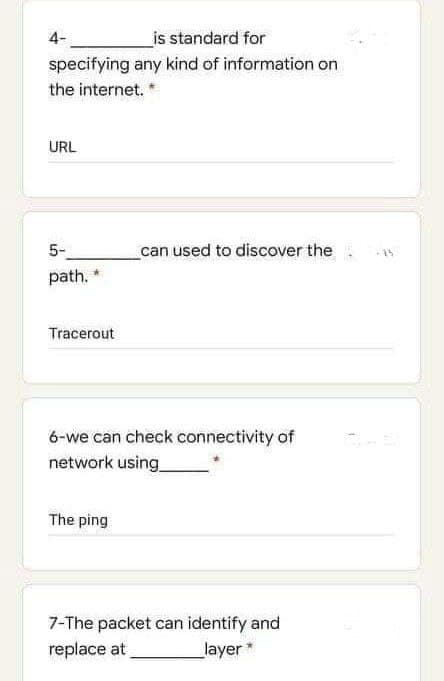
4- is standard for specifying any kind of information on the internet. * URL can used to discover the 5- path." Tracerout
Q: Computer architecture and computer-based organization are two distinct but related concepts in the…
A: Introduction: The process of merging physical components to create a computer system is known as…
Q: hat are use-case diagrams used for?
A: Introduction: The dynamic behaviour needs to be captured, as this is the most crucial part. The…
Q: What is the OS's role in controlling the processor?
A: Answer: The OS is utilized to run programs by tapping on a symbol, choosing the program from a menu,…
Q: What operating system components are always in memory?
A: Introduction: The portion of the operating system that lives in memory and is referred to as the…
Q: Rewrite the following function using a while loop. det munched(values): Hysterious for a while.…
A: #re-writing given function using while loopdef munched(values): value_limit=40 result=[]…
Q: What difficulties were intended to be remedied by the initial Internet research? In the end, how did…
A: Given: The development of the Internet has been influenced in a variety of various ways by a wide…
Q: Fill in the blank: LC-3 instruction types include: computational instructions, data movement…
A: Answer: Control flow instructions conditionally change the PC. The LC-3 keeps three 1-bit registers…
Q: Consider the current state of the internet and its technical underpinnings.
A: Intro Consider the internet's development and the technical foundations it now relies on. The…
Q: 10. I Love CCS by Jemar Jude Maranga Write a program that will take as input an integer n, and will…
A: We will use Java programming language for this question Algorithm: Ask user to input an integer…
Q: his cod >>7* The result of executing .----((6&1) + (~0.00) +(0&5)); is 7 O 49 O 48 O error cod O 14…
A: Please refer below for your reference: The operators used in below expression are bitwise and ,…
Q: What is a circular linked list? How the end-of-list condition will be tested in circular linked…
A: The first member of a circular linked list points to the last element, while the last element points…
Q: 6. What is the value of sizeof(int)? (a) 1 (b) 2 7. What is the value of sizeof(uint16_t)? (a) 1 (b)…
A: The question is to select correct option for the given questions.
Q: The following instruction is used for: GPIO PORTA_DIR_R&= -0x20; Select one: O a. direction PFS…
A: Answer the above question are as follows
Q: Is it conceivable for an UDP-running programme to acquire a dependable data transmission at the same…
A: Introduction: UDP, or User Datagram Technology, is a time-critical Internet communication protocol…
Q: Is it beneficial to use the internet if you have a disability, mental or physical? Are there any…
A: Internet: People who are visually challenged benefit from the internet. Thanks to the internet, they…
Q: As one variable goes up, the other variable goes down” is a description of:
A: Correlation is a method of statistical measure which is expressing the extent to of two variables…
Q: he inode (index node) is a data structure in a Unix-style file system that describes a file-system…
A: Answer 1…
Q: The residue of 6 (mod 5) is (Round to the nearest whole number.)
A: The above question is solved in step 2 :-
Q: In what ways are TCP and UPD session hijacking different from one another?
A: The term "session hijacking" refers to the act of an attacker taking control of another user's…
Q: 1. Among the advantages of the control system, what specific advantage addresses that control system…
A: The question has been answered in step2
Q: Please describe, in as few words as possible, the main differences between the Linux clone operating…
A: Introduction: Linux is a functional operating system that is based on UNIX.
Q: Where do ethics fit into the realm of computer science technology ?
A: Ethics are a structure of norms and practices that impact how people lead their lives. It isn't…
Q: If A and B are sets and f: A→ B, then for any subset S of A we define f(S) = {be B: b= f(a) for some…
A:
Q: Write a C++ Program to find Factorial of a number using class. int main() is provided, all you have…
A: #include <iostream>using namespace std;//factorial classclass factorial{ private: int…
Q: Tot Create a Java program that will declare a method parameter list ( amtPerUnit, totalUnits,…
A: I have implemented the TotalFee() and main method to test the above method.
Q: Create a flowchart calculating the average grade of students. Grades M1-77, M2-80, M3-75,…
A: Use diamonds to create decision box Use ovals to start/end Use rectangles to perform operations
Q: What is the acronym for "Transaction Protocol Data Unit" in the discipline of computer science?
A: Intro In the field of computer science, what does the abbreviation for "Transaction Protocol Data…
Q: erson class. Your class must have the following features: Student - major: String + Student() +…
A: Given : Student inherited from Person class
Q: B/ Write a matlab code to find sum all elements of a vector, if the vector is the following. M=[5, 7…
A: Introduction: MATLAB is the is of the programming platform to do Mathematics calculations and in…
Q: Concurrent processing methods provided by rival operating systems are integrated into Linux.
A: Concurrent processing of a computer model in which multiple processors execute instructions…
Q: i need the answer quickly
A: The answer to the following question:-
Q: Find Context-Sensitive Grammars equivalent to the below grammars: S→ LaMR L → LT | E T a →…
A: Below I have provided the handwritten solution
Q: The more time you spend on social networking, the more advantages you'll reap. The definition of…
A: Social networking: A social networking service (also known as a social networking site) is an online…
Q: * The means if a sample is compressed in one direction it tends to get thicker in the lateral…
A: Answer 1: At the point when an example of material is extended in one course it will in general get…
Q: Define a Turing Machine that accepts the following language: L = {w € {!,}* | w = vw'v where v, w' =…
A: Below I have provided the solution:
Q: Which protocol encrypts data transferred between a browser and a web server using SSL or TLS?
A: Introduction: Encryption protocols known as SSL (Secure Sockets Layer) and TLS (Transport Layer…
Q: Assume the alphabet is (a, b, c). In the following questions, give a regular expression that…
A: Below is the answer to above question. I hope this will be helpful for you..
Q: Make sure to look at the protocols currently in use while you're evaluating the internet. An…
A: Given: Tracking the False Positive Reporting Rate is one technique to assess the efficacy of…
Q: The natural logarithm can be approximated by the following series. x-1 1 + ( ) ( ) ( ) + + +... X 2…
A:
Q: In what ways are processors able to communicate with their main memory counterparts?
A: In what ways are processors able to communicate with their main memory counterparts?
Q: When it comes to computers, computer-based architecture and computer-based organization are two…
A: Introduction: Computer-based architecture: It involves the way physical components/units are…
Q: What is a model in the context of System Analysis? Use logic and physical models to distinguish…
A: In system analysis, the design, definition, and analysis of a model may be used to relate particular…
Q: What are the essential components of an organization’s IS infrastructure?
A: The complete solution is given below:-
Q: ess to your department's DNS servers' DNS caches. How would you go about discovering which web…
A: Introduction: DNS server or client to save DNS records locally and reuse them in the future,…
Q: A program in a procedural programming language, such as C or Java, consists of a list of statements,…
A: Solution is given below
Q: What are the numerous components that comprise a conventional piece of web-based software, and how…
A: Intro A typical Web application consists of the following components: Client-Side Application…
Q: Raspberry Pi has the following features: Select one or more: a. small size b. Hard disk drive c.…
A: Answer- a ,e , f , h.
Q: Should there be an essay written about how important networking is in the field of information…
A: Information technology : Information technology (IT) is the use of computers, storage, networking,…
Q: ating system differs from UNIX proce
A: Introduction: An operating system that performs similarly to classic UNIX (forking methods, same way…
Q: 19 KS]: Write the number as a word. 31 100
A: let's see the correct answer of the question
Step by step
Solved in 2 steps

- q38- Which statement is true about VLSM? Select one: A. It implies classful routing B. It is only suitable for smaller organizations C. It leads to a lot of IP addresses being unused D. It creates subnets of different sizes E. It is subnetting large networks only6 Implement live video over udp from sender to viewer with opencv Please don't copy from internet. Thank you!14) __________ refers to the combination of HTTP and SSL to implement secure communication between a Web browser and a Web server. A) TLS B) HTTPS C)SSH D) IPSec
- q33- What is one of the characteristics is commonly associated with dynamic routing protocols? Select one: A. Requre special subnets masks B. Require less processing power than static routes require C. Require device configuration D. Consume some bandwidth to exchange routes informationQ7. Suppose we have the following IP addresses for two different organizations, we have to create 5 networks having 30 hosts in it. Find first sub network ID, Fist address, Last address and Braodcast for each of the following given addresses.a. 17.23.120.8b. 252.5.15.111Which of the following is NOT a reason to be against using static routing? O. More resources, such increased CPU power or bandwidth, are not necessary. O.b. Since the routing tables are very small, minimal maintenance is required. O.c. Any modification to the topology will have an impact on the configuration. The path never veers from the objective on the way there.
- Please answer the following questions asking for protocols we’ve encountered thus far. When stating the protocol, use ONLY the acronyms that describe them (e.g. “UDP”). No answer should repeat: a. I’m a host that just attached to a public network. I obtain an IP automatically via: _______?(Which protocol?) b. I’m an application wishing to establish a reliable connection with a server via port 80.Therefore, I open a connection-oriented session using: _______ ?(Which protocol?) c. I want to reach a web server host at www.google.com, so I then obtain its IP addressusing _______ ?(Which protocol?) d. Once I connect, I---the application---pull/retrieve the web page using _________?(Which protocol?) e. Whoa, I’m the server! You tried to reach a PORT number that actually doesn’t exist!Therefore I convey my error and reply back by using ________ ?(Which protocol?) f. Hold it right there, cowboy, I’m a router! I need to figure out all the best routes for all othernodes connected in my intra-AS…Lab – Routing Objective Learn and practice routing using Node and Express. Specification Create a web server that Accepts and processes request messages submitted from browser, and Generates and sends response messages back to browser for display. Your web server must be able to handle URL with hostname and port Request message URL: 0.0.1:3000 Response message: “SUCCESS!” URL with hostname, port and path echo Request message URL: 0.0.1:3000/echo Response message: “SUCCESS! echo” URL with hostname, port, path foxtrot and route parameter value kilo Request message URL: 0.0.1:3000/foxtrot/kilo Response message: “SUCCESS! Received kilo via foxtrot” where the value kilo must be retrieved via the route parameter Invalid/unexpected URL Request message URL: 0.0.1:3000/<any other value> Response message: “FAILED! Fix your URL.” Hostname 127.0.0.1 can be replaced by localhost. Port number 3000 can be replaced by any other port number that is from 1024 (2^11)…What distinguishes the three protocols known as Simple Mail Transfer Protocol (SMTP), Post Office Protocol (POP), and Internet Message Access Protocol (IMAP) when it comes to sending and receiving electronic mail over the web? To provide a complete picture, it's helpful to describe the agents on both the sending and receiving nodes.
- 34. Which of the following algorithms is not a broadcast routing algorithm? a. Flooding b. Multi-destination routing c. Reverse path forwarding d. All of the aboveM06 Discussion Board - Networking 99 unread replies.99 replies. Scenario: You have just installed a SOHO router in your customer's home and the owner has called you saying that Internet gaming is too slow. The customer is using a wireless connection to the network. What are the possibilities you might consider in order to speed up the customer's gaming experience?Transcribed Image Text 2. You are required to design IP addressing scheme for the Pantai Siring's branch for all floors using VLSM subnetting. You may use any private IP address class (10.0.0.0 to 10.255.255.255, 172.16.0.0 to 172.31.255.255 or 192.168.0.0 to 192.168.255.255). User group are as follows: a. Ground Floor- Administrator – 10 hosts b. 1* Floor - Lecturer – (Based on the last 2 digits of your Matric Number) For Example: B031910402 – 2 hosts only c. 2nd Floor - Student – 250 hosts d. 3rd Floor - Management – 80 hosts Explain in steps the calculations of your IP addressing scheme.



