(1) Consider the adjacency matrix A of a directed network of size N =4 given by 1 A = 1 0 0 1 0 we will indicate with 1 the column vector with elements N and we will indicate with Ithe identity matrix. In the following 1 for i = 1,2, - (a) Draw the network (b) Calculate the eigenvector centrality using its definition. (c) Calculate the Kate centrality. %3D %3D ... (1) lk gontrolity
(1) Consider the adjacency matrix A of a directed network of size N =4 given by 1 A = 1 0 0 1 0 we will indicate with 1 the column vector with elements N and we will indicate with Ithe identity matrix. In the following 1 for i = 1,2, - (a) Draw the network (b) Calculate the eigenvector centrality using its definition. (c) Calculate the Kate centrality. %3D %3D ... (1) lk gontrolity
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter2: Basic Linear Algebra
Section2.5: The Inverse Of A Matrix
Problem 11P
Related questions
Question
Course is Complex Networks. It would be appreciated if you please answer it in a shorter time span. Thanks
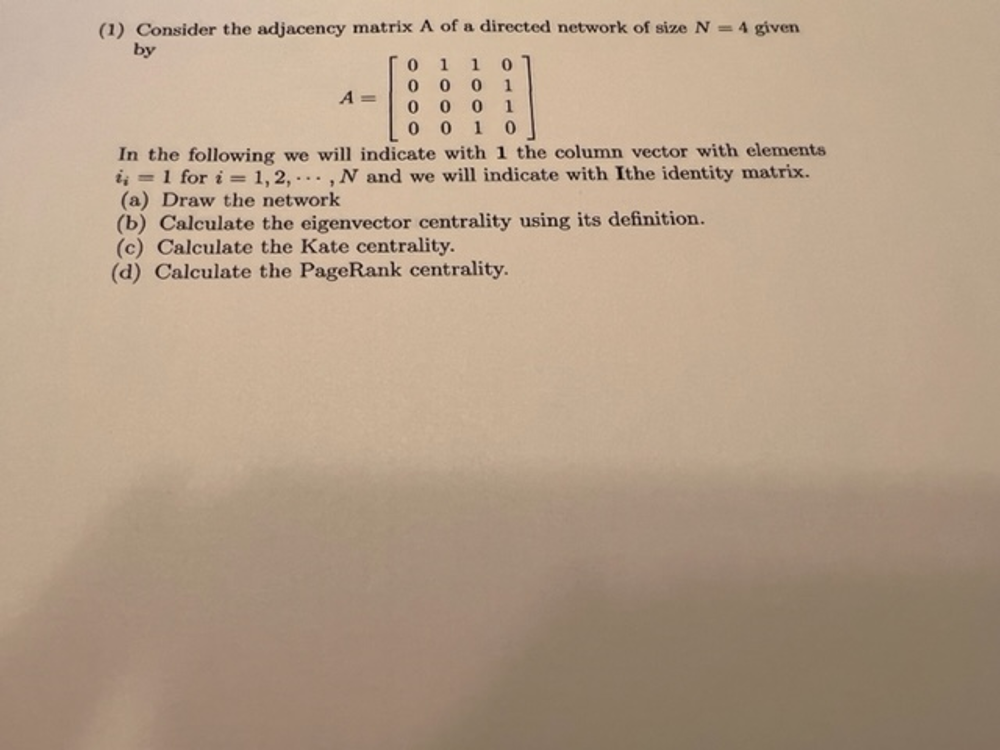
Transcribed Image Text:(1) Consider the adjacency matrix A of a directed network of size N 4 given
by
1
1
1
A =
0 0 0 1
0 0
In the following we will indicate with 1 the column vector with elements
i, =1 for i = 1, 2, ..., N and we will indicate with Ithe identity matrix.
(a) Draw the network
(b) Calculate the eigenvector centrality using its definition.
(c) Calculate the Kate centrality.
(d) Calculate the PageRank centrality.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole