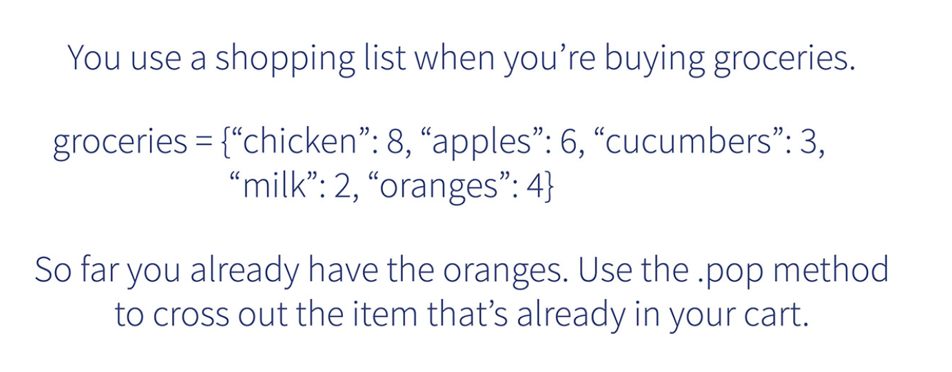
You use a shopping list when you're buying groceries. groceries = {"chicken": 8, "apples": 6, "cucumbers": 3, "milk": 2, "oranges":4} So far you already have the oranges. Use the .pop method to cross out the item that's already in your cart.
Q: 5, 8, 13, 21 etc. TI to write the fibona es without recursi
A: #include<stdio.h> int main() { int a=0,b=1,c,i,n; printf("Enter the number…
Q: What are some problems with gradients Computer science
A: Problems with gradients: Vanishing Gradient problem: The problem is that in some cases, the gradient…
Q: Python Programming: If I have a list: (let's say myList) myList = [1, 2, 3, 4, ...] (the elements…
A: Python is a very famous programming language these days, It is an Object oriented programming, which…
Q: 1.Solve the following differential equations using MATLAB 1.1. y"+ 6y'+9y= t.sint, y(0)=2, y'(0)=−1
A: We need to write a Matlab program to solve the given differential equation.
Q: с В D E
A: Answer - As the given graph has a cycle so we cannot use the backtracking approach. We need to use…
Q: Learn about the 10 most recent cyber-attacks on computers, networks, and information security, and…
A: Intro An attack is any effort to obtain unauthorized access to or utilize assets in order to expose,…
Q: What is the most effective method for obtaining application software? You should offer relevant…
A: Intro Application software is a sort of computer application that allows users to carry out…
Q: How significant is the importance of standardization?
A: Standardization is establishing norms to control the development of a product or service based on…
Q: What are some of the most noticeable differences between the operating systems used by a mainframe…
A: Intro A mainframe operating system is network software that runs applications, connects devices, and…
Q: What circumstances must be satisfied for an algorithm that ordinarily recursively calls itself to no…
A: Intro What are the conditions under which a recursive algorithm will no longer call itself?
Q: Is internet traffic routed through a single point of control that is located somewhere? Is this the…
A: Intro Firstly we will see ,What is a centralized network? A centralized network architecture is…
Q: Consider utilising Structured English to describe processes that do not fall under the purview of a…
A: Intro System analysis is defined as "the study of a method or organization to determine its aims…
Q: Explain why selective retransmission might be a good way to make the TCP protocol even better. Is…
A: Introduction: PROTOCOL FOR SELECTIVE RETRANSMISSION • Balances the TCP and UDP extremes • Loss vs…
Q: Indices can speed up query processing, but indexing every characteristic, and every combination of…
A: Intro Indices can speed up query processing, but indexing every characteristic, and every…
Q: X=0 E 2 To что E -E E E E Xse To 3 To E Vs
A:
Q: What exactly are routines and other Programming extensions?
A: Introduction: Routine and subroutine are almost equivalent words in computer programming for any…
Q: In three circumstances, the usage of a surrogate key for the primary key of a connection has been…
A: Intro In data analysis, a surrogate key is a key with no contextual relevance used to identify the…
Q: Give the IP address of each subnet in binary and in dotted decimal notation (a.b.c.d/x) (show your…
A: The answer is
Q: Explain the distinctions between Authorization and Authentication in Web testing.
A: Intro The authorization and authentication process in a Web application is different than in a…
Q: How can you make an ER diagram-based conceptual model?
A: Intro An Entity-Relationship model is what is meant by the abbreviation ER model. It is a data model…
Q: How can you describe in further depth the primary aspects of hacking and the ways in which they are…
A: How can you describe in further depth the primary aspects of hacking and the ways in which they are…
Q: (1) What are advantage and disadvantages of Apriori Algorithm
A: Disclaimer: “Since you have asked multiple question, we will solve the first question for you. If…
Q: C# application that will store expenses in an array groceries, water and electricity, travel costs
A: C language is a general-purpose programming language which can be used to develop software like…
Q: OSI security architecture has complex measures for data protection?
A: Introduction: Architecture for the Interoperability of Operating Systems (OSI) The term "security…
Q: 8 e velocity of 2 X 10° m/s. Calculate the
A: The answer is
Q: M= M= Low High 0.5 0.5 E = E= Good Bad Mileage Mileage Engine AC = AC = Working Broken Air…
A: Bayesian network is the essential computer technology for dealing with the probabilistic events and…
Q: What happens when you open a picture, then adjust the frame to a different size? What happens if you…
A: What happens when you open a picture, then adjust the frame to a different size? Ans : When we open…
Q: Solve it using round Robin scheduling Find the average waiting
A: Given :
Q: 1. Write a MIPS Assembly program to ADD the numbers: 1, 2, 3, 4, 5, 6, 7, 8 (as in ex-1) . Use ONLY…
A: Code:- .data .text main: #load values 1,2,3,4,5,6 to $t0 #and add all values one by one,and store in…
Q: give me the names of the three main frequency bands that are utilized in wireless communication…
A: Frequency Band: The lowest section of the electromagnetic spectrum, known as radio frequency (RF),…
Q: What's the connection between an IoT device and data?
A: Introduction: Sensor data from IoT devices can be shared and then sent to the cloud for analysis or…
Q: May you put me in the appropriate spot so that I can learn more about Windows Service Control…
A: Intro Under the Windows NT family of operating systems, Service Control Manager (SCM) is a unique…
Q: 5. A positive whole number n > 2 is prime if no number between 2 and √n (inclusive) evenly divides…
A: def is_prime(n): if n==1:return False elif n==2:return True for f in…
Q: C Program to swap two numbers withol third variable
A: According to the Question below the Solution: Output:
Q: The function of Service-Oriented Architecture (SOA) in web application architecture will be…
A: The above question is solved in step 2 :- SOA(service-based architecture) describes how to make…
Q: Armstrong Number in C Before going to write the c program to check whether the number is Armstrong…
A: #include<stdio.h> int main() { int num,x,sum=0,tem; printf("enter the number=");…
Q: Is there a major difference between the Internet's capabilities and those of the World Wide Web, and…
A: Intro In this part of the article, we are obligated to talk about the differences between the…
Q: Which two of the following are two reasons why layered protocols should be used? Give examples of…
A: Intro Reason For Using Layered Protocols Layered protocols are mainly used in technology for…
Q: There are several advantages to being computer literate. What are the potential benefits of…
A: Given: Individuals with computer literacy may improve their professional performance, integrate…
Q: For the following C statement, write the corresponding RISC-V assembly code. Assume that the C…
A: f is placed in the register x5 g is placed in the register x6 h is placed in the register x7 addi…
Q: Computers and smartphones, both of which are regarded advances in technology, are not considered…
A: Computers and mobile phones have not been extensively adopted for the following reasons:
Q: 1.Solve the following differential equations using MATLAB 1.1. y"+ 6y'+9y= t.sint, y(0) = 2, y(0)=-1
A: //Matlab code given below
Q: It is vital to consider data backup and restoration from various perspectives.
A: Introduction: Data backup and recovery is the process of backing up your data in the event of a…
Q: Describe the way that pictures seem when viewed on computer displays.
A: First, familiarize yourself with the background: Pixels Pixels make up every picture on your…
Q: What are the drawbacks of analog computers?
A: Given: An analogue computer is made up of a collection of circuit modules, each of which is able to…
Q: What are the security goals of the information technology industry? Describe briefly
A: Intro Cybersecurity and data security cowl totally different objectives and scopes with some…
Q: Both reasons for layered protocols are persuasive. An example must substantiate your assertion
A: Introduction: Layered Protocols: Many protocols are required for many networking operations, such…
Q: Information security management in today's fast-paced world.
A: The above question is answered in step 2 :-
Q: 1.Solve the following differential equations using MATLAB 1.1. y"+ 6y'+9y= t.sint, y(0)=2, y'(0)=-1
A: We are given a differential equation, and we need to solve it using Matlab.
Q: No programing language needed! Question: John and Diane want to have $376,000.00$376,000.00…
A: The above question is answered in step 2 :-
use python. and do the following
Step by step
Solved in 2 steps with 3 images

- in coral language Write a program that first gets a list of 5 integers from input. Then, get another value from the input, and output all integers less than or equal to that value. Ex: If the input is 50 60 140 200 75 100, the output is: 50 60 75 For coding simplicity, follow every output value by a space, including the last one. Then, output a newline. Such functionality is common on sites like Amazon, where a user can filter results.in coral languge Write a program that first gets a list of 5 integers from input. Then, get another value from the input, and output all integers less than or equal to that value. Ex: If the input is 50 60 140 200 75 100, the output is: 50 60 75 For coding simplicity, follow every output value by a space, including the last one. Then, output a newline. Such functionality is common on sites like Amazon, where a user can filter results.Extreme Fizz BuzzFizz Buzz is a classic Computer Science problem about Selection. For an integer x, print:• “Fizz” if x is only divisible by 3,• “Buzz” if x is only divisible by 5,• “FizzBuzz” if x is divisible by both 3 and 5,• the number x if it is not divisible by both 3 and 5.This problem is the extreme version of Fizz Buzz. You are given a list of K distinct integers A and a list of K characters S. Both lists are numbered from 1 to K. The integer Ai corresponds to the character Si. Denote B as the subset of A. There will be a rule for each possible subset: if an integerx is only divisible by all elements in B, print a string which is the concatenation of the corresponding character of each element in B, sorted by the index in ascending order. However, if B is an empty subset, print the first digit of x instead. Does it look complicated? Do not worry, as it is just a generalization of the regular Fizz Buzz. For example, if A = [3, 5] and S = [F, B], you will get the normal Fizz…
- In Java: When analyzing data sets, such as data for human heights or for human weights, a common step is to adjust the data. This can be done by normalizing to values between 0 and 1, or throwing away outliers. For this program, adjust the values by subtracting the smallest value from all the values. The input begins with an integer indicating the number of integers that follow. Assume that the list will always contain less than 20 integers. Ex: If the input is: 5 30 50 10 70 65 the output is: 20 40 0 60 55 For coding simplicity, follow every output value by a space, even the last one. Your program must define and call a method:public static int getMinimumInt(int[] listInts, int listSize) import java.util.Scanner; public class LabProgram {/* Define your method here */ public static void main(String[] args) {/* Type your code here. */}}Write a java application for an Auto Car shop that shows a user a list of available services: oil change, tire rotation, battery check, or brake inspection. Allow the user to enter a string that corresponds to one of the options, and display the option and its price as €9, €7, €5, or €3, accordingly. Display an error message if the user enters an invalid item. ALSO SHOW OUTPUTIn this task you are asked to construct a table showing the sequence of numbersfrom 0 to a maximum value as specified by the user. Within the table, if the number in the cell is a highlighted (e.g., blue in thescreenshot below) when it is divisible by a number that is also specifiedbytheuser, known as the divisor. For example, the user could input for the maximumavalue of 100 and for the divisor a value of 23; this should result in the cellscontaining the values: 0, 23, 46, 69 and 92; being highlighted.
- Write a program that prompts the user to enter apositive integer and displays all its smallest factors in decreasing order. Forexample, if the integer is 120, the smallest factors are displayed as 5, 3, 2, 2,2. Use the StackOfIntegers class to store the factors (e.g., 2, 2, 2, 3, 5) andretrieve and display them in reverse order.THIS IS MEANT TO BE IN JAVA Write a program that first gets a list of integers from input. The input begins with an integer indicating the number of integers that follow. Then, get the last value from the input, which indicates a threshold. Output all integers less than or equal to that last threshold value. Assume that the list will always contain fewer than 20 integers. Ex: If the input is: 5 50 60 140 200 75 100 the output is: 50,60,75, The 5 indicates that there are five integers in the list, namely 50, 60, 140, 200, and 75. The 100 indicates that the program should output all integers less than or equal to 100, so the program outputs 50, 60, and 75. For coding simplicity, follow every output value by a comma, including the last one. Such functionality is common on sites like Amazon, where a user can filter results. Please show code.Write a complete JAVA program that user can randomly customized item they want to put in the gift box [ limit 5 item in a box]. Each user can create only 2 box. For example: Create a few lists: List 1: Chocolate Strawberry, Chocolate Milk, Chocolate Nuts List 2: Balloon red, Balloon blue, Balloon orange, Balloon Pink List 3: Candy 1, Candy 2, Candy 3, Candy 4, Candy 5 List 4: Card 1, Card 2, Card 3 Box 1: Chocolate Strawberry [2], Balloon orang [2]. Balloon Pink [1] Box 2: Candy 1[1], Candy 4[1], Card 1[1]. Balloon blue[1], Balloon red[1]
- def fun_cities(adict, city): """ Question 7 - Given a dict that maps a fun activity to a list of cities where you could practice it, return the set of activities that one could practice at the provided city! - For an extra challenge, try doing this in one line (Optional). Args: adict (dict) city (str) Returns: set >>> activity_dict = {"Sightseeing": ["Venice", "Istanbul", "London"], "Kayaking": ["Venice", "Oslo", "Paris"], "Food Tasting": ["Paris", "Istanbul", "Mumbai"], "Going to the Theater": ["Paris", "Oslo", "London"]} >>> fun_cities(activity_dict, "Paris") {'Kayaking', 'Food Tasting', 'Going to the Theater'} >>> fun_cities(activity_dict, "Venice") {'Sightseeing', 'Kayaking'} # activity_dict = {"Sightseeing": ["Venice", "Istanbul", "London"], "Kayaking": ["Venice", "Oslo", "Paris"], # "Food Tasting": ["Paris", "Istanbul", "Mumbai"], "Going…Write a program that first reads a list of 5 integers from input. Then, read another value from the input, and output all integers less than or equal to that last value. Ex: If the input is: 50 60 140 200 75 100 the output is: 50 60 75 For coding simplicity, follow every output value by a space, including the last one. Then, output a newline. Such functionality is common on sites like Amazon, where a user can filter results.In python: Write a program that first gets a list of integers from input. The input begins with an integer indicating the number of integers that follow. Then, get the last value from the input, which indicates a threshold. Output all integers less than or equal to that last threshold value. Ex: If the input is: 5 50 60 140 200 75 100 the output is: 50 60 75 The 5 indicates that there are five integers in the list, namely 50, 60, 140, 200, and 75. The 100 indicates that the program should output all integers less than or equal to 100, so the program outputs 50, 60, and 75. Such functionality is common on sites like Amazon, where a user can filter results.

