55. The GDPR replaced which of the following EU regulations? A. Cookie Policy B. GLBA C. Data Directive D. Omnibus Rule
Q: How different are network apps from other kinds of apps in terms of their layout?
A: A network application is defined as the application which is running on one host providing…
Q: How can banks guarantee the security of the personal information of its clients?
A: According to the information given:- We have to define that banks guarantee the security of the…
Q: Do you worry about security and privacy issues associated with the growing use of cloud computing in…
A: Here is your solution -
Q: 17. Which of the following is NOT a type of safeguard mandated by the Security Rule of the…
A: The Gramm-Leach-Bliley Act (GLBA) is a U.S. federal law that was enacted in 1999. It is also known…
Q: When making a cybercrime complaint, the "FIA Complaints Registration Form" must be filled out. Where…
A: The first step in understanding the FIA Complaints Registration Form is to familiarize yourself with…
Q: 44. Did the pharmacy commit a violation of HIPAA's Privacy Rule? A. No, the insurance identification…
A: Correct answer and incorrect answers are explained
Q: 78. Under the Fair Credit Reporting Act, Consumer Reporting Agencies must follow reasonable…
A: Consumer reporting agencies (CRAs) are required to adhere to reasonable processes under the Fair…
Q: 4. One of the lessons that can be derived from the Equifax Data Breach is that companies should…
A: Millions of people's personal information was compromised in 2017's huge cyberattack known as the…
Q: There are a few ways in which conventional email might be compromised by a denial of service attack.…
A: Denial of Service attack on email is a malicious attack that used to disrupt the normal functioning…
Q: This article covers cyberbullying from every conceivable perspective, beginning with its roots and…
A: Cyberbullying is a growing problem in our society, with millions of people around the world being…
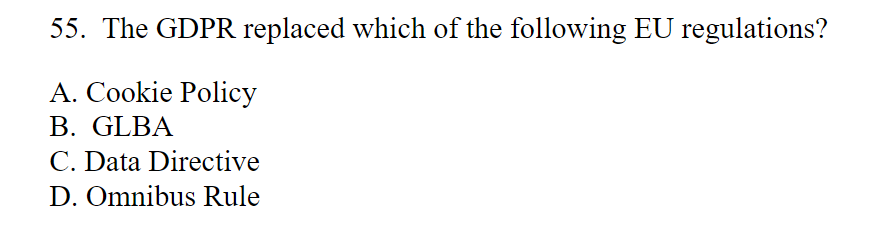
Q: 55. The GDPR replaced which of the following EU regulations? A. Cookie Policy 3. GLBA C. Data…
A: Correct answer is given below
Q: 46. Which of the following is not a privacy/security law? A. TCPA B. HIPPA C. GLBA D. FCRA
A: The Telephone Consumer Protection Act (TCPA), which limits telemarketing calls and unsolicited…
Q: Denial of service attacks may harm traditional email. Will you use this information to defend…
A: Denial of Service (DoS) attacks includes an attacker flooding a targeted system or network with…
Q: 5. Within how many days must a company cease distributing marketing emails upon receiving an opt-out…
A: Correct answer for mcq question is given below
Q: Why is it important to control the protection of information?
A: Controlling the protection of information is crucial for several reasons, including:…
Q: 4. One of the lessons that can be derived from the Equifax Data Breach is that companies should…
A: Correct answer is given below with explanation. Please note that even incorrect answers explanation…
Q: A Cyber Treaty can be paralleled to which treaties defined before it? Group of answer choices…
A: The world has become increasingly interconnected with the rapid development of technology,…
Q: RISK REGISTER : CYBER SECURITY LAB (KEYLOGGING SOFTWARE). Please add 3 more risks. Intructions:…
A: In project management, it is important to identify and assess risks in order to develop effective…
Q: Explain in detail how a challenge-response system is used to verify a user's identity. It's not…
A: In this question we need to explain how challenge response system is utilized for verifying a user's…
Q: Debit cards that are issued by banks come with a one-of-a-kind identifying number that adds an extra…
A: According to the information given:- We have to define the above scenario with explain the reason…
Q: Cybercrime and society 2) Determine the best Internet-crime prevention methods.
A: Internet crime, otherwise called cybercrime, has turned into a huge danger to people, organizations,…
Q: Choose security devices (video cameras, monitoring, Intrusion Protection/Detection systems,…
A: According to the information given:- We have to define choose security devices that you will install…
Q: A case study on a recent incident involving an authentication or access control security…
A: According to the information given:- We have to define above case study.
Q: For your additional piece of mind, debit cards supplied by banks often include a unique security…
A: Financial institutions need to use encryption and ad hoc management solutions to protect the…
Q: The "FIA Complaints Registration Form" must be completed when reporting an incident of cybercrime. I…
A: A cybercrime complaint is an essential first step if you have experienced online abuse or fraud.…
Q: 3. The National Do Not Call Registry is primarily enforced by which two entities through their…
A: Telemarketing is defined as the process of virtually selling products or services through the…
Q: Carry out a quick risk management analysis on your laptop. Determine what you have, what you need to…
A: In the age of the digital era, most of our daily activities are done through computers and laptops.…
Q: 60. The European Union takes which approach to privacy protection? A. Comprehensive B. Sectoral C.…
A: In this question we need to choose the correct option related to European Union (EU) privacy…
Q: What kinds of assumptions about the person who performed an illegal act on the internet are often…
A: Introduction : When unlawful conduct is committed on the internet, assumptions about the culprit are…
Q: In a large corporation, what are the typical steps involved in obtaining clearance to update a…
A: Here is your solution -
Q: 0. In the healthcare sector, cybersecurity through IoT devices like wireless insulin pumps hich…
A: Correct mcq answer is explained below Please note explaination for incorrect answers is also given
Q: Can cybercrime teach us about ideation and conclusion-drawing?
A: Here is your solution -
Q: 2. If an information technology auditor working on behalf of a hospital with a valid business…
A: The hospital and auditor are required to comply with the Health Insurance Portability and…
Q: Explain what you mean by the term "cybersecurity" and why it's so important to put it into effect.
A: Here is your solution -
Q: 41. The Computer Fraud and Abuse Act contains a potentially problematic definition of "protected…
A: A federal legislation known as the Computer Fraud and Abuse Act (CFAA) makes a number of…
Q: A recent incident involving a security vulnerability in authentication or access control could be…
A: => A security vulnerability, also known as a security flaw or security weakness, is a…
Q: 34. Which rule within the HIPAA Privacy Rule requires transfer of only the protected health…
A: In this question we need to choose the correct HIPAA privacy rule which requires transfer of the…
Q: Differentiate digital piracy from intellectual property infringement using examples.
A: In this question we need to explain the differences between intellectual property infringement and…
Q: 69. Which of the following statutes is included in the Electronic Communications Privacy Act? A.…
A: The statute included in the Electronic Communications Privacy Act (ECPA) is the Stored…
Q: Create a logic circuit system for the following expressions. A'B'+ABC (XY)'Z X+Y+Z A'B'C AB'+CD…
A: 4. Given, The inputs of the logic circuit are A, B, and C. And the output of the logic circuit is…
Q: You are the IS Manager at Agate Construction Company, Ltd. (ACCL). The company's board of directors…
A: This is my answer to the question you just posed. As the information systems manager at Agate…
Q: How does a data breach effect cloud security? What are some possible countermeasures?
A: According to the information given:- We have to define data breach effect cloud security? What are…
Q: Better and cheaper technology will allow it to be distributed across the global, this is known as…
A: The global technology revolution is defined as the revolution of materials, devices, and…
Q: 6. When a website operator states in its privacy notice that it will not share financial information…
A: Here is your solution -
Q: 3) Given that main memory is composed of only three page frames for public use and that a seven-page…
A: FIFO is a simple and easy-to-implement algorithm, but it may not always result in optimal…
Q: 29. The Fair Credit Reporting Act has regulations, of some variety, for all of the following…
A: The Fair Credit Reporting Act (FCRA) is a federal law that governs the collection, disclosure, and…
Q: If your company's email server tells you that your password has changed, it is your obligation to…
A: According to the information given;- We have to define If your company's email server tells you that…
Q: A- Describe the three steps in ElGamal cryptosystems. Encrypt the message m=5 for p=17 and a=6.
A: The ElGamal cryptosystem is a public-key cryptosystem that relies on the intractability of the…
Q: The options for b is 108,5001,78, 99- choose one The options for a is 99,78,120, none-choose one…
A: The definition of error correction codes communication protocols are designed error detection and…
Q: .Which federal agency formally manages the United States' cybersecurity policies?
A: Here is your solution -
please choose the correct option.
Step by step
Solved in 3 steps
