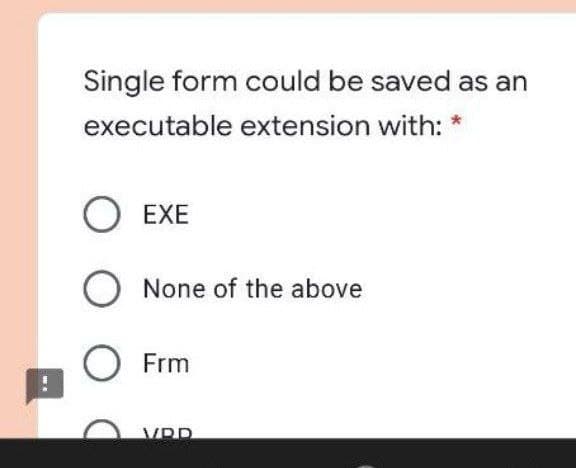
Single form could be saved as an executable extension with: O EXE None of the above Frm VRD
Q: 1. Write a program using switch statement to display the days of the week. For example if the user e...
A: Below is the solution for above questions in C Language, output of the screenshot is included at the...
Q: PHP exercise 1 For your first PHP exercise, echo the following statement to the browser: “Twinkl...
A: <?php echo "Twinkle Twinkle little star\n"; $txt1 = "Twinkle";$txt2 = "star"; echo $txt1 ." ". $t...
Q: What exactly is a page fault?
A: Introduction: Page Fault: It can be defined as a scenario in which takes a program while execution...
Q: You have numerous filesystems on your hard drive, each of which is mounted to a different directory ...
A: The possible causes can be: (i) The hard disk drive may be damaged. (ii) The file-system may be dama...
Q: What is open source in computer science?
A: This question comes from Internet Technologies which is a paper of computer science. Let's discuss i...
Q: What is the distinction between a call by value and a call by reference? What issues could emerge if...
A: answer is
Q: What is data mining and what sorts of information may be obtained from it?
A: Data mining: Data mining is considered as one type of process which is used to analyze the big amoun...
Q: When a fresh IP configuration is required, DHCP clients issue a DHCPREQUEST packet. Is this true or ...
A: DHCP Dynamic Host Configuration Protocol is a network management protocol. It is used on Internet ...
Q: In C#, why are Strings immutable?
A: Introduction: In reality, a string is a collection of characters. The CLR (Common Language Runtime) ...
Q: What does the superparamagnetic limit of disc drives imply?
A: Introduction: Superparamagnetism: A form of magnetism that appears in small ferromagnetic or ferro...
Q: Packets transmitted to a mobile host's home LAN are intercepted by its home agent on that LAN when i...
A: Intro Care-of address. when the Mobile host is not at home, it gets a temporary IP address. This IP ...
Q: 12. Perform the given calculations in base-five notation. Assume that the numerals are already writt...
A: Base 5 notation numbers contains number from 0 to 4.
Q: What exactly is database security? What are two methods for keeping a database safe?
A: Introduction: What exactly is database security? What are two methods for keeping a database safe?
Q: Assume your organisation has leased one Class C licence, 120.10.10.0, and wishes to sublet the first...
A: Introduction: CIDR notation is basically a compress representation of the IP address as well as its ...
Q: What is the underlying concept of MEMS storage?
A: Introduction: MEMS storage is employed in the development of small integrated devices or systems.
Q: Make a thorough note on software testing concepts, issues, and techniques.
A: Concept of Software Testing Testing is the final stage of a product's development before it is deli...
Q: Describe the distinctions between replication and duplication.
A: Introduction: the distinction between DNA replication and duplication is that replication primarily ...
Q: What are the different kinds of data patterns? Provide instances of each.
A: Data Patterns - The data patterns that are of different types are very much important and also usefu...
Q: List and explain the functions of the ten application framework components that are part of the Andr...
A: answer is
Q: 31. During the implementation phase of a project, the developer revises part of the project that has...
A: Regression testing is a sort of testing that is used to ensure that a software change does not affec...
Q: C++ PROGRAMMING EXERCISE Given an array of integers below, write a program to reverse all the elemen...
A:
Q: A Triangle will have 3 sides. The class will be able to keep track of the number of Triangle object...
A: the code is an given below ;
Q: computer science - Explain in your own words which process model you will use to design an online ho...
A: Introduction: The following are the reasons why I will use the Agile Process Model to design an onli...
Q: In C programming In a main function declare an array of 1000 ints. Fill up the array with random ...
A: Step 1 : Start Step 2 : In the main function, Declare an array of 1000 integers. Step 3 : Declaring ...
Q: What are implicit heap-dynamic variables, when, how, and why should they be utilised, and when shoul...
A: Intro Implicit heap-dynamic variable: Implicit heap-dynamic variable is a bound which is executed...
Q: Viewing HTML in web development software is called____. Group of answer choices Code View D...
A: Given :- Viewing HTML in web development software is called____. Group of answer choices Code Vi...
Q: What is the major distinction between key-value and document stores?
A: Introduction: There are 4 types of NoSQL databases: 1. Document database2. Key-value stores3. Colum...
Q: CPU Priority Scheduling-preemptive: Write a Java program to implement a priority scheduling algorith...
A: Below I have provided the java code:
Q: A process that spawns or initiates another process is known as. a. a child process b. forking c. bra...
A: Intro The process initiating another process Forking happens when developers take a copy of source ...
Q: What exactly is polymorphism? How can operator overloading help with polymorphism? To demonstrate, u...
A: Introduction: Polymorphism: The word polymorphism means having many forms. In simple words, we can d...
Q: Why is it critical that the protocols used on the Internet be freely available in their most basic f...
A: Intro the above question is about Why is it critical that the protocols used on the Internet be free...
Q: What is the name of the modulation technique that is utilized by twisted pair cable computer network...
A: Modulation: Modulation is nothing but a way to convert useful data into digital signals for just tra...
Q: Discuss and explain the importance of new cloud computing technologies that enable scalability.
A: Introduction: Cloud Computing: Customers can use cloud computing to obtain comparable programs throu...
Q: Why would a system designer want Unicode to be the default character set for a new system? What reas...
A: Intro Reasons for the system designer to use Unicode as default character set: Operating systems s...
Q: What is modelling language and how does it work?
A: Introduction: A modelling language is any artificial language that can express information, knowledg...
Q: What exactly is an APIPA?
A: APIPA stands for automatic private IP addressing. It is the feature of the operating system which en...
Q: s) A (p V r)) = (q V s) s Ab) A (1
A: Let n premises and C be its conclusion. Then an argument of the form P1 ∧P2 ∧...Pn ⇒C is written in...
Q: Define data mining as an enabling technology for corporate intelligence, as well as the applications...
A: Definition Data mining is defined as a process that analyzes the data from various sources and summa...
Q: What exactly is face validity?
A: Introduction: Validity signifies and states whether the test is actually and accurately measuring wh...
Q: Could you perhaps elaborate on how cloud scalability works and what it entails? What are some of the...
A: Introduction: Cloud computing refers to the on-demand availability of data storage and processing ca...
Q: C++ Define a problem with user input, user output, Pointers, and Pointer Arithmetic. If no output e...
A: a system that calculates user input values and displays the odd number of identical members on the...
Q: algorithms, pseudocode and flowchart of arithmetic formula
A: assume the arithmetic formula step 1: find the first and last term sn =2a + ( n - 1) d sn = nth ter...
Q: Construct a PDA that matches all strings in the language over {x,y} such that each string has at lea...
A: Initial state = q0 Final state = qF Strings accepted = xyyy, xxyyyy,...................................
Q: Why is it that on today's Internet, audio and video traffic is frequently carried through TCP rather...
A: Introduction: UDP: UDP stands for "User Datagram Protocol" which offers an unreliable and connection...
Q: Write a JAVA program to input a single line message from the user and check whether the message cont...
A: Write a JAVA program to input a single line message from the user and check whether the message cont...
Q: What are the most prevalent types of functions in C++? Using a program, define three typical types o...
A: Introduction A function is a block of statements that can be reusable and part of our program Based ...
Q: Describe the five phases of testing in detail.
A: Introduction: This cookie policy describes what cookies are and how we utilise them. Additionally, i...
Q: In terms of the amount of encryption operations required to send a big file, compare cypher block ch...
A: Intro Cipher block chaining mode in DES (Date Encryption Standard): It is a type of cipher mode whe...
Q: 1. Assume that all data and metadata begin on disk. Assume further that all inodes are in separate b...
A: The answer is given below:
Q: Exp
A: (T or F) 12 was a cooperative initiative between government, industry and google. O True False
Step by step
Solved in 2 steps

- Each of the following files in the Chapter.01 folder of your downloadable student files has syntax and/or logical errors. In each case, determine the problem and fix the program. After you correct the errors, save each file using the same filename preceded with Fixed. For example, DebugOne1.cs will become FixedDebugOne1 .cs. a. DebugOne1.cs b. DebugOne2.cs c. DebugOne3.cs d. DebugOne4.csWrite an application that displays the name, containing folder, size, and time of last modification for the file FileStatistics.java.Write an application that displays the name, containing folder, size, and time of last modification for the file FileStatistics.java. Example output: File name is FileStatistics.java Folder name is sandbox File's size is 884 File's creation time is 2018-05-30T16:28:01.410343Z
- Modify it and should pass 2 testcase if not then Thumbsdown.Lets say I have 2 forms Form1 and Form2 since I created form1 first its going to run first. How do I make form2 run first instead of form1 what method should I implement in Form2 or in form1 to make this happen on run time C# windows form. Please helpWhich of the following is TRUE about a postfix expression? Stack of bricks The operator follows its two operands Table of contents The operator is between its two operands
- Please help with the below C# Windows Forms code, to get the Luhn method to work to validate the SSN / Swedish person number. Please see the bold below I have errors at the "return (sum % 10) == 0;" below. Please send back the answer in whole with the changes in the code. Thanks! using System; using System.CodeDom.Compiler; using System.Windows.Forms; namespace WindowsFormsApp1_uppgift_3 { class Person { public string firstName { get; set; } public string lastName { get; set; } public string securityNumber { get; set; } public Person(string firstName, string lastName, string securityNumber) { this.firstName = firstName; this.lastName = lastName; this.securityNumber = securityNumber; } public string Checking() { try { if (securityNumber.Length > 0 && securityNumber.Length % 2 == 0 && ((Convert.ToInt64 (securityNumber) % 100) / 10) % 2 == 1) { return "Correct personnummer, Male."; } else if (securityNumber.Length > 0 && securityNumber.Length %…Each of the following files in the Chapter.10 folder of your downloadable student files has syntax and/or logical errors. In each case, determine the problem and fix the program. After you correct the errors, save each file using the same filename preceded with Fixed. For example, DebugTen01.cs will become FixedDebugTen01 .cs. a. DebugTen01.cs b. DebugTen02.cs c. DebugTen03.cs d. DebugTen04.csEach of the following files in the Chapter.04 folder of your downloadable student files has syntax and/or logical errors. In each case, determine the problem, and fix the program. After you correct the errors, save each file using the same filename preceded with Fixed. For example, save DebugFour1.cs as FixedDebugFour1.cs. a. DebugFour1.cs b. DebugFour2.cs c. DebugFour3.cs d. DebugFour4.cs
- The name of a class file ends with which of the following filename extensions? .cla .cls .vb None of the above.What type of object is created by the OpenText method? a. File b. SequenceReader c. StreamWriter d. None of the above.Each of the following files in the Chapter.05 folder of your downloadable student files has syntax and/or logical errors. In each case, determine the problem, and fix the program. After you correct the errors, save each file using the same filename preceded with Fixed. For example, save DebugFive1.cs as FixedDebugFive1 .cs. a. DebugFive1.cs b. DebugFive2.cs c. DebugFive3.cs d. DebugFive4.cs







