You have installed Qualys cloud Agent on the target host. Next, you want to assign a patch job but that cannot be done until cerlainpatth manag below, check all the steps required to complete the patch management setup Choose all that DAssign host to CA Configuration Profite (with PM enatlec O Awgn hos to the PM Aset Group apply DAsign host to an enabled PM ASsessment Profie O Activate PM module on host
You have installed Qualys cloud Agent on the target host. Next, you want to assign a patch job but that cannot be done until cerlainpatth manag below, check all the steps required to complete the patch management setup Choose all that DAssign host to CA Configuration Profite (with PM enatlec O Awgn hos to the PM Aset Group apply DAsign host to an enabled PM ASsessment Profie O Activate PM module on host
Chapter12: Network Configuration
Section: Chapter Questions
Problem 2DE
Related questions
Question
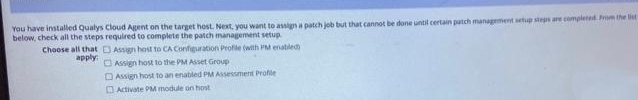
Transcribed Image Text:You have installed Qualys Cloud Agent on the target host. Next, you want to assign a patch job but that cannot be done until certain patch management setup steps are completed. Prom the list
below, check all the steps required to complete the patch management setup
Choose all that DAssign host to CA Configuration Profie (with PM enatled
O Assign host to the PM Asset Group
apply
DAssign host to an enabled PM ASsessment Profie
O Activate PM module on host
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L