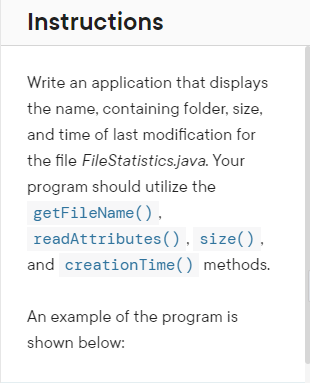
Write an application that displays the name, containing folder, size, and time of last modification for the file FileStatistics.java. Your program should utilize the getFileName(). readAttributes(), size(), and creation Time () methods.
Q: Do you believe wireless applications gain the most from error correction? Give examples to support…
A: Introduction: Securely transmitting high-quality photos over a wireless network is a considerable…
Q: What factors influence the appeal of cybercrime to particular individuals?
A: Introduction: When the computer is used for illegal activities like trafficking, committing fraud,…
Q: Identify any three protocols that are susceptible or prone to attack if the organization's users are…
A: Introduction The following are examples of protocols: 1) Address Resolution Protocol (also known as…
Q: Any three protocols that are not secure or vulnerable to assault for the organization's users would…
A: Protocol: When it comes to exchanging information, a protocol is a set of standards and norms to…
Q: What is the relationship between relational algebra and relational databases, and how do they…
A: Introduction: SQL is built on the foundation of relational algebra. The SQL parser transforms the…
Q: Investigate the possibilities of using Structured English to describe processes in fields other than…
A: Intro: Investigate the possibilities of using Structured English to describe processes in fields…
Q: Think of your department's DNS servers as being accessible to you. Which web servers do your…
A: Introduction: It's feasible to obtain access to the DNS (Domain Naming Server) server's cache. This…
Q: Distinguish between the advantages and disadvantages of the existing network environment.
A: Introduction A network is a collection of distributed autonomous systems that exchange and…
Q: Compared to abstract classes, what are the benefits of using interfaces instead?
A: Introduction: Computer programming is the process of creating a set of instructions that tells a…
Q: How is the repeated calls to a recursion function controlled? What type of control structure is…
A: Introduction: In a computer language, a recursive function is a routine that calls itself directly…
Q: What sets embedded computers apart from general-purpose computers?
A: Introduction: Differences between embedded and general-purpose systems are :
Q: Is it possible to explain locality of reference and how it improves memory access efficiency
A: Introduction: Locality of Reference: If the CPU executes a program me and accesses a certain…
Q: 2. Use Boolean Algebra to simplify the following expressions (clearly state which rule/laws you used…
A: Boolean Algebra Laws: Associative Law: It states that any operation will be performed in any order…
Q: if the organization's users depend heavily on the network for their day-to-day operations, what…
A: Solution: Network Protocols are a set of well-understood rules for governing and controlling data…
Q: Is there a list of the four most important qualities of software development that can be broken down…
A:
Q: What distinguishes each network generation, as well as its advantages and disadvantages?
A: Intro What distinguishes each network generation, as well as its advantages and disadvantages?…
Q: w significant are the challenges faced by global information networks
A: Significant challenges faced by global information networks : Legal rights difference Network…
Q: NOTE: In all what follows, DOB refers to your day of birth and MOB would be the month of your birth.…
A: Draw the following binary tree. Where only the key is shown:35, 20, 23, 15, 40, 38, 24, 45, 33, 48,…
Q: Why is it that the internet is considered to be such a shining example of information and…
A: Given: What makes the internet one of the best examples of information and communication technology?…
Q: When the configuration of a database changes, the DEMS must update its catalogue. Manually changing…
A: Intro When the configuration of a database changes, the DEMS must update its catalogue. Manually…
Q: Recognize the benefits and drawbacks of today's network environment.
A: Intro Recognize the benefits and drawbacks of today's network environment.
Q: Do you have any experience with software piracy?
A: Introduction: In fact, given a question about incidents of software piracy
Q: Provide a student who is not majoring in information technology with a concise explanation of IT…
A: Introduction: The sector of information technology is a very profitable one. The yearly salary that…
Q: Explain the concept of command line arguments with suitable example in C
A: Command line arguments When a program is run, it receives a parameter called a command line…
Q: Could you please explain the distinctions between the ARM and Core i3 architectures?
A: Introduction: ARM Advanced RISC Machines (ARM) are a class of older 32-bit processor cores that are…
Q: What kinds of usability testing techniques, including cognitive walkthroughs, are available so that…
A: Introduction: Candidate Usability analysis methods, Usability analysis methods will provide input on…
Q: n systems used inside the working environment?
A: Interorganizational supply chains and electronic markets are managed using information systems..
Q: Are you able to provide any further details on the CSRF attack?
A: Introduction: Cross-Site Request Forgery, also known as CSRF, is a type of attack that tricks…
Q: When a file extension is created and by what programs are the two questions that need to be…
A: Given: There are many different file types on your computer, each with its own file extension. A…
Q: In order to determine whether two graphs are related, can you use DFS? Step-by-step instructions are…
A: DFS is an algorithm traverses or searches tree or graph data structures. The algorithm begins at the…
Q: How does today's era of artificial intelligence compare to that of AI from 50 years ago, in terms of…
A: Introduction: In terms of machine learning or deep learning algorithms, how does today's AI differ…
Q: The associativity of an exponentiation operator ^ is right side. a) True b) False
A: The question has been answered in step2
Q: C# please create an abstract class named "Payment" and abstract method named "Authorized" . Create…
A: C#: C# is pronounced by C-sharp. It is developed by Microsoft. It is object oriented programming…
Q: Server Sid... Hi nothing Wht abt ur dinner? 10 X Send Client Sid.... Hello! whts up? X Send
A: AppServer.java import java.awt.*;import java.awt.event.*;import java.io.*;import java.net.*; public…
Q: How Many Memory Types Are There in a Computer?
A: Memory is a storage unit which is used store all the data or information in the computer system.…
Q: Distinguish the benefits and drawbacks of the current network environment.
A: Intro Distinguish the benefits and drawbacks of the current network environment.
Q: Evaluate the following and choose the correct answer. a/b+c*d where a=4, b=2, c=2, d=1. a) 1 b) 4 c)…
A: The answer will be 4 (option b) Explanation:- The infix notation mainly used in the arithmetic…
Q: On mobile phones, how Linux is utilised
A: Introduction: Android is without a doubt one of the most popular Linux-based technologies of all…
Q: Name and describe at least two operating systems, which provide graphical user interface for working…
A: The two operating systems, which provide the graphical user interface for working on computers are…
Q: What are the three most crucial database management tasks?
A: Introduction: Database administration encompasses the whole set of responsibilities performed by a…
Q: Composer is used to convert higher-level programmes into programmes with a lower level of…
A: Compilers transform sophisticated programs into machine code. So, it's crucial beyond CPU and…
Q: When compared to alternative database management system applications, what are the benefits of…
A: Introduction: MySQL - MySQL is an open-source software developed by Oracle that is primarily used to…
Q: In what ways does the Internet contribute to the development of a worldwide information network? Is…
A: Given: To what extent does the internet contribute to the development of a global information…
Q: Compare and contrast the browsers Edge and Chrome. In terms of functionality, what are their…
A: I will give certain parameters and will differentiate the edge and chrome browser. SPEED- Edge is…
Q: What does it mean to be computer literate, and how can you go about demonstrating this knowledge?
A: Given: Learning how to use a computer requires being knowledgeable about its capabilities and…
Q: What is the risk of using the SSTF disc scheduling algorithm?
A: Introduction: The shortest seek time first (SSTF) approach is used to choose a disc I/O request if…
Q: How does the use of disparate information systems give rise to concerns and difficulties, and what…
A: Losses and malfunctions of computers are a significant issue, resulting in wasteful expenditures and…
Q: What are the differences between TCP and UPD session hijacking?
A: Hijacking occurs when an attacker utilizes a remote server to display an image, music, or video to…
Q: What is the difference between the BST and the AVL tree?
A: Introduction: A tree is a hierarchical data structure that consists of nodes and connected edges.…
Q: Invoice Total Calculator Customer Type: Regular Invoice Subtotal: 2250.25 Invoice Date: 5/19/2024…
A: Code:- <!DOCTYPE html><html><head> <style> input{…
I need Answer Quickly
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- I am having error E0020 and E0140 in C++. How can I fix it? /*Christopher JimenezCIS247CATM application24 November */ // bring in our libraries //Step #1#include <iostream>#include <conio.h>#include <string>#include <fstream> // read/write to files#include <ctime> // time(0)#include <iomanip> //setprecision()using namespace std; // prototypesvoid deposit(double* ptrBalance);void withdrawal(double* ptrBalance, float dailyLimit); // overloaded method - this version does not take withdrawal amountvoid withdrawal(double* ptrBalance, float dailyLimit, float amount); //overloaded method that takes withdrawal amount ///Entry point to the applicationint main(){ // create constant values -- cannot be changedconst int EXIT_VALUE = 5;const float DAILY_LIMIT = 400.0F;const string FILENAME = "Account.txt"; //create balance variabledouble balance = 0.0; // look for the starting balance; otherwise generate a ramdom starting balanceifstream iFile(FILENAME.c_str());…Suppose you have Java source files under the directorieschapter1, chapter2, . . . , chapter34. Write a program to insert the statementpackage chapteri; as the first line for each Java source file under the directorychapteri.Create a program named FileComparison that compares two files. First, use a text editor such as Notepad to save your favorite movie quote. Next, copy the file contents, and paste them into a word-processing program such as Word. Then, write the file-comparison application that displays the sizes of the two files as well as the ratio of their sizes to each other. To discover a files size, you can create a System. 10. Filelnfo object using statements such as the following, where FILE_NAME is a string that contains the name of the file, and size has been declared as an integer: FileInfo fileInfo = new FileInfo(FILE_NAME); size = fileInfo.Length;
- In Chapter 11, you created the most recent version of the MarshallsRevenue program, which prompts the user for customer data for scheduled mural painting. Now, save all the entered data to a file that is closed when data entry is complete and then reopened and read in, allowing the user to view lists of customer orders for mural types.a) Create a system call int sys_wolfie(void *buf, uint size), which copies an ASCII art image of Wolfie to a user-supplied buffer, provided that the buffer is large enough. You are welcome to use an ASCII art generator, or draw your own by hand. If the buffer is too small, or not valid, return a negative value. If the call succeeds, return the number of bytes copied. B) Write a user-level application, called wolfietest.c, that gets the Wolfie image from the kernel, and prints it to the console. When the OS runs, your program's binary should be included in fs.img and listed if someone runs ls at the xv6 shell's command prompt. Language in CPlease complete these files. There are two text files attached. Running the code should result in the creation of an output file ("PE_output.txt"). Please give full reasoning to the answer. Please also paste the full java code and please attach a screenshot of the successful program run. package solution; import java.io.*;import java.util.Scanner; public class PE_1_problem {@SuppressWarnings("resource")public static String readFirstLetters(String filename) {String result = "";File f = new File(filename);// Surround the next command inside a try/catch block,// as it is possible the file doesn't exist.try {Scanner fileContents = new Scanner(f);while (fileContents.hasNextLine()) {// 1. Get the next line and store in a variable// 2. Check the length of the line. If the line is not an// empty string, add the character at the start of the line// to the result string.// 3. Otherwise, add an empty space to the result string.}fileContents.close();} catch (FileNotFoundException e) {…
- IN JAVA Which XXX allows information to be written to a file using print( )? FileOutputStream foStream = null; PrintWriter outFS = null; foStream = new FileOutputStream("outfile.txt");XXXoutFS.println("Java is my favorite language!"); A. outFS = new PrintWriter("outfile.txt"); B. new PrintWriter(foStream); C. outFS = PrintWriter.open(foStream); D. outFS = new PrintWriter(foStream);You are going to write a program (In Python) called BankApp to simulate a banking application.The information needed for this project are stored in a text file. Those are:usernames, passwords, and balances.Your program should read username, passwords, and balances for each customer, andstore them into three lists.userName (string), passWord(string), balances(float)The txt file with information is provided as UserInformtion.txtExample: This will demonstrate if file only contains information of 3 customers. Youcould add more users into the file.userName passWord Balance========================Mike sorat1237# 350Jane para432@4 400Steve asora8731% 500 When a user runs your program, it should ask for the username and passwordfirst. Check if the user matches a customer in the bank with the informationprovided. Remember username and password should be case sensitive.After asking for the user name, and password display a menu with the…Write a utility program that combines the files together into anew file using the following command:java Exercise17_12 SourceFile1 . . . SourceFilen TargetFileThe command combines SourceFile1, . . . , and SourceFilen into TargetFile.
- Suppose you have Java source files under the directorieschapter1, chapter2, . . . , chapter34. Write a program to remove the statement package chapteri; in the first line for each Java source file underthe directory chapteri. Suppose chapter1, chapter2,. . . , chapter34are under the root directory srcRootDirectory.The root directoryandchapteridirectory may contain other folders and files. Use the followingcommand to run the program:java Exercise12_20 srcRootDirectoryWrite a program FileSorter that takes the name of adirectory as a command-line argument and prints out all of the files in the currentdirectory, sorted by file name. Hint : Use the File data type.Here is the code I've tried. Although I used the full path to the file and the file is located in the same directory as my program executable, when I run it is doesn't read the text file #include <iostream>#include <fstream>#include <sstream>#include <iomanip> using namespace std; void loadArrays(string product[], int quantity[], float cost[], int& counter) {ifstream file; //ifstream functionstring inLine, prod, qty, cst; //variables to hold read line temporarily //open input filefile.open("C:\\Users\\Honeypie\\source\\repos\\Project4\\inventory.txt", ios::in); while (getline(file, inLine)) { //read first lineistringstream ss(inLine); //split the line using a delimeter//you may change this delimeter according to your input filegetline(ss, prod, '|');getline(ss, qty, '|');getline(ss, cst, '|'); if (prod != "Product Code") { //if statement that will ignore the column headersproduct[counter] = prod; //insert product code to product arrayquantity[counter] =…





