• Write a Python code to calculate and plot the square and cube of values between -10 and + 10. Hint: use functions to calculate the square and cube values. The plot should be done inside a function.
• Write a Python code to calculate and plot the square and cube of values between -10 and + 10. Hint: use functions to calculate the square and cube values. The plot should be done inside a function.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter6: Modularity Using Functions
Section: Chapter Questions
Problem 2PP
Related questions
Question
Need Correct solution
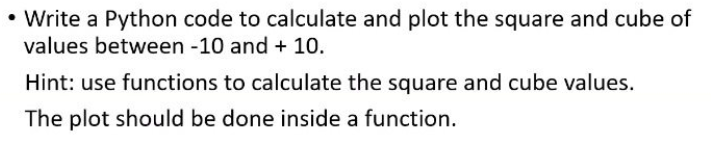
Transcribed Image Text:• Write a Python code to calculate and plot the square and cube of
values between -10 and + 10.
Hint: use functions to calculate the square and cube values.
The plot should be done inside a function.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 5 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning