4. Create and save a screenshot of the results. How many threats were identified on your machine? 5. Review any potentially malicious files that were identified, and quarantine those you believe are malicious. If you are not sure, the safest option is to quarantine the file. 6. Locate the setting options for Malwarebytes. Does Malwarebytes scan for rootkits by default? 7. What does PUP stand for?
4. Create and save a screenshot of the results. How many threats were identified on your machine? 5. Review any potentially malicious files that were identified, and quarantine those you believe are malicious. If you are not sure, the safest option is to quarantine the file. 6. Locate the setting options for Malwarebytes. Does Malwarebytes scan for rootkits by default? 7. What does PUP stand for?
Enhanced Discovering Computers 2017 (Shelly Cashman Series) (MindTap Course List)
1st Edition
ISBN:9781305657458
Author:Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Publisher:Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Chapter4: Programs And Apps: Productivity, Graphics, Security, And Other Tools
Section: Chapter Questions
Problem 3M
Related questions
Question
please provide screenshots and step by step information
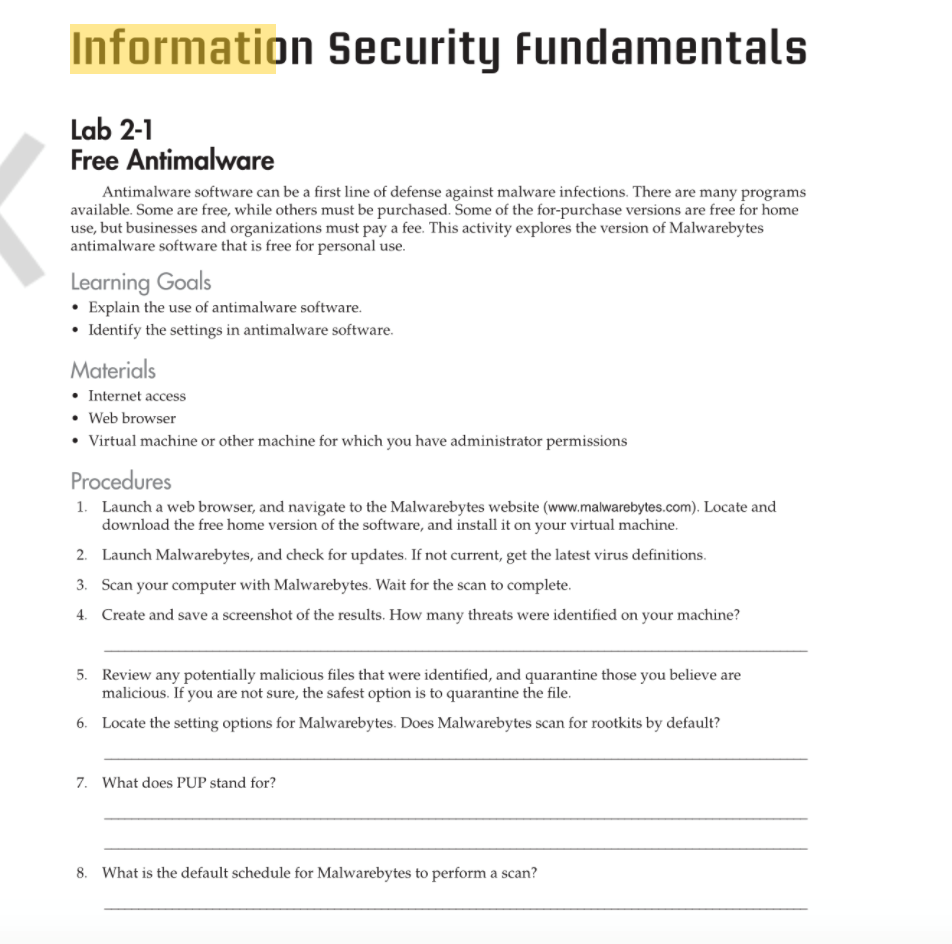
Transcribed Image Text:Information Security Fundamentals
Lab 2-1
Free Antimalware
Antimalware software can be a first line of defense against malware infections. There are many programs
available. Some are free, while others must be purchased. Some of the for-purchase versions are free for home
use, but businesses and organizations must pay a fee. This activity explores the version of Malwarebytes
antimalware software that is free for personal use.
Learning Goals
• Explain the use of antimalware software.
• Identify the settings in antimalware software.
Materials
• Internet access
• Web browser
• Virtual machine or other machine for which you have administrator permissions
Procedures
1.
Launch a web browser, and navigate to the Malwarebytes website (www.malwarebytes.com). Locate and
download the free home version of the software, and install it on your virtual machine.
2. Launch Malwarebytes, and check for updates. If not current, get the latest virus definitions.
3. Scan your computer with Malwarebytes. Wait for the scan to complete.
4. Create and save a screenshot of the results. How many threats were identified on your machine?
5. Review any potentially malicious files that were identified, and quarantine those you believe are
malicious. If you are not sure, the safest option is to quarantine the file.
6. Locate the setting options for Malwarebytes. Does Malwarebytes scan for rootkits by default?
7. What does PUP stand for?
8. What is the default schedule for Malwarebytes to perform a scan?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Enhanced Discovering Computers 2017 (Shelly Cashm…
Computer Science
ISBN:
9781305657458
Author:
Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Publisher:
Cengage Learning

Enhanced Discovering Computers 2017 (Shelly Cashm…
Computer Science
ISBN:
9781305657458
Author:
Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Publisher:
Cengage Learning