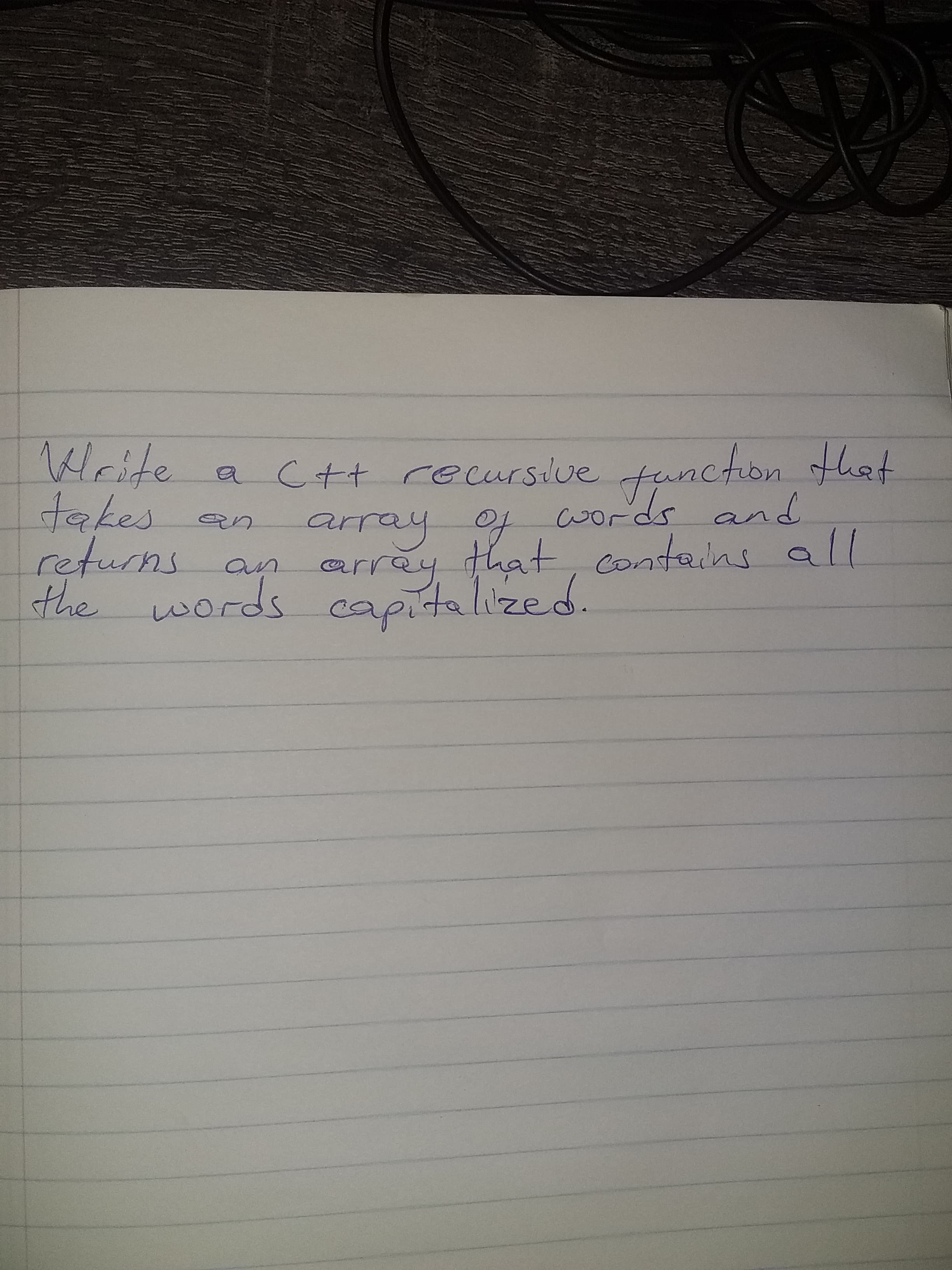
Write e a c+t recursive function that takes returns the words capitalized. array of cwords and an array that, contains ll an
Q: Prove De Morgan's Law for set equality AUB = AnB
A: Prove De Morgan's Law for set equality AUB=AnB by showing with a chain of IFF's that x e the left-ha...
Q: Write a regular expression for {wE {a, 6}" : w contains either exnctly one or exactly three a's (and...
A: Regular Expression: A regular expression is exists for all the regular languages. A regular expressi...
Q: what the GRANT statement is and how it pertains to the security of the system. What kinds of privile...
A: It is defined as a statement that enables system administrators to grant privileges and roles, which...
Q: What are whole disc encryption (WDE) solutions and when do they need to be used?
A: Introduction: In the broadest sense, whole Disk Encryption (WDE) solutions are the most important in...
Q: nvm
A: nvm
Q: why the performance metrics SPEC is REPEATABLE but NOT RELIABLE?
A: Answer: A repeatable experiment assures that the same value is measured every time. A deterministic ...
Q: How do you make sure each machine utilises its own private key pair while using IPsec?
A: Check further steps for the answer :
Q: Explain what the memory addressing capacity of the 20-bit address bus will be.
A: Introduction: The memory capacity is determined by various factors, including the number of address ...
Q: What is the difference between using +/- versus = when setting file permissions? Is there any benefi...
A: Basically +/- is used to add or delete permissions for the file. = is used to specify the new set of...
Q: Instructions MovieQuotelnfojava 1 class MovieQuoteInfo { public static void main(String[] args) { //...
A: Here, I have to provide a java solution to the above question.
Q: Take a look at the data you have on your computer. Do you have any personal data on your computer? W...
A: Data has become an integral part of the industry these days. Safety and security of data is very imp...
Q: What is the mantissa and exponent for 6.75 in 8-bit binary floating point?
A: Find mantissa and exponent for 6.75
Q: Wireless networking offers both advantages and disadvantages. Given the security concerns, should wi...
A: - We need to talk about the wireless networking being the exclusive means of communication in the of...
Q: Identify and explain the mode of data transfer in which cpu continuously monitor the status register...
A: Let's understand step by step : Mainly there are 3 types of mode of transfer : 1. Programmed I/O...
Q: Take a look at the data you have on your computer. Do you have any personal data on your computer? W...
A: Computer stores data ,personal data of the user ,and to protect these data we need to have good secu...
Q: Look into one intriguing data or text mining application and explain it.
A: Text mining: Text mining, also known as text data mining, is the technique of extracting high-qualit...
Q: 4 5
A: DFS traverse of first node i.e. 1 with minimum number in all the nodes- Now we have to select the n...
Q: Translate the following signed decimal number to an binary: -7
A: -7 is the signed decimal in next step will find 8-bit binary
Q: Create a program which totals a list of numbers that are read in using the input statement. The numb...
A: The program for given problem statement is written in python l=[]while(1): a=int(input()) if(a...
Q: The directory entry tracks the ____________. Files ending cluster Files starting cluster...
A: The directory entry tracks the ____________.
Q: Vrite a Python program to show the use of the isinstance() function to check whether the value 0.5 i...
A: Please find the answer below :
Q: Neutral Networking problem: Do not copy-paste anything from google or any previous solves. kindly wr...
A: Neutral Networking problem: Do not copy-paste anything from google or any previous solves. kindly wr...
Q: Examine the benefits and drawbacks of various system models.
A: answer is
Q: What is the difference between using +/- versus = when setting file permissions? Is there any benefi...
A:
Q: What exactly was "Networking"?
A: Networking: Networking, sometimes referred to as computer networking, is the process of transferring...
Q: One of the most frequent IT-related issues we encounter deals with connectivity. "I can't get to the...
A: One of the greatest deal and challenge these days, IT has to encounter is of the networking issues o...
Q: Examine the advantages and disadvantages of various system models.
A: A system model is a representation of a process that is abstract. The system model is divided into p...
Q: For each invoice, list the invoice number, invoice date, item ID, quantity ordered, and quoted price...
A: Answer: -- create database KIMTAY create database KIMTAY; -- ensure that KIMTAY is used use KIMTAY; ...
Q: the IOPS number calculated for the CIO to determine a purchase of new storage equipment and the vend...
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: “use” of the word DEFINE purpose:
A: DEFINE is used in C Programming and SQL server both. In C DEFINE is a directive which is used for al...
Q: Examine the advantages and disadvantages of various system models.
A: System Models are mainly divided into 5 types: -> Minicomputer model -> Workstation model -...
Q: List 10 merits and demerits of ict
A: ICT is abbreviated for information and communications technology and in today’s world called as IT(I...
Q: Describe the tools and technologies that are uti
A: Describe the tools and technologies that are utilized to enable information technology project manag...
Q: Complete the code provided to add the appropriate amount to totalDeposit. 5290 2416604.qx3zqy7 1 #in...
A: Introduction:
Q: For Loops: What will be displayed to the screen when the following for loop is executed? for i in r...
A: Given code : for i in range (5,10,2): #start, stop, step print (i) print (“we are here”) The gi...
Q: Can you find 5 bad consequences of starting the test late in the project? Can you find 5 ways to pre...
A: The major five bad consequences of starting the test late in the project are :- 1. cost overruns. 2....
Q: What is the RAND Corporation's Report? Why was it created? What was in RAND Report R-609?
A: What is RAND report? RAND reports present research findings and objective analysis that address the ...
Q: Isn't it true that different systems save disc folders at different track places on the disc for a r...
A: Solution: Advantages: creating more than one partition has the following" The separation of the ...
Q: Write a Python program to show the use of the isinstance() function to check whether the value 0.5 i...
A: Approach: The isinstance() function in Python takes the object and the class as the parameters and r...
Q: Find the Worst case time Complexity of the following recursive function T(n) = T(n-1)+n -1, T(1) = 0...
A: Given:T(n) = T(n-1)+n-1, T(1) = 0Solving it using substitution:T(n) = T(n-1)+n-1 <-(1)T(n-1) = T(...
Q: What part of a disk drive consists of columns of tracks on two or more disk platters? Head ...
A: Option(b) is correct.
Q: write c++ program to input a year and to check whether it is a leap year or not
A: I have provided C++ CODE along with CODE SCREENSHOT and also provided TWO OUTPUT SCREENSH...
Q: What is the difference between hardware and software interrupts, and what are some examples of when ...
A:
Q: vhat the memory
A:
Q: What is the most effective technique to keep track of RFIS?
A: Introduction: Request for information is a standard business practice that aims to gather written in...
Q: In the preceding PL/SQL block, determine the values and data types for each of the following cases. ...
A: PL/SQL block, the values and data types for each of the following cases are: a) The value of v_cus...
Q: E Expert Q&A Please read the questions carefully before answering and also your answers must be in C...
A: Given :- Please read the questions carefully before answering and also your answers muste in C ++ pr...
Q: Why is KM such a multidisciplinary area? What challenges does this present?
A: KM is known to be a multidisciplinary field and contributing disciplinary areas are: Management sci...
Q: Write a program in c to implement a Stack using array. In order to implement the stack, program for...
A: Stack is a linear data structure that follows a particular order in which the operations are perform...
Q: Explain the phrase "balanced scorecard" in just a few words. What role does it play in the operation...
A: Operation of the Business: The everyday actions of a firm that help it build its worth and earn prof...
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

- 1. Write a C++ function named "extractDebugOption" that accepts arguments similar to argc (an integer for the array size) and argv (an array of pointers to C-string). It will determine whether it has the argument of "/debug yes" or "/debug no". It will return true if the debug option is yes. If "/debug no" or there is no debug option or "/debug" without "yes" or "no" followed, it will return false. Note: command line arguments are simply an array of pointers to C-string. Please test it with the following command line arguments These will return true"/debug yes""/compile /debug yes" These will return false"/debug no""/debug""debug""yes /debug""no /debug"In c++, please and thank you! Write a function that dynamically allocates an array of integers. The function should accept an integer argument indicating the number of elements to allocate. The function should return a pointer to the array.Reversing an Array1. Describe the definition of recursive function.oBase case(s)oRecursive case(s)2. Write the code.
- C++ program: Write a function that accepts an array/vector as an input and calculate the sum of all the elements in the array. This function must use recursion to achieve this. Show code: Please show all steps.In C++ I need to compose a function that accepts an array of integer values as an argument and returns the total of the values in the arrayClasswork Requirements: Developa program in C++ that: Reads as many test scores as the user wants from the keyboard (assuming at most 50scores). Test scores should be whole numbers. You must validate user input; only positive numbers are valid. Prints the scores in original order sorted from high to low the highest score the lowest score the average of the scores Implement the following functions using the given function prototypes: void displayArray(int array[], int size)- Displays the content of the array void selectionSort(int array[], int size)- sorts the array using the selection sort algorithm in descending Hint: refer to example 8-5 in the textbook. int findMax(int array[], int size)- finds and returns the highest element of the array int findMin(int array[], int size)- finds and returns the lowest element of the array double findAvg(int array[], int size)- finds and returns the average of the elements of the array
- write in c++ please but not use stl, use array please... Use the following headers to create a function that returns sorted strings. Create a test program that receives the string sort(string&s) string and outputs the newly sorted string to the screen.sample execution resultEnter a string s : silentThe sorted string is eilnstC codeblocks Only write a function that receives an array, its size and a value to search for (define your function in the same way as the given function prototype). The function should return the index of the searched element in the array. If the element is not found, it should return -1. If the array has more than one element of that same value, it should return the value -2. The array is not necessarily sorted and should not be sorted in the function. #include <stdio.h>#include <stdlib.h>int searchIt(int arr[], int size, int value);int main() {int a[]={1,2,3,4,5};printf("%d", searchIt(a,5,3));return 0;}//Your answer starts here. For example: Test Result int a[]={1,2,3,4,5}; printf("%d", searchIt(a,5,3)); 2 int b[]={3,2,5,7,10,2,4}; printf("%d", searchIt(b,7,2)); -2 int c[]={-1,0,234,43,2,1,4,5}; printf("%d", searchIt(c,8,99)); -1JAVA CODE PLEASE Recursive Functions Quiz by CodeChum Admin Create a recursive function named sequence that accepts an integer n. This function prints the first n numbers of the Fibonacci Sequence separated by a space in one line Fibonacci Sequence is a series of numbers in which each number is the sum of the two preceding numbers. In the main function, write a program that accepts an integer input. Call the sequence function by passing the inputted integer. Input 1. One line containing an integer Output Enter·a·number:·5 0·1·1·2·3
- JAVA CODE PLEASE Recursive Functions Practice l by CodeChum Admin Create a recursive function named fun that prints the even numbers from 1 to 20 separated by a space in one line. In the main function, call the fun function. An initial code is provided for you. Just fill in the blanks. Output 2·4·6·8·10·12·14·16·18·20C++ Coding: ArraysTrue and False Code function definitions for eoNum() and output(): Both eoNum() and output() are recursive functions. output() stores the even/odd value in an array. Store 0 if the element in the data array is even and store 1 if the element in the data array is odd. eoNum() displays all the values in an array to the console.8.10 (Appending Part of a String) Write a program that uses function strncat to append part of a string to another string. The program should input the strings, and the number of characters to be appended, then display the first string and its length after the second string was appended. **Note solve question without using pointers in c language

