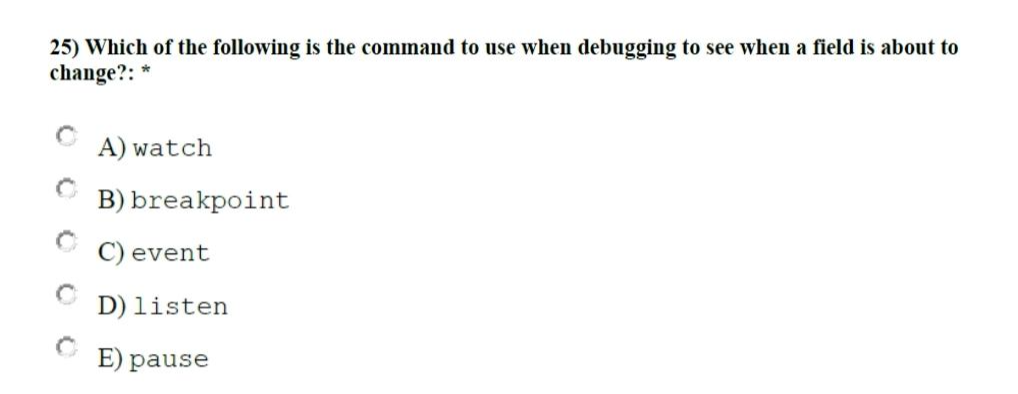
25) Which of the following is the command to use when debugging to see when a field is about to change?: * A) watch B) breakpoint event D) listen E) pause
Q: Give an explanation of all seven OSI model layers, their seven sublayers, and the protocols that are…
A: OSI: Discuss the OSI layer and its seven levels and protocols. The OSI Model describes a networking…
Q: What effect do interrupt management strategies have on the speed of the machine?
A: Comparatively speaking, external devices are slower than a CPU. Therefore, without an interrupt, the…
Q: What characteristics do Agile frameworks all share? then press Send. a certain number of repetitions…
A: Agile Frameworks: High levels of communication and cooperation, quick and effective reactions to…
Q: List the benefits and drawbacks of using each of the three primary kinds of networks.
A: Introduction: In a computer network, two or more computers may communicate with one another and…
Q: How much do you know about CASE software?
A: CASE software is discussed below
Q: uickly I need.
A: We are going to design a logic circuit which will produce output F=1 when a valid BCD number is…
Q: quickly describe the variations between active and passive transformations?
A: Both passive and active transformations are possible.The number of rows are processed by an active…
Q: What distinguishes the Internet from the World Wide Web the most?
A: The Internet is a network of many computers that are connected around the globe. WWW stands for…
Q: Give examples of contemporary cloud computing applications and how they have benefited society as a…
A: What is Cloud Computing? Cloud computing refers to the delivery of on-demand computing…
Q: When shifting your IT operations to the cloud, where should you look for governance issues?
A: Using the infrastructure as a service (Ia As) deployment model, the charity's administration…
Q: Suppose you are contacted by a software developer to create a hospital patient management system.…
A: software specifications requirements (SRS) A program system requirements specification (PSRS), often…
Q: Can the terms "Internet" and "World Wide Web" be distinguished from one another?
A: Internet: Multiple computer networks are connected at once via the internet. Since the internet is…
Q: When shifting your IT operations to the cloud, where should you look for governance issues?
A: According to the information given:- We have to describe when shifting your IT operations to the…
Q: What measures are used to assess software maintenance?
A: Introduction Software Maintenance: After a software product has been delivered to the customer, it…
Q: most popular programmes used by hosts of software firewalls
A: In computing, a protected network such as a defense is a system of security that protects people…
Q: The word used to describe the display that is often used in desktop computers is cathode ray tube,…
A: Due to this: Cathode-ray tubes, a prevalent kind of display in desktop computers, are the subject of…
Q: What distinguishes the Internet from the World Wide Web the most?
A: Internet is used to connect the different network of the computer. Internet is majorly hardware.…
Q: What should one keep in mind while switching from one system to another? Why don't you go into more…
A: Keep the following in mind a while switching between several systems: It is impossible to…
Q: What advantages and drawbacks do REA and commercial systems have?
A: The term "resources, events, and agents" - (REA) refers to a concept that can be used to…
Q: Where can you find malware? What makes worms distinct from viruses? By breathing in contaminated…
A: Given: Describe pathogens. Pathogens are organisms that infect the body and can harm health. They…
Q: The logical levels of a distributed client-server programme are what
A: Given: A well-known software application design called "three-tier architecture" divides programmes…
Q: Any typical DSS consists of three main components, namely database, software system and user…
A: We have to describe various mathematical and statistical models utilised by the software component…
Q: The following criteria, given in descending order of importance, impact a hash table's Big-O…
A: The crucial factors that affect a hash table's Big-O performance are illustrated below: How to…
Q: To distinguish between scalar and superscale CPUs, utilise examples. The length of time required to…
A: Introduction: One item of data is processed by a scalar processor simultaneously, A vector processor…
Q: why single linked list and doubly linked list is confusing in c++
A: In this question we need to explain why in C++ singly linked list and doubly linked list is hard to…
Q: Which of the following ports provide power to the Raspberry Pi? Is it an HDMI port, a Micro USB…
A: A raspberry pi has many ports in it for various functions.
Q: Write a program java that reads a number of feet from the user, then prints out either the same…
A: Explanation Scanner class is used for input long miles = totalFeet/5280; long foot =…
Q: Do several varieties of malware exist? Is there a difference between worms and viruses? The primary…
A: The answer to the question is given below:
Q: company has been in business for 40 years. It has tens of thousands of customer addresses in three…
A: We need to find the correct option regarding organizing and securing the information.
Q: Given that all the data were thrown into one bucket, our hash map wasn't created very properly (that…
A: Introduction: Hash tables are collections of sorted things that make it possible to find them fast…
Q: What separates network architecture from application architecture?
A: Given: The communication process may be divided into levels in network organisations thanks to…
Q: How does MVC benefit their company in terms of web applications? What benefits may MVC architecture…
A: MVC is known for Model, View and Controller.
Q: Identify for each table, the followings: Foreign keys Candidate keys Primary key Alternate keys
A: The question has been answered in step2
Q: How safe is Lamport's OLP given the relevance of the hash function's properties?
A: In this question we need to explain how secure is the Lamport's OLP (one time login password) with…
Q: Explain why Windows reports 8 GB of memory even though the one SO-DIMM contains 4 GB of memory.
A: Windows reports 8 GB of memory because the laptop has a dual-channel memory configuration, meaning…
Q: do live backups of physical hard drives may have an influence on how much storage space is really…
A: the solution is an given below :
Q: - For the given IP address 128.168.0.1/20, calculate the Subnet mask, Network address, total number…
A: The question has been answered in step2
Q: How much do you know about CASE software?
A: Introduction: Software of the highest caliber and without errors is ensured using CASE. Designers,…
Q: Q5/ Write simple C++ program that create struct to read an informations of 20 Students (Name, 7…
A: C++ Programming is the object oriented programming languages that are used to create the web…
Q: It is required to explain the implementation of finite-state machine control.
A: A finite automaton (FA, plural: Sass) is a kind of finite-state machine (FEM): An automaton (plural:…
Q: What distinguishes structural from data independence?
A: When modifications to the file structure may be made without affecting the appliance program's…
Q: A universal register, a single accumulator, or a stack are the three different central processing…
A: The component of the computer that gets and executes instructions is called the central processing…
Q: Which firewall construction style has emerged as the de facto norm for companies operating in the…
A: Introduction: Below is a list of 15 various business functions, whether they are a company's or a…
Q: Write a triangle (x0, y0, x1, y1, x2, y2) function to draw the triangle with vertices (x0, y0), (x1,…
A: Here is the python code: See below step for code
Q: Give an explanation of all seven OSI model layers, their seven sublayers, and the protocols that are…
A: GIVEN: Discuss the OSI layer and describe the purposes of the seven different levels, as well as…
Q: Figure 3 shows a LAN topology Assume that no port security implemented on both switches. The…
A: According to the information given:- We have to elaborate the mentioned LAN Topology scenario in…
Q: What advantages and drawbacks do REA and commercial systems have?
A: REA stands for resources, events and agents. This could help us in building AIS databases. This…
Q: What many technological approaches are used in the process of identifying network intrusions?
A: Introduction: Any illegal or unauthorised activity on a computer is considered an intrusion.
Q: e data are simple to fake, how can people disti
A: Introduction: Manipulated videos, audio, and images have been around for a long time, but the rise…
Step by step
Solved in 3 steps

- How do you get to a file's Properties box to alter a file attribute?Write a statement that reads the entire file associated with the inFile variable and assigns the file’s contents to the txtDocument control.3. Above For this exercise, assume that the user will correctly enter ID numbers and zip codes, but force each customer name to six characters, padding it with spaces or truncating it if it is too long or too short. Issue an error message, and do not save the records if the user tries to save a record with an ID number that already has been used. Write a program named CreateItemFile.java that creates a file of items carried by the company. Include a three-digit item number and up to a 20-character description for each item. Issue an error message if the user tries to store an item number that already has been used. Accept user input until 999 is input for the item number. Enter customer ID number or 999 to quit >> 1 Enter item number >> 7 Customer: 1 Name: Joe zip code: 88888 ordered Item #7 which is a Cake/Brownies Enter customer ID number or 999 to quit >> 8 Enter item number >> 2 Customer: 8 Name: Jill zip code: 11111 ordered Item #2 which is a Cookies…
- Fill in the blank question- Only answer needed without explanation Q. Open() command can be used to ___________ and open a file.Use Notepad++ to create a js file 1. Create variables to store adventurer names, number of adventurers killed, number of survivors and the leader name. 2. The survivors is equal to the number of adventurers - number killed 3. Display "Welcome to The God Among Us" 4. Display the introduction as: A group of adventurers began their search for the mystical god said to live among us. In charge of the squad was < display leader name here> who was famous for his past exploits. Along the way, the group of comrades were attacked by the god's loyal followers. The adventurers fought with bravado and strength under the tutelage of <display leader name here> the followers were defeated but they still suffered great losses. After a headcount of the remaining squad, <display number killed> were found to be dead which left only <display number of survivors> remaining survivors. -insert the variable values in the story as shown above by the text in between <>'s. 5.…Fill in the blank question- Only answer needed without explanation Q. _____________ command is used to create and open a file.
- Create ASM statements that, when the left mouse button is pressed, cause the cursor to jump to label Button1.MATCH OUTPUT AS IT IS . FOLLOW QUESTION ----------------------------------------- Dr. Varun needs an application for his clinic to maintain all the appointments for the day. The application should make appointments on the basis of first come first serve basis. And it should also perform the following functions: insert new appointment, delete an appointment, display all the appointments, show next appointment, check if there is no appointment or number of appointments are full for a day. Use class templates to perform the above-mentioned operations. Write a C++ program to perform the Queue operation. Note:Use the following class template for Queue creation. template <class T>class Queue{ private: int front,rear; T *queue; int maxsize;}; Define the following function in the class Queue class Method name Description int isFull() The method is used to check whether the queue is full or not. void insert(T) The method is used to display the rear…Which of the following INT 33h functions shows and hides the mouse pointer?

