1. What is the size (C) of this cache in bytes?
Enhanced Discovering Computers 2017 (Shelly Cashman Series) (MindTap Course List)
1st Edition
ISBN:9781305657458
Author:Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Publisher:Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Chapter6: Computing Components: Processors, Memory, The Cloud, And More
Section: Chapter Questions
Problem 21CT
Related questions
Question
Please Help ASAP!!!!
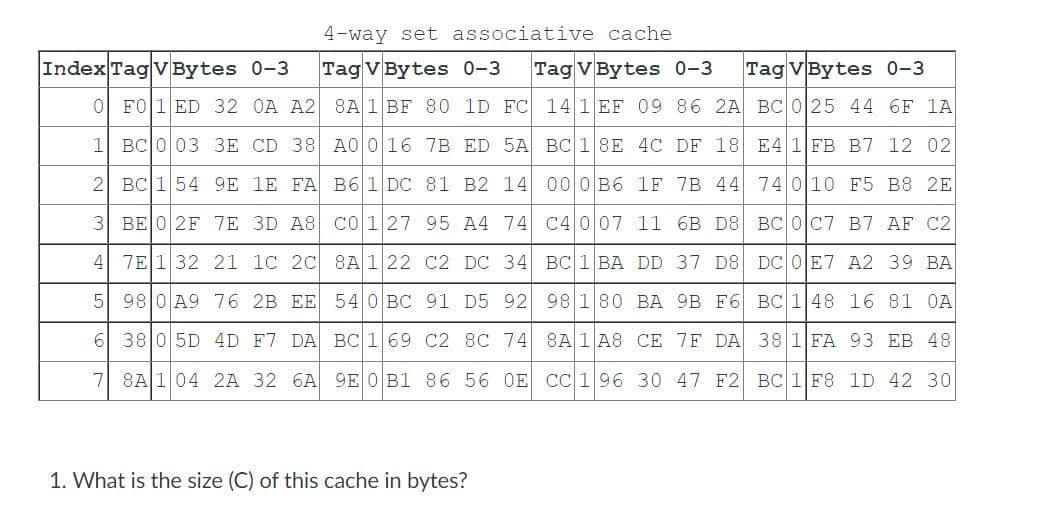
Transcribed Image Text:4-way set associative cache
Tag V Bytes 0-3 Tag V Bytes 0-3 Tag VBytes 0-3
141 EF 09 86 2A BC 0 25 44 6F 1A
8A 1 BF 80 1D FC
7B ED 5A
1
BC 003 3E CD 38 A0 0 16
B7 12 02
BC 1 8E
00 0B6
4C DF 18
1F 7B 44
E4 1 FB
74 0 10
2 BC 1 54 9E 1E FA B6 1 DC
81 B2 14
F5 B8 2E
3
BE 0 2F
7E 3D A8
95 A4 74
C4 007 11 6B D8
BC 0 C7
B7 AF C2
C01 27
8A1 22
4
7E1 32
21 1C 2C
C2 DC 34
BC 1 BA DD 37 D8
DC 0 E7
A2 39 BA
5 98 0 A9
76
2B EE
540 BC 91 D5 92
BC 1 48
16 81 0A
98 180 BA 9B F6
CE 7F DA
6
38 0 5D
4D F7 DA BC 1 69 C2 8C 74
38 1 FA
93 EB 48
8A 1 A8
CC 1 96
7
8A 1 04 2A 32 6A 9E 0 B1 86 56 OE
30 47 F2
BC 1 F8
1D 42 30
Index Tag V Bytes 0-3
0 F01 ED 32 0A A2
1. What is the size (C) of this cache in bytes?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Enhanced Discovering Computers 2017 (Shelly Cashm…
Computer Science
ISBN:
9781305657458
Author:
Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Publisher:
Cengage Learning

Enhanced Discovering Computers 2017 (Shelly Cashm…
Computer Science
ISBN:
9781305657458
Author:
Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Publisher:
Cengage Learning