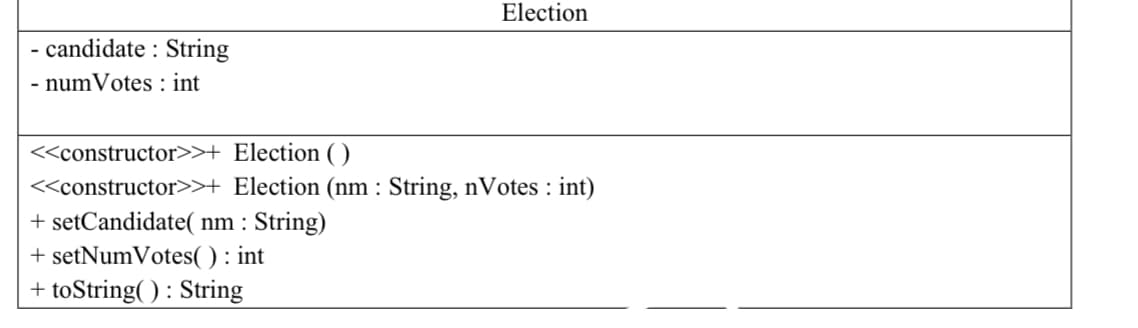
write the following uml in java
Q: In both cases, what is a brute force assault and why are admin/root accounts vulnerable to brute…
A: Given: A brute-force attack is when an attacker tries to guess valid user credentials by trying them…
Q: e to play such a millennia?
A: Computers have been huge since they were first developed, however they are currently universal. As…
Q: What is the endgame for artificial intelligence? Include a synopsis of the different categories, as…
A: Answer: Artificial intelligence's overall goal is to develop technology that allows computers and…
Q: Question 2 Which of the following are not examples of correct usage (conceptually or syntactically)…
A: In this question we have the find the correct implementation of the auto_ptr conceptually and…
Q: Create a Java program that determines if two (2) words rhyme. Write the import statements to be…
A: I have provided JAVA CODE along with CODE SCREENSHOT and 3 OUTPUT SCREENSHOTS---------
Q: Write a C program to find the sum of two dimensional array using Row Block decomposition?
A: I give the code in C along with output and code screenshot
Q: Make a list of the differences between dynamic programming and divide-and-conquer.
A: Your answer is given below.
Q: Find at least three different firms on the internet that provide CASE tools that are either free or…
A: CASE: A CASE tool is a software package that helps with the design and implementation of information…
Q: 1. Create a list of the most significant components of the operating system that uses Visual Basic…
A: VisualBasiWindow: Visual basic window - An IDE window. This window appears when the current…
Q: What do you consider to be one of the most significant uses of AI in the working world today? Have a…
A: Artificial Intelligence Examples: Putting together robots. Autonomous cars. Smart assistants.…
Q: Take, for example, the database of a major airline company that bases its data management on…
A: Analysts of the system: System analysts are the persons who are in charge of designing and…
Q: Let's say that in order for your child to use the internet, they connect on to the school's wireless…
A: Introduction: LAN is a set of linked devices in a building, company, or household.A LAN may range…
Q: In order to redistribute a route into EIGRP, what is the mandatory parameter that must be used? The…
A: Given: Redistribution is the use of a routing system to promote routes learned by another technique,…
Q: The storage of data on the cloud provides a diverse selection of use cases, business strategies,…
A: Microsoft Azure is a cloud computing platform that offers various cloud services, including storage,…
Q: Consider the ways in which you can use Structured English to describe processes that aren't included…
A: Given: The process of doing a system analysis may be defined as "the act of studying a method or…
Q: Please provide examples of each kind of application software and explain the distinctions between…
A: Start: Application software fulfils a particular educational, personal, or commercial role. Each…
Q: Let's have a conversation on the social and ethical repercussions of using and abusing information…
A: The following are examples of social and ethical consequences that might arise from employing and…
Q: Write a statement that prints the word "succotash" to standard output. There should be no white…
A: Program in C++
Q: PLEASE SOLVE THIS IN C++ CODE ONLY! PLEASE READ AND DO THE PROGRAM WITH ACCORDING TO THE CONDITIONS…
A: #include <iostream>#include <string.h>using namespace std; int main(){ string str;…
Q: Create the following Wide Area Network(WAN) design in Cisco Packet tracer. Assign Class 'B' IP…
A: Creating WAN in CISCO Packet tracer
Q: What is the difference between cohesion and coupling in the context of the design and development of…
A: Cohesion and Coupling: The terms "coupling" and "cohesion" define the interactions between modules…
Q: Prim's MST technique may be used to a real-world weighted network.
A: Given: Prim's method (also known as Janke's a algorithm) is a greedy technique in computer science…
Q: What advantages does a hash index table provide?
A: Hash index table: The value in the table's index position is called a hash index. With its key and…
Q: Give the simplest form of F = Y(X + Y) + (X+Y)' Z + YZ a. F= XY + X' Z + XYZ b. F=Y+X' Z OC.F=X+Y' Z…
A:
Q: What procedures are required to install software on a local computer, a portable device, or a web…
A: The above question is solved in step 2:-
Q: Provide an explanation of the idea of portability as it relates to the various programming…
A: Explanation: Portability is a property of programming languages that allows an application to run in…
Q: Consider utilizing structured language when trying to describe processes that do not need systems…
A: Given: Structured Analysis is a development method that uses diagrams to help the analyst get a…
Q: Create five suggestions for possible preventative actions against cyberattacks, and explain why each…
A: Introduction Make five tips for how to protect against cyber-attacks. Engineering Social Behavior:…
Q: Take into consideration the following ten hazards associated with managing IT projects:
A: Start: The following list of the most common project dangers that contemporary businesses may face…
Q: It is possible that further information on the metrics that are used to measure the progress of…
A: You don't have to worry about your software's private or public assets when building it. Because it…
Q: Examine and debate graphical user interfaces.
A: A graphical user interface (graphical user interface) is a system of visually interactive elements…
Q: Find at least three different firms on the internet that provide CASE tools that are either free or…
A: Definition: CASE tools, or computer-aided software engineering tools, are used to handle precise…
Q: Using examples, explain your opinion on the software structure review process.
A: Software Review is a systematic evaluation of the programme carried out by one or more personnel who…
Q: 1. How many stars are outputed when the following code is executed? for (int i = 0; i < 5; i++) {…
A: As per guidelines we are supposed to answer only one question. Kindly repost other questions as a…
Q: There are many different kinds of parts that go into making up an information system.
A: Definition: To acquire, create, and distribute relevant data, people build and use information…
Q: How far along is the Internet of Things now in its development?
A: How far along is the Internet of Things now in its development?
Q: What is the true operation of software project management, and what does the term "project…
A: Project: A project is a set of activities that need to be carried out in order to accomplish a…
Q: Examine the advantages of agile development versus more traditional methods.
A: Types of terrorism definitions: The illegal use or threat of violence to intimidate the population…
Q: Find the inverse of the given matrices using Gauss-Jordan Method
A: Find the required answer with calculation given as below :
Q: Create a rundown of the processes that are followed by the system analyst while assessing a software…
A: Determine: Provide a listing of the system analyst's methods while working with software packages.…
Q: Are there any benefits and drawbacks associated with the use of symmetric encryption methods? What…
A: Lets see the solution in the next steps
Q: A discussion of the consequences that the use of new technologies and their proliferation have for…
A: Issues of social and ethical concern Making the transition to rising growth trends: Multinational…
Q: Find the independence number, clique number, chromatic number, as well as optimal coloring for the…
A: Given graph G contains 12 vertices and between these vertices there are many edges are present.…
Q: What function does the Model-View-Controller (MVC) play in the construction of internet…
A: MVC stands for Model-View-Controller and is regarded as one of the most powerful software and online…
Q: You should make an attempt, preferably by using English that is organized, to describe processes…
A: Given: Structured English is going to be used to explain procedures that have nothing to do with…
Q: Do you think that it is possible to create a fake RSA-based digital signature? Whether you agree or…
A: Install the RSA digital signature system: For signing and validating communications, the RSA…
Q: Which component of the hardware of a device is responsible for making it feasible for the device to…
A: Modem:A modem is a piece of hardware that allows a computer to connect to the internet over a phone…
Q: Which four characteristics are the most important when it comes to developing software? Think about…
A: To Do: To put down the four most significant qualities
Q: When it comes to social and ethical implications, what are the potential effects of AI and robotics?…
A: Given: Artificial intelligence develops computer systems to accomplish activities that need human…
Q: You may find it beneficial to utilize structured English when discussing processes that aren't…
A: Structured English: All logic is expressed in structured English using sequential structures,…
write the following uml in java
Step by step
Solved in 2 steps

- The __str__ method of the Bank class (in bank.py) returns a string containing the accounts in random order. Design and implement a change that causes the accounts to be placed in the string in ascending order of name. Implement the __str__ method of the bank class so that it sorts the account values before printing them to the console. In order to sort the account values you will need to define the __eq__ and __lt__ methods in the SavingsAccount class (in savingsaccount.py). The __eq__ method should return True if the account names are equal during a comparison, False otherwise. The __lt__ method should return True if the name of one account is less than the name of another, False otherwise.code: public class PasswordGeneratorAndStorage {/*** Adds an application to the applications ArrayList. If index is -1, add application* to the end of applications. Else is index is within the size of applications, add* application at that index in applications. Otherwise, return. However, if applications * or application is null, return.* * @param applications* @param application* @param index*/public static void addApplication(ArrayList<String> applications, String application, int index) {// TODO: FILL IN BODY}/*** Generates a random password of length passwordLength and adds it to the end of* passwords if index is -1, or adds it to the index of passwords if index is within the* size of passwords (similar to how the addApplication adds an application). To generate* the random password, use rand to generate a random int within the size of characters. You* can then use this int to grab the char at that index in characters and concatenate that* to your String password variable.…# define stemmer functionstemmer = SnowballStemmer('english') # tokenise datatokeniser = TreebankWordTokenizer()tokens = tokeniser.tokenize(data) # define lemmatiserlemmatizer = WordNetLemmatizer() # bag of wordsdef bag_of_words_count(words, word_dict={}): """ this function takes in a list of words and returns a dictionary with each word as a key, and the value represents the number of times that word appeared""" for word in words: if word in word_dict.keys(): word_dict[word] += 1 else: word_dict[word] = 1 return word_dict # remove stopwordstokens_less_stopwords = [word for word in tokens if word not in stopwords.words('english')] # create bag of wordsbag_of_words = bag_of_words_count(tokens_less_stopwords) Use the stemmer and lemmatizer functions (defined in the cells above) from the relevant library to find the stem and lemma of the nth word in the token list. Function Specifications: Should take a list as input and…
- Not allowed to add variables in brackets next to originIndex * @return index of the point that is closest to the origin, which is (0, 0) In * case of a tie, return the lowest index */ public int closestToOriginIndex() {public List<String> getLikes(String user) This will take a String representing a user (like “Mike”) and return a unique List containing all of the users that have liked the user “Mike.” public List<String> getLikedBy(String user) This will take a String representing a user (like “Tony”) and return a unique List containing each user that “Tony” has liked. create a Main to test your work. import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.ArrayList;import java.util.Arrays;import java.util.HashMap;import java.util.HashSet;import java.util.List;import java.util.Map;import java.util.Set; public class FacebookLikeManager { public List<String> facebookMap; private Set<String> likesSets; public FacebookLikeManager() { facebookMap = new ArrayList<>(); likesSets = new HashSet<>(Arrays.asList("Mike","Kristen","Bill","Sara")); } public void buildMap(String filePath) {…Computer Science JAVA: Fill in the ParsedRequest method in the CustomParser.java file. The point of it is to parse the data that is found in the BasicRequestTest.java file. CustomParser.java: package request; public class CustomParser { public static ParsedRequest parse(String request){ //fill in here } } ParsedRequest.java: package request; import java.util.HashMap; import java.util.Map; public class ParsedRequest { private String path; private Map<String,String> queryMap = new HashMap<>(); private String method; private String body; public String getQueryParam(String key){ return queryMap.get(key); } public void setQueryParam(String key, String value){ this.queryMap.put(key, value); } public void setPath(String path) { this.path = path; } public void setMethod(String method) { this.method = method; } public String getPath(){ return path; } public String getMethod(){ return method;…
- Vigenere.h #include<string>using namespace std;//Create class Vigenereclass Vigenere {//Membersprivate:string key;//Functionspublic://ConstructorVigenere();//Setter and gettervoid setKey(string key);string getKey();//Convert into upper casestring toUpperCase(string k);//Encryptstring encrypt(string word);//Decryptstring decrypt(string word);}; Vigenere.cpp //Implementation#include "Vigenere.h"//ConstructorVigenere::Vigenere() { this->key = "";}//Setter and gettervoid Vigenere::setKey(string key) { this->key = key;}string Vigenere::getKey() { return key;}//Convert into upper casestring Vigenere::toUpperCase(string k) { for (int i = 0; i < k.length(); i++) { if (isalpha(k[i])) { k[i] = toupper(k[i]); } } return k;}//Encryptstring Vigenere::encrypt(string word) { return key; string output = ""; for (int i = 0, j = 0; i < word.length(); i++) { char c = word[i]; if (c >= 'a' && c <= 'z') { c += 'A'…JavaScript //6. addButtonListeners //a. Selects all buttons nested inside the main element //b. If buttons exist: //c. Loop through the NodeList of buttons //d. Gets the postId from button.dataset.postId //e. Adds a click event listener to each button (reference addEventListener) //f. The listener calls an anonymous function (see cheatsheet) //g. Inside the anonymous function: the function toggleComments is called with the //event and postId as parameters //h. Return the button elements which were selected //i. You may want to define an empty toggleComments function for now. Not all tests //will pass for addButtonListeners until toggleComments exists. I recommend //waiting on the logic inside the toggleComments function until we get there.UML diagram for the java code below public class CourseDBManager implements CourseDBManagerInterface { private CourseDBStructure dataMgr = new CourseDBStructure(20); public void readFile(File inputFile) throws FileNotFoundException{ try { Scanner fileData = new Scanner(inputFile); while(fileData.hasNext()) { String id = fileData.next(); int crn = fileData.nextInt(); int numCredits = fileData.nextInt(); String roomNum = fileData.next(); String instructor = fileData.nextLine(); add(id, crn, numCredits, roomNum, instructor); } fileData.close(); } catch(FileNotFoundException e) { System.out.print("File not found"); e.getMessage(); } } public void add(String id, int crn, int credits, String roomNum, String instructor) { CourseDBElement newElement = new CourseDBElement(id, crn, credits, roomNum, instructor); dataMgr.add(newElement); } public…
- Java Program: There are errors in the lexer and shank file. Please fix those errors and there must be no error in any of the code at all. Below is the lexer, shank, and token files. The shank file is the main method. There is a rubric attached as well. Lexer.java import java.util.ArrayList;import java.util.HashMap;import java.util.List; import mypack.Token.TokenType; public class Lexer { private static final int INTEGER_STATE = 1;private static final int DECIMAL_STATE = 2;private static final int IDENTIFIER_STATE = 3;private static final int SYMBOL_STATE = 4;private static final int ERROR_STATE = 5;private static final int STRING_STATE = 6;private static final int CHAR_STATE = 7;private static final int COMMENT_STATE = 8; private static final char EOF = (char) -1; private static String input;private static int index;private static char currentChar;private static int lineNumber = 1;private static int indentLevel = 0;private static int lastIndentLevel = 0; private static…Please draw the UMLfor this code package lap; import java.util.Date; class Covenant { private String name; private String type; private Date dateCreated; private String employeeName; private int employeeID; public Covenant(String name, String type, Date dateCreated, String employeeName, int employeeID) { this.name = name; this.type = type; this.dateCreated = dateCreated; this.employeeName = employeeName; this.employeeID = employeeID; } public void setName(String name) { this.name = name; } public String getName() { return name; } public void setType(String type) { this.type = type; } public String getType() { return type; } public void setDateCreated(Date dateCreated) { this.dateCreated = dateCreated; } public Date getDateCreated() { return dateCreated; } public void setEmployeeName(String employeeName) { this.employeeName = employeeName; } public String getEmployeeName() { return employeeName; } public void setEmployeeID(int employeeID) { this.employeeID = employeeID; }…JAVA – color: String – make: String – model: String – msrp: double + Car() + Car(color: String, make: String, model: String, msrp: double) + getColor() : String + setColor(color : String ) : void + getMake() : String + setMake(make: String ) : void + getModel() : String + setModel(model: String ) : void + getMsrp () : double + setMsrp(msrp: double) : void + toString(): String The Car class will have four attributes/instance variables/fields and 11 methods. CarDealership Class The CarDealership class will simulate a real life automotive dealership. This class will create 3 Car objects and store them in an array named Lot. The class will then display all of the information pertaining to each car (color, make, model, etc.) to the User and allow the User to select one to purchase. Once the User selects a car to purchase, the Car object should be removed from the array (Lot) and another Car object should be put in its place.











