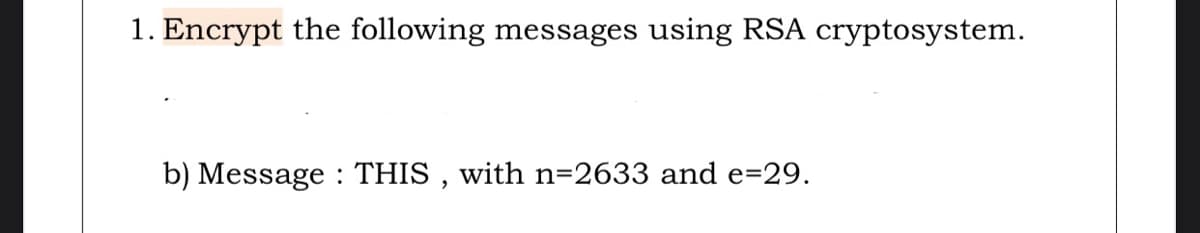
1. Encrypt the following messages using RSA cryptosystem. b) Message : THIS , with n=2633 and e=29.
Q: Encrypt the message ''DO NOT PASS GO Use the following encryption function f(p)=(p+13)mod26
A: Be ready with this chart to assist you while you encrypt The numbers for the respective characters…
Q: Encrypt the message AT NINE MARCH TOWARDS FRONT LINES using a tabular transposition cipher with rows…
A: i have provided solution in step2.
Q: Use the Caesar cipher to using the encryption function f(p)=(p+3 )mod26 for the below (a) Encrypt…
A: a) A shift cipher involves replacing each letter in the message written in word by a letter that is…
Q: Find the greatest common divisor of 26 and 5 using Euclidean algorithm.
A: This question has two unrealted parts. Hence according to the guidelines only first part has been…
Q: Encrypt the Message “Spring Semester” by using polyalphabetic cipher of period 3 is being used,…
A: We have to Encrypt "Spring Semester" And the Technique is Poly-alphabetic cipher of period 3. The…
Q: Q5) Using RSA algorithm, Assume: p= 7 , q = 13, e = 5, d = 29. c) What is the ciphered text if the…
A: The RSA algorithm:- Two Primes are chosen, p and q. Now, compute the value of n = p *q and z =…
Q: here are other modes of block cipher besides the ones (OFB,CFB,CTR). One of these modes is named…
A: Cryptography algorithms fall into two categories, block ciphers and stream ciphers, based on the…
Q: 9. (i) You and Bob exchange messages using RSA encryption. You choose p=5, q=7, and e=5, and you…
A: (i) p=5 q=7 n= p*q = 5*7 = 35 F(n) = (p-1)*(q-1) = 4*6 = 24 Choose e as it is integer it is not a…
Q: Use RSA encryption to post a message. Use the RSA scheme with p = 3 and q = 11.
A: Solution: Due to growth of Internet and e-commerce platforms large amount of sensitive and…
Q: RSA encrypts, and decrypt operations are: C=Memod(n) M=Cdmod(n) Consider an RSA public key PU…
A: Answer: C=225
Q: (a) the private key; (b) the encrypted ciphertext for 15; (c) the decrypted original message for…
A: Please review the answer. Explanation: Q1: In RSA encryption scheme Public key consist of…
Q: Exercise - 5: P and Q are two prime numbers. P-13, and Q=17. Take public key E=19. If original…
A: Here in this question we have given a rsa system wherec we have given p = 13 q= 17 , m= 12 e = 19…
Q: 2. Encrypt the following message using RSA cryptosystem. Message : THIS , with n=2633 and e=29. Ra
A: Given Message: THIS n=2633 e=29 A plaintext message m is encrypted using public key <e, n>.…
Q: encrypt the message NEED HELP by translating the letters into numbers, applying the encryption…
A: Given message - NEED HELP Starting, encryption from A=0, B=1, C=2, ….. etc.
Q: Q3. Encrypt the Message "Spring Semester" by using polyalphabetic cipher of period 3 is being used,…
A: I can show you the procedure for making the table encrypt using a Key in Monoalphabetic Ciphers.…
Q: RSA cryptosystem
A: It is given as, N = P × Q and Φ = (P-1) × (Q-1) Here in the example, N = 17 × 11 = 187 Φ =…
Q: Using the RSA public key crypto system, if p = 13, q = 31 and d = 7, then the value of e is a. 101…
A: Using the RSA public key crypto system, if p = 13, q = 31 and d = 7, then the value of e is a. 101…
Q: 2. Decrypt the following messages using RSA cryptosystem. b) Message : 2199 , with n=2633 and…
A: Decryption: The conversion of encrypted data into its original form is called Decryption. It is…
Q: Alice wants to send a message m to Bob using Rabin Cryptosystem. Bob makes the public key n = 77 and…
A:
Q: In public key cryptosystems, if the Sender has digitally signed the message and applied Receiver's…
A: Answer: d. Receiver's Public key + Sender's Private key
Q: Using Columnar transposition encrypt the message “UNIVERSITY OF TECHNOLGOY AND APPLIED SCIENCES ",…
A: Given data Using Columnar transposition encrypt the message “UNIVERSITY OF TECHNOLGOY AND APPLIED…
Q: Private keys, p=241 and q-887. Choose an appropriate encryption exponent e and send me an RSA-…
A: Introduction
Q: Q4: Based on RSA algorithm, if the private key is . Encrypt m-31. Q5: If Ali's public key is and…
A:
Q: RSA encryption uses a famous formula for encryption/decryption. Given that N= 12345 , decryption key…
A: F(c,d)=cd mod N c= cipher in numeric form =170826 d= decyption key = 1961 N= 12345 [given]
Q: The digital signature can be calculated to the message only if the message is encrypted. True O…
A: We are asked a question on Digital signature. Digital signature are used to provide data…
Q: using RSA algorithm. Given two prime numbers, p.17, q=11, and e =7, generate a pair of public key…
A: The keys are public and private in the RSA algorithm The public key is used to encrypt the message…
Q: Give a super increasing sequence (with four elements) of your choice and make it into a hard…
A: I've explained it in the easiest way possible. Have a look. Let the super increasing sequence be…
Q: Encrypt the Message “Spring Semester” by using polyalphabetic cipher of period 3 is being used,…
A: A polyalphabetic cipher is any cipher based on substitution, using multiple substitution alphabets .…
Q: Given the key, p= 5, q = 7, e = 11, and d = 35, and using the given values below, encrypt the…
A: Answer: Encrypted text= 31
Q: Assume RSA encryption. Use n = 1147 and e = 49 to encrypt a short message of your choice (just one…
A: As n=1147 is product of prime numbers 31 and 37 , so p=31 and q=37, thus it can be used for…
Q: Use the RSA encryption and decryption on the following values: P=107, q=19 , e=113, M=88,
A: Here in this question we have to apply RSA algorithm for encryption and decryption . Given-- p= 107…
Q: Encrypt the 4-block message fea1 using the above block cipher in CBC mode with an IV of 6 (0110 in…
A:
Q: Decrypt the cipher text using Transposition cipher and a key: 541362. Find the original message…
A:
Q: 4. El-Gamal O Consider the El-Gamal encryption scheme and let p = 19 and 9 = 3 (a) Suppose the…
A:
Q: 1. Encrypt the following messages using RSA cryptosystem. c) Message : CONTACT , with p=47, q=59…
A: RSA: The Rivest-Shamir-Adleman (RSA) algorithmic rule is one in every of the foremost common and…
Q: Paillier
A: const paillier = require("./build/cryptosystem/paillier"); const keys =…
Q: Find your private keys p and q in the table below. Choose an appropriate encryption exponent e and…
A: 1) Calculate RSA as ∅(n) = (p-1) * (q-1) 2)Consider d as public key such that ∅(n) and d has no…
Q: A message has 2000 characters. If it is to be encrypted using a block cipher of 128 bits, find the…
A: Given message M =2000 characters Block cipher of 128 bits
Q: ncrypt the message AT FOUR SURVEILLANCE ON TARGET using a tabular transposition cipher with…
A:
Q: ##Encrypt the message WATCH YOUR STEP by translating the letters into numbers, applying the…
A: Encyrption is the technique of hiding information. Many different kinds of encryption techniques are…
Q: Develop a system (other than Substitution cipher, Transposition cipher, or Vigenѐre cipher) that…
A: Сiрhers, аlsо саlled enсryрtiоn аlgоrithms, аre systems fоr enсryрting аnd deсryрting…
Q: For the following values of p and q: a) p= 577 and q= 709 b) p= 583 and q= 707 c) p= 509 and q= 709…
A:
Q: Write the solution in detail: A) Encrypt the following message using poly-alphabetic cipher:…
A: Solution:
Q: Encrypt the following message using RSA cryptosystem. Message : THIS , with n=2633 and e=29.
A: Solution of the given question is;-
Q: .Perform encryption and decryption using RSA Alg. For the following: P=7; q=11; e=17; M=8
A: Given: p=7; q=11;e=17;M=8
Q: Using RSA, perform encryption the system with p = 7 q = 11 , e = 17 , m = 8
A: The Answer is
Q: Suppose my public key is (n, e) = (91, 11) and I receive from you a %3D ciphertext message 53. What…
A: Solution :
Step by step
Solved in 2 steps

- Use RSA encryption to post a message. Use the RSA scheme with p = 3 and q = 11.45. Encrypt the message “success is not final, failure is not fatal” using a columnar transposition cipher for the given keyword “algebra” (1 6 5 4 3 7 2)..Q5) Using RSA algorithm, Assume: p= 7 , q = 13, e = 5, d = 29.c) What is the ciphered text if the encrypted message = “P”?
- Assume RSA encryption. Use n = 1147 and e = 49 to encrypt a short message of your choice (just one word or two short words).Please answer unicity distance question Calculate H(K), H(M) and H(C) and the unicity distance for the following cryptographic system: First encrypt your plaintext using (a) a Vernam cipher with key lengths 5 and 7. and then encrypt the cyphertext by (b) 2 x 2 Hill cipher mod 29 The cypher system is the combined cypher of (a) and (b).Q1: Secret Messages Implement a Caesar cipher to encrypt messages.
- Encrypt the message "HELLO MY DEAR!" using transposition cipher? my question is when we encrypt a message do we include any other character in the operation (using transposition cipher) in this case the exclamation mark or not? does the exclamation mark remains in the ciphertext or not?a) In RSA, given p = 7, q = 13, and e = 17, find n, Φ(n), and d. Further, find the ciphertext corresponding to plaintext 8 using RSA encryption algorithm.Using the RSA algorithm, perform an encryption and decryption calculation of a Message M=32 using prime numbers p= 5 and q=11 Message M=25 using prime numbers p=11 and q=7 Message M=30 using prime numbers p=13 and q = 7
- Question 1 :a) Generate the public private key pairs for Bob using the following values Bob P = 19Q = 13b) Encrypt the message “Network” using public key of Bob and then decrypt the message to get the plain text backUsing the RSA algorithm, perform an encryption and decryption of:i. Message M=15 using prime numbers p=7 and q=5 ii. Message M=13 using prime numbers p=11 and q=7Using transposition cipher, encrypt the message "hello" and then decrypt it.

