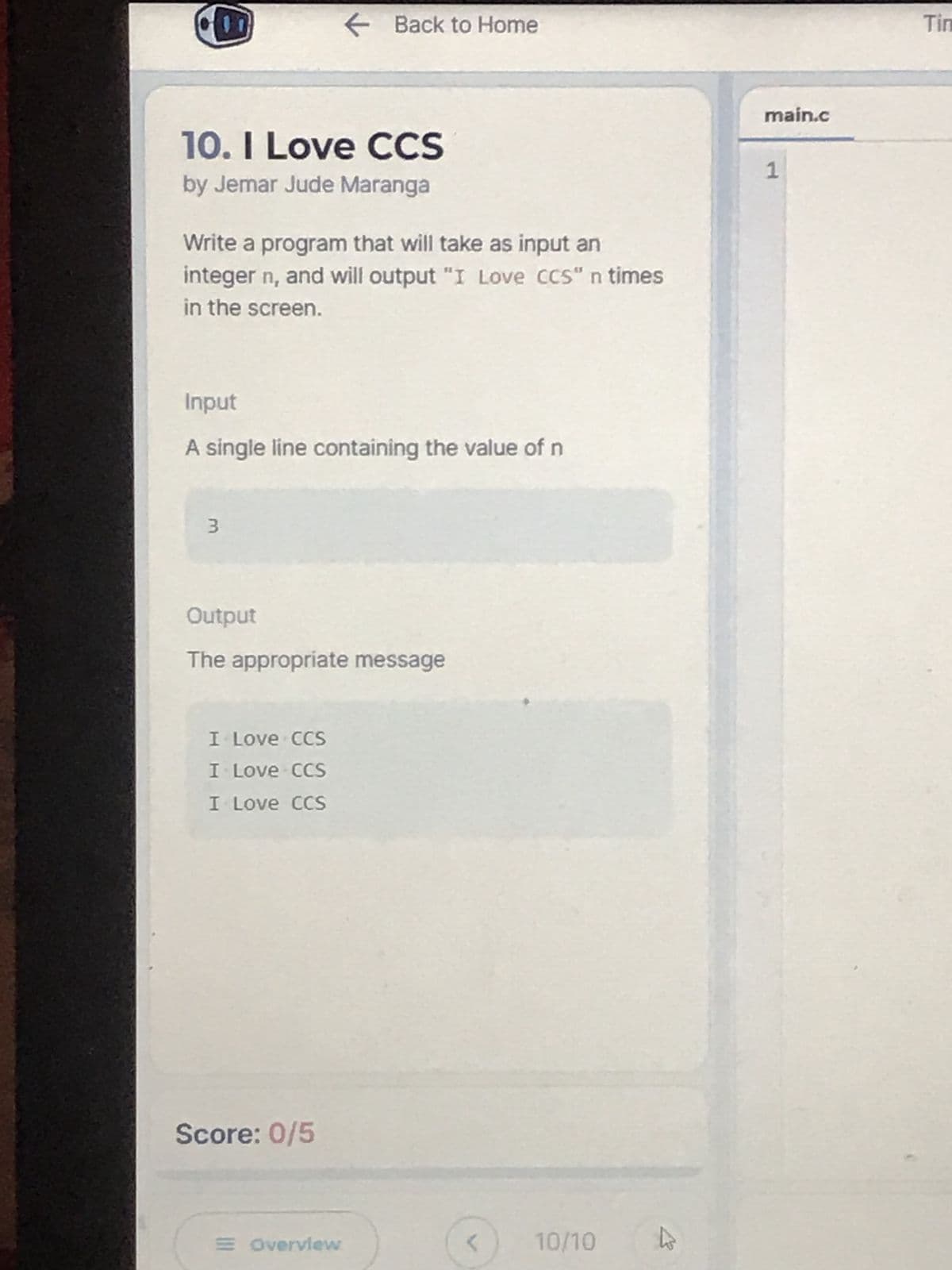
10. I Love CCS by Jemar Jude Maranga Write a program that will take as input an integer n, and will output "I Love CCS" n times in the screen. Input A single line containing the value of n 3 Output The appropriate message I Love CCS I Love CCS I Love CCS
Q: uld you do if the keys were all di
A: 1. How many passes should you do if the keys were all different?
Q: It's important to understand the concept of challenge–response authentication. Compared to a…
A: Inspection: Password-based authentication is standard in client-server databases. It is not safe to…
Q: The following paragraphs will provide an explanation of the Internet Explorer Box Model Bug, as well…
A: Given: A connection-oriented strategy ties the sender to the recipient and examines whether a…
Q: Please provide a description of the method used by the system that enables you to solve all of the…
A: Database : Database technique solves conventional file management system's shortcomings. Eliminating…
Q: tinue to run until the user picks exit. Functionalities: 1. Each playlist and song node is defined…
A: the program is an given below :
Q: In software development, what is the difference between V&V and V&V?They must be distinguished in…
A: Introduction: V&V stands for Verification and Validation in the context of software project…
Q: Use Input to print "< =" and stop the program until the user enters a value and presses the Enter…
A: Question Use Input to print "< =" and stop the program until the user enters a value and…
Q: Matlab code if you knew to include marks as in the following: Write a program that ask about the…
A: I am writing a matlab script on calculating averages of 5 test scores of unknown number of students…
Q: Q2: If you know that the marks should be included as follows: The ratio A 100-90 B 90-80 C 80-60 D…
A: As the programming language is not mentioned here, we are using PYTHON The code and output…
Q: With your new system in mind, talk about password management and the importance of a strong…
A: A Strong Password is characterized as a secret word that is sensibly hard to figure in a brief…
Q: Write a program that works out if a given year is a leap year This is how to workout whether if a…
A: Code: function leapYear_697(year){ return (year % 100 === 0) ? (year % 400 === 0) : (year % 4 ===…
Q: What is the advantage of breaking down your application's code into smaller functions?
A: Introduction: The following are some advantages to dividing the code up into smaller parts:
Q: IT Use of different web browsers for educational purposes besides canvas and what are the advantages…
A:
Q: Provide examples for each of the three basic methods of managing files while you describe each…
A: File system in a the computer system, is the way or the method of naming the files and then to know…
Q: Purpose To assess your ability to: Evaluate yourself as a change agent. Create a plan for…
A: The question has been answered in step2
Q: Examine system access and authentication for information security.
A: Introduction: Access control is a method of information security that, when applied to computers,…
Q: To put it another way, what are you hoping to achieve with the authentication process? Consider the…
A: Start: What are some of the objectives of the authentication process? Investigate both the positives…
Q: Please explain to us the fundamentals of successful data entry fields. There may be occasions…
A: Intro while this may seem obvious, it is necessary to say. Many illustrations deceive the viewer by…
Q: please i need corect answaer 10. Consider the following page reference string: 3, 2, 3, 4, 2, 1,…
A: The number of page fault=7
Q: Draw a dependency diagram to show the partial and transitive dependencies in this data.
A: Partial Dependency : when the attribute in the table depends on only some part of the primary key…
Q: Jobs Arrival Time Burst P1 0.0…
A: Lets understand each of the given algorithms: Shortest remaining time first : it is a pre-emptive…
Q: You have been tasked to create a program named “artistSearchOop”
A: Complete code to search or fetch data from database table using OOPS in PHP. Note: This is how we…
Q: There are substantial differences between software modelling and software development. Explain how…
A: Intro The Methods Used in the Creation of Software: In software engineering, the practice of…
Q: Describe the steps necessary to prepare a brand new computer for usage ?
A: Some steps to be taken after buying a brand new computer. 1) Connect the new computer to the…
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let…
A: The answer is
Q: When it comes to gaining access to files, you have two options: In other words, how do you…
A: Intro Access to the Files: When a file is opened, the contents of the file are read into the memory…
Q: What is not a disadvantage of priority scheduling in operating systems? a) A low priority process…
A: Priority scheduling in Operating system is a mechanism in which tasks are executed based on…
Q: What other browsers have been developed since 1990, outside the ones we currently use, such as…
A: Introduction From 1990 until the present, a plethora of browsers have been produced. There are the…
Q: Describe a hypothetical login management scenario. List as many different ways of authentication as…
A: Scenario Management: Scenario management is an excellent way to manage futures and create customized…
Q: What are the aims of the authentication procedure? Comparing and contrasting the advantages and…
A: Authentication is the most common way of recognizing a singular cycle or element that is endeavoring…
Q: An authentication challenge–response system is a notion that you need to explain. Why is this more…
A: Password-based system: Users may be easily authenticated with simple password authentication. In…
Q: Data backup is the responsibility of both database administrators and server administrators.
A: Intro DBAs are in charge of storing and organizing data via the use of specialized software. Some of…
Q: What is the distinction between a link and an association?
A: The above question is answered in step 2 :-
Q: n this day and age, what role do access limitations play in the grand scheme of things? In your…
A: Access control: Adequate security of information and information systems is a fundamental management…
Q: What role do access restrictions play? Give at least two access control examples.
A: Introduction: The significance of access controls :
Q: Is the Open Systems Interconnection (OSI) security architecture outfitted with cutting-edge…
A: Introduction: The OSI Security Architecture specifies a well-thought-out standard architecture for…
Q: Write a pseudocode that asks for a numeric grade and translates it according to the table below.
A: The complete pseudo-code for the given problem is shown below. Have a look.…
Q: What sets a mobile app apart from others?
A: Introduction: The following characteristics are what set a mobile app apart from other types of…
Q: What makes authentication based on biometrics more secure?
A: Extensive and integral use of Biometrics will help the organisations in keeping their systems and…
Q: Does the internet play a role in the lives of persons with physical or mental disabilities? What new…
A: These days, science has come a long way beyond our wildest dreams. We can now provide people with…
Q: Imagine that you are introducing a new system to college students where they would have to use a…
A: The Answer is
Q: Explain the differences between internal and external fragmentation in memory management in an…
A: The above question is solved in step 2 :-
Q: Walk me through the three most common approaches to managing my files, and show me how they work
A: File system in a the computer system, is the way or the method of naming the files and then to know…
Q: What exactly is the meaning of computer integration?
A: Computer Integration is characterized in designing as the most common way of uniting the part…
Q: Precedence: Highest *, /, not +, -, &, mod - (unary) =₁ /=, =, > and Lowest or, xor Associativity:…
A: Given that, The order of evaluation is shown below. Precedence Highest *, /, not +, -, &,…
Q: What exactly is the function of the canvas element in HTML5?
A: The Answer is in step2
Q: The return address of a function can be displayed via a series of commands. Keep in mind that any…
A: Return address of a function: A return statement in computer programming forces execution to exit…
Q: What exactly are microcomputers sensing?
A: Introduction: The microcomputer is a compact and affordable type of computer that consists of a…
Q: Is there a way to tell the difference between the advantages and disadvantages of various…
A: Multi-factor Authentication (MFA) is a validation strategy that requires the client to give at least…
Q: Differentiate Big Endian and Little Endian Computer Architectures
A: Distinguish between significant endian and little-endian computer architecture.
Step by step
Solved in 3 steps with 1 images

- 3.2.2: Read and format integers. Jump to level 1 First, read in an input value for variable inputCount. Then, read inputCount integers from input and output each integer on a newline followed by the string " entries.". Ex: If the input is 3 35 5 90, the output is: 35 entries. 5 entries. 90 entries. #include <iostream>using namespace std; int main() { int inputCount; int i = 0; for (i = 0; i < 4; ++i) { cin >> inputCount; cout << inputCount << " entries." << endl; } return 0;} Input 3 35 5 90 Your output 3 entries. 35 entries. 5 entries. 90 entries. Expected output 35 entries. 5 entries. 90 entries. clear2: Compare outputkeyboard_arrow_up Output differs. See highlights below. Special character legend Input 1 100 Your output 1entries.100 entries. 100entries.100entries. Expected output 100 entries. clear3: Compare outputkeyboard_arrow_up Output differs. See highlights below.…Review the following program: import urllib.request, urllib.parse, urllib.error fhand = urllib.request.urlopen('http://data.pr4e.org/romeo.txt') counts = dict() for line in fhand: words = line.decode().split() for word in words: counts[word] = counts.get(word, 0) + 1 print(counts) 3.1 Provide an explanation for EACH line of the following program. 3.2 Run the above program and include a full window screenshot with system time and date in the answer. 3.3 Run the above program with https://www.py4e.com/code3/romeo-full.txt and include a full window screenshot with system time and date in the answer.1te a program to t d fp?‘iflt there dlfference
- I need "comments" fo this whole code, for my better understanding. comment for every line. also i want this code to be separated in .cpp and. hpp files. thank you #include <iostream>#include <conio.h>#include <windows.h>#include <dos.h>#include <time.h>#include <graphics.h> #define MAXSNAKESIZE 100#define MAXFRAMEX 119#define MAXFRAMEY 29 using namespace std; HANDLE console = GetStdHandle(STD_OUTPUT_HANDLE);COORD CursorPosition; void gotoxy(int x, int y){CursorPosition.X = x;CursorPosition.Y = y;SetConsoleCursorPosition(console, CursorPosition);}void setcursor(bool visible, DWORD size) // set bool visible = 0 - invisible, bool visible = 1 - visible{if(size == 0){size = 20; // default cursor size Changing to numbers from 1 to 20, decreases cursor width}CONSOLE_CURSOR_INFO lpCursor;lpCursor.bVisible = visible;lpCursor.dwSize = size;SetConsoleCursorInfo(console,&lpCursor);} class Point{private:int x;int y;public:Point(){x = y = 10;}Point(int x,…I've been asking about this poker game that I have been trying to compile in c++ Main.cpp #include <iostream>#include <string>#include <fstream>#include <iomanip>#include <sstream>#include "card.h"#include "deck.h"#include "hand.h"using namespace std;int main(){string repeat = "Y";Deck myDeck;Hand myHand;string exchangeCards;while (repeat == "Y" || repeat == "y"){cout << endl;myHand.newHand(myDeck);myHand.print();cout << endl;cout << "Would you like to exchange any cards? [Y / N]: ";getline(cin, exchangeCards);while (exchangeCards != "Y" && exchangeCards != "y" && exchangeCards != "X" && exchangeCards != "n"){cout << "Please enter Y or N only: ";getline(cin, exchangeCards);}if(exchangeCards == "Y" || exchangeCards == "y"){myHand.exchangeCards(myDeck);}cout << endl;myHand.print();cout << endl;myDeck.reset(); // Resets the deck for a new gamecout << "Play again? [Y / N]: ";getline(cin,…I've been asking about this poker game that I have been trying to compile in c++. Main.cpp #include <iostream>#include <string>#include <fstream>#include <iomanip>#include <sstream>#include "card.h"#include "deck.h"#include "hand.h"using namespace std;int main(){string repeat = "Y";Deck myDeck;Hand myHand;string exchangeCards;while (repeat == "Y" || repeat == "y"){cout << endl;myHand.newHand(myDeck);myHand.print();cout << endl;cout << "Would you like to exchange any cards? [Y / N]: ";getline(cin, exchangeCards);while (exchangeCards != "Y" && exchangeCards != "y" && exchangeCards != "X" && exchangeCards != "n"){cout << "Please enter Y or N only: ";getline(cin, exchangeCards);}if(exchangeCards == "Y" || exchangeCards == "y"){myHand.exchangeCards(myDeck);}cout << endl;myHand.print();cout << endl;myDeck.reset(); // Resets the deck for a new gamecout << "Play again? [Y / N]: ";getline(cin,…
- Question 2: B – Write a program that prompts for an input string of variable length. Once input, your program will do the following: Output the length of the string Output the first and last characters of the string Output the middle character of the string (and its position) Transpose (switch) the two halves; 2nd half starts with the middle character. Print the string out in all upper case characters Example Sessions: Please input a string :>> Firewall Program Output: String length is: 8 First char is: F Last char is: l Middle char at position 4 is: w Transpose: wallFire Upper Case: FIREWALL Please input a string :>> Program Program Output: String length is: 7 First char is: P Last char is: m Middle char at position 3 is: g Transpose: gramPro Upper Case: PROGRAMusing System; class main { publicstaticvoid Main(string[] args) { Random r = new Random(); int randNo= r.Next(1,11); Console.Write("Hi, my name is Stevie. I am thinking of a number from 1 to 10.\nGuess which number I am thinking of? "); int guess = Convert.ToInt32(Console.ReadLine()); do { if(guess<randNo) { Console.WriteLine("Your guess is too low.please enter another number"); guess = Convert.ToInt32(Console.ReadLine()); } if(guess>randNo) { Console.WriteLine("Your guess is too high.please enter another number"); guess = Convert.ToInt32(Console.ReadLine()); } if(guess == randNo) { Console.WriteLine("You guessed correctly!"); } }while(guess!=randNo); } } Hello! This program is in C# and it's a guessing game. The user must choose a number between 1-10 and if the guess is wrong it will say if the guess is too high or too low. How can it be modified to guess a color on the rainbow (ROYGBIV)?In python, create a Coder application that prompts the user for a string and then displays an encoded string.The encoding should add 2 to the Unicode value of each letter to create a new letter. The applicationshould keep all spaces between the words in their original places and the letters x and y shouldbe converted to a and b, respectively. Coder application output should look similar to: Enter a string: hello there Encoded Message: jgnnq vjgtg
- 5. What is this program doing ? pid = fork ( ) ; int pipefd [2 ]; pipe ( pipefd ) ; if ( pid == 0 ) { fclose ( pipefd [1] ; read ( pipefd [0], buf, 10 ); fclose ( pipefd [0 ] ) ; } else { fclose ( pipefd [0] ; write ( pipefd [1], "Hi There", 8 ); fclose ( pipefd [1 ] ) }Given the following local variable declarationsString a = “Enter your Complete Name”;String s = a;String t;What is the value of the following expressions (or ERROR)?1. __________ s.length()2. __________ t.length()3. __________ 1 + a4. __________ a.toUpperCase()5. __________ "Tomorrow".indexOf("r")6. __________ "Tomorrow".lastIndexOf('o')7. __________ "Tomorrow".substring(2,4)8. __________ (a.length() + a).startsWith("a")9. __________ s = = a10. __________ a.substring(1,3).equals("bc") Provide output screenshotsWhat is the output assuming dynamic scoping? #include <iostream> using namespace std; int total = 5; int c = 3; int fun1(int); int fun2(int); int main() { int x = 2; int y = 8; cout << " variables x y and c have values: " << x <<" " << y << " " << c << endl; cout << "main: fun1(x) = " << fun1(x) << endl; cout << " After Call to fun1(x) variables x y and c have values: " << x <<" " << y << " " << c << endl; return 0; } int fun1(int a) { int b = 6; int c = 3; b = total + c + a; cout << "in fun1: b= " << b << endl; cout << "in fun 1 after call to fun2(total) the return value is " << fun2(total) << endl; return (b); } int fun2(int w) { c = c * 2; total = total + w + c; cout << "in fun2: total= " << total << endl; return(c); }

