Write a program to set zero in the lower triangular of a given matrix a(4,4). For example array below. .... 1 2 45 o2 36 o o8 9 00 04 For i = 1 To 4 For j = 1 To 4 a(i, j) = InputBox("") Next j: Next i %3D For i = 1 To 4 For j = 1 To 4 1-. 2-. 3-. 4- End If Next j Print Next i 1-lf i <= j Then 2-Print a(i, j); 3-Else 4- Print "0"; 1-lf i <= j Then 2-Print a(i, j); 3-Blank 4- Print "0"; 1-lf i >= j Then 2-Print a(i, j); 3-Else 4- Print "O"; O 1-lf i <= j Then 2-Print "0"; 3-Else 4-Print a(i, j);
Write a program to set zero in the lower triangular of a given matrix a(4,4). For example array below. .... 1 2 45 o2 36 o o8 9 00 04 For i = 1 To 4 For j = 1 To 4 a(i, j) = InputBox("") Next j: Next i %3D For i = 1 To 4 For j = 1 To 4 1-. 2-. 3-. 4- End If Next j Print Next i 1-lf i <= j Then 2-Print a(i, j); 3-Else 4- Print "0"; 1-lf i <= j Then 2-Print a(i, j); 3-Blank 4- Print "0"; 1-lf i >= j Then 2-Print a(i, j); 3-Else 4- Print "O"; O 1-lf i <= j Then 2-Print "0"; 3-Else 4-Print a(i, j);
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter6: Arrays
Section: Chapter Questions
Problem 17RQ
Related questions
Question
i need the answer quickly
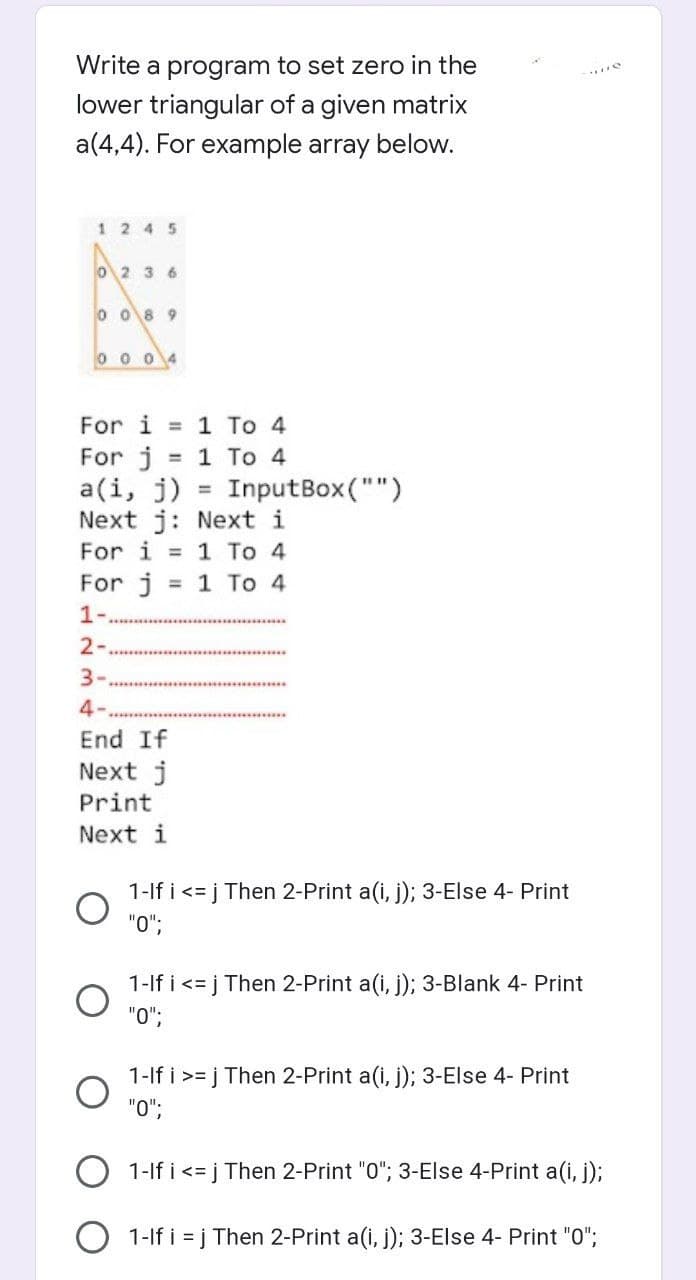
Transcribed Image Text:Write a program to set zero in the
lower triangular of a given matrix
a(4,4). For example array below.
1 2 45
o2 3 6
0 08 9
0 0 04
For i = 1 To 4
For j
a(i, j)
Next j: Next i
For i = 1 To 4
= 1 To 4
InputBox ("")
%3D
For j
1-.
3 1 Tо 4
2-
3-
4-
End If
Next j
Print
Next i
1-lf i <= j Then 2-Print a(i, j); 3-Else 4- Print
"O";
1-lf i <= j Then 2-Print a(i, j); 3-Blank 4- Print
"0";
1-If i >= j Then 2-Print a(i, j); 3-Else 4- Print
"0";
O 1-If i <= j Then 2-Print "0"; 3-Else 4-Print a(i, j);
O 1-lf i = j Then 2-Print a(i, j); 3-Else 4- Print "0";
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage