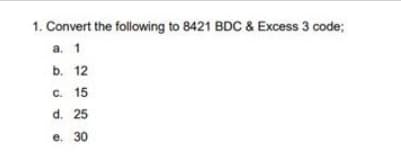
1. Convert the following to 8421 BDC & Excess 3 code; a. 1 b. 12 c. 15 d. 25 e. 30
Q: Identify three protocols that are insecure or prone to attack in the organisation since the network…
A: Protocol for Address Resolution 1 (ARP) A protocol for determining a media access control (MAC)…
Q: We'd appreciate it if you could identify any three protocols that are unsecure or prone to attack…
A: Three network protocols that are susceptible to attack must be turned on. The three procedures are…
Q: List the arithmetic operators used in BASIC and state their priorities of execution in a statement.…
A:
Q: Given the following truth table: Inputs ABC 000 0 001 1 010 0 011 0 100 1 101 1 110 0 111 1 e.…
A: K- map is used to simplify the boolean expression.
Q: (Q3)The matrix A= [3 3 3; 5 2 1; 7 5 1] create the submatrix as the following: 1- B matrix is the…
A: All the submatrixes are given below in MATLAB form A = [3 3 3 ; 5 2 1 ; 7 5 1 ] or A = 3 3 3 5…
Q: As far as strength of encryption is concerned (how secure is the cipher), Domain Validation (DV) and…
A: Answer: An Extended Validation SSL Certificate (otherwise called EV SSL for short) is the most…
Q: 4- To prevent print the result statement in MATLAB we can put a- semicolon. b- end. 5- A[2,4] refer…
A: Answers 4: *) To prevent print the result statement in MATLAB we can put Semicolon in the end .…
Q: Describe the differences between services in cloud. Write in paragraph.
A: NOTE :- Below i explain the answer in my own words by which you understand it well. There are…
Q: Model-driven engineering's advantages are well-known, but how successful is it in actual use?…
A: Model-Driven Engineering: Model-driven engineering, often known as MDE, is an approach to software…
Q: Is it possible to determine whether or not a given graph is linked using DFS? A step-by-step…
A: Given: Is it possible to identify whether two graphs are connected using DFS? If you can discover…
Q: brother country watch child person
A: Plural words for Country Watch Child Person
Q: is the displayed text in---- command widow as a result >>x= [5, ;4, 8, 1/2, 2.33] 5 4 8 1/2 2.33.…
A: Find the required answer with explanation given as below :
Q: What is a system of record? Under what conditions does a designer need to declare one system to be…
A: Please find the answer below :
Q: Should the security needs of society, the owners of the information system, and the users of the…
A: Given: It safeguards the company's operations. It ensures the safety of IT applications. It…
Q: Use Input to print "< =" and stop the program until the user enters a value and presses the Enter…
A: While loop is used to solve this
Q: Consider how the internet has evolved through time and how it depends on the current technical…
A: Answer:
Q: Given the following NFA. Draw the computation tree for the string 1000 0 0 1 90 0 1 (92) 0,1 91 0,1
A:
Q: What difficulties were intended to be remedied by the initial Internet research? In the end, how did…
A: Introduction:- Difficulties were intended to be remedied by the initial Internet research? In the…
Q: ther information about the metrics used in the software development process, if that is possible?…
A: Introduction: Software development metrics are useful quantification of a software project that aid…
Q: True/False Questions (. 1. If the "Primal" objective function is a "maximization" problem, then the…
A:
Q: What determines event order in text-based environments like the command line?
A: Given: The issue focuses on the progression of activities that takes place whenever a user runs a…
Q: What was the goal of the early Internet research? In the end, how did these issues get resolved?
A: Answer: The Internet has changed the PC and correspondences world don't like anything previously.…
Q: Q3) Design a perceptron neural network to distinguish patterns between bananas and pineapples, based…
A: According to the information given:- We have to design a perception neural network to distinguish…
Q: For those in charge of setting up the network at a university, selecting the suitable NAT method is…
A: Step 2 contains the first answer to the aforementioned query. The most popular justification for…
Q: What are the distinctions between IT security solutions for on-premises data centers and those for…
A: Today’s businesses can decide between on-premises vs. cloud solutions for just about every element…
Q: Which metrics are utilized when performing maintenance on software?
A:
Q: A systems analysis can't capture all of the details of a process, so consider how you may utilise…
A: System analysts must be knowledgeable about computers and systems, as well as possess the…
Q: Describe the differences between for services in cloud
A: The complete solution is given below:-
Q: 1 You have matrix A = 5 9 2 6 10 34 78, what will be result by code >>A (1:2, 3:4); 11 12
A: This can be done in MATLAB.
Q: B/ let x=[ 2 -3 5 ;0 11 0], y=[ 1 0 9 ;0 0 6], write a matlab code to find: 1- Not x. 2- x and y 3-…
A: Please refer below for your reference: language used is MATLAB: ismember is an inbuilt function of…
Q: Discuss the evolution of information systems while focusing on the significant people and events…
A: Given: Discuss the development of information systems, focusing on the significant individuals and…
Q: Consider who would be interested in using your warehouse's data. There are a number of ways to…
A: Warehouse of data: Users will be able to access enormous volumes of data quickly and easily using a…
Q: What are the goals of prototyping in software engineering and how does it achieve them?
A: Following are some of the goals of prototyping. Prototyping lowers the cost of development by…
Q: To what extent can you tell the difference between operating systems that support real-time…
A: Real-time applications- 1)Real-time task is the task that is associated with a time-bound. 2)It can…
Q: Which of the following statement(s) is/are TRUE in the area of artificial intelligence? Select one…
A: Artificial intelligence is the simulation of the human intelligence in machines that are programmed…
Q: Choose the appropriate NAT mechanism if you are the network administrator for a university. Explain…
A: Network address translation (NAT) changes the network address information in the IP header of a…
Q: please code in python You are probably familiar with the famous Fibonacci sequence of numbers,…
A: The question is to write the recursive python code for the given problem.
Q: The difference between overloading and generics can be explained. Ad hoc polymorphism is sometimes…
A: Given: A subnetwork is a network that exists inside another network. Subnets make networks more…
Q: 3-) Find a,b,c. a) 2.5 GB in MB? b) 32 x 2¹0 bits in KB? c) 3.5 MB in bits?
A: The conversions of sizes are, 1 Byte= 8 bits 1 KB= 210B 1 MB= 210KB 1 GB= 210MB
Q: This is the data frame for: Idle Select one: O O O Frame Start DO D1 D2 D3 D4 D5 D6* D7* D8* P* Stop…
A: Lets examine the dataframe 1) It can't be SPI protocol as it doesn't have start, stop and pairty…
Q: Write a sample JSON document that has a structure consistent with the conceptual schema given above.…
A: Please check the step 2 for solution
Q: 1- Current Directory Browser used to?
A: Given 1. To know about the current directory browser in Matlab.
Q: (Q3) The matrix A= [3 3 3; 5 2 1; 7 5 1] create the submatrix as the following: 1- B matrix is the…
A: Hey there, I hope you find my solution helpful. Also, part 4 is wrong as A matrix doesn't have the…
Q: Write the program to print odd number from (1:11) using for loop?
A:
Q: How is 0b0110 written in decimal? (a) 10 (c) 6 (b) 0d0110 (d) 42
A: Due to company policies I am compelled to solve only one question and that is the first question.…
Q: parallel and running programs concurrently
A: Hey there, I hope you find my solution helpful.
Q: In a company, worker efficiency is determined on the basis of the time required for a worker to…
A:
Q: How is 0xD3 written in binary? (a) 0b1001 0011 (b) 0b1101 0101 (c) 0b11000011 (d) 0b1101001
A: Find the required answer with explanation given as below :
Q: For example, malicious traffic may be switched from one VLAN to another, resulting in a network…
A: Observation In the early stages of an assault, a nation-state finds its goal. Examining pertinent…
Q: An explanation of file extensions and the applications that create them will be provided in this…
A: Explanation of File Extensions: File extensions are used by computers to indicate the kind of a…
Step by step
Solved in 3 steps with 2 images

- Please please don't copy Computer Science for BCH (16,12). when input is (0, 4, 14, 14, 4, 4, 15, 2, 4, 2, 15, 13), what are the check digits?USE X = 9 AND Y = 3GIVEN THE FOLLOWING DATA AND CODE >> A= [1,1/2,3;6,10,1;0,3,2] A = 1.0000 0.5000 3.0000 6.0000 10.0000 1.0000 0 3.0000 2.0000 >> B= [0,-8,10;5,3,1] B = 0 -8 10 5 3 1 >> C= [4,9,-3;13,0,7;1,2,11] C = 4 9 -3 13 0 7 1 2 11 >> D= [A(3,3);A(2,1);C(2,2);C(1,1)] D = 2 6 0 4 >> E= [A(1,:);B(2,:);C(2,:)] E = 1.0000 0.5000 3.0000 5.0000 3.0000 1.0000 13.0000 0 7.0000
- This problem covers floating-point IEEE format.(a) Assuming single precision IEEE 754 format, what is the binary pattern for decimal number -6.16?(b) Assuming single precision IEEE 754 format, what decimal number is represented by this word:0 01111100 01100000000000000000000(Hint: remember to use the biased form of the exponent.)Insert =,< ,> as appropriate in the problem 1/6,1/8 B. 1/4, 1/3 C. 1/5 ,1/8Need asap in JAVA 4. Reading data from movies.txt must handle invalid input. - Check for number of values provided - Check for valid movie Ids. Must be Integers

