1. write a C program that will do the following : Ask the user to enter 2 float values Create a function that swap these 2 values • Pass the address of both values in to the function • Return to the main function • Display the new value for each variable make -s (main
Q: What is the definition of lazy evaluation?What exactly are promises? What is the definition of…
A: Introduction: Lazy Assessment: Lazy evaluation, also known as call-by-need in programming language…
Q: TCP is a reliable and full duplex transport layer protocol when it comes to providing services.…
A: Given: The Transmission Control Protocol (TCP) combines the bytes into a packet at the transport…
Q: For E = {a, b}, construct dfa's that accept the sets consisting of (d) all strings with at least one…
A: Below is the answer to above question. I hope tis will be helpful for you...
Q: Science ## Question 4 Calculate the following problem step-by-step. [5 - (6 x 3) + (4 / 2) x 10] +…
A: We need to write code in R language to compute the given expression.
Q: Do you know when an interruption will arrive? What does this have to do with context switching?
A: Introduction: An interrupt happens automatically when a hardware event occurs that is asynchronous…
Q: Disconnecting a computer from the Internet will lead to: i) increase in confidentiality. ii)…
A:
Q: What distinguishes PHP-powered websites from those built using HTML, CSS, and JavaScript?
A: Introduction: PHP(Hypertext preprocessor) is a server-side scripting language i.e. used for web…
Q: When do “zombie” threads finally get cleaned up?
A: Introduction: Zombie thread is nothing but a dead thread, it basically de-allocates the utilized by…
Q: What types of non-text data could you wish to store in a database? What problems can arise when…
A: Let discuss about the non-text data: Non text data can be of multiple types which includes images,…
Q: A. Convert the binary number 1010101101001.1110 to hexadecimal. B. Determine the power set of the…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: Why do we like the event delegation model and its components in GUI programming? Use good examples…
A: The event delegation model defines standard and consistent mechanisms to generate and process…
Q: For what reasons is the internet hailed as one of the pinnacles of ICT? Do particular examples and…
A: Inauguration: It is an important way to communicate, discuss, and even look into information from a…
Q: Do you know when an interruption will arrive? What does this have to do with context switching?
A: Establishment: When a hardware event happens that is asynchronous to the current programme execution…
Q: 1. Given the following array declaration: int A [3 ][2 ]={{13, -23}, {3, 80} ,{91,55} }; declare…
A: I give the code in CPP along with output and code screenshot
Q: Using the state equations and/or state table in the picture. Present a circuit. Use D Flip Flop…
A: Here since we are using D flip flop, the input to D flip flop will be same as next state bits. We…
Q: نقطتان )2( Multiple inheritance is When a class is derived from other two derived classes When a…
A: When a class is derived from two classes
Q: What impact does the data type of a field have on its integrity?
A: The quality and consistency of data are referred to as data integrity. When constructing databases,…
Q: Explain what is meant by the Interaction Design Pattern, then also explain the types!
A: Design patterns are reusable or recurring components which designers use to solve common problems in…
Q: Use the following representation methods to convert the decimal number 30 to an 8-bit binary number:…
A: Given: Decimal number 30 is provided. Requirements:Using the One's complement approach, convert the…
Q: Using awk, how would you print only the first two fields from /etc/passwd? Ubuntu-Linux is a Linux…
A: Linux's awk command: The command is useful for searching for files that have the specified patterns.…
Q: x metadata r
A: The Index metadata association has been standardized. The Index metadata connection does exclude a…
Q: Chap 14. Interfacing to external memory 1. Interface two 16 Kbytes RAM chips (16K x 8) with the…
A: It is defined as one of the basic type of microcontroller, designed by Intel in 1980’s. This…
Q: This is the situation because computers are so powerful. Since when has the use of computers in the…
A: Introduction: Computers are incredibly powerful for a multitude of reasons. They operate at a…
Q: Write and assembly language code to calculate a factorial of n number using a recursion.
A: Answer assembly language code to calculate a factorial of n number using a recursion is in step 2…
Q: Describe basic C input/output functions. Name and describe standard input and output devices.
A: Have been submitted, we will respond to the first one. If you have a particular question that you…
Q: Consider the following proposition: The greatest threat to individual privacy in modern times is…
A: In fact, the following is the solution given:Procedure Number Two (Secondary)Privacy, in its most…
Q: Why do Chrome OS machines use less internal storage than other desktop operating systems?
A: Chrome OS: It is a Linux-based operating system created by Google. It is based on the open-source…
Q: Give four page replacement algorithms a name and a description. Compare and contrast them?
A: Foundation: Though similar in nomenclature to NRU, the least recently used (LRU) page replacement…
Q: computer science Why is calculating the performance of a system in the design phase difficult
A: Answer The system performance is difficult during the design phase because the design is very…
Q: What are the parallels between reinforcement and goal-setting theory?
A: Reinforcement theory is the method of forming behavior by controlling the outgrowths of the…
Q: phishing assaults on your network: how to prevent falling victim to their tricks In order to prevent…
A: phishing: Phishing is a sort of social engineering assault that is often used to obtain sensitive…
Q: Views may be used as data security components, but they also have their constraints.
A: Introduction: It is the process of verifying data to ensure data quality by ensuring that it has…
Q: The information revolution is centered on IT. However, the function and impact of IT might be…
A: Information Revolution: The information revolution is an era of development that may prove to be…
Q: Why is the public-key method of encryption so crucial in internet commerce
A: Public key cryptography remains the most secure protocol because users never need to transmit or…
Q: Should an essay be done on the importance of networking in information technology?
A: Answer: Importance of networking in information technology: In the world of Information Technology…
Q: What are the differences between the two types of integrity constraints?
A: Integrity Constraints: Integrity Constraints are the rules that all data columns in a table must…
Q: Computer science What is network protocol? Explain the following network protocols (in your own…
A: Introduction: A network protocol is a predefined set of rules that govern how data is delivered…
Q: What exactly is an endless recursion?What exactly is a direct recursion? What exactly is an indirect…
A: Introduction: It will continue to make repeated calls until the recurrence reaches the default…
Q: Write down all 16 tests to satisfy Multiple Base Choice coverage (MBCC) for the second…
A: Introduction: Testing is about choosing elements from input domain. The input domain of a program…
Q: An essay about the importance of networking to the development of information technology?
A: Employees to share ideas more easily and work more efficiently: It not only helps you locate new…
Q: What does "infrastructure mode" mean for a wireless network? What mode of operation is the network…
A: In a wireless network, there are two modes of operation: infrastructure mode and other modes of…
Q: The influence of information technology on our everyday lives and society at large. Justify the…
A: Encryption: The most recent revolution is in information and communication technology (ICT).…
Q: What does "infrastructure mode" mean for a wireless network? What mode of operation is the network…
A: In a wireless network, there are two modes of operation: infrastructure mode and other modes of…
Q: Define a function named "Verify" that takes as parameters two arrays of integers A[] and B[] of size…
A: Solution - Programming language used: C All necessary comments are included in program code.…
Q: b. To write a C-program for implementation of different CPU Scheduling Algorithms
A: Priority Scheduling 1. Inside the structure declare the variables. 2. Declare the variable i, j as…
Q: You should keep your software design as simple as possible.
A: Software design must have the following qualities: The design of the software is as simple as…
Q: administr
A: Data system is a term used to allude to an organized assortment of symbols and cycles that may be…
Q: |1 min has 60 sec (nothing new here), write an assembly language code (hint: use loops) to count the…
A: Here our task is to count the number of seconds in 71 minutes using assembly language code. Here It…
Q: In what ways are information systems organised, managed, and technological?
A: Information Systems(IS): A formal, sociotechnical, organisational system intended to gather,…
Q: What does “infrastructure mode” mean for a wireless network? What mode of operation is the network…
A: We need to explain what does “infrastructure mode” mean for a wireless network? What mode of…
in C language
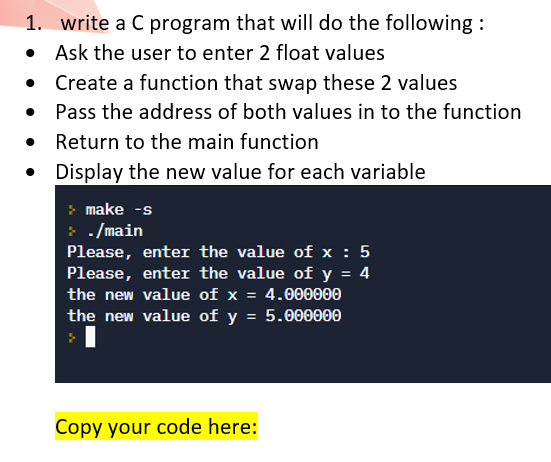
Step by step
Solved in 3 steps with 2 images

- Write a C++ program for the following In this task, your job is to create a function Swapper() that takes three arguments num1,num2, and difference. The first argument should be passed by pointer, second argumentshould be passed by reference, and third argument should be passed by value. YourSwapper function should first swap the values of num1 and num2 with each other, andthen compute the difference of most significant digits of both numbers. You have to storethe difference result in difference variable. In the end, you need to display the values ofall three variables inside your Swapper method as well as in your main function.Note: You are not allowed to create any other variable or pointer inside your Swappermethod.Write a C program to swap two integers you should write a function named as swap_intand it should accept arguments as pointers then it should swap integers bydereferencing those pointers.Write a C++ program for the following Create a function Display() and declare four variables and four pointers of types int,char, double and float in it. You can initialize the variables with any values of yourchoice. After variable initialization, assign addresses of those variables to thecorresponding declared pointers. At the end, you need to print the following values• values stored in all variables• values stored in pointers• addresses of all the variables• addresses of all the pointers• sizes of all the variables• sizes of all the pointers
- Write a C program that includes the following: Has 2 functions: main and swap. swap will receive two integer pointers and swap the integer values using these pointers main will have 2 integers a = 5 and b = 2 main will call swap so that a becomes 2 and b becomes 5 main will display the value of a and b both before and after the swap.When a variable is stored in memory, it is associated with an address. To obtain the address of avariable, the & operator can be used. For example, &a gets the memory address of variable a.Let's try some examples.Write a C program addressOfScalar.c by inserting the code below in the main function. 1 // intialize a char variable, print its address and the next address2 char charvar = 'a';3 printf("address of charvar = %p\n", (void *)(&charvar));4 printf("address of charvar - 1 = %p\n", (void *)(&charvar - 1));5 printf("address of charvar + 1 = %p\n", (void *)(&charvar + 1));67 // intialize an int variable, print its address and the next address8 double doublevar = 1.0;9 printf("address of doublevar = %p\n", (void *)(&doublevar));10 printf("address of doublevar - 1 = %p\n", (void *)(&doublevar - 1));11 printf("address of doublevar + 1 = %p\n", (void *)(&doublevar + 1)); Questions:1) Run the C program, attach a screenshot of the output in the answer…Write a C program that uses a function to calculate Rt. The user will be prompted to enter R1, R2 & R3 which will be passed to the function as parameters, do not use global variables or pointers. The values have no specified range for them but if any of the 3 inputs are less than 0, the function should return 0. The main function should then display the calculated value of Rt with 2 decimal places or an appropriate error message. (Do not use printf or scanf inside the function ... all input/output should be in main) Use appropriate message to prompt the user to enter each value. Three resistors (R1, R2 and R3) are connected so that R1 & R2 are in parallel then in series with R3. Their equivalent resistance (Rt) is calculated using the following equation: Rt=(R1xR2/R1+R2)+R3
- Part 2:Write a C program addressOfArray.c by inserting the code below in the main function. 1) Run the C program, attach a screenshot of the output in the answer sheet. 2) Attach the source code in the answer sheet 3) Then explain why the address after intvar is incremented by 4 bytes instead of 1 byte.Write a C function that is given a pointer to memory, the number of bytes of memory the pointer points at, and two pointers to uint32_t. Your job is to treat the pointer as if it were a pointer to an array of uint32_t, find the min and max values of the array, and write the results to the locations pointed at by the uint32_t pointers. The number of bytes will be a positive multiple of 4. Do not worry about endianess in this problem. Note the tester has command line options -Wall -Wextra -Werror -fsanitize=address to help you catch errors.Write a complete C++ program that asks the user to input two floating-point numbers (i.e., base, perimeter ). There is a function named side that accepts two floating-point numbers as a parameter and returns one value of type float. The function calculates and returns the side of the parallelogram if the base and perimeter are positive otherwise this function will return zero. Then your C++ program will allow the user to input two float values to pass them on the side function. Then the program will display the value return from this function. (Hint: side of the parallelogram is .
- Q) Write a program C++ to exchange the value of x from K to Y then print the address and value before and after exchanging using Pointers to functions? *A programmer implemented a swap function in C as follows: void swap(int x, int y) { int temp; temp = x; x=y; y = temp; } However when he tried to use the swap function in the main function as given below, it didn’t work. int main () { int a=10, b=20; swap(a,b); ... } i. Explain why this function doesn’t work. ii. Suggest a way of fixing it.Write a C++ program that asks your if he wants to store student’s data such as name, id (20i-xxxx) andaddress. Your program should be able to store data for any number of student but, efficiently utilizingthe memory.Your program must have the following function.1) TakingInput: Takes input from user regarding student name, id and address.2) StoringData: Data from TakingInput is then passed to this function where it(data) is stored in adata structure.



