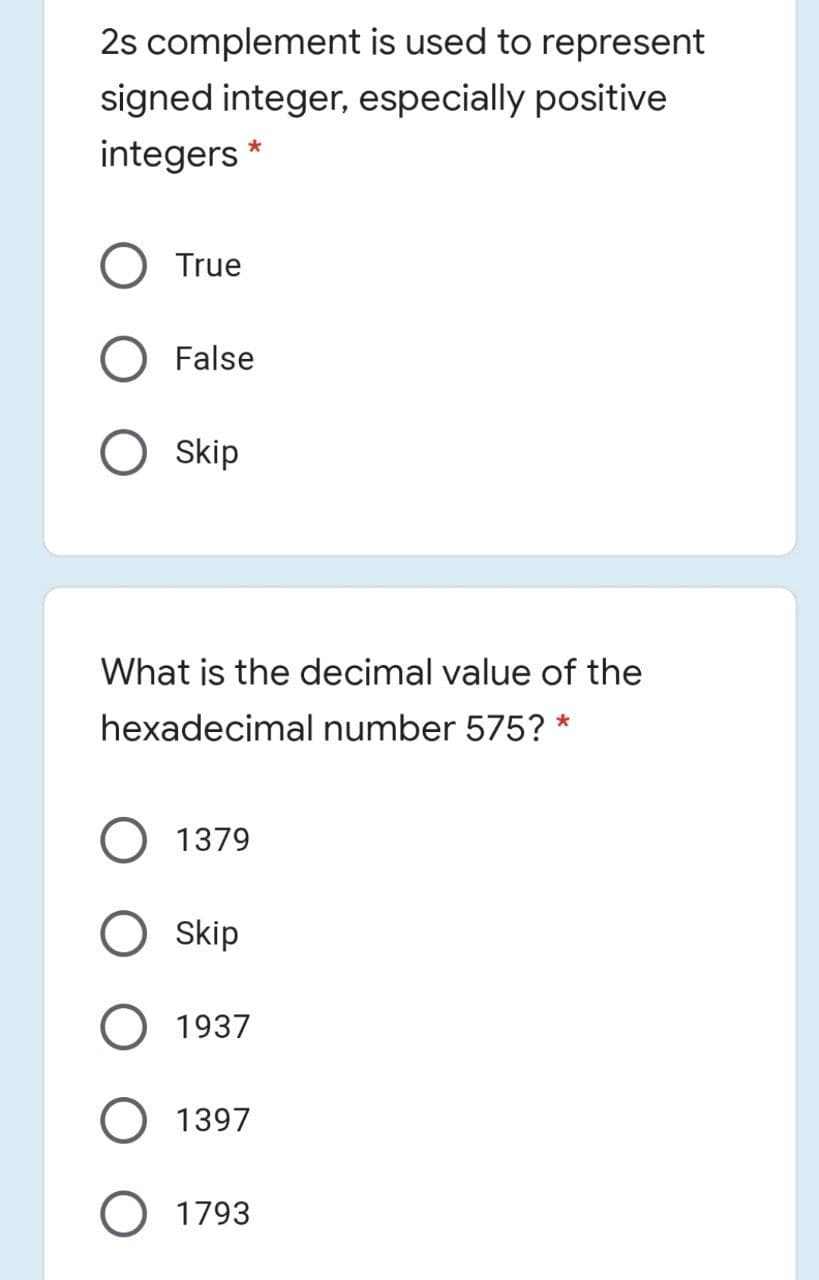
2s complement is used to represent signed integer, especially positive integers * True False O skip What is the decimal value of the hexadecimal number 575? * 1379 Skip 1937 1397 O 1793
Q: Integrity controls are used to secure databases in what ways?
A: Introduction: This question discusses the integrity measures that are used to safeguard databases. B...
Q: can you please show me how exactly i should change the code in order for it to run?
A: Here in the function wordtomorse(), we have a set named Mcode. Next, we have iterated over the strin...
Q: Describe the dilemma of the dining philosophers and how it relates to operating systems.
A: Dining Philosophers Problem Overview Five philosophers are seated at a circular table with a plate ...
Q: Facilitator (FacilitatorID, LastName, FirstName, Street, City, ZipCode) Forum (ForumNum, ForumDate,...
A: Here the attribute customerNum of relation Forum corresponds to primary key FacilitatorID of relatio...
Q: Explain the three types of data mining analysis and how Intel may utilise them to get BI.
A: Each of the following data mining techniques serves several different business problems and provides...
Q: When it comes to presenting data to humans or other devices, what element of the computer is respons...
A: Introduction : Make a list of the data to be gathered and its format, as well as the study's goals. ...
Q: Define and implement the following functions using a C project structure: int sum(int x, int ...
A: The C project code for the above problem is attached below: main.c file functions.h file function...
Q: The three stages of data modeling should be differentiated from one another.
A: There are three stages of data modelling. The stages are :- Conceptual stage Logical stage and Phy...
Q: What are some of the main reasons he gives for having a robust cyber defence?
A: Introduction: Defending your device, software, and network from cyberattacks or threats is what cybe...
Q: 1. Numbers, Codes, Logic, Circuits a) Convert 101001012 to decimal. b) Convert -6310 to binary using...
A: Convert 57 decimal to binary Convery 66 decimal to hexadecimal Convert AC9 hexadecimal to decimal A...
Q: Which of the following two tools may a software developer or system administrator use to register an...
A: Introduction: Which of the following two tools may a software developer or system administrator use ...
Q: Question :) With practical examples, discuss the difference(s) between a Web Server software and a W...
A: answer is
Q: Execute the following commands in the order listed below and obtain a (single) screenshot showing th...
A: Display the current date using the ‘date’ command (press Enter at the prompt to keep the same date) ...
Q: Assume x goes to $s0, y goes to $s1, and the address of the first element in the array A goes to $s2...
A: y = A[2]; The equivalent MIPS code is
Q: Find regular expressions that define the following languages: 1. XML opening and closing tags where ...
A: Answer: This question based on regular expression and find regex
Q: Create a java program that puts numbers as argument in the command prompt and display total positive...
A: Given: To write a Java program that puts numbers as argument in the command prompt and display total...
Q: In this chapter's case study, JWD Consulting used the predictive approach to build their intranet si...
A: Agile methodology is a recurring method of software development. Each repetition of a quick course t...
Q: The prefix of 3 is the first 3 characters of a String. Given a String input, output the first three ...
A: use the method substring as String.substring(int startindex,int lastindex) here start index= 0 last ...
Q: The approximate word is when the value on the left of th word is equal to the total value on the rig...
A: Algorithm - Create a function with argument a string. define the two variable with sum of left ...
Q: Print Person Information from file In this lab you are asked to complete the function : print_person...
A: ########################## Complete this function#########################def print_person_from_file...
Q: Computer science . Describe AWS Lambda in detail.
A: Introduction: A lambda is essentially a code block that may be supplied as an argument to a function...
Q: is an open source Python library that provides visualization tools. You can use the library to build...
A: Answer:
Q: Explain the role of the Turing test in the development and advancement of AI robots
A: Introduction: Turing test's role in the creation and improvement of robots in the AI domain:
Q: 15. Filename: password dls369.cpp, but replace my email id with yours. (a) Write a function which re...
A: I give the code in C++ along with output and code screenshot
Q: What steps should we take to extend the life of a dot matrix printer?
A: A printer that creates graphics from dots using hammers and a ribbon. These machines, which are used...
Q: Describe the three primary forms of testing and the sequence in which they are carried out.
A: Introduction: There are three types of testing: In every system, testing is done to see if the produ...
Q: In BCD Addition, if and only a 4-bit sum is greater than 9, it is an invalid result. *
A: True In 4-bit binary addition it is invalid if sum is greater than 9.
Q: Write the prototype and definition of a new non-member function int size(…..) to the class Stack bas...
A: Write the prototype and definition of a new non-member function int size(…..) to the class Stack bas...
Q: computer science -What Are the Advantages of Data Cleaning?
A: Introduction: Data Cleansing: The practise of repairing or deleting inaccurate, corrupted, improperl...
Q: Use a for loop to print all characters at odd index * positions of a string, one per line. * You sho...
A:
Q: Consider the WAN, or wide-area network, as your preferred means of wireless connectivity. What disti...
A: Intro It can be tough to defend your home wireless network from infiltration if your wifi connection...
Q: Your goal is to create a Contact Book program that enables users to: 1. Create New Contact • This al...
A: Given :- Our job is to create a smartphone directory that accumulates user contact information until...
Q: Topic: Array Write a C++ program to store and process an integer array. The program creates an ar...
A: Your C++ program is given below as you required with an output.
Q: . Java is known to be an object oriented program. Objects are also known to exist in real life. You ...
A: A real-world entity such as a pen, chair, table, computer, watch, and so on is referred to as an obj...
Q: Describe two applications that might be better suited to assembly language than than a high-level la...
A: Applications that suited to assembly language:
Q: Read the following case study, which describes the data requirements for a motorcycle rental company...
A: Solution :: Let's see the above question you have posted above I have ER diagram and some entities a...
Q: ( as) Write a Java method named displayTree. The main method will pass it the Tree created above and...
A: postOrder: import java.util.Stack; public class BinaryTreePostOrder { public static class ...
Q: What are the advantages of utilising containers to replace virtual machines?
A: Intro Virtual machine (also known as a virtual machine): A Virtual Machine (VM) is a registered ass...
Q: Consider the grammar below: S → aSb|bSa|SS|A For the string ab, how many leftmost derivations with 4...
A: Here, we are going to find out number of leftmost derivations with 4 or fewer steps for string ab.
Q: For what reasons has virtual private network (VPN) technology become the most popular technique of c...
A: Definition - A VPN is a service that creates an online safe connection that is encrypted and helps t...
Q: What are some of the advantages of data profiling?
A: Introduction: Data profiling enhances data quality, shortens the time it takes to perform large proj...
Q: Computer science Explain why end-to-end testing is required and what the purpose of doing so is.
A: Introduction: The process of creating objective assessments of how well a system (device) meets, exc...
Q: 2.In the 'Table Area' below, create a table with three headings with the following order: Year, Tota...
A: MS excel is a worksheet that is used to store and analyze numerical data. It has functions that make...
Q: Structural Induction: Prove that a nonempty binary tree t of height h(t) has at most 2t)+1 1 nodes.
A: We are going to prove binary tree of height h(t) has at most 2h(t)+1 -1 nodes. Please refer to the i...
Q: Write a program that uses a switch statement as follows: If game contains the letter p , or P the fu...
A: C++ Program: #include <iostream>using namespace std; // Function print the words Play Station ...
Q: s the concept of registry manage
A: Sorry for that as per the bartleby guidelines we can solve only one question for you if you want to ...
Q: The following strcopy.function uses the C++ traditional pointer-based array declaration for its para...
A: source code #include<iostream> using namespace std; void strcopy(char dest[], const char src...
Q: a) Encrypt the plaintext "blotto" using CT R mode. Please enter your answer in hex. (Please do *not*...
A: We have to encrypt the given following plaintexts into the equivalent hexadecimal format using diffe...
Q: Assume the CPU has access to two types of memory. Level 1 has 1000 data words and has an access time...
A: Intro Assume the CPU has access to two types of memory. Level 1 has 1000 data words and has an acces...
Q: Suppose you have a RISC machine with a 2.7 GHz clock (i.e., the clock ticks 2.7 billion times per se...
A: Below is the correct answer to above question. I hope this will helpful for you.....
Step by step
Solved in 2 steps

- 7) Under computer integer arithmetic, the quotient J/K of two integers J and K is less than or equal to the usual quotient. True or false?A number in base 2 (binary) is a number such that each of its digits is 0 or 1. To convert frombinary to decimal (base 10), the digits starting from the right are multiplied by powers of 2(starting at 0) and added. For example, the value in decimal of 10011 is calculated as follows:& progoam €8 [eheck Whother an integer ent Armstrong number of RGE.
- Convert the following numbers into base ten. (a) 32five (b) 22six (c) 410five (d) 3203five (e) 202five (f) 1222six (g) 202four (h) 404seven (i) 1000two (j) 11011two (k) 88sixteen (l) 707sixteen ?a. f1(n) is Ω(f6(n)) b. f5(n) is Q(f3(n)) c. f1(n) is O(f3(n)) d. f5(n) is O(f1(n)) e. f6(n) is Ω(f4(n))Evaluate the following Postfix: "4 9 + 8 * 1 - 6 6 + - 13 - 2 /" (All the numbers are in single digit. Everything is separated with a space)* 50.0 49.5 39.5 39 38 76
- ISBN-13 is a new standard for identifying books. It uses13 digits d1d2d3d4d5d6d7d8d9d10d11d12d13. The last digit d13 is a checksum, which iscalculated from the other digits using the following formula: 10 - (d1 + 3d2 + d3 + 3d4 + d5 + 3d6 + d7 + 3d8 + d9 + 3d10 + d11 + 3d12)%10If the checksum is 10, replace it with 0. Your program should read the input as astring. Here are sample runs: Enter the first 12 digits of an ISBN-13 as a string: 978013213080 ↵EnterThe ISBN-13 number is 9780132130806Binary numbers need more places for counting because: A. 0's and 1's can be added in front of them B. 0's and 1's have to be properly placed C. They are always big numbers D. Binary base is small E. None of the aboveA)The decimal number 162 what is the binary representation of it ? B)the decimal number of -53 what is the binary representation of it ?
- TAKE THE 2 LAST DIGITS OF YOUR STUDENT NUMBER. BY CONSIDERING IT AS A DECIMAL NUMBER, CONVERT ITINTO BINARY NUMBER. MY student number : 202010022The following is an addition problem in binary notation. Each letter represents a unique binary digit. Which letter represents 1 and which represents 0? Design an algorithm for solving problems like this. YXX+ XYX=XYYY(xiii) Determine all the permutations of the numbers less than or equal to some given number n. For example, if n = 123, then the permutations are: 123 321 231 132 213 312 (xiv) Find a series of five consecutive numbers, the sum of the squares of the first three of which is equal to the sum of the squares of the last two. For example, (– 2)2+ (– 1)2+ 02= 12+ 22 (xv) Limit the checking within 1000, to show all the triad numbers within 10,000. A number is said to be a triad number if the double and triple of the number contain all separate digits with no repetition of any one of them. (xvi) Identify and show the integer values of x, y, and z that satisfy the equation: Z²= X²+ y²

