X: y D X 0 0 0 0 1 1 1 1 Output of F(x, y, z) y 0 0 1 1 0 0 1 1 Z 0 1 0 1 0 1 0 1 F 0 0 1 1 0 0 0 0
Q: Show the state of the index after each operation:
A: Extendible hashing is a dynamic hashing method.
Q: LAB: Convert to reverse binary Write a program that takes in a positive integer as input, and…
A: Input: Receive a positive integer x.Initialize an empty string: Create an empty string to store the…
Q: (i) insert, which takes an integer (a key) and inserts it in the binomial heap. The method returns…
A: The implementation of a Binomial Heap, a versatile and efficient data structure, lies at the core of…
Q: Does the Knapsack Problem with b=7994 and the following sequence have a solution?…
A: The rucksack Problem is a well-known optimization problem in which the objective is to ascertain,…
Q: 1. Write a flowchart and C code for a program that does the following: o Declare variables with…
A: Start the program.Declare variables grade1, grade2, grade3 as integers.Declare variable average as a…
Q: Suppose we are developing a program that a car dealership can use to manage its inventory of used…
A: 1. Create an Automobile class - Define class `Automobile` with private attributes: - `make`…
Q: What is a context switch? Explain with a diagram. 10. What is user & kernel Thread? Explain with…
A: We have to understand about the context switching and user & kernel thread, these topic need to…
Q: Choose the correct answer: i. The second generation of mobile communication phones was a) digital b)…
A: As per the company guidelines, since you have posted a question with several sub-parts, we will…
Q: Q.1 Calculate the following: a) Alice and Bob use the Diffie-Hellman key exchange technique with a…
A: In this question we have to solve the following questions:a) Using the Diffie-Hellman key exchange…
Q: Define virtualization and its role in cloud computing.
A: Virtualization is a technology that allows the creation of multiple virtual instances or…
Q: write progra should be able to: at simulates a basic rary catalog system. Display the list of…
A: Initialize a library catalog dictionary and other necessary variables.Read the initial catalog from…
Q: A small Hotel owner wish to computerized the management of hotel operations. You are asked to assist…
A: The objective of the question is to design a database schema for a hotel management system. The…
Q: How are informatics used in public health? Explain with an example.
A: Informatics is a multidisciplinary field that involves the acquisition, storage, processing, and…
Q: Design a 128×16 RAM by adding minimal wiring and logic to two identical 64×16 RAM components.
A: Here, the task mentioned in the question is to design a 128 x 16 RAM from two identical 64 x 16…
Q: (CarbonFootprint Calculator: Arrays of Function Pointers in C) Using arrays of function pointers,…
A: Programming approach:- Startincluding necessary header files.declaring method building.declaring…
Q: 1.THE BANKER'S ALGORITHM FOR A SINGLE RESOURCE o It is modeled on the way a small-town banker might…
A: The Banker's Algorithm, a pivotal concept in operating systems, ensures the prevention of deadlock…
Q: C++
A: In step 2, I provided the answer with a brief explanation...
Q: 20. When should a server begin looking for signs of impairment?
A: In the realm of database technology, the server should begin looking for signs of impairment when…
Q: What are the steps in a linear search algorithm? It searches all the elements in a vector until it…
A: A linear search algorithm, also known as sequential search, is a simple method for finding a…
Q: Discuss the impact of artificial intelligence and machine learning on cloud services.
A: Artificial intelligence (AI) and machine learning (ML) have had a significant influence on cloud…
Q: 1. Which fields of the IP header change from router to router? 2. Calculate the HLEN value if the…
A: One of the most important parts of network communication is the IP (Internet protocol) header, which…
Q: Highlight the considerations when choosing a deployment model.
A: Choosing the deployment model is a decision, in computer science. It decides how a software…
Q: Given any two distinct vertices of a tree, there exists a unique path from one to the other. I need…
A: Imaginе a lush forеst of knowlеdgе, its branchеs intеrwеaving to form a trее of connеctions. You…
Q: Alice and Bob want to use Diffie-Hellman Key Establishment to share a key and they have agreed to…
A: To determine the suitability of g for Diffie-Hellman Key Establishment, we need to check whether…
Q: Identify THREE key factors for defining a robust key to enhance algorithm security? Explain your…
A: The solution is given in the below steps
Q: Write a pseudocode and draw a flowchart to display the n terms of harmonic series and their sum. 1…
A: In step 2, I have provided PSEUDOCODE...In step 3, I have provided FLOWCHART...In the final step, I…
Q: Given two input integers for an arrowhead and arrow body, print a right-facing arrow. Ex: If the…
A: In this question we have to understand about the program requirement to form an arrow head and body…
Q: Consider the Extendible Hashing index shown in figure below: 2 12 20 00 01 10 11 2 Show the state of…
A: Extendible hashing is a dynamic hashing technique used in computer science to efficiently manage and…
Q: In class HashTable implement a hash table and consider the following:(i) Keys are integers…
A: The question is asking to implement two classes, HashTable and HashTable2, which are hash tables…
Q: Name 2 scheduling algorithm’s
A: Two fundamental scheduling algorithms are widely employed: "First-Come, First-Served (FCFS)," which…
Q: The Galactic Federation is implementing a new security protocol for access to classified…
A: Create a function is_prime to check if a number is prime.Create a function validate_access_code that…
Q: I have a problem with my code in java, replit. When I run my code in the console, the output for the…
A: To address the issue with the null values for the player's name and the default values (0, 0, 0) for…
Q: what is the meaning of Processor coupling?
A: Processor coupling refers to the degree of interdependence or coordination between different central…
Q: What is the output of the following Python code: print('CCCC chegg a) ['chegg India'] b) ['chegg',…
A: In this question we have to understand about the given python code for the correct output.Let's…
Q: /* Using JAVASCRIPT write a function that iterates through the given object and displays the…
A: Iterate through each book in the person's favorite books list.Display each book in a readable…
Q: # Define a function named display_bookstore_info that prints information about "Book Haven". # The…
A: Print welcome message and store location.Create a list of genres and print them.Print a special…
Q: So my teacher gave HW and I need help matching the answers to the right descriptions.......
A: The objective of the question is to match the correct terms with their respective descriptions in…
Q: 1. Prepare a list of orders by Shipper showing the Shipper ID, Order ID, Product ID and Quantity.…
A: In this question we have to understand about given SQL database and prepare the list of queries…
Q: Please I want a solution with drawing 2. Explain process state with the help of diagram. 3. Explain…
A: This question is from the subject Operating System. Here we have to define process state &…
Q: 1)Discusss the security aspects of gmail system
A: The objective of this question is to understand the various security measures that Gmail, a popular…
Q: In C++, can you provide a simple string Null Termination Error program and then show how to fix it…
A: Algorithm: Finding Maximum NumberInput: Array of integers arr[], Length of array nOutput: Maximum…
Q: # Define a function named display_store_info that prints information about Indian Meubles. # The…
A: This is a Python programming question. Here we are dealing with python function. A function is a set…
Q: Explain the basic concept of cloud computing.
A: The use and manipulation of data via computers, including data storage, processing, analysis, and…
Q: Modify the program for carrying out compound interest calculations given in Example 5.2 so that the…
A: Define a function named compound_interest that takes three inputs:P: the principal amountr: the…
Q: Explain replace and translate functions in Oracle sql
A: The TRANSLATE function in Oracle SQL is used to swap out one set of characters for another when it…
Q: Question 3: A graph G has order 24 and size 72. The degree of each vertex is 3, 6 or 9. There are 6…
A: When dealing with a graph, the order signifies the total number of vertices, while the size reflects…
Q: What is an operating system? Provides a link to interface the hardware and application programs…
A: Operating System:An essential software element that acts as a mediator between user programs and…
Q: Discuss the challenges associated with scaling applications in a cloud environment.
A: Scaling applications in a cloud environment introduces a set of challenges stemming from the dynamic…
Q: How do you build a C++ program that asks the user to enter three integer values as input and stores…
A: Below is C++ program that prompts the user to enter three integer values, stores them in variables,…
Q: What are some common C++ string manipulation errors that can be encountered? How can these errors be…
A: The objective of this question is to identify common errors that can occur when manipulating strings…
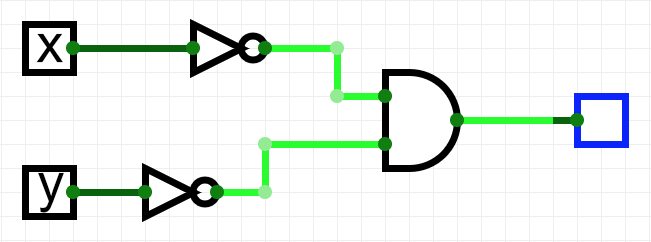
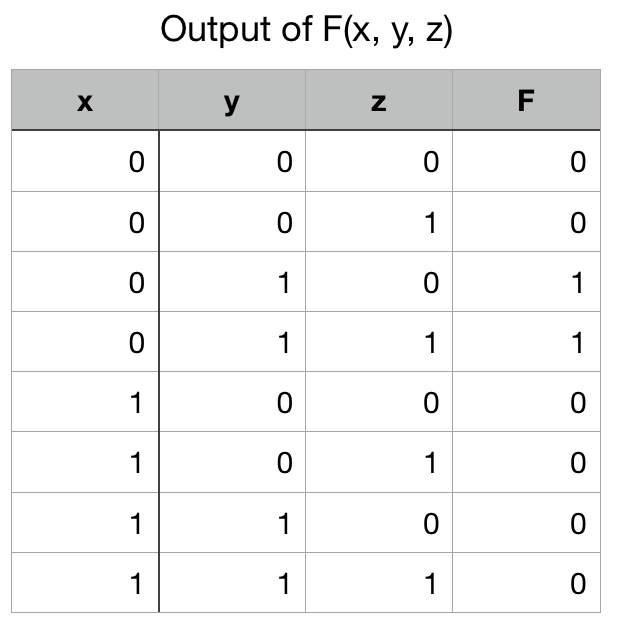
Output of F(x, y, z)
For the truth table above, what logic circuit below represents it?
Unlock instant AI solutions
Tap the button
to generate a solution
Click the button to generate
a solution
- 7. Compute the minimum hamming distance of the following four code words correctly1110001110010111100101101000111000101111011011111100000000011111 PS: Please do them in a word processor not hand-written!7. Compute the minimum hamming distance of the following four code words1110001110010111100101101000111000101111011011111100000000011111 PS: Please do them in a word processor not hand-written!1024 bytes X 1 kilobyte is equal to
- Computer Science write down the machine code; MOV DX, 5 MOV AX, 0B000H MOV ES, AX MOV D1, 1454 ; 1454 = 05AEH SUB CX,CX OUT 43H, ALCompute the Hamming distance of the following code words: 0011010010111100 0000011100001111 0010110110101101 0101011010011110 Please show all working understandable. THANK YOU VERY MUCHExplain why the Hamming Error Correction algorithm is significant.
- (a) Find the length of each side of a square computer chip with 580 million transistors, if each transistor occupies a square of side 45 nm. (b) Find the number of transistors on a chip of the same size you found in (a) if the transistor size can be reduced to 32 nm on a side.Microprocessor(Binary number) solve the ff with solution 1. 1000000 – 1100011 – 1001002. 111+ 101101 + 110010 + 1113. 101111 + 101011 - 1014. 11100 + (1011001 – 101011)5. 101000 + 110110 - 111116. 1100110 – 1111 – 1101107. 101010 + 100001 - 100118. 100100 + 111000 - 111109. 1100011 - 11011 – 11111110. 1010011 – 101001 + 1111119. Find the quotient and remainder for the following modulo 2 division problems correctly.a. 1000102 / 10112b. 11101112 / 1002 PS: Please do them in a word processor not hand-written nor in a JPEG screenshot Format!!

