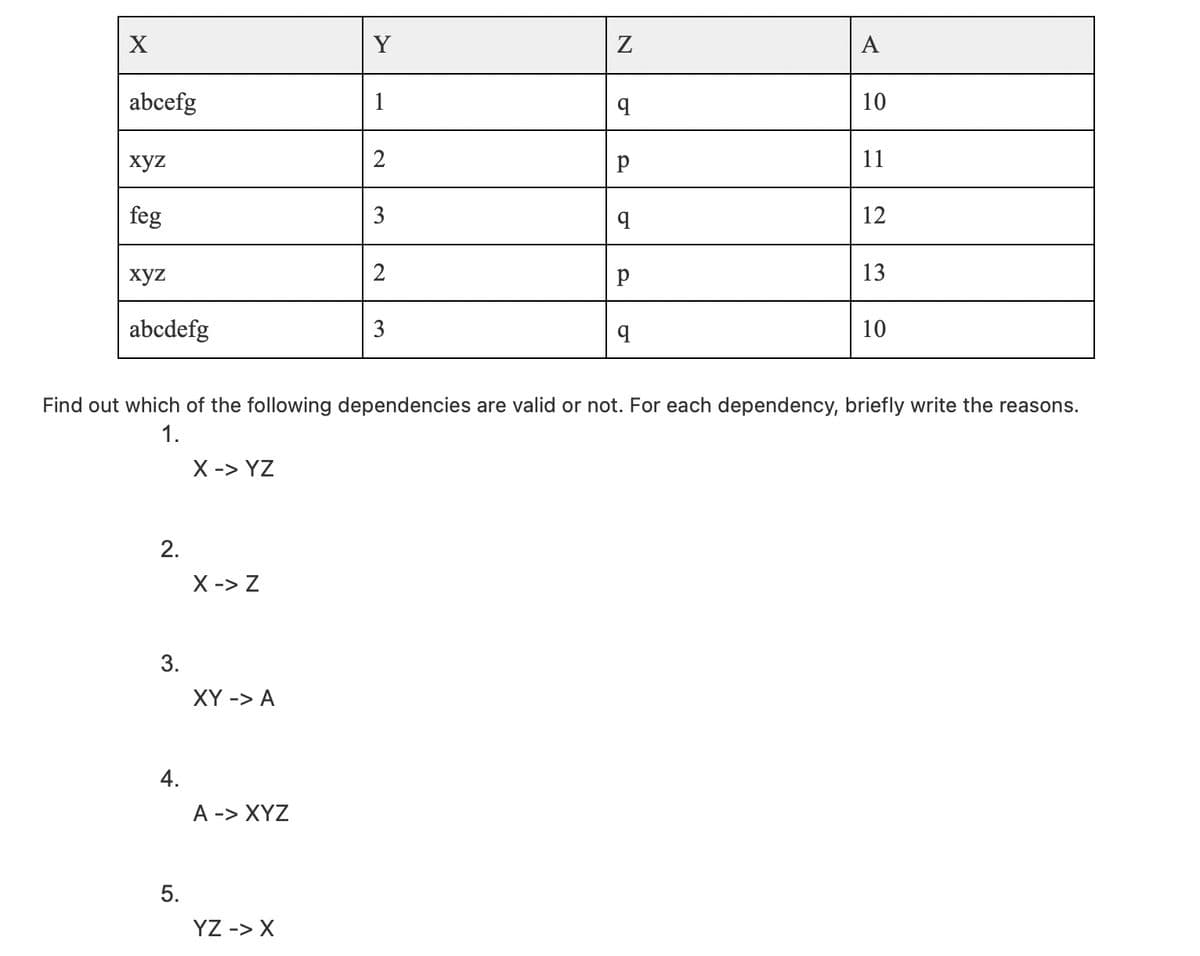
Y A abcefg 1 10 хуz 2 11 feg 3 12 xyz 13 abcdefg q 10 Find out which of the following dependencies are valid or not. For each dependency, briefly write the reasons. 1. X -> YZ 2. X -> Z 3. XY -> A 4. A -> XYZ 5. YZ -> X 3.
Q: Create a program using a loop in C++ and ARM Assembly language that executes the following: The…
A: Program in c++: #include <iostream> using namespace std; int main() { int a=-30,b=96;…
Q: What is the function of the Toolbox when it is used inside the Visual Studio environment?
A: Toolbox: Normally concealed along the left side of the Visual Studio IDE, the toolbox becomes…
Q: Software development is a four-step process. What are the steps?
A: Software Development: Software development is a collection of computer science activities concerned…
Q: reachability in Prolog with and without labeling.
A: Reachability in Prolog: The possibility is explaining below:
Q: Why do we use function prototypes?
A: According to the Bartleby guideline we are suppose to answer only one question at a time. Kindly…
Q: hich of these collections can you not iterate over dex or key value of?
A: Lets see the solution.
Q: Write C++ program, to read 3*4 20- array, then replace each value equal S with o
A: Step 1 : Start Step 2 : In the main function , declare the array variable arr with size 3x4. Step 3…
Q: Question 22 Not yet 1.7-1 Networking history - when did it happen? Match the networking event with…
A:
Q: What order is an algorithm that has as a growth-rate function 8*n° - 9*n O 0(8 * n°) O O(n* * n) O…
A: For the given growth-rate function: 8n3 - 9n The highest power term is 8n3.
Q: -An ISP is granted the block 80.70.56.0/21. The ISP needs to allocate addresses for two organization…
A: The answer is
Q: Write a code to delete a node from a Binary search tree. The format of the function is void…
A: Start. Check if the tree is null or not. If not then repeat the function with next node if the key…
Q: Which functional units are often present in a microcontroller?
A: Microcontroller: A microcontroller is a small integrated circuit that is used to manage a particular…
Q: 6. [::] 0 1 2 3 - Find A X B A = 3 4 5 B = 9. 10 11 00
A: Dear learner , hope you are dong well , I will try my best to answer this question. According to our…
Q: What are the four essential activities of software development
A: Software development model is the process to develop any software which include from requirement…
Q: What do you mean when you say "header-based vulnerabilities"? Please provide three instances.
A: Introduction: Here we are required to explain what is header-based vulnerabilities, and list three…
Q: Using the code below, answer the following questions: 1) What are each of the 3 functions…
A: NOTE - As per our guidelines we are supposed to answer only the first three parts, please re-submit…
Q: Software development is a four-step process.
A: answer is
Q: There are several stages that go into creating software. Find out when and how to utilise each kind.…
A: Software: A collection of instructions, data, or programs used to control computers and perform…
Q: Q2: In a wireless network company, one user create a signal for call making. IT officer is asked to…
A: Fork() System Call Fork system call is the function which is use to create a child process from a…
Q: What is the difference between the two in terms of the creation of computer programmes?
A: The two main types of software are system software: One distinction is that computer science…
Q: Write a Java class that populates an array of 20 random ints between 0 and 100. Write two methods:…
A: Step 1 : Start Step 2 : Define a method getLargest() which accepts an array and returns the largest…
Q: Write a C programme to determine if a given number can be expressed as the sum of two prime numbers.…
A: Here I written C program for given problem. I hope you like it.
Q: How can you transition to a different form in Visual Studio
A: Answer :
Q: Q2: Based on Diffie-Hellman protocol, if the public key is g = 23,p = 449, and c = 141. Find the…
A: a=20
Q: Write method findZero, as started below. findZero should return the index of the first element of…
A: Iterate from 0 to pos Check for 0 If found, return the index
Q: In terms of the graph ADT implementation, when is an adjacency list better to use than an adjacency…
A: We are going to understand when using adjacency list is better than using adjacency matrix and also…
Q: Computer Science C Language program break and continue statement do # 2 nested loops. modify make…
A: The break and continue statements are important because these statements are used to jump out of…
Q: Given the Bayesian network shown in the attached figure that establishes the relations between…
A: The probability here is computed as:a) P((burglary = false) ∧ (earthquake = true) ∧ (alarm = false)…
Q: The content of registers and memory are summarized as follow: R0=0x24682244 R1=0x00446688…
A: 1. Movs instruction moves the content to destination and sets the condition code flag depending upon…
Q: The property of a control determines whether or not it is shown on the form during runtime, much…
A: Attribute Control : Attribute Control Charts are a group of control charts explicitly created for…
Q: 5) Let's say you and your friend are trying to predict the outcome of a flip of a coin. In MATLAB,…
A: Answer
Q: 1. Write the SQL code that will list all employees with Job_cod and Job_description. 2. Write the…
A: According to Bartleby rules, we are answering the first 3 questions. The queries are given below
Q: Part 3: Exercises 1. Calculate the sum of series of odd numbers from the list of numbers. The length…
A: Answer
Q: A database may be 1) Distributed over separate locations, but must be processed by a single…
A: A distributed database is a database that consists of two or more files located in different sites…
Q: Do you know what makes certain software projects more challenging than others?
A: Software projects can having the lot of challenges because of the end user satisfaction always end…
Q: What sort of variable is required to use an object in code?
A: According to the question the data type identify the value with object variable in the code always…
Q: Construct a truth table for (p V (~p V q))^ ~ (q^ ~ r).
A: We are given an expression which has 3 variables p,q and r and we are going to make truth table for…
Q: What is the significance of discrete event simulation?
A: Discrete event simulation: Simulation of discrete events. A stochastic mathematical modelling tool…
Q: What drove the evolution of computer programming languages?
A: Programming languages is the indeed the fundamental unit of today's tech world. It is considered as…
Q: Are there any drawbacks to adopting B2C? Explain.
A: Business-to-Consumer(B2C): The phrase business-to-consumer (B2C) refers to the process of selling…
Q: How is a hash value safeguarded for message authentication? Can a MAC algorithm be exploited without…
A: Benning: hash function is generated by the sender combining a message with some symmetric key,…
Q: a. Explain why we need hash tables and explain the two main components of the hash tables with an…
A: Part a: The need for a hash table is to directly access an element by using a key value. For…
Q: 6. [::] 0 1 2 3 - Find A X B A = 3 4 5 B = 8 9 10 11 %3D
A: Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: The class dateType defined in Programming Exercise 6 prints the date in numerical form. Some…
A: extDateTypeImp.cpp #include <iostream>#include "extDateType.h" using namespace std;//define…
Q: One of the questions to be considered at the maintenance stage of the Software Development Life…
A: SDLC is for Software Development Life Cycle. It is an organized process that allows for the…
Q: Something important that software engineering does not account for is not taken into account.…
A: Inability To Recognize The Business's Needs: The failure of software initiatives is due to a lack of…
Q: What is the output of the following code? #include iostream void myFunction( int &a ); using…
A: First let's understand the code properly to know what it will print . The code is very simple . The…
Q: Name three virtualization tools. Contrast them
A: The Virtual machine software helps in simulating the environment by using one hardware that is also…
Q: how large integer number does python can be store?
A: answer is
Q: When it comes to software development, what are the four most important activities?
A: Given: Software development is the process of generating and maintaining applications, frameworks,…
Step by step
Solved in 2 steps

- Consider the following schedule of transactionsW1(A) W2(A) W1(A) W2(A) W1(A)Which of the following properties are true for the above schedule and justify the reason for your answer with explanation?a) Conflict Serializableb) View Serializablec) Recoverable Please answer these question in detail with full explaination. I need a proper long answer. Thanks :)List all nontrivial functional dependencies satisfied by the below A. B. Ca1. b1. c1a1. b1. c2a2. b1. c1a2. b1. c3Which of the followings can possibly be a canonical cover Fc of a set F of functional dependencies? (The actual set F or the actual relation R is not required to answer this question.) (a) {A → B,B → D,B → C}(b) {A → D,AB → C,D → B}(c) {A → B,AB → B,C → D}(d) {A → C,D → B,AB → C}(e) none of the above
- Which of the following functional dependencies are satisfied (and not satisfied) by this relation and Why? (a) A → B Why? (b) A → CD Why? (c) AB → CD Why?Which of the following functional dependencies are satisfied (and not satisfied) by this relation and Why? (g) AD → BC WHY? (h) D → B WHY? (i) D → C Why? (j) C → D Why?Assume each bank branch can issue loan independently of other branches and assumecustomers may jointly make a loan. Which of the following is correct functional dependency for the tableLoans (CustomerID, Branch, LoanNo, LoanAmount)?A) CustomerID --> LoadNo, LoanAmountB) CustomerID, Branch --> LoanNo, LoanAmountC) LoanNo, Branch --> CustomerIDD) Branch, LoanNo --> LoanAmountE) LoanNo --> LoanAmount
- Which of the following has no repeating groups but can contain partial or transitive dependencies? unnormalized data 1NF 2NF 3NF18. Which is not a desirable property of a transaction ? a. Isolation b. Atomicity c. Durability d. All are desirableIn the table Enrollments (studentID, courseNo, sectionNo, grade, status), which of the followingfunctional dependency is true?A) studentID --> gradeB) studentID, courseNo, sectionNo --> grade, statusC) studentID, courseNo --> grade, statusD) grade, status --> studentID, courseNo, sectionNo
- Database Systems Question 1. A B C D 1 20 M 101 2 21 N 102 3 22 O 103 1 21 M 104 4 22 O 105 Find out which of the following dependencies are valid or not. For each dependency, briefly write the reasons. A -> BCD AB -> C AB -> D D -> ABC BC -> ASuppose a user creates a new relation r1 with a foreign key referencing another relation r2. What authorization privilege does the user need on r2? Why should this not simply be allowed without any such authorization?Please help me with this assignment 1. Open and examine the following ERR design file people.mwb (https://acconline.austincc.edu/bbcswebdav/pid-18686108-dt-content-rid-70255490_1/xid-70255490_1) a. Each person is described by their name and email.b. Each person can be registered in multiple countries.c. Ensure it is in 3rd normal form.d. Ensure the relationships and primary and foreign keys are correct. 2. Create a database from the design. 3. Import the following data into the database people.txt (have to modify the data to match the design) people.txt Email,Full Name,Country,Date RegisteredCarley_Bahringer@destiny.com,Carley Bahringer,Brazil,1987-10-03 22:09:54Patricia_Fadel@avis.com,Patricia Fadel,Chile,2012-05-10 11:07:49Sedrick@godfrey.ca,Sedrick Kuphal,Chile,2007-11-12 00:09:53Briana_Berge@axel.ca,Briana Berge,Iceland,2006-03-26 15:32:08Lucy_Lockman@abby.org,Lucy Lockman,Iceland,2014-02-13 10:26:57Lucy_Lockman@abby.org,Lucy Lockman,France,1999-02-12…

