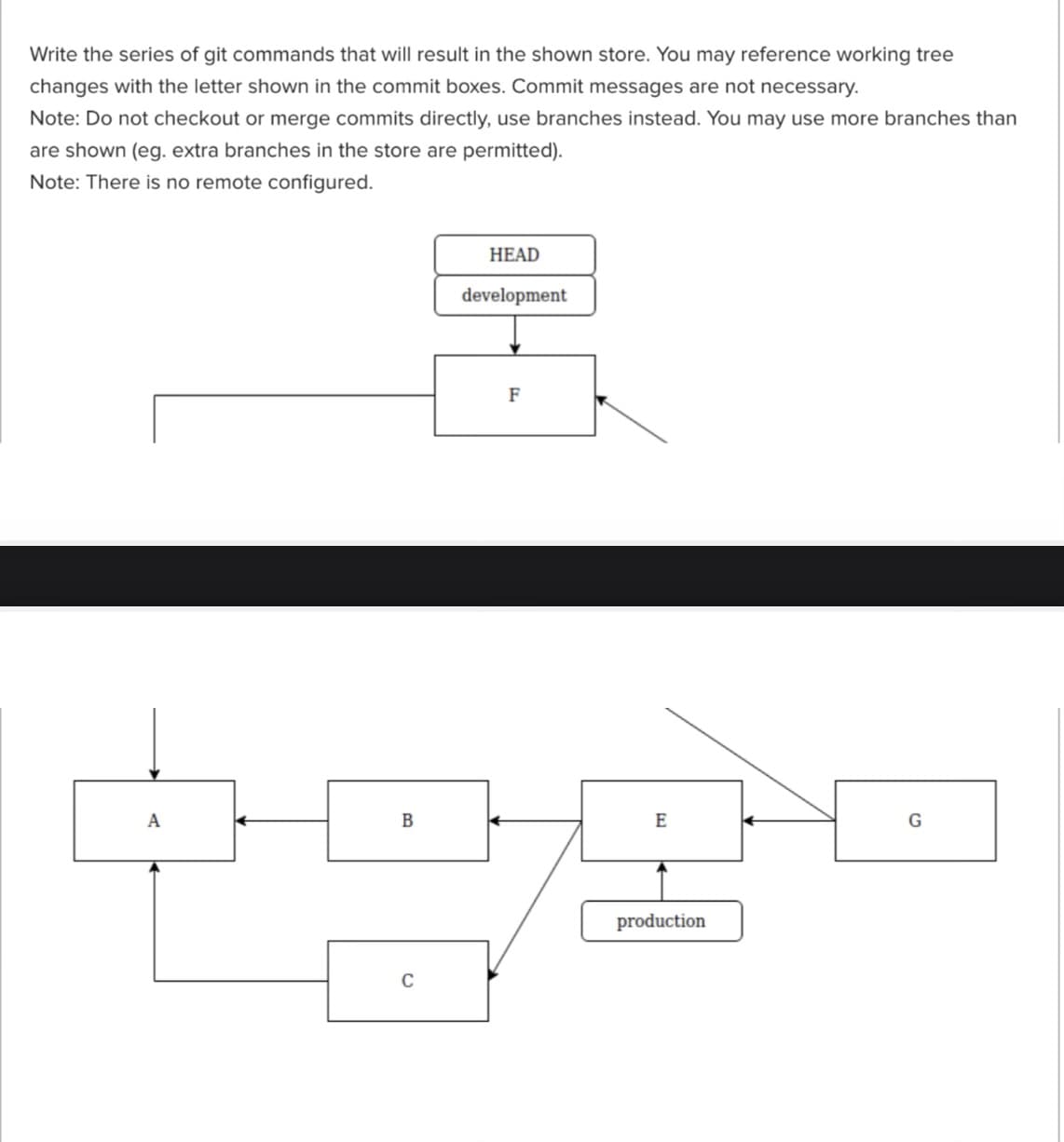
Write the series of git commands that will result in the shown store. You may reference working tree changes with the letter shown in the commit boxes. Commit messages are not necessary. Note: Do not checkout or merge commits directly, use branches instead. You may use more branches than are shown (eg. extra branches in the store are permitted). Note: There is no remote configured. HEAD development F
Q: You are implementing a binary search tree class from scratch, which, in addition to insert, find,…
A: Algorithm: Start Create a TreeNode class to represent each node in the tree. Each node should have…
Q: Capital costs vs. operating expenses: what's the difference?
A: Capital costs and operating expenses are two categories of costs that businesses incur in their…
Q: CREATE IN JAVA PLEASE 1. Create a class named Taxes. 2. Create two instance variables, one variable…
A: Algorithm for Taxes.java: Define a class called Taxes. Create two private instance variables,…
Q: Why is it so difficult for companies to deploy a cloud-based platform, and what are some of the…
A: Cloud based platform refers to the operating system and hardware of a server in an internet based…
Q: Big-existence: why? O's Big-O's worst case? Why worry?
A: The big-O notation is used to calculate how the time needed to execute an algorithm increases as the…
Q: Donot copy any Ai tool otherwise i give downwote Which of the followings are mobile platform…
A: Given options: A) Same risks as any Internet device B) Malware C) Bonets D) vishing/smishing
Q: Please convert to CFG: I want to travel I like Texas I want to swim Go to South Padre Get a…
A: Context-free grammars, also known as CFGs, are formal systems used to describe the structure of…
Q: Can network interfaces share MAC addresses? Why? Why not? Can network interfaces exchange IP…
A: Can network interfaces share MAC addresses? Why? Why not? Can network interfaces exchange IP…
Q: What are the various software issues?
A: Your answer is given below.
Q: Question : Imagine that you track your commute times for (10 days) and recorded your observations in…
A: In this scenario, we have been given a set of observations that represent the commute times for 10…
Q: Show examples of the four network security risks that might harm Internet of Things devices.
A: The Internet of Things (IoT) refers to a network of physical devices, vehicles, home appliances, and…
Q: What does a network router do? Provide at least four points of distinction.
A: The router is a device that directs traffic between different networks, often by connecting them…
Q: If it is possible to construct an optimal solution for a problem by constructing optimal solutions…
A: The dynamic programming technique works by solving the subproblems in a bottom-up fashion, starting…
Q: What's the database's main parts of the database?
A: A database is a collection of data which is stored in organised manner with features of operating…
Q: LO CODE A
A: This is a Python implementation of the BFS (breadth-first search) algorithm with two different…
Q: What are the benefits of implementing a CRM system in a business, and how can it improve customer…
A: Customer relationship management (CRM) is a strategy for controlling how a business interacts with…
Q: software architectural documents provide admin module examples
A: What software architectural documents provide admin module examples?
Q: What responsibilities do device controllers perform?
A: What is device: A device refers to any physical component of a computer system that performs an…
Q: Porque el 1 de mayo es tan importante para los trabajadores
A: In this question we have to understand Why May 1 is so important for workers Let's understand and…
Q: How can wireless Internet affect computer policing growth?
A: Because the wireless internet enables law enforcement organizations to access and analyze digital…
Q: Implement a quicksort with a 2k-sample-size-based sample. The sample should be sorted first, after…
A: Implement a quicksort with a 2k-sample-size-based sample. The sample should be sorted first,…
Q: Using your new found knowledge about full and half adders, you are to build a circuit that can add…
A: Here's the solution for your asked question , hope it helps: To add two, three-digit binary numbers…
Q: You are implementing a binary search tree class from scratch, which, in addition to insert, find,…
A: We must make sure that each node has an equal chance of being chosen before we can use the…
Q: Assembly Language Programming Must show full code and screenshots of outpoyt please. Leap Year The…
A: Given, The month of February normally has 28 days. But if it is a leap year, February has29 days.…
Q: Carpet Calculator The Westfield Carpet Company has asked you to write an application that calculates…
A: PROGRAM: File name: “RoomDimension.java” class RoomDimension{ //declaring instance variables…
Q: Create a programme that will guess a number entered by the user. In this programme, the user will…
A: import math def guess_number(maximum): # Get the secret number from the user secret_number =…
Q: What are some of the key features and functionalities that businesses should look for when selecting…
A: Customer Relationship Management (CRM) software has become an essential tool for businesses of all…
Q: Troubleshoot common Linux hardware, software, file systems, and networks problems.
A: Hardware Problems: No power or the system won't boot up: Check power supply or power cables,…
Q: 60) In a supervisory system in execution mode, the user is provided with an environment graph that…
A: In the System database, variables can be defined to store values, such as user preferences, session…
Q: "Direct access device" in magnetic discs means what?
A: In magnetic discs, a "direct access device" refers to a type of storage device that allows for…
Q: All designs problems are ill-defined. This leads designer to design a machine that, by definition,…
A: Hi. Check below to find your answer
Q: It would be useful if you could elucidate to me what "cloud scalability" means. In cloud…
A: The ability of a cloud computing system or platform to increase or decrease its resources, such as…
Q: Pipelining fails in Princeton computing. Explain and fix this.
A: Pipelining is a technique used in computer architecture to improve the performance of processors by…
Q: Most devices can copy registers both ways. The Memory Address Register (MAR) is always used as a…
A: The Memory Address Register (MAR) is a special type of register in a computer that holds the address…
Q: Which database, MongoDB or Neo4J, would you suggest to the CEO?
A: The Business intelligence tools will play a crucial role in the process of processing and then…
Q: In the realm of information technology, what are some of the most recent advancements that have…
A: What is information technology: Information technology (IT) refers to the use of technology to…
Q: How can software engineering help create software?
A: Software engineering is defined as systematic, disciplined and quantifiable approach for the…
Q: Which operating system differs most between mainframes and notebooks? How do they compare?
A: Operating systems used by mainframes and laptops are distinct from one another and differ greatly in…
Q: How are web-based and conventional software development different?
A: Web-based software development involves building application on mesh browsers, while conventional…
Q: How do computer engineers ensure the security and privacy of computer systems?
A: As the use of computer systems and networks increases exponentially, ensuring the security and…
Q: The binary addition of 1 + 1 + 1 + 1 = __________. 0100 (base 2) 1111 (base 2) 0001 (base…
A: Correct answer is: 0100 (base 2) Explanation: We start by adding the rightmost column, which is…
Q: ageValue and weightValue are read from input. Declare and assign pointer myGoose with a new Goose…
A: Declare double variables ageValue and weightValue. Read input values for ageValue and weightValue…
Q: Why is it that a RISC central processing unit (CPU) is easier to pipeline than a CISC CPU?
A: We must first comprehend what pipelining is and how it operates before we can comprehend why a RISC…
Q: The traversed graph is acyclic if and only if DFS discovers no back edges.
A: Background: In computer science, depth-first search (DFS) is a graph traversal algorithm…
Q: Explain why adding additional cores to a CPU to boost performance and keep up with Moore's Law is…
A: According to Moore's Law, a computer axiom, a microchip's transistor count doubles roughly every two…
Q: Why is IT Stigmergy excellent communication?
A: Stigmergy is a mechanism of indirect communication and coordination between agents in a system…
Q: Discuss at least five (5) challenges Google might face to handle large volumes of data
A: Big data is a term used to describe large, complex, and diverse datasets that cannot be easily…
Q: This work requires you to research prevalent anti-patterns and identify them by Design, Development,…
A: God Object: A God Object is a design anti-pattern where an object knows or does too much. This…
Q: Are there any governance concerns that may arise as a result of shifting from on-premise servers to…
A: What is an on premise server: An on-premise server is a physical server located on-site at an…
Q: How do you feel about the TCSEC orange book
A: The Trusted Computer System Evaluation Criteria (TCSEC), commonly referred to as the Orange Book, is…
Step by step
Solved in 3 steps

- After three records with keys 40, 15, and 18 are inserted into an empty AVL tree, which of the following is correct? Question options: A. a single left rotation is needed at node 18 B. no rotation is needed to maintian AVL tree C. a single right rotation is needed at node 40 D. a single left rotation is needed at node 15solve the question :1- create an AVL tree by inserting the following key:60,20,100,120,80 2- write the necessary command to traverse the tree elements in order. 3- the main class will contain loop Note : write in NetBeanss 8.2After three records with keys 40, 18, and 15 are inserted into an empty AVL tree, which of the following is correct? Question 5 options: no rotation is needed to maintian AVL tree a single right rotation is needed at node 40 a single left rotation is needed at node 18 a single left rotation is needed at node 15
- Which node of the B-tree index contains ROWIDs?a. branch blocksb. root blockc. leaf blocksd. None of the above because the primary key is used to identify rowsconvert UNF for 1NF to 2NF to 3NF, progressively. UNF:Order(OrderID, OrderDate, CustID, CustName, CustPhone, CCNum, CCExpDate, CCBank, BnkContName, BnkContPhone, CustEmail, OrderIP, SiteRefFrom, ShipStreet, ShipCity, ShipSt, ShipZip, OrderLineNum, ItemID, ItemName, ItemDesc, ItemQtyOrdered,ItemListPrice, ItemSalePrice, ItemQtyShip, ShipCharge, Tax, TotalDue)Try switching the joins pthread_join(tid2, NULL); pthread_join(tid1, NULL); Do you see any difference? Please report if and why you do or do not see any difference in terms of the randomness in the result of the shared resource. In the inc_dec_resource() function, implement mutual exclusion (pthread_mutex_lock) to ensure that the result becomes 0 every time when you execute your program. Put your updated code in the report (highlighted) and show your screenshot of the execution by running the script three time using $ time ./shared_resource_mutex. Hint: Your loop is incrementing/decrementing the resource which should be protected by each thread while it is executing that portion. #include <stdio.h> #include <pthread.h> #define iterations 300000000 long long shared_resource = 0; pthread_mutex_t mutex = PTHREAD_MUTEX_INITIALIZER; // Thread function to modify shared resource void* inc_dec_resource(void* arg){ //get the pointer from main thread and dereference it…
- Try switching the joins pthread_join(tid2, NULL); pthread_join(tid1, NULL); Do you see any difference? Please report if and why you do or do not see any difference in terms of the randomness in the result of the shared resource. In the inc_dec_resource() function, implement mutual exclusion (pthread_mutex_lock) to ensure that the result becomes 0 every time when you execute your program. Put your updated code in the report (highlighted) and show your screenshot of the execution by running the script three time using $ time ./shared_resource_mutex. Hint: Your loop is incrementing/decrementing the resource which should be protected by each thread while it is executing that portion. /* Compile: gcc -o shared_resouce_mutex shared_resource_mutex.c -lpthread Execute: ./shared_resource_mutex */ #include <stdio.h> #include <pthread.h> #define iterations 300000000 long long shared_resource = 0; pthread_mutex_t mutex = PTHREAD_MUTEX_INITIALIZER; // Thread function to…Which of the following technique stores data in a separate entity in case of a collision?a) Open addressingb) Chaining using doubly linked listc) Linear probingd) Double hashingIn a B+-tree, it always requires reorganizing the entire index file to maintain performance. True or False?
- You should solve the collisions with chaining by using linked lists and put values to your hash table after hashing your key. When a table element is empty, you can put the value to the place. But when there is a value in the specified place of hashtable, you should use a linked list structure and put the new value at the end of the linked list of that element. For the hash function, inputs and more details, please refer to what ı wrote #include <stdio.h>#include <stdlib.h> #define ARR_SIZE 22#define HASH_SIZE 10 typedef struct HASH_TABLE_s *HASH_TABLE;typedef struct HASH_TABLE_s{ int key; int flag; void *value;} HASH_TABLE_t[1]; typedef struct LINKED_LIST_NODE_s *LINKED_LIST_NODE;typedef struct LINKED_LIST_NODE_s { LINKED_LIST_NODE next; void *data;} LINKED_LIST_NODE_t[1]; typedef struct LINKED_LIST_s { LINKED_LIST_NODE head;} LINKED_LIST_t[1], *LINKED_LIST; LINKED_LIST linked_list_init() { LINKED_LIST new; new = (LINKED_LIST) malloc(sizeof(LINKED_LIST_t));…The rules for deleting a key k from a node n: Rule 1. If n has more than the number of keys and the k is not the largest in n, simply delete k from n. Rule 2. If n has more than the minimum number of keys and the k is the largest in n, delete k and modify the higher level indexes to reflect the new largest key in n. Rule 3. If n has exactly the minimum number of keys and one of the siblings of n has few enough keys, merge n with its sibling and delete a key from the parent node. Rule 4. If n has exactly the minimum number of keys and one of the siblings of n has extra keys, redistribute by moving some keys from a sibling to n, and modify the higher level indexes to reflect the new largest keys in the affected nodes (if necessary).How do you access, modify, or search a BST (Binary Search Tree) containing a set of user IDs and passwords?

