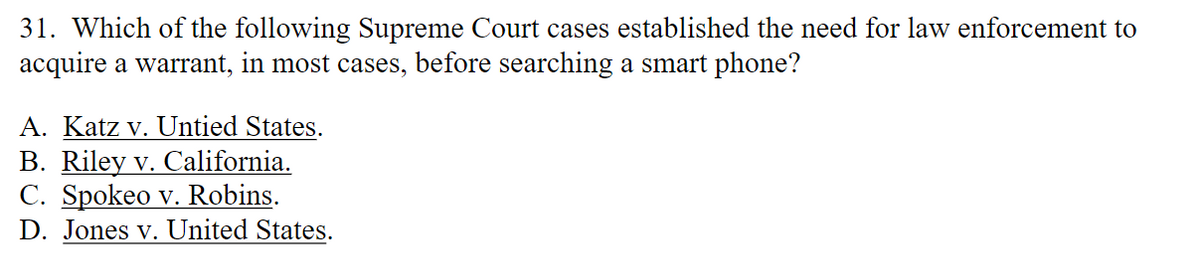
31. Which of the following Supreme Court cases established the need for law enforcement to acquire a warrant, in most cases, before searching a smart phone? A. Katz v. Untied States. B. Riley v. California. C. Spokeo v. Robins. D. Jones v. United States.
Q: Carry out a quick risk management analysis on your laptop. Determine what you have, what you need to…
A: In the age of the digital era, most of our daily activities are done through computers and laptops.…
Q: -lated to consumer privacy? . Federal Communication Commission ("FCC"). . Federal Trade Commission…
A: Answer is explained below in detail
Q: .Which federal agency formally manages the United States' cybersecurity policies?
A: Here is your solution -
Q: 43. Has a reportable violation of the Health Insurance Portability and Accountability Act occurred?…
A: The question presents a scenario involving characters from the television show "The X-Files" and a…
Q: 57. Which of the following statutes does NOT provide for a private right of action whatsoever? A.…
A: There is no private right of action under HIPAA. The Office for Civil Rights of the Department of…
Q: 60. The European Union takes which approach to privacy protection? A. Comprehensive B. Sectoral C.…
A: In this question we need to choose the correct option related to European Union (EU) privacy…
Q: USE MY SQL List all the data in your table movie_prod, sorted by the id of the movie (smallest…
A: MySQL is based on the SQL programming language and allows developers to store, organize, and…
Q: 37. Which of the following is not an example of an administrative safeguard? A. Trainings for staff…
A: Here is your solution -
Q: 1. The Children's Online Privacy Protection Act ("COPPA") was enacted to primarily prevent which of…
A: In this question we need to choose the main purpose of Children's Online Privacy Protection Act…
Q: On this link: https://nca.gov.sa/legislation?item=182&slug=guidelines-list you can find different…
A: According to the information given:- We have to define Cloud Cybersecurity Controls Policy. Based…
Q: 0. In the healthcare sector, cybersecurity through IoT devices like wireless insulin pumps hich…
A: Correct mcq answer is explained below Please note explaination for incorrect answers is also given
Q: Denial of service attacks may harm traditional email. Will you use this information to defend…
A: Denial of Service (DoS) attacks includes an attacker flooding a targeted system or network with…
Q: a) Our task is to find the approximate frame error rate (FER) for FEC in percentage Answer: b)…
A: The error handling overhead in communication links can include: Error correction codes:…
Q: How can banks guarantee the security of the personal information of its clients?
A: According to the information given:- We have to define that banks guarantee the security of the…
Q: 1. The Children's Online Privacy Protection Act ("COPPA") was enacted to primarily prevent which of…
A: In this question we need to choose the main purpose of Children's Online Privacy Protection Act…
Q: How does a data breach effect cloud security? What are some possible countermeasures?
A: According to the information given:- We have to define data breach effect cloud security? What are…
Q: 1.What is the primary goal of change management? To prevent any changes to the IT environment To…
A: So, here three MCQs are given. I will provide you explanation of both correct and incorrect options.…
Q: Trace each pass of selection, insertion, and quick sort for the list of values below. For quick…
A: Answer is explained below in detail Given numbers are 6,3,11,4,9,8,17,7
Q: Why do some people commit crimes online, and how can this be prevented?
A: As we know, With the rapid growth of technology and the internet, the world has become more…
Q: 3. The National Do Not Call Registry is primarily enforced by which two entities through their…
A: Option a). Department of Transportation and the FTC: The Department of Transportation has no direct…
Q: Could you clarify "cybercrime"? Explain and provide examples of these three internet offenses:
A: Cybercrime is a crime involving a computer or computer network. .
Q: Q1-Vigenere cipher is a method of encrypting alphabetic text using a simple form of polyalphabetic…
A: The Vigenère cipher is a type of polyalphabetic substitution cipher that uses a keyword to encrypt…
Q: 75. Which of the following is not a term used to describe a method of acquiring personal identifying…
A: Cybercriminals utilise human engineering, often referred to as social engineering, as a strategy to…
Q: 55. The GDPR replaced which of the following EU regulations? A. Cookie Policy B. GLBA C. Data…
A: No matter where the data is processed or kept, the GDPR is intended to protect the personal data of…
Q: 5. Within how many days must a company cease distributing marketing emails upon receiving an opt-out…
A: The term "email" (short for electronic mail) refers to a digital communication technique that…
Q: 55. The GDPR replaced which of the following EU regulations? A. Cookie Policy 3. GLBA C. Data…
A: Correct answer is given below
Q: 9. The Health Insurance Portability and Accountability Act ("HIPAA") consists of which two rules to…
A: The Health Insurance Portability and Accountability Act (HIPAA) is a federal law governing the…
Q: Better and cheaper technology will allow it to be distributed across the global, this is known as…
A: The global technology revolution is defined as the revolution of materials, devices, and…
Q: specific consent from a patient prior to disclosure, assuming you have received prior authorization…
A: Answer for the mcq question is given below with explanation
Q: Computer ethics examines a vast number of topics, some of which include the following: governance,…
A: As technology progresses, computer ethics ensure the protection of sensitive data. The field of…
Q: For an Orthogonal frequency-division multiplexing data transmission with a cyclic prefix of 20 and…
A: Orthogonal Frequency Division Multiplexing (OFDM) is a digital modulation technique used in modern…
Q: The options for b is 108,5001,78, 99- choose one The options for a is 99,78,120, none-choose one…
A: The definition of error correction codes communication protocols are designed error detection and…
Q: 34. Which rule within the HIPAA Privacy Rule requires transfer of only the protected health…
A: In this question we need to choose the correct HIPAA privacy rule which requires transfer of the…
Q: Can cybercrime teach us about ideation and conclusion-drawing?
A: Here is your solution -
Q: What common beliefs and practises define the vast majority of current cybercrime? Please include…
A: Cybercrime refers to criminal activities that are committed using a computer, network, or other…
Q: Please provide at least three reasons why it is necessary to encrypt data.
A: Data is converted from its unencrypted form into an impenetrable code via the process of encryption.…
Q: Discuss a key finding from the Church Committee investigations and how you might improve the…
A: The Church Committee investigations were conducted in the 1970s to examine the intelligence…
Q: A recent incident involving a security vulnerability in authentication or access control could be…
A: => A security vulnerability, also known as a security flaw or security weakness, is a…
Q: While using Windows 10, how can I create a backup, and what are the main benefits?
A: This question wants clarity on the numerous backup techniques that are offered in Windows 10 as well…
Q: What steps do you think are essential to ensure the safety of data during transmission and storage?…
A: To ensure the safety of data during transmission and storage, there are several steps that can be…
Q: For your additional piece of mind, debit cards supplied by banks often include a unique security…
A: Financial institutions need to use encryption and ad hoc management solutions to protect the…
Q: You are the IS Manager at Agate Construction Company, Ltd. (ACCL). The company's board of directors…
A: This is my answer to the question you just posed. As the information systems manager at Agate…
Q: Vulnerability 1: Name and consequences of the vulnerability: As a hacker, how can you exploit the…
A: Vulnerability in cybersecurity means the weakness in the system that cybercriminals/hackers can make…
Q: Why You Should Employ the Cyber Kill Chain Model.
A: The Cyber Kill Chain model is a framework that was originally developed by Lockheed Martin to help…
Q: When making a cybercrime complaint, the "FIA Complaints Registration Form" must be filled out. Where…
A: The first step in understanding the FIA Complaints Registration Form is to familiarize yourself with…
Q: Cybercrime and society 2) Determine the best Internet-crime prevention methods.
A: Internet crime, otherwise called cybercrime, has turned into a huge danger to people, organizations,…
Q: What are the main distinctions between certificate-based authentication and password-based…
A: According to the information given;- We have to define the main distinctions between…
Q: 67. Which of the following constitutional protections is frequently a hurdle in passing laws and…
A: We have laws for the protection of regulations designed to restrict information shared or posted…
Q: 2. If an information technology auditor working on behalf of a hospital with a valid business…
A: The hospital and auditor are required to comply with the Health Insurance Portability and…
Q: Choose security devices (video cameras, monitoring, Intrusion Protection/Detection systems,…
A: According to the information given:- We have to define choose security devices that you will install…
please choose the most correct anwser.
Step by step
Solved in 5 steps
