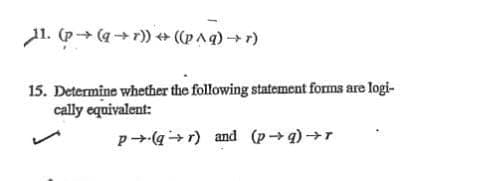
11. (p→ (q→r)) ↔ ((p^q)+r) 15. Determine whether the following statement forms are logi- cally equivalent: p(qr) and (p→q) →r
Q: In this article, the concepts of interrupt latency and context switching time are broken down.
A: Answer: The idea of interrupt latency will be discussed, as well as its relationship to context:…
Q: To further demonstrate the five most common uses of computer-aided system design and modeling,…
A: System Design: System Design encompasses a wide range of design, modelling, and simulation services…
Q: xactly is meant by the phrase "Big Data"? What are the most significant benefits that Big Data has…
A: Answer to the given question: "Big data" is like little data yet bigger. "Big" in big data not…
Q: ctly is system testing? Explain the various so
A: Introduction: Below the describe system testing and various sorts of testing methodologies
Q: What precautions can a company take to protect itself from the threats presented by viruses and…
A: Intro The importance of cyber security cannot be overstated for any firm. Criminals with the…
Q: The processes of software modelling and software development should not be confused with one…
A: The Software Development Methodology: The split of development activities into many phases is known…
Q: What exactly are Sequential Access Files, and how can I put them to good use?
A: Access in a certain order: The data or information in a sequential file is organized in…
Q: What exactly are sequence access files, and how exactly do they perform their functions
A: Please find the answer below :
Q: In your opinion, how important of an impact has the evolution of computers and the many ways they…
A: Intro The development of computers has come a long way from earlier systems such as ENIAC or big,…
Q: What exactly is a batch file
A: Batch File A batch file is a content record that stores orders to be executed in a chronic request.…
Q: Utilizing examples allows for a direct comparison and contrast between unstructured and organized…
A: Given: A business is a kind of economic activity that involves the selling and acquisition of…
Q: The last question I have is this: what exactly is the point of artificial intelligence? Are there…
A: Create the AI goals by writing: In the early days of computing, researchers developed algorithms…
Q: Q3/ Write a Program to compute the area of circle with design.
A: According to the information given:- We have to write a program to compute the area of a circle with…
Q: How many subnets are created by the ?address 192.168.1.0255.255.255.248
A: here in the question ask for multiple choice question,
Q: There should be a list of the five most popular network topologies given. Which one do you consider…
A: In this question we have to explain the network topologies and which one is the most reliable and…
Q: 25 An example of SOP expression is A+B(C+D) A'B+ AC + AB'C (A+B+C)(A + B' + C) All of the answers…
A:
Q: We suggest that Flynn's taxonomy be elevated by one level in order to accommodate our proposal. What…
A: Answer: This question, which relates to Flynn's taxonomy, might perhaps profit from an extra level,…
Q: What is the most important difference between programming in logic and programming in procedures?
A: The following is a breakdown of the procedural and logic programming differences: Declarative logic…
Q: Because of this, it is necessary to deal with each interrupt class in its own unique manner. It is…
A: What are your odds of getting the challenge answer right: Verification of a challenge's response may…
Q: Explain the distinction between the Ethernet and Wi-Fi LAN technologies.
A: Intro Ethernet is primarily a standard communication protocol used to create local area networks.…
Q: * * How many subnets are created by the ?address 192.168.1.0255.255.255.248 16 O .8 • 32 .4 If all…
A: Please refer below for your reference: Number of subnets created is given by: Ip address :…
Q: The question contains 10 multiple choices questions with four choices. ?pick the correct one * is a…
A: This questions belongs to Computer Network. Note that The options of 3rd questions are not showing…
Q: Discuss the most important aspects of the information technology shared service conceptual model,…
A: Encryption: Conceptual models are psychological representations of how tasks should be done.…
Q: Repeater operates in of OSI model ?
A: 1. Switches operates in data link layer of OSI model and uses MAC address to send data packets. 2.…
Q: What exactly are files that are output?
A: Computer file is used for recording the data in a storage device of computer . It is identified by…
Q: A computer is an electrical device that can swiftly and correctly store, retrieve, and analyse both…
A: Introduction: A computer is a piece of electronic equipment that can be used to manage information…
Q: What takes place whenever a catch block is responsible for throwing an Exception?
A: Introduction: The catch block is responsible for throwing an Exception :
Q: What are the four lessons learned from the creation of MINIX, and how do they apply to the…
A: Introduction: In relation to the creation of MINIX, we discovered the following four things:
Q: Describe the distinctions between replication and duplication.
A: The above question is answered in step 2 :-
Q: What information is stored in the table that manages entry-level interrupt vectors?
A: Table of interruptions caused by vectors: An interrupt vector table, also known as an IVT, is a data…
Q: It is critical to offer a detailed explanation of not just why you feel a real-time operating system…
A: Intro Real-time operating system: A real-time operating system (RTOS) is a kind of operating system…
Q: Do you have any suggestions for the topologies of network systems?
A: Network Topology A network topology is the physical and consistent plan of nodes and associations in…
Q: the many ways in which it may be made more secure
A: Answer to the given question: The terms data protection and data security are frequently utilized…
Q: In Python, Create a function that accepts a string as input. The function will take the initial…
A: I have provided PYTHON CODE along with CODE SCREENSHOT and 3 OUTPUT…
Q: How are you able to contribute to the beginning of a new era marked by significant technical…
A: Emerging technologies such as industrial robotics, artificial intelligence, and machine learning are…
Q: There is a clear separation between the code segment, the data segment, and the stack section. The…
A: Launch: A process (a running software) takes up a particular amount of memory. It may be used to…
Q: What role does logic play in the process of creating software for computers? What types of…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Logic…
Q: It looks as if this section need to provide a concise explanation of the two components wwwww of the…
A: operating system: An operating system is a software programmed that manages and operates a broad…
Q: What are the fundamental components of an Android mobile application ?
A: Introduction: Android applications (apps) are a type of software that may either be installed on a…
Q: Authentication is put to use for a wide range of reasons; what are some of the more typical…
A: Authentication: Servers will employ authentication to identify who is accessing their data or…
Q: What kind of connection exists between reporting on the internet and the educational pursuits of…
A: Intro Proposal: A proposal is a written record to satisfy the reader for a proposed plan of action.…
Q: With respect to the following nested loops, what is missing or wrong? int loopCount; while…
A: The loops are a programming construct that are utilized to run a bunch of code a number of times…
Q: What are the advantages of employing a document store as opposed to a relational database, and why…
A: Given: When we talk about databases that are relational, we are referring to tabular representations…
Q: What is the status of the auxiliary carry flag after executing the instruction ADD AX, BX? (write 1…
A: ADD AX,BX will add values in AX,BX. If Carry is their then Auxiliary Carry Flag (It is one of the…
Q: How can one get application software in the most efficient manner? In your answer, you should…
A: The above question is solved in step 2 :-
Q: What precisely does the term "encapsulation" mean when it comes to object-oriented techniques?
A: Intro Object-oriented programming is a paradigm for computer programming that is based on the…
Q: It looks as if this section need to provide a concise explanation of the two components of the…
A: The above question is solved in step 2 :-
Q: How many distinct types of computer software are there from which to choose?
A: There are basically Two types of computer software present 1) System software 2) Application…
Q: First, you should define and describe the components of the core of the operating system that are…
A: The question has been answered in step2
Q: Professional in information system security (CISSP) (150 Words) Professional security tester (OPST)…
A: Intro CISSP:- CISSP is an information security certificate created by the International Information…
Step by step
Solved in 2 steps with 2 images

- dict1 = {(1,1,1):"red", (2,1,-1):"green", (0,-1,1):"red", (0,0,-2):"blue"}In this case, there are 2 red points, and their centroid is at ( (1+0)/2, (1-1)/2, (1+1)/2 ) = (0.5, 0, 1)Considering that in this example there is only one green and one blue point, they are representing the respective color's centroid. Hence, your function should return the following dictionary:{"red":(0.5,0.0,1.0), "green":(2.0,1.0,-1.0), "blue":(0.0,0.0,-2.0)}Let A ={1, 2, 3, ... , 10}, B = {2, 3, 6, 8}, and C = {3, 5, 4, 8, 2} Write the Venn diagram representation of the following sets. How many elements are there in A U B U C.T=4, n=12 and A=(3,5,8,8,9,16,29,41,50,63,64,67). Draw the corresponding walkthrough as shown in P.146.
- F(w, x, y, z) = ∑(1, 3, 4, 5, 10, 11, 12, 13, 14, 15) List of prime implicantQ5) Let Σ = {0, 1}. Convert the following NFA's to DFA's:4. Let Σ = {0, 1} be an alphabet and let L ⊆ {0, 1} ∗ be the language defined as L = {w ∈ {0, 1} ∗ |w = x10y, x, y ∈ {0, 1}∗}. (a) Determine whether 01 ∈ L.(b) Determine whether 0101 ∈ L.
- Given A={1,2,3,4,5,6}, B={4,5,6,7,8,9}. Compute (c)A−B=Define upper bound. If f(n) = 3n * 5 for what values of C and n this function is said to be upper bounded.Graph Neural Network: Consider the un-directed graph shown in the Fig. The values inside the node refer to the feature value of the node. The order of the nodes is A,B,C,D when following the matrix form in below questions.(You can use python or other languages to find the eigen values and other operation for this question): 1.Consider the values in the circle to be the values of the input feature of the data point. Find the spectral representation of the data point.2.Let W = 2, B = 1 and a ReLU activation function f(x) = max(0,x) as explained in question 1. Find one step updated features h(1)v for all nodes using the Graph Convolution Network (GCN) algorithm
- Please do question d and e. It follows from a, b and cAssume the following scoring matrix. A T C G - A 1 -1 -1 -2 -1 T 1 -1 -1 -1 C 2 -1 -1 G 1 -1 Fill out the dynamic programming table for the global alignment between sequences v = TAGCTCCG and w = GCATCCA using the scoring matrix above. Use the following recursive scoring formula. w= G C A T C C A 0 1 2 3 4 5 6 7 v= 0 T 1 A 2 G 3 C 4 T 5 C 6 C 7 G 8 What is the score and global alignment between v and w?1. Simplify the following expression using K-Map for a and write the simplified equation. I need help understanding this question. Can you please show steps clearly? I will rate! Please answer the question and don't copy paste another solution. Thank you very much!

