4.1-4. What type of control plane? We've seen that there are two approaches towards implementing the network control plane - a per-router control-plane approach and a software-defined networking (SDN) control-plane approach. Which of the following actions occur in a per-router control-plane approach? The other actions that you don't select below then correspond to actions in an SDN control plane. O A control agent in router receives a complete forwarding table, which it installs and uses to locally control datagram forwarding. A router exchanges messages with another router, indicating the cost for it (the sending router) to reach a destination host. | Routers send information about their incoming and outgoing links to other routers in the network. | All routers in the network send information about their incoming and outgoing links to a logically centralized controller.
4.1-4. What type of control plane? We've seen that there are two approaches towards implementing the network control plane - a per-router control-plane approach and a software-defined networking (SDN) control-plane approach. Which of the following actions occur in a per-router control-plane approach? The other actions that you don't select below then correspond to actions in an SDN control plane. O A control agent in router receives a complete forwarding table, which it installs and uses to locally control datagram forwarding. A router exchanges messages with another router, indicating the cost for it (the sending router) to reach a destination host. | Routers send information about their incoming and outgoing links to other routers in the network. | All routers in the network send information about their incoming and outgoing links to a logically centralized controller.
Principles of Information Security (MindTap Course List)
6th Edition
ISBN:9781337102063
Author:Michael E. Whitman, Herbert J. Mattord
Publisher:Michael E. Whitman, Herbert J. Mattord
Chapter6: Security Technology: Access Controls, Firewalls, And Vpns
Section: Chapter Questions
Problem 2RQ
Related questions
Question
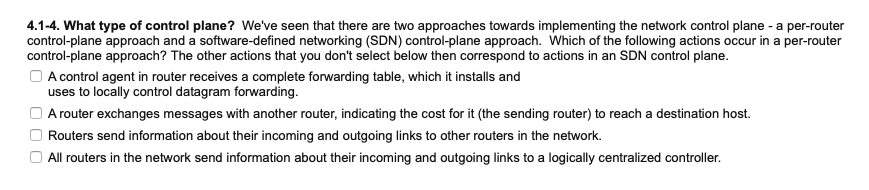
Transcribed Image Text:4.1-4. What type of control plane? We've seen that there are two approaches towards implementing the network control plane - a per-router
control-plane approach and a software-defined networking (SDN) control-plane approach. Which of the following actions occur in a per-router
control-plane approach? The other actions that you don't select below then correspond to actions in an SDN control plane.
O A control agent in router receives a complete forwarding table, which it installs and
uses to locally control datagram forwarding.
A router exchanges messages with another router, indicating the cost for it (the sending router) to reach a destination host.
Routers send information about their incoming and outgoing links to other routers in the network.
All routers in the network send information about their incoming and outgoing links to a logically centralized controller.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning