Write the following assembly language codes: a) Write a single instruction to add the carry flag to register AH. b) Write the code to find the number of 1s in the register AL. c) Write the code to place 1 in register AL if the value in BL is odd. d) Declare two byte values and find the sum of the values and place the value in a byte location called sum, multiply the values and place in a word location called product and divide the values and save the quotient and remainder in byte locations called quotient and remainder.
Write the following assembly language codes: a) Write a single instruction to add the carry flag to register AH. b) Write the code to find the number of 1s in the register AL. c) Write the code to place 1 in register AL if the value in BL is odd. d) Declare two byte values and find the sum of the values and place the value in a byte location called sum, multiply the values and place in a word location called product and divide the values and save the quotient and remainder in byte locations called quotient and remainder.
Chapter4: Processor Technology And Architecture
Section: Chapter Questions
Problem 15VE: A(n) ________________ instruction always alters the instruction execution sequence. A(n)...
Related questions
Question
assembly language
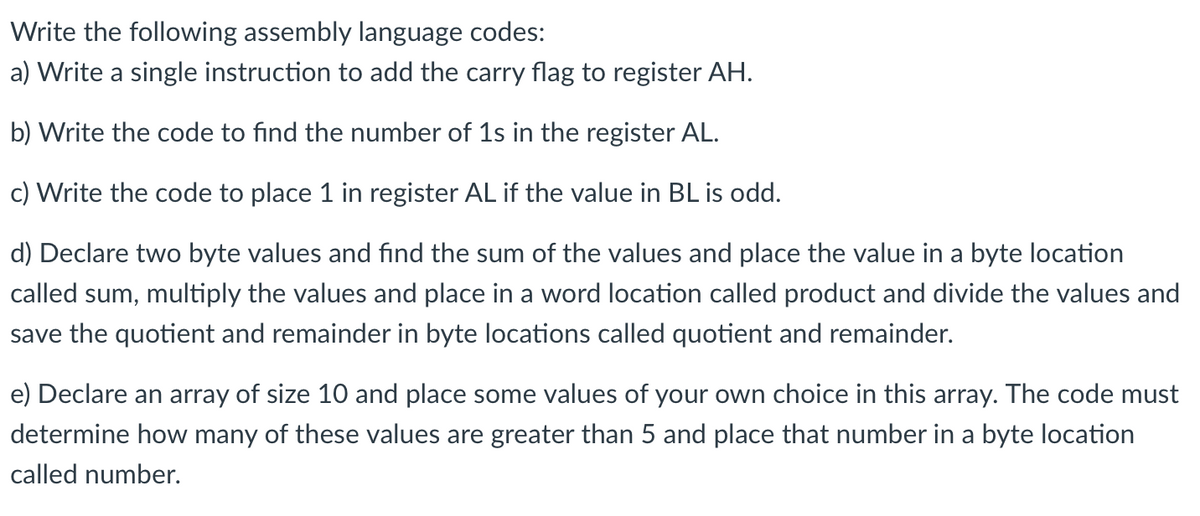
Transcribed Image Text:Write the following assembly language codes:
a) Write a single instruction to add the carry flag to register AH.
b) Write the code to find the number of 1s in the register AL.
c) Write the code to place 1 in register AL if the value in BL is odd.
d) Declare two byte values and find the sum of the values and place the value in a byte location
called sum, multiply the values and place in a word location called product and divide the values and
save the quotient and remainder in byte locations called quotient and remainder.
e) Declare an array of size 10 and place some values of your own choice in this array. The code must
determine how many of these values are greater than 5 and place that number in a byte location
called number.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning