mov edx,1 mov eax,7FFFh
Q: 3. For the RSA algorithm with a large n, explain why Bob can calculate d from n, but Eve cannot.
A:
Q: Older compilers were designed according to a pipe and filter architecture, in which each stage would…
A: The design goals that may have triggered the shift from pipe and filter to repository architecture.
Q: Show how STS-9's can be multiplexed to create an STS-36. Is there any extra overhead involved in…
A:
Q: parent's message buffer, what happens normally?
A: The answer is
Q: Please attach a picture,I need downloadable images as an answer. The RL can be implemented without…
A:
Q: It is clear that a software development project carried out by a software house for a specific…
A: 1) The answer is unequivocal YES. Why? Because a customer-supplier relationship is nothing more than…
Q: The TCP/IP Networking Model is called a "de facto" standard, while the OSI Networking Model is…
A: TCP/IP networking model (De facto standard) The third type of the standard often seen in the…
Q: WHAT IS THE RELATION OF METASTABILITY TO MEMORY ELEMENTS?
A: metastability denotes an intermediate energetic state within a dynamical system other than the…
Q: How does IPSec create a set of security parameters?
A: Introduction: IPsec was at first evolved on the grounds that the most well-known web convention,…
Q: What is the difference between what a switch does and what a router does? Why do we need both?…
A: What is the difference between what a switch does and what a router does? Why do we need both?…
Q: Indicate what will be displayed after the following do-while loop has been executed. ShowAnswer…
A: while loop executes until the condition passed to it becomes false. Here condition passed is…
Q: Compare and contrast byte-stuffing and bit-stuffing. Which technique is used in byte-oriented…
A: Answer: We need to write the differences between the byte-stuffing and bit-stuffing . so we will see…
Q: 90 Q6.1 Kruskal 0 40 50 80 130 110 70 S 150 60 30 10 120 140 20 100 List the weights of the MST…
A: Steps: 1. Sort all the edges in non-decreasing order of their weight. 2. Pick the smallest edge.…
Q: s of operating s
A: Operating system: An operating system (OS) is system software that oversees PC hardware, software…
Q: olve expresssion and draw also.
A: - With the restrictions placed on us because of our guidelines we are allowed to answer the first…
Q: (Time in Seconds) Write a function that takes the time as three integer arguments (forhours,…
A: Lets see the solution.
Q: Briefly describe the issues involved in using ATM technology in LANS.
A: ATM stands for Asynchronous Transfer Mode. For transmission of data from source to destination it…
Q: We have discussed greedy algorithm during lectures. A greedy algorithm is an algorithm that…
A: The correct answer for the above mentioned question is given in below steps.
Q: (Recursive Exponentiation) Write a recursive function power(base, exponent) that wheninvoked…
A: Lets see the solution.
Q: Q: One way to handle parameter conversion in RPC systems is to have each machine send parameters in…
A: First of all, when one computer sends byte 0, it always arrives in byte 0. Thus the other side…
Q: Consider a workflow system supporting software developers. The system enables managers to model the…
A:
Q: QUESTION 26 Given: vector mag = 78,107, 37,102, 37, 120, 121, 122, 105, 106, 115, 121, 37, 120,…
A: The above question is solved in step 2 :-
Q: Can the system under consideration be represented as an actor? Justify your answer.
A: System under consideration is a system which is taken as a main focus on which every thing is…
Q: Please code this in Java. Write a program to input a phone number and output a phone directory with…
A: Hello student Please do like if this solution will help you I really work hard for getting accurate…
Q: Define the concept of a unified memory architecture.
A: The answer for the above mentioned question is given in the below steps for your reference.
Q: Assuming no padding, does the efficiency of ATM using AAL3/4 depend on the size the packet? Explain…
A: Introduction: Padding: It is the addition of additional bytes that do not contribute to the payload…
Q: ached below the
A: According to the question I have created or made a vector of integers here and then stored the data…
Q: Q: Consider Globe. Outline a simple protocol by which a secure channel is set up between a user…
A: Please find the detailed answer in the following steps.
Q: Define a function trophic_class(trophic_level_index) which returns the trophic classification (as a…
A: Here is the python solution for the above problem using if statements. (# indicates comments in…
Q: Experiment with Hypercard or another hypertext system if you have access to one. As you work through…
A: Introduction This is associate degree experimental exercise which needs access to a object-oriented…
Q: What is the difference between serial and parallel port ?
A: S.NO SERIAL PORT PARALLEL PORT 1. Serial port is used to achieve serial transmission. While…
Q: Outline a simple implementation of a fault-tolerant JavaSpace.
A: Fault tolerance refers to the ability of a system (computer, network, cloud cluster, etc.) to…
Q: In 1-2 sentences explain the difference between cyber forensics and data recovery. In 1-2 sentences…
A: STEP BY STEP COMPLETE SOLUTION REGARDING YOUR PROBLEM WITH EXPLANATIONS :
Q: Describe how testing activities can be initiated well before implementation activities. Explain why…
A: Introduction: Let’s examine this in exceptionally easier words for better comprehension. Testing…
Q: (Towers of Hanoi: Iterative Solution) Any program that can be implemented recursivelycan be…
A: (Towers of Hanoi: Iterative Solution) Any program that can be implemented recursivelycan be…
Q: What is the difference between status meetings and decision meetings? Should they always be kept…
A: Status meetings are periodically scheduled events at different levels in which information relating…
Q: What are the relative advantages of flat staffing versus gradual staffing?
A: A flat organization refers to an organization structure with few or no levels of management between…
Q: Explain the relative advantages and disadvantages of an embedded OS based on an xisting commercial…
A:
Q: Q: Consider Globe. Outline a simple protocol by which a secure channel is set up between a user…
A: Consider the replica R that we found on the other side, in that case, we execute some steps that are…
Q: What is the minimum number of cells resulting from an input packet in the AALS layer? What is the…
A: The answer to the question is given below:
Q: What is the purpose of the Record Protocol in SSL?
A:
Q: Why is Frame Relay a better solution for connecting LANs than T-1 lines?
A: .
Q: Compare and contrast byte-oriented and bit-oriented protocols. Which category has been popular in…
A:
Q: First, read in an input value for variable valCount. Then, read valCount integers from input and…
A: count() is used to return a number of occurrences of an element in a given range. Please find the…
Q: are action buttons and how are they used in microsoft powerp
A: Points: PowerPoint is a part of the Microsoft tool. There is a lot of in-built button on…
Q: Write a program that takes an integer list as input and sorts the list into descending order using…
A: Note: The correct code and output attached below. If you have any further query please let me know…
Q: rite a program that asks the user to enter an integer consisting of 4 digits only, and check w many…
A: Code is given below #include <iostream>using namespace std;int main() { int num,…
Q: What are the major achievements of computer vision? What are the major problems that remain to be…
A:
Q: Someone has attempted to censor my strings by replacing every vowel with a Luckily, I've been able…
A: You have not mentioned any specific language so I provide the code in JavaScript along with output…
Q: (a) How should the description in Problem 5.30 (a) be written to have the same behavior when the…
A: In verilog, (<=) operator is termed as non-blocking assignment operator.In this,the assignment…
dont dont dont post copied and exissting strict action skip if dont know
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Please do this question through https://cpulator.01xz.net/?sys=arm-de1soc Assembly language using ARM Write an assembly language program that uses 3 registers. R0,R1 and R2 . The registers should have values 2, 5, and 0, respectively. The program will add, sub, divide and multiply the contents of the Register R0 to that of R1 and store the result into R3.The following assembly language intruction contains ERRORS: Line 1 MOV 23,AX Line 2 MOVE TOTAL,BX Line 3 MOV IP, DX Line 4 MOV AX, DL Line 5 DIV AL, CL What are the errors? identify and write the correct instuctions.Microprocessor 8086 Code Mov 0058H ,04H Mov 0053H,06H So when I calculate physical address in formula Ds*10+offset address I get my Ds indicates 3000 So 3000*10+0058=30058 physical address When try to find 30058 in the memory location in emu8086 I couldn’t find this physical address in the memory but I see another address is that I am wrong in this way What want to do is When go to 30058 physical address in this address to value of 04H on its data a m wrong?
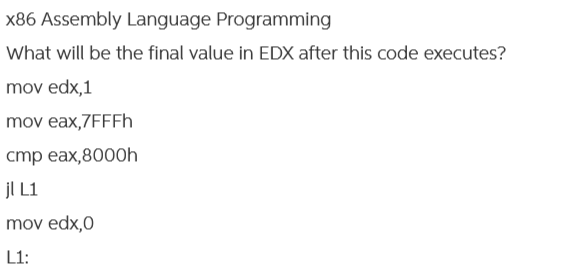
- VMware and VirtualPC execute all x86 instructions in the exact same manner as a real x86 CPU would Group of answer choices True Falsemicroprocessor 8086/8088 which one and how ? Assume the content of the segment register ES = ACEE H, the possible value for segment register CS= ? CS=B822H CS=A215H CS-ACEEH CS=2ED5HSubject: Assembly Language Q: What will be the final value of EAX in this example? mov eax, 0 mov ecx, 10 L1: mov eax, 3 mov ecx, 5 L2: add eax, 5 loop L2 loop L1
- Explain the interfacing operation of 8259A with 8086 system? Write the Operation command word formats (OCW1, OCW2 & OCW3) of 8259A.The MSP430 can move/copy a byte or a word at a time using the instructions mov.b and mov.w respectively. In particular, the instructions mov.b &source_address, R4 mov.w &source_address, R4 copy the byte or word that resides at the given address (&source_address) to the given destination (the core register R4 in the CPU). Which of the following instructions are valid? (a) mov.b &0x1C03, R4 (b) mov.w &0x1C02, R4 (c) mov.b &0x1C00, R4 (d) mov.w &0x1C05, R4using the tasm syntax (intel style), write a x86 assembly code that does the following tasks: (a) add two groups of numbers using the loop instruction, 1 + 3 + 5 + ... + 99 2 + 4 + 6 + ... + 100 (b) print the two results on the screen. (c) the code must be assembled/built/run successfully with the gui_tasm software
- Rearrange the steps for X86 interrupt processing: a. Save current processor status word (condition codes) b. Switch to kernel mode c. Interrupt handler saves registers it might clobber d. Save current program counter e. Switch to kernel stack; put SP, PC, PSW on stack f. Vector through interrupt table g. Save current stack pointer1- What is the X86 architecture family of the Intel? 2- What is the proposed work that the authors were trying to implement by doing their study? 3- Discuss the performance of 8086 microprosseors identified by the author of paper? 4- What is floating point number? How 8086 prossors improve floating point computation performance. 5- Discuss various feature of 8086 CPU as identified by the authors.Which of the following two systems is better?• A program is converted into 4 billion MIPS instructions by acompiler ; the MIPS processor is implemented such thateach instruction completes in an average of 1.5 cycles andthe clock speed is 1 GHz• The same program is converted into 2 billion x86 instructions;the x86 processor is implemented such that each instructioncompletes in an average of 6 cycles and the clock speed is1.5 GHz



