Your Class is Sage: Your Following Stats should be the following when you start the program: Attack:1-5(ranging) Health:90-100(Randomize) Mana: 300-500(Randomize)
Q: After a data breach, are there methods to increase the security of cloud storage? What are some of…
A: A data breach in Cloud Storage is. Unlawful access to restricted data stored in the cloud. This can…
Q: Is it even feasible to describe what a digital signature is, and how exactly does one function in…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Two cyber security regulatory frameworks—pros and cons?
A: To mitigate risks, various regulatory frameworks have been developed to guide organizations in…
Q: Graph Algorithm. Show the d and pi values that result from running breadth-first search on this…
A: In this question we have to perform the graph algorithm where we hav eto show d and pi values that…
Q: In the context of computer systems, how do real-time and non-real-time OSes differ, and what are the…
A: A computer system is a mix of hardware and software parts that cooperate to play out a particular…
Q: Please help me with the two questions (questions and 4) using the truth table and the diagram. I am…
A: As per our company guidelines, only 3 sub parts will be answered. So, please repost the remaining…
Q: How hard is it to keep track of the change from on-premise computers to those housed in a design…
A: The utilization of on-premise PCs is gradually giving methods for cloud computing models like…
Q: Asset management was not understood or valued at the firm you audited. How can you educate…
A: Asset management is the process of monitoring and maintaining an organization's assets to maximize…
Q: Twitter is becoming more popular as a social media platform that can be used for both personal and…
A: Trending on Twitter refers to the popular topics, hash tags, or keywords that are organism discussed…
Q: When creating a MIS information security strategy, what cyber threats should you anticipate and…
A: When creating an information security strategy for a management information system (MIS), there are…
Q: Make a list of the "lost and found" app's student requirements
A: When creating an app like a "lost and found" app, it is critical to define a clear set of criteria…
Q: ***PYTHON 3 PLEASE*** dying_countries: This function takes a formatted countries DataFrame that has…
A: In this question we have to write a python code for the given problem description Let's code and…
Q: Have an example in mind that relates to the working c
A: When it comes to the working context, having a clear understanding of a concept, process or idea is…
Q: The roles and duties of the different access control groups for computer security are compared and…
A: Access control is a data security technique that allows organizations to govern who can access…
Q: The whole domain name system (DNS), from iterated queries to root servers, authoritative servers to…
A: The Domain Name System (DNS) is a hierarchical and distributed naming system that translates domain…
Q: In the context of Software Development Project Methodologies, which of the following statements best…
A: The statement that best distinguishes between the traditional Software Development Life Cycle (SDLC)…
Q: System software and embedded system software can be distinguished by a distinct dividing line. Could…
A: System software includes the operating system, device drivers, and system utilities. It supervises…
Q: Is there a governance difficulty involved in switching from servers located on-premises to an…
A: There can be governance difficulties involved in switching from on-premises servers to an…
Q: This detailed tutorial covers everything from DNS records to authoritative servers to iterated and…
A: DNS, or the Domain Name System, is an essential part of the internet infrastructure. It is the…
Q: Why is it preferable to use cloud-based storage software as opposed to traditional client-based…
A: Cloud-based storage refers to saving data on distant servers that are accessible via The internet…
Q: A three-schema design has three levels, and at each level, requests are turned into results.
A: The three-schema design is a hypothetical structure for position and organization database systems.…
Q: Let's say you work for a big company that uses a firewall to keep people from getting into its…
A: In the meadow of network security, it is vital to apply various layer of defense. This idea, known…
Q: How do add-on extensions on a web browser function technically?
A: Web browsers are essential software applications that allow users to access and view web pages on…
Q: Explain the rationale behind the Domain Name System's (DNS) design as a distributed database.
A: Domain Name System (DNS) The DNS are the system that converts the domain name, such as www.xyz.com,…
Q: How does a developer's mindset differ from a tester's? Why is software tester code reading so…
A: Developers and testers both play crucial roles in the software development process. While developers…
Q: What are some of the barriers that prevent people from adopting IoT technologies?
A: The Internet of Things (IoT) promises to revolutionize various aspects of our lives by connecting…
Q: 1. Implement the Forward algorithm in Python. Your task is to write code for the following…
A: As per our guidelines we are answering the question.
Q: Define authoritative and root DNS servers, authoritative and non-authoritative DNS queries, and DNS…
A: DNS (Domain Name Server): It is a system that translates domain names, such as www.edu.com into IP…
Q: discuss the concept of SEEK time as it relates to disk optimization. What are the major components…
A: in the following section we will learn about what is concept of SEEK time as it relates to disk…
Q: Convert the following NFA to a DFA. Show your work. Show both the DFA table AND the graph of the…
A: Finite Automata is defined as a machine that is simple and is used to recognize the patterns that…
Q: In one sentence, describe the main parts of a standard operating system.
A: Operating System An Operating System (OS) is a type of software that manages computer hardware…
Q: How many cyber dangers will you prepare for when creating a comprehensive MIS information security…
A: 1) A Management Information System (MIS) information security strategy is a comprehensive plan that…
Q: I need fix this code Please help me def add(a,b): return a+b def subtract(a,b): return…
A: Define mathematical functions for addition, subtraction, multiplication, division, power, and…
Q: Why is Microsoft Access better at managing data than Microsoft Excel?
A: Both Microsoft Access and Microsoft Excel are effective tools for handling data, but they were made…
Q: What precisely is meant by the term "virtualization," and how does its use pertain to cloud…
A: Virtualization is a technique used in computing to create virtual versions of resources, such as…
Q: Please provide a definition of unclean data and at least FIVE (5) sources for it.
A: In computer science, data is considered to be the most critical asset that any organization…
Q: In the context of the architecture of web applications, what role does MVC play? What are some of…
A: MVC means: - Model (M): Manages the data (database). View (V): Manage what the user sees (html,…
Q: What is the key difference between a 7CH bit address and a 7CH byte address? Which part of the…
A: => A memory address is a unique identifier that points to a specific location in computer…
Q: In a Big Endian machine, the highest order byte of a word is stored at the smallest memory address.…
A: True. In a Big Endian machine, the most significant byte (highest order byte) of a word is stored at…
Q: Is smartphone user interface design difficult? Describe what happens when a product or category is…
A: The design of user interfaces for smartphones is an intricate task that requires cautious thought of…
Q: /*Author: Cody Guardipee Date: 5/1/2023 Purpose: Calculate Fuel Economy in Miles Per Gallon and…
A: C is a procedural and general-purpose programming language that can provide level access to system…
Q: There is a thorough look at many different parts of DNS queries, such as iterated and non-iterated…
A: Domain Name Servers are the devices that map the hostname to the IP addresses of the…
Q: Where does Amazon Web Services vary from Microsoft Azure?
A: A free and open-source cloud computing platform called Azure provides data storage, service hosting,…
Q: Types of DNS records are listed. Every case has a reason behind it. Can the same name be used for…
A: The DNS system transforms domain names into IP addresses. DNS (Domain Name System) is essential to…
Q: write a program in Java that would ask the clerk to enter the total amount of the customer’s order.…
A: The JAVA code is given below with output screenshot
Q: Microsoft isn't the only company offering cloud services; there are other ones as well. How does AWS…
A: Businesses of all sizes use Amazon Web Services (AWS) and Microsoft Azure, two of the most…
Q: What precisely is meant by the term "semaphore," and how many different types of semaphores are…
A: In this answer, we will describe what semaphore is, how it works, and some concrete examples of its…
Q: Which of the following best describes a type of artificial intelligence (AI) algorithm process whose…
A: Artificial Intelligence (AI) refers to the development of computer systems that can perform tasks…
Q: Using the constructions described in the proof of Kleene’s theorem, find nondeterministic…
A: Kleen's Theorem: A language is said to be regular if it can be represented using Finite Automata or…
Q: A stack is very useful in situations when data have to be stored and then retrieved in the —-…
A: For given question we need to identify in which situation stack is very useful when data have to be…
Simple game C#
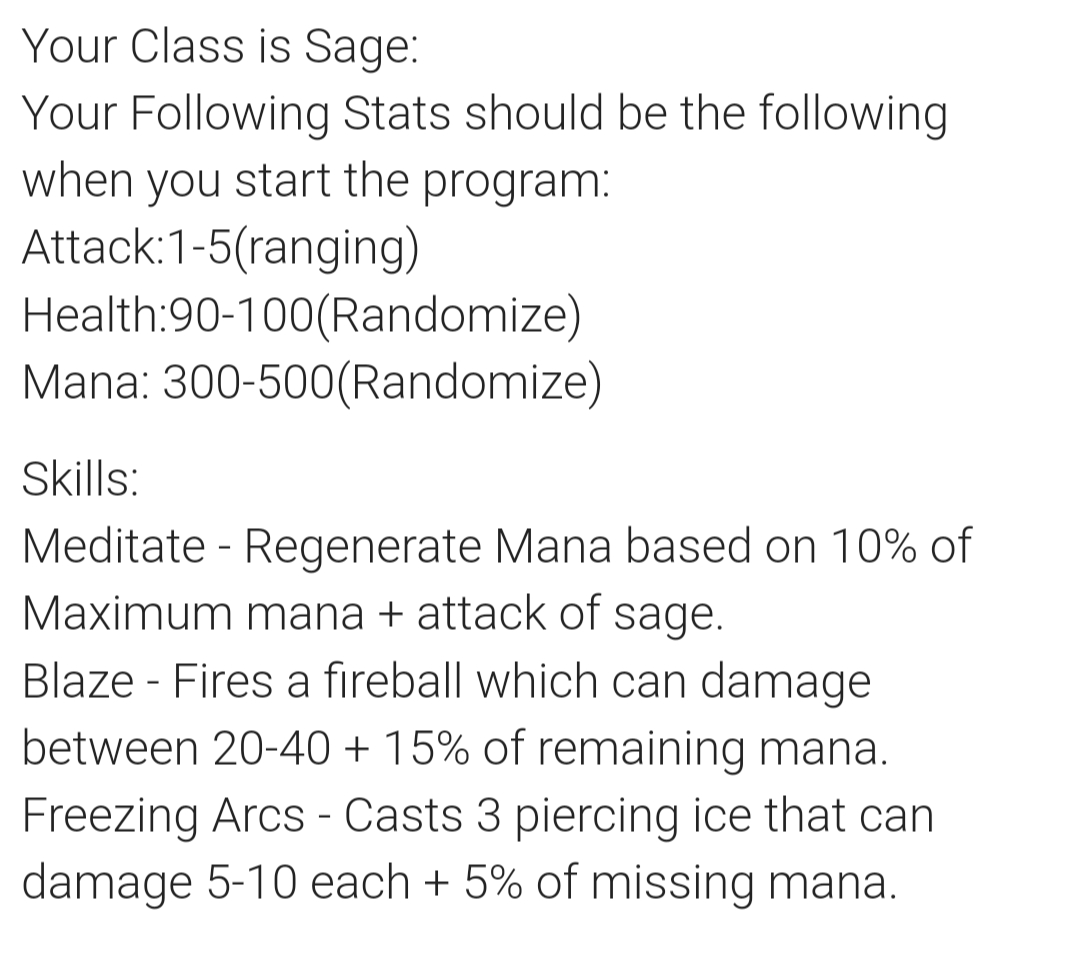
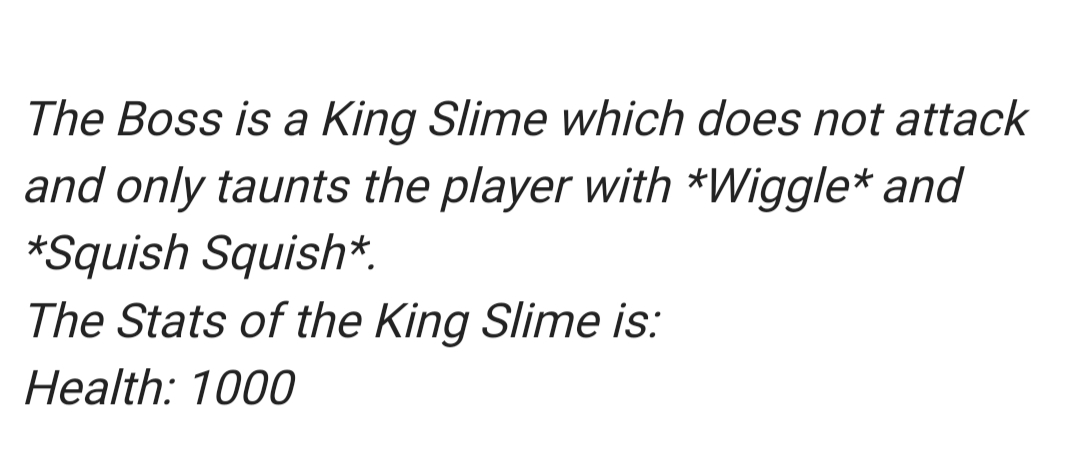
Step by step
Solved in 3 steps with 1 images

- A "mad-lib" is a fill-in-the blank game. One player writes a short story in which some words are replacedby blanks. For each word that is removed, the appropriate part of speech is noted: e.g. noun (person/-place/thing), adjective (word that describes a noun), verb (an action, e.g. eat), adverb (modifies a verb, e.g.quickly). Then, before reading the story, the story-writer asks the other player to write down a word of theappropriate part of speech for each blank without knowing the context in which it will be used. In this way,a humorous (sometimes) or non-sensical (usually) story is created.Write your own mad-lib. It must have at least three blanks in it. Now write a Python program that doesthe following:- Using the input() syntax (see the section "Reading Strings from the Keyboard" from the course read-ings) for reading strings from the console, prompt the user to enter a word of the appropriate part ofspeech for each blank in your program. Have a different, appropriately named…A "mad-lib" is a fill-in-the blank game. One player writes a short story in which some words are replacedby blanks. For each word that is removed, the appropriate part of speech is noted: e.g. noun (person/-place/thing), adjective (word that describes a noun), verb (an action, e.g. eat), adverb (modifies a verb, e.g.quickly). Then, before reading the story, the story-writer asks the other player to write down a word of theappropriate part of speech for each blank without knowing the context in which it will be used. In this way,a humorous (sometimes) or non-sensical (usually) story is created a)Exercises: PolymorphismProblem 1. VehiclesWrite a program that models 2 vehicles (Car and Truck) and will be able to simulate driving and refueling them inthe summer. Car and truck both have fuel quantity, fuel consumption in liters per km and can be driven givendistance and refueled with given liters. But in the summer both vehicles use air conditioner and their fuelconsumption per km is increased by 0.9 liters for the car and with 1.6 liters for the truck. Also the truck has a tinyhole in his tank and when it gets refueled it gets only 95% of given fuel. The car has no problems when refueling andadds all given fuel to its tank. If vehicle cannot travel given distance its fuel does not change.Input On the first line - information about the car in format {Car {fuel quantity} {liters per km}} On the second line – info about the truck in format {Truck {fuel quantity} {liters per km}} On third line - number of commands N that will be given on the next N lines On the next N lines –…
- Modify the Item class to maintain a priority value. This value must also be set in the constructor. private int num; public Item(int num) { this.num = num; } public int GetNum() { return num; }Four in a row is a game in which players take turns adding tokens to the columns on the game board. Tokens fall to the lowest position in the chosen column that does not already have a token in it. Once one of the players has placed four of their tokens in a straight line (either vertically, horizontally, or diagonally), they win the game If the board is full and no player has won, then the game ends in a draw. TASK Using the following class descriptions, create a UML diagram and a version of Four in a row game The game must allow for a minimum of two and maximum of four players The game must allow each player to enter their name(duplicate names should not be accepted) The game should give the players the ability to choose how many rows (between four and ten), and how many columns (between four and ten) the game board should have. The code uses several classes, including "Player", "Board","Game" and exceptions for handling errors such as invalid moves and full columns.…JAVA PROGRAMMING Write two java files for this assignment: Circle.java, and Main.java. The Circle.java file will create an actual class. The Circle class: MEMBER VARIABLE double radius double x double y Eight methods: Six of the methods are simple: getter’s and setter’s for x, y, and radius. There should also be a getArea method that returns the area (derived from the radius) A doesOverlap method. This method should accept a Circle as an argument, and return true if this circle overlaps the circle that the method was invoked on. [Note: two circles overlap if the sum of their radius' is greater than or equal to the distance between their centers.] void setX(double value) double getX() void setY(double value) double getY() void setRadius(double value) double getRadius() double getArea() boolean doesOverlap(Circle otherCircle) second class will be the typical replit Main class, with its static main method .It should contain code that tests the Circle class. submit code that…
- Help, I am making a elevator simulation using polymorphism. I am not sure to do now. Any help would be appreciated. My code is at the bottom, that's all I could think off. There are 4 types of passengers in the system:Standard: This is the most common type of passenger and has a request percentage of 70%. Standard passengers have no special requirements.VIP: This type of passenger has a request percentage of 10%. VIP passengers are given priority and are more likely to be picked up by express elevators.Freight: This type of passenger has a request percentage of 15%. Freight passengers have large items that need to be transported and are more likely to be picked up by freight elevators.Glass: This type of passenger has a request percentage of 5%. Glass passengers have fragile items that need to be transported and are more likely to be picked up by glass elevators. public abstract class Passenger { public static int passangerCounter = 0; private String passengerID; protected…In the card game War, a deck of playing cards is divided between two players. Each player exposeda card; the player whose card has the higher value wins possession of both exposed cards. Createa console-based computerized game of War named WardCardGame in which a standard 52-carddeck is randomly divided between two players, one of which is the computer. Reveal one card forthe computer and one card for the player at a time. Award two points for the player whose cardhas the higher value. (For this game, the king is the highest card, followed y the queen and jack,then the numbers 10 down to 2, and finally the ace.) if the computer and player expose cards withequal values in the same turn, award one point to each. At the end of game, all 52 cards shouldhave been played only once, and the sum of the player’s and computer’s score will be 52.Use an array of 52 integers to store unique values for each- card. Write a method name FillDeck()that places 52 unique values into this array. Write…In the card game War, a deck of playing cards is divided between two players. Each player exposeda card; the player whose card has the higher value wins possession of both exposed cards. Createa console-based computerized game of War named WardCardGame in which a standard 52-carddeck is randomly divided between two players, one of which is the computer. Reveal one card forthe computer and one card for the player at a time. Award two points for the player whose cardhas the higher value. (For this game, the king is the highest card, followed y the queen and jack,then the numbers 10 down to 2, and finally the ace.) if the computer and player expose cards withequal values in the same turn, award one point to each. At the end of game, all 52 cards shouldhave been played only once, and the sum of the player’s and computer’s score will be 52.Use an array of 52 integers to store unique values for each- card. Write a method name FillDeck()that places 52 unique values into this array. Write…
- In c Hangman gameWrite a terminal based on the game of Hangman. In a hangman game, the player is given a wordthat they need to guess, with each letter of the word represented by an underscore/blank. Theplayer tries to guess a letter of the word by entering it into the terminal. If the letter is correct, theblank corresponding to that letter is filled in. If the letter is incorrect, a part of a stick figure isdrawn. The player has a limited number of incorrect guesses before the stick figure is fully drawnand the game is lost. The player wins the game if they guess all the letters of the word before thestick figure is fully drawn.The program should have an array of possible words to choose from. A different word should berandomly chosen from the array every time we run the program.Question: 2Implement the design of the Chillox and Customer classes so that the following code generates the output below:print(f"It's been a good day!. \nToday, we have already served {Chillox.order_id} customers.")print("**************************************************")outlet1 = Chillox()print("1.==========================================")print("Burger Menu:")print(Chillox.menu)print("2.==========================================")outlet1.addBurger("Chicken Burger",180,"Chicken with Cheese",200)print("3.==========================================")print("Burger Menu:")print(Chillox.menu)print("4.==========================================")c1 = Customer("Samin")c1.order = "2xChicken Burger"outlet1.placeOrderof(c1)print("5.==========================================")outlet1.addBurger('Chicken Smoky BBQ Cheese',225)c2 = Customer("Rafi")c2.setOrder("2xChicken with Cheese,3xChicken Smoky BBQ…**Java Code** Think Java Exercise 14.2 Write a loop that plays the game 100 times and keeps track of how many times each player wins. If you implemented multiple strategies in the previous exercise, you can play them against each other to evaluate which one works best. Hint: Design a Genius class that extends Player and overrides the play method, and then replace one of the players with a Genius object.



