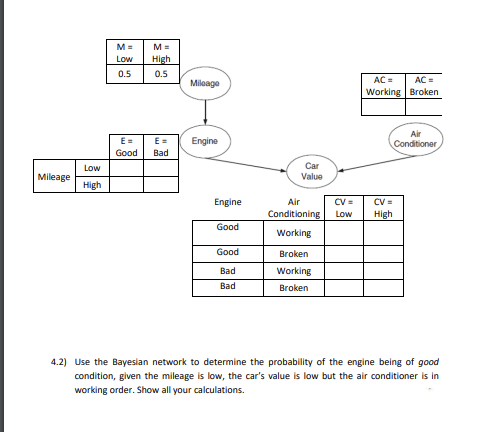
M= M= Low High 0.5 0.5 E = E= Good Bad Mileage Mileage Engine AC = AC = Working Broken Air Conditioner Low Car Value High Engine Air CV= CV= Conditioning Low High Good Working Good Broken Bad Working Bad Broken 4.2) Use the Bayesian network to determine the probability of the engine being of good condition, given the mileage is low, the car's value is low but the air conditioner is in working order. Show all your calculations.
Q: Write a program to create a file named Exercise13_1.txt if it does not exist. If it does exist,…
A: Answer:
Q: When comparing on-premises and cloud IT SECURITY systems, what are the most noteworthy differences…
A: The typical corporate computing paradigm uses on-premises servers.
Q: To transmit the data 1011000 to his friend using hamming code technique. Calculate (i) number of…
A: 1. 4 bits [0,1,0]2. 7, 6, 5, 4, 3, 2, 13. 7 bits4. 10110105. After using the hamming code…
Q: What exactly is "hacking"? Provide a concise explanation of the many forms of hacking, as well as…
A: Given: Hacking exploits a computer's system or private network. It's illegal access or control of…
Q: Several professionals in the field of cybersecurity believe that fingerprinting is unethical and…
A: Answer: Finger Print is unethical because it can steal by the third party and do some suspicious…
Q: Describe key characteristics of the ATA and SATA interfaces.
A: To be decided: Describe the fundamental differences between the ATA and SATA interfaces.
Q: Determine the costs of the following instruction sequences: LD R0, c LD R1, i…
A: As expected, the code generator input is the output of the central code generator. We assume that…
Q: What factors should be considered while putting up a solid Disaster Recovery strategy?
A: here in given question ask for factor should be considered while putting up a solid disaster…
Q: BMI is a measure of body condition and it is related to a person's weight and height. In the metric…
A: This code is used to know the condition of person whether he’s healthy or obese. If the BMI is less…
Q: When establishing a disaster recovery strategy, what elements should be taken into account?
A: Introduction: The disaster recovery plan checklist identifies key IT systems and networks,…
Q: What are the input parameters for the DumpMem procedure?
A: Introduction:- ProcDump is an order line utility whose basic role is observing an application…
Q: In your own words, please explain what an assembler, a compiler, and an interpreter are.
A: A translator performs an essential part in language conversion. It serves as an intermediary.
Q: Explain the fundamental difference between an array and an arraylist.
A: Array: It is dynamically-created object and serves as a container which holds constant number of…
Q: Several professionals in the field of cybersecurity believe that fingerprinting is unethical and…
A: Given: Browser fingerprinting collects device-specific characteristics for identification or…
Q: Explain why an index is only useful if there is sufficient variation in the values of an attribute.
A: A term index is a data structure used in computer science to aid the quick lookup of words and…
Q: or Linux, everything is considered a file, including regular files, directories and hardware…
A: Answer Total answers posted by the expert is: 282 %%%%%%%%% Part 1%%%%%%%%%%%%%%% a) ls -la…
Q: Unlike a database software, an expert system does not have a user interface?
A: Answer is given below-
Q: what is the correct syntax in displaying the "8" in the given array? int nums[]={,3,5,8,9,11};…
A: Note - Your given array is missing one value in the starting. So I assume it from my side answer is
Q: Create a single regular expression that matches a time expressed in the form "1:45 PM". Additional…
A: Here is the explanation about the regular expression:
Q: Use control flow programs to generate the Fibonacci sequence starting from F1=1 up to a given "n"…
A: As per question statement, We need to write MATLAB code.
Q: Assume the following precedence parenthesizing all subexpressions and associativity rules shown…
A: Operator Precedence order is a standard that helps to determine the flow of execution in an…
Q: What challenges could arise as a consequence of separating a connection vertically?
A: When a marriage comes to an end, the PRA assumes that both couples contributed equally to the…
Q: Let P(X) = “x ate lunch at Jollibee” and S(x) = “x is a Leeward CC Student” 5. Assume the…
A: Here in this question we have given P(X) = “x ate lunch at Jollibee” S(x) = “x is a Leeward CC…
Q: In an entity-relationship diagram, what does cardinality mean? 1:The data is saved concerning a…
A: In an entity-relationship diagram, what does cardinality mean? 1:The data is saved concerning a…
Q: How many times is the loop below executed? What is the output of this code? i=1 while i < 10:…
A: in the following section we will be discussing about the correct answer for the above question along…
Q: What does "security" even entail when it comes to the topic of safety? What are some of the most…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. A great…
Q: Draw the equivalent one flip-flop per state. PQ = 00 A 2 X B Link 2 1 с 0 X X Link 3 PQ-01 Link 4…
A: Here is the two flip-flops are P and Q.
Q: Names and definitions for entities, relationships, and attributes should all be proper.
A: Relationships and Entities: An entity–relationship model (or ER model) depicts related entities of…
Q: What are some of the possible causes of a network's decreased speed?
A: Given: Has been completed. Becoming be aware of the elements that lead a network to sluggish.
Q: Create a Visual Basic project to solve for the roots of the quadratic equation -b+√b²-4ac 2a 3…
A:
Q: pooling,stride-2 --->3X3-filter (128-filters), Stride-2,padding-0 --> 2X2 max-pooling,stride-2 --->…
A: The answer is
Q: In your opinion, where does information security begin and stop in a business?? At what point in…
A: Definition: Information security prevents unauthorised access, use, disclosure, disruption,…
Q: Your computer may be shielded from any threats coming from the outside world if you have a firewall…
A: Answer 1) many times yes. because if we have installed firewall , so protected against outside…
Q: Describe four challenges that might arise while merging relationships.
A: Merging relationships: A cumulative kind of acknowledgment is used by either the mobile host or the…
Q: "\n", "Consider the list presented below, where each pair represents a grade and attendance. Write a…
A: Solution- Programming language - Python Use google colab/ python Jupyter notebook to run this…
Q: How can you describe in further depth the primary aspects of hacking and the ways in which they are…
A: How can you describe in further depth the primary aspects of hacking and the ways in which they are…
Q: Make a list of all the online tools that make it easier for you to communicate. The characteristics…
A: The answer of this question is as follows:
Q: Make a C program that will display the factorial of a number. Note: Use a for loop. Definition: n!…
A: let us see the answer:- Introduction:- Definition: n! (read as n factorial) n!=n(n−1)(n-2)...(2)(1)…
Q: What does "security" even entail when it comes to the topic of safety? What are some of the most…
A: let us see the answer:- Introduction:- What does "security" even entail when it comes to the topic…
Q: What kind of data would you keep in an entity subtype?
A: Given: A subtype is sub-grouping of the entities that make up an entity type that has significance…
Q: Fingerprinting, according to the opinions of a number of cybersecurity experts, is a kind of misuse…
A: Browser fingerprinting: Browser fingerprinting (sometimes called device or online fingerprinting) is…
Q: Which two of the following are the most compelling arguments in favor of layered protocols? Please…
A: Your answer is given below. Introduction :- A layered protocol architecture is a notion for…
Q: Describe some of the data security measures that are utilized in tandem with software-based…
A: Software-based security: The inquiry is interested in learning more about the software-based…
Q: Why should assembly language not be used when developing programs for general-purpose use? In what…
A: Assembly is a low-level programming language that allows a computer to interface directly with its…
Q: 6). in the destructive read-out memory read and write operations, in order to maintain the original…
A: Below i write in what fill in the blanks.…
Q: 1. Perform the following subtraction using 10's complement on 532 - 794.
A: subtraction using 10's complement 532-794
Q: Content: Encyrpt a message using AES algorithm for Round 1. All encryption steps has to be shown…
A: Plaintext matrix: M I C H A E L Key matrix: S A L I H After Round 1 of AES algorithm:…
Q: C++ program Write C++ program to read 5 numbers and determine if the numbers sorted ascending or…
A: Source code : #include<iostream> using namespace std; bool isSorted(int arr[5]) { static…
Q: Consider the two codes presented below, do these codes produce the same output? Justify your answer.…
A: Introduction: Python was created with readability in mind, and it bears some resemblance to the…
Q: What are the most important aspects of a cybersecurity architecture, and how can they be protected…
A: Introduction: A system that frames the hierarchical construction, guidelines, standards, and useful…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Suppose we use the following KB (where x,y,z are variables and r1, r2, r3, goal are constants) to determine whether a particular robot can score a) Open(x) ∧ HasBall(x) -> CanScore(x) b) Open(x) ∧ CanAssist(y,x) ∧ HasBall(y) -> CanScore(x) c) PathClear(x,y) -> CanAssist(x,y) d) PathClear(x,z) ∧ CanAssist(z,y) -> CanAssist(x,y) e) PathClear(x,goal) -> Open(x) f) PathClear(y,x) -> PathClear(x,y) g) HasBall(r3) h) PathClear(r1, goal) i) PathClear(r2, r1) j) PathClear(r3, r2) k) PathClear(r3, goal) Intuitively, CanScore(x) means x can score on goal. CanAssist(x,y) means there exists some series of passes that can get the ball from x to y. Open(x) means x can shoot on goal directly. And PathClear(x,y) means the path between x and y is clear. Provide a SLD-derivation for the query CanScore(x) in which the answer provided is r1. Provide a SLD-derivation for the query CanScore(x) in which the answer provided is r3. How many "distinct" derivations (i.e., involving different…In a prison, there is a door b/w any pair of adjacent cells and one exit guarded by a guard G. One prisoner is a maniac M which kills anybody he can see when he enters a cell. If M returns to the cell with his victim, then he loses consciousness and stops. In the evening all inmates and the guard went to sleep in their cells. In the morning, maniac M is gone and all other prisoners with the guard were found dead in their cells. Show the route of the maniac.Suppose we use the following KB (where x, y, z are variables and r1, r2, r3, goal are constants) to determine whether a particular robot can score. (a) Open(x) ∧ HasBall(x) → CanScore(x)(b) Open(x) ∧ CanAssist(y, x) ∧ HasBall(y) → CanScore(x) (c) PathClear(x,y) → CanAsist(x,y)(d) PathClear(x,z) ∧ CanAssist(z,y) → CanAssist(x,y) (e) PathClear(x,goal) → Open(x)(f) PathClear(y,x) → PathClear(x,y) (g) HasBall(r3)(h) PathClear(r1,goal) (i) PathClear(r2,r1) (j) PathClear(r3,r2) (k) PathClear(r3,goal)
- Suppose we use the following KB (where x, y, z are variables and r1, r2, r3, goal are constants) to determine whether a particular robot can score. (a) Open(x) ∧ HasBall(x) → CanScore(x)(b) Open(x) ∧ CanAssist(y, x) ∧ HasBall(y) → CanScore(x) (c) PathClear(x,y) → CanAsist(x,y)(d) PathClear(x,z) ∧ CanAssist(z,y) → CanAssist(x,y) (e) PathClear(x,goal) → Open(x)(f) PathClear(y,x) → PathClear(x,y) (g) HasBall(r3)(h) PathClear(r1,goal) (i) PathClear(r2,r1) (j) PathClear(r3,r2) (k) PathClear(r3,goal) Intuitively, CanScore(x) means x can score on goal. CanAssist(x, y) means there exists some series of passes that can get the ball from x to y. Open(x) means x can shoot on goal directly. And P athClear(x, y) means the path between x and y is clear. Provide a SLD-derivation for the query CanScore(x) in which the answer provided is r1. Provide a SLD-derivation for the query CanScore(x) in which the answer provided is r3. How many “distinct” derivations (i.e., involving different…Correct answer will be upvoted else Multiple Downvoted. Don't submit random answer. Computer science. every cell of the network contains a non-negative integer. Each turn, a player should play out every one of the accompanying activities all together. Pick a beginning cell (r1,c1) with non-zero worth. Pick a completing cell (r2,c2) to such an extent that r1≤r2 and c1≤c2. Lessening the worth of the beginning cell by some sure non-zero integer. Pick any of the most limited ways between the two cells and either increment, lessening or leave the upsides of cells on this way unaltered. Note that: a most limited way is one that goes through the most un-number of cells; all cells on this way barring the beginning cell, yet the completing cell might be altered; the subsequent worth of every cell should be a non-negative integer; the cells are changed freely and not really by a similar worth. On the off chance that the beginning and finishing cells are something very…Correct answer will be upvoted else Multiple Downvoted. Computer science. You are given an integer n (n>1). Your assignment is to find a succession of integers a1,a2,… ,ak with the end goal that: every simulated intelligence is completely more prominent than 1; a1⋅a2⋅… ⋅ak=n (I. e. the result of this grouping is n); ai+1 is separable by simulated intelligence for every I from 1 to k−1; k is the most extreme conceivable (I. e. the length of this grouping is the greatest conceivable). In case there are a few such groupings, any of them is adequate. It tends to be demonstrated that somewhere around one substantial grouping consistently exists for any integer n>1. You need to answer t autonomous experiments. Input The primary line of the input contains one integer t (1≤t≤5000) — the number of experiments. Then, at that point, t experiments follow. The main line of the experiment contains one integer n (2≤n≤1010). It is ensured that the amount of n…
- A drawer contains 7 pair of socks where 8 socks are white, and 6 are red. In how many ways we can take 14 random socks out of the drawer so each sock is next to its matching pair. a. 441 ways b. 42 ways c. 1225 ways d. 70 waysHow make simulation Aquarium Automatic Care (AOC) system (incl. coding) with Arduino. AOC is simulated using Tinkercad based on below conditions? Conditions: 1. Water must be replaced when -Water level (T) < 41 mm -Discard water and fill 30% of Aquarium water volume when high Acidic pH (pH> 9)2. Fish food (pellets): 1 x 4.5 mL/day at 6am in the morning, the machine only contains 100 mL (warning on D-day is over)3. To save electricity, the aquarium lights are on at night (8 hours)Correct answer will be upvoted else downvoted. Computer science. way from block u to obstruct v is a grouping u=x0→x1→x2→⋯→xk=v, where there is a street from block xi−1 to hinder xi for each 1≤i≤k. The length of a way is the amount of lengths over all streets in the way. Two ways x0→x1→⋯→xk and y0→y1→⋯→yl are unique, if k≠l or xi≠yi for some 0≤i≤min{k,l}. Subsequent to moving to another city, Homer just recalls the two exceptional numbers L and R yet fails to remember the numbers n and m of squares and streets, separately, and how squares are associated by streets. Be that as it may, he accepts the number of squares ought to be no bigger than 32 (in light of the fact that the city was little). As the dearest companion of Homer, if it's not too much trouble, let him know whether it is feasible to see as a (L,R)- constant city or not. Input The single line contains two integers L and R (1≤L≤R≤106). Output In case it is difficult to track down a (L,R)- consistent city…
- A police academy has just brought in a batch of new recruits. All recruits are given an aptitude test and a fitness test. Suppose a researcher wants to know if there is a significant difference in aptitude scores based on a recruits’ fitness level. Recruits are ranked on a scale of 1 – 3 for fitness (1 = lowest fitness category, 3 = highest fitness category). Using “ApScore” as your dependent variable and “FitGroup” as your independent variable, conduct a One-Way, Between Subjects, ANOVA, at α = 0.05, to see if there is a significant difference on the aptitude test between fitness groups. Identify the correct values for dfbetween and dfwithin A. dfbetween = 7 dfwithin = 7 B. dfbetween = 13 dfwithin = 2 C. dfbetween = 2 dfwithin = 13 D. dfbetween = 2 dfwithin = 2If the probability of an event is 62%, what is the probability of its complement?Let l be a line in the x-y plane. If l is a vertical line, its equation is x 5a for some real number a. Suppose l is not a vertical line and its slope is m. Then the equation of l is y 5mx 1b, where b is the y-intercept. If l passes through the point (x0, y0,), the equation of l can be written as y 2y0 5m(x 2x0 ). If (x1, y1) and (x2, y2) are two points in the x-y plane and x1 ≠ x2, the slope of line passing through these points is m 5(y2 2y1 )/(x2 2x1 ). Write a program that prompts the user two points in the x-y plane. The program outputs the equation of the line and uses if statements to determine and output whether the line is vertical, horizontal, increasing, or decreasing. If l is a non-vertical line, output its equation in the form y 5mx 1b.

