1. The code below prints the numbers from 1 to 50. Rewrite the code using a while loop to accomplish the same thing. *untitled* | File Edit Format Run Options Window Help for i in range (1,51): print (i) Ln: 4 Col: 0
1. The code below prints the numbers from 1 to 50. Rewrite the code using a while loop to accomplish the same thing. *untitled* | File Edit Format Run Options Window Help for i in range (1,51): print (i) Ln: 4 Col: 0
Chapter13: File Input And Output
Section: Chapter Questions
Problem 3PE
Related questions
Question
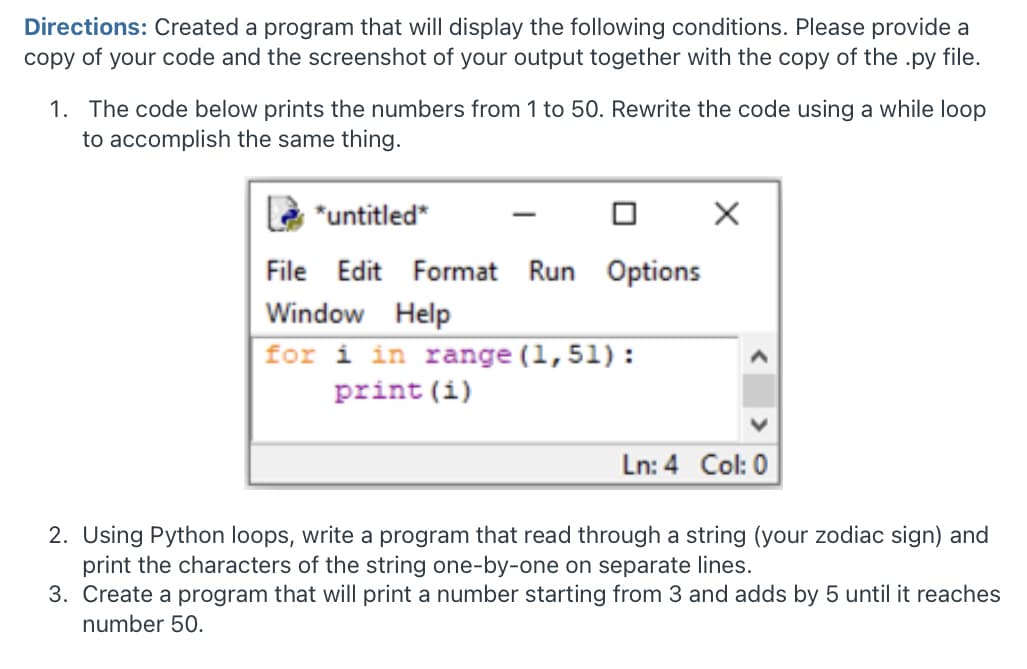
Transcribed Image Text:Directions: Created a program that will display the following conditions. Please provide a
copy of your code and the screenshot of your output together with the copy of the .py file.
1. The code below prints the numbers from 1 to 50. Rewrite the code using a while loop
to accomplish the same thing.
*untitled*
-
File
Edit Format Run Options
Window Help
for i in range (1,51):
print (i)
Ln: 4 Col: 0
2. Using Python loops, write a program that read through a string (your zodiac sign) and
print the characters of the string one-by-one on separate lines.
3. Create a program that will print a number starting from 3 and adds by 5 until it reaches
number 50.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning