Document
Text Document
CLASS File
Name
application
java ProgramKit20 fullfilename
java ProgramKit20
module-info.class
Date modified
3/16/2023 1:25 AM
3/16/2023 1:21 AM
3/15/2023 2:18 AM
3/16/2023 1:25 AM
Size
1 KB
1 KB
1 KB
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 5 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:
9780133976892
Author:
Paul J. Deitel, Harvey Deitel
Publisher:
PEARSON

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781337627900
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:
9780073373843
Author:
Frank D. Petruzella
Publisher:
McGraw-Hill Education