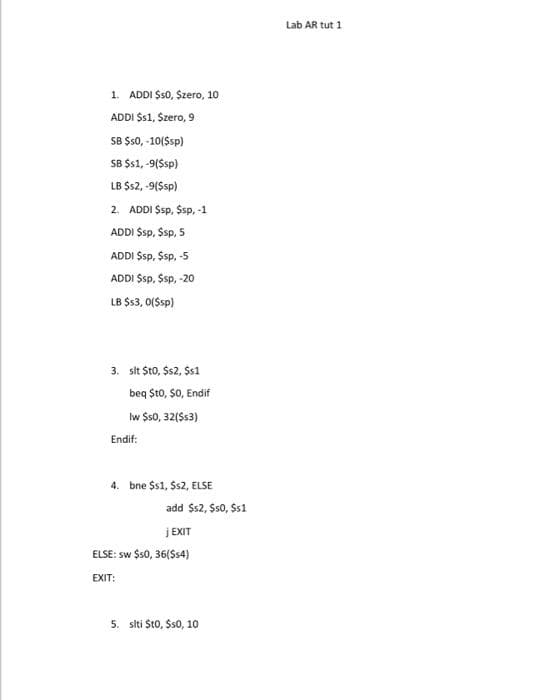
1. ADDI Ss0, Szero, 10 ADDI Ss1, Szero, 9 SB $s0, -10(Ssp) SB $s1, -9(Ssp) LB $s2, -9(Ssp)
Q: 1. log(n) = O(n) 2. n= O(log n) 3. log? (n) = O(n)
A: Note: A per our company guidelines, we are supposed to answers only the first three subparts. Kindly...
Q: A 32-bit signed integer may be stored in which data type?
A: A 32-bit that means 4 bytes singed integer can be store the following way. This differs programming ...
Q: Identify the basic business processes included within the scope of product lifecycle management.
A: -Product lifecycle management (PLM) is the process of managing the life cycle of products, services,...
Q: What skills are needed for predictive modelling?
A: Introduction: Predictive analytics use analytics approaches to analyse historical and present data i...
Q: What exactly is a computer programme?
A: Intro Computer program: A computer program is a set of instructions that are given to a computer to...
Q: Brie and I are talking about evaluating emanic rules in syntax-directed definin. 1009 44 ENG IN 1/1 ...
A: Intro Semantic rules of syntax-directed translation are basically evaluated in order to calculate th...
Q: Was there a "desktop computer" before this?
A: Desktop computer is a computer which is designed for the regular purpose and this is used at a singl...
Q: Software Design
A: The answer of 1: Is B(Software Development) Explanation: A) Software style is that the method by tha...
Q: Question 2 (1 point) Consider the following sequence: aj = 2, and 2a,-1 + 1, for n > 1. an What is t...
A: Question 2 (1 point) Consider the following sequence: al = 2, and an = 2an_1 + 1, for n > 1. What...
Q: For m=4 bits, using the signed two's complement representation, (neatly) construct a table consistin...
A:
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms prop...
A: please find the handwritten solution in step 2
Q: °Mouses with an optical sensor that can tell when the mouse moves.
A: An optical mouse is a mouse, which uses a light source (LED) and light detector,
Q: A complex number has two parts: real value and imaginary value. In mathematics, we learnt how to add...
A: Answer: Code : Code : class Complex { int real, imaginary; // Default constructor C...
Q: What's the problem with the fracture risk algorithm?
A: The facture risk algorithm was invented by World Health Organization to calculate the 10-year probab...
Q: Given the IP address 153.36.147.82 and assuming 4 bit subnetting, answer the following questions. A....
A: The answer is
Q: What is a downgrade attack, and how can you fight back against it?
A: An attack on a computer system compromises its security.
Q: Consider a database system for an airline that employs snapshot isolation. Describe a situation in w...
A: Given: Consider a database system for an airline that employs snapshot isolation. Describe a situati...
Q: Write the contents of a specification file for a c++ class named ContestResult that contains the fo...
A: what is Class in C++? In C++, a class is the fundamental building element of Object-Oriented program...
Q: PYTHON ONLY AND PLEASE COMMENT CODE 1. A) write a For loop that iterates through a list of product...
A: #A. list of products that are sold in a storelst = ["fan", "fridge", "freezer", "washer", "televisio...
Q: t will be the
A: given - What will be the initial value which front is initialized?
Q: Write a NumPy program to combine last element with first element of two given ndarray with different...
A: The Missing code will be: result = np.r_[array1[:-1], [array1[-1]+array2[0]], array2[1:]]
Q: What kind of error messages may you get if you try to login using the ssh -i option?
A: The Answer is
Q: A hypothetical video game involves two phases. In the first phase, players negotiate to obtain weapo...
A: Given That: (1) In the first phase, players negotiate to obtain weapons and resources by sending an...
Q: List all the ways to select two different members from S without repetition. The order in which memb...
A: The order in which members are selected is important:-
Q: Write a segment code in any language you prefer that behaves differently if the language used ...
A: Given :- Write a segment code in any language you prefer that behaves differently if the language us...
Q: For questions 2-4, please refer to the neural network equations below: "- xw "-(my -"wn -(") -E- ()-...
A: Let's see the solution in the next steps
Q: Given a vector of strings, write a CPP program to concatenate all the strings present in the vector ...
A: Given: A vector of strings is given. vector<string> strs = {"VECTOR", "vector", "Program", "ve...
Q: Justify the requirement for a trained project manager to oversee complicated tasks.
A: According to the question the project manager always has power to conduct something explain everyone...
Q: A function best allows code to be... O Written early in the program but not executed until later O R...
A: About python functions and for loops
Q: Brief information about matlab software
A: MATLAB software is a high level language software which is used for the object oriented programming....
Q: LWC Assignment: Create a LWC component to display the output: Data Binding Example Hello, Jhon Ron! ...
A: Lightning Web Components uses core Web Components standards and provides only what’s necessary to pe...
Q: --Problem -3 -Create a flowchart design that depicts the solving of the following problem: Asks user...
A: logic:- read a, b and c if a>b && a>c display a is maximum if b>a && b>...
Q: C code into MIPS assembly
A: Program Code: sub sp, sp, #16 mov w0, 5 str w0, [sp, 12] ...
Q: TablerPC-PT Tabiet PCO PC-PT PCO Server-PT STC Server SMARTPHONE-PT Smartphoneo Cloud-PT Cloudo Home...
A: Step 1 : c. Find the configuring devices using the desktop tab tutorial.what information can you con...
Q: 15) Let M be the language over {a, b, c, d, e, f} accepting all strings so that: 1. There are precis...
A:
Q: Q10 Data consistency is a big deal in data processing. a. What needs to be sacrificed, to ensure hig...
A: Data Consistency: In database systems, consistency (or correctness) refers to the condition that eac...
Q: Design a windows (WPF) application which will display contents from your local movie Db. Demonstrate...
A: Design a windows (WPF) application which will display contents from your local movie Db. Demonstrate...
Q: Consider the following C program: int fun(int *i) { *i +=10; return 9; void main() { int x = 6; %3D ...
A: concept of pointer for the value of pointer we use %u
Q: It includes encoding and testing of the project components and its entire system evaluation planning...
A: A software is collection of instructions that is used to execute a specific task. Software developme...
Q: Fred was frightened to be alone in the old house.
A: arrangement
Q: Mr. Ali deposits an amount x in a Bank. The bank gives an annual interest of 6% and also charges a m...
A: function main(): Start Declare amount, interest, service_charge, interest_earned, final_amount Read...
Q: What is regression testing?
A: Here is the solution with an explanation:-
Q: The word "API" refers to a programming interface for applications. What does this mean in terms of h...
A: API is a representation of hardware components on the software level, which is generated from a hard...
Q: The following three questions are related to conversion of 100.00011 x 2° using IEEE 754 floating po...
A: IEEE Standard 754 floating point is the most common representation today for real numbers on compute...
Q: Please do it with regular expression. Don't use loops please. Do fast, I have no time left Write a j...
A: Required:- Please do it with regular expression. Don't use loops, please. Do fast, I have no time l...
Q: (a) Find all those graphs G of order n ≥ 4 such that the subgraph induced by every three vertices of...
A: Consider the graph G as a subgraph of a complete graph Kn. Then G must contain exactly two edges fro...
Q: -Create a flowchart design that depicts the solving of the following problem: Asks user to input thr...
A: Start Take Num1, Num2, Num3 three numbers as an user input Check if Num1 is greater than Num2 and Nu...
Q: Justify the requirement for a trained project manager to oversee complicated tasks.
A: According to the question the project manager always has power to conduct something explain everyone...
Q: O consider the consider the followlng tables :- table names : sales city paris Salesman-id commissio...
A: SQL is used to communicate with the database. It supports several queries to create a table, insert ...
Q: Prepare a presentation using the presentation program you chose, on one of the following topics:
A:
Step by step
Solved in 2 steps

- 1- What is the optimal mutual exclusion strategy in OpenMP if a critical section looks like x += b;? Assume there are no other crucial portions in the program. a. lock b. critical section c. atomic 2- What is the optimal mutual exclusion strategy in OpenMP if a critical part looks like x += c; y+=b;? Assume there are no other crucial portions in the program. a. lock b. critical section c. atomic 3- In OpenMP, we can't always tell how many crucial sections are in a program just by glancing at the source code. a. True b. False 4- Let's say we want to start a kernel with the following command: kernelname 4,4>>> (argument list...);Let's say the kernel has a global variable called x. How many x instances will there be? a. 16 b. 4 c. 8 d. 1 e. 2An ISP is granted a block of addresses starting with 160.40.0.0/16. The ISP wants to distribute these blocks to 2600 customers as follows. a. The first group has 200 medium-size businesses; each needs 128 addresses. b. The second group has 400 small businesses; each needs 16 addresses. c. The third group has 2000 households; each needs 4 addresses. Design the subblocks and give the slash notation for each subblock. Find out how many addresses are still available after these allocations.A buddy system allocates memory from a fixed-size segment consisting of physically contiguous pages using a power-of-2 allocator. Consider a computer system that has 256M memory available. By using diagram, show the results of each memory request/release via memory layout at each stage according to the followings orders: requests 25M requests 110M requests 52M Release A Release C requests 75M Page Time Loaded Last Reference R bit M bit 2 117 212 1 1 0 130 264 0 0 3 58 240 1 0 1 86 203 1 1 In your own words, explain what happened to the memory block prior to the last request allocation. Calculate the total of internal fragmentation (in M unit) after memory allocation to request C is fulfilled.
- Consider the following snapshot of a system: Allocation Max A,B,C,D A,B,C,DP0 0,2,0,2 2,3,3,8P1 1,3,2,2 3,5,2,5P2 1,2,0,1 3,4,5,1P3 2,1,1,1 3,2,1,3P4 1,0,2,0 2,3,3,1 Using the banker’s algorithm, determine whether or not each of the following states is unsafe. If thestate is safe, illustrate the order in which the processes may complete. Otherwise, illustrate why thestate is unsafe . Show algorithm procedure a. Available = (1, 2 , 0, 2)b. Available = (2, 1, 0, 2)An ISP is granted a block of addresses starting with 150.80.0.0/16. The ISP wants to distribute these blocks to 2600 customers as follows: The first group has 200 medium-size businesses; each needs approximately 128 addresses. The second group has 400 small businesses; each needs approximately16 addresses. The third group has 2000 households; each needs 4 addresses. Design the subblocks and give the slash notation for each subblock. Find out how many addresses are still available after these allocations.An ISP is granted a block of addresses starting with 10.100.10.0/16.The ISP needs to distribute these addresses to three groups ofcustomers as follows:. The first group has 64 customers; each needs 128 addresses.. The second group has 128 customers; each needs 128 addresses.. The third group has 128 customers; each needs 32 addresses.. Design the sub blocks and find out how many addresses are still available after these allocation.
- Process P0 and process P1 both want to access a shared datum, X, which is currently 0. P0 wants to add 2 to it, P1 wants to add 3 to it. Answer the following.a. Without synchronization, what value(s) can X result in?b. With synchronization, what value(s) can X result in?c. If another process, P2, was supposed to access X after P0 and P1 completed their stores, where P2 sets X to 5, would your answer to a or b change?110. A system has 12 magnetic tape drives and 3 processes : P0, P1, and P2. Process P0 requires 10 tape drives, P1 requires 4 and P2 requires 9 tape drives.Process P0 P1 P2 Maximum needs (process-wise : P0 through P2 top to bottom) 10 4 9Currently allocated (process-wise)522Which of the following sequence is a safe sequence ? a. P0, P1, P2 b. P1, P2, P0 c. P2, P0, P1 d. P1, P0, P2Q: Answer the following questions 1. What is the munin problem in FIFO quening nd what do you suggest fo overcome this problem? 2. Explain the flow specification parts in IntServ In IntServ. 3. Distinguish between guarantecd services and controlled-load services. 4. Why are Path and Resv messages needed in RSVP?
- “Dirty bit is used to reduce the overhead of page transfer”. Statewhether the given statement is true or false. Justify your answer withsuitable example.An ISP is granted a block of addresses starting with 129.80.0.0/16. The ISP wants to distribute these blocks to 2600 groups as follows: i. The first group has 200 medium sized businesses; each needs 14 hosts. ii. The second group has 400 small businesses; each needs 6 hosts. iii. The third group has 2000 point-to-point links; each needs 2 hosts. iv. Design the sub-blocks and give the slash notation for each sub-block1) What are the available resources for R1 and R2? a. 0 and 0 respectively b. 2 and 4 respectively c. 2 and 1 respectively d. 1 and 1 respectively 2) What is the remaining resource need of process A? a. R1=4, R2=2 b. R1=0, R2=2 c. R1=1, R2=2 d. R1=3, R2=0 3) What is the remaining resource need of process D? a. R1=1, R2=2 b.R1=0, R2=1 c. R1=3, R2=0 d. R1=1, R2=1 4) What is the current state of the system? a. System has circular path b. The system is in safe state c. It is unsafe state d. The state is undetermined 5) What is the safe sequence of the system? a. <D C B A> b.<D B C A> c. None, because it is unsafe d. <D C A B>

