4. 5. In a group of 100 students, 90 study Mathematics, 80 study Physics, and 5 study none of these subjects. Find the probability that a randomly selected student: (a) studies Mathematics given that he or she studies Physics, and (b) does not study Physics given that he or she studies Mathematics. In a certain assembly plant, three machines, Machine 1, Machine 2 and Machine 3 make 30%, 45% and 25% respectively of the products. It is known from the quality control data collected from the past that 2%, 3% and 2% of the products made by each machine respectively, are defective. If a product is chosen randomly chosen and found to be defective, what is the probability that it is made by Machine 32
4. 5. In a group of 100 students, 90 study Mathematics, 80 study Physics, and 5 study none of these subjects. Find the probability that a randomly selected student: (a) studies Mathematics given that he or she studies Physics, and (b) does not study Physics given that he or she studies Mathematics. In a certain assembly plant, three machines, Machine 1, Machine 2 and Machine 3 make 30%, 45% and 25% respectively of the products. It is known from the quality control data collected from the past that 2%, 3% and 2% of the products made by each machine respectively, are defective. If a product is chosen randomly chosen and found to be defective, what is the probability that it is made by Machine 32
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter19: Probabilistic Dynamic Programming
Section19.4: Further Examples Of Probabilistic Dynamic Programming Formulations
Problem 10P
Related questions
Question
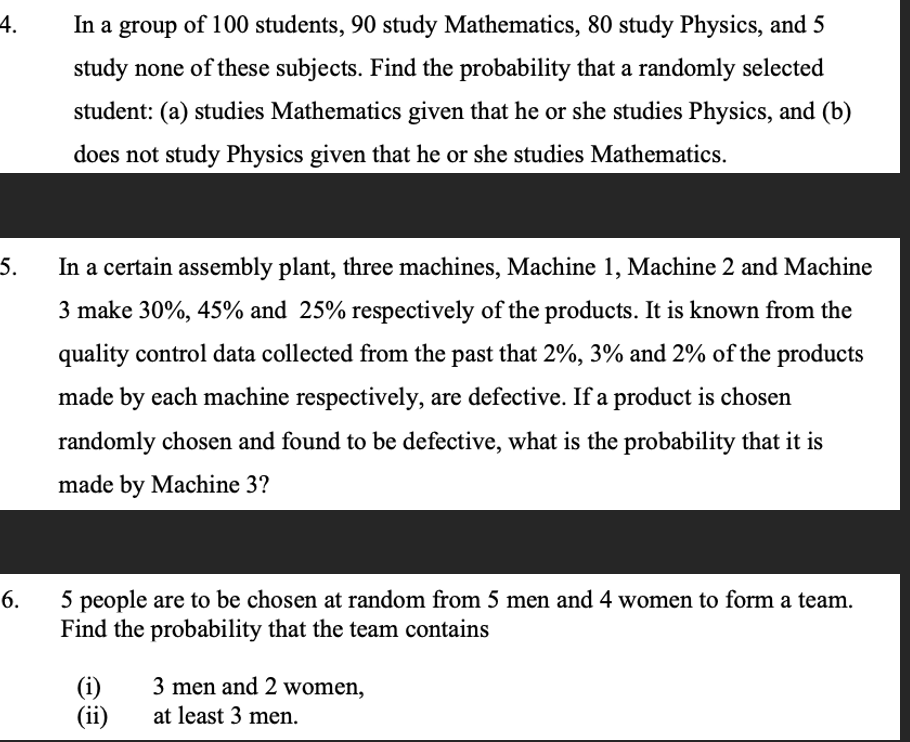
Transcribed Image Text:4.
5.
In a group of 100 students, 90 study Mathematics, 80 study Physics, and 5
study none of these subjects. Find the probability that a randomly selected
student: (a) studies Mathematics given that he or she studies Physics, and (b)
does not study Physics given that he or she studies Mathematics.
In a certain assembly plant, three machines, Machine 1, Machine 2 and Machine
3 make 30%, 45% and 25% respectively of the products. It is known from the
quality control data collected from the past that 2%, 3% and 2% of the products
made by each machine respectively, are defective. If a product is chosen
randomly chosen and found to be defective, what is the probability that it is
made by Machine 3?
6.
5 people are to be chosen at random from 5 men and 4 women to form a team.
Find the probability that the team contains
(i)
(ii)
3 men and 2 women,
at least 3 men.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole