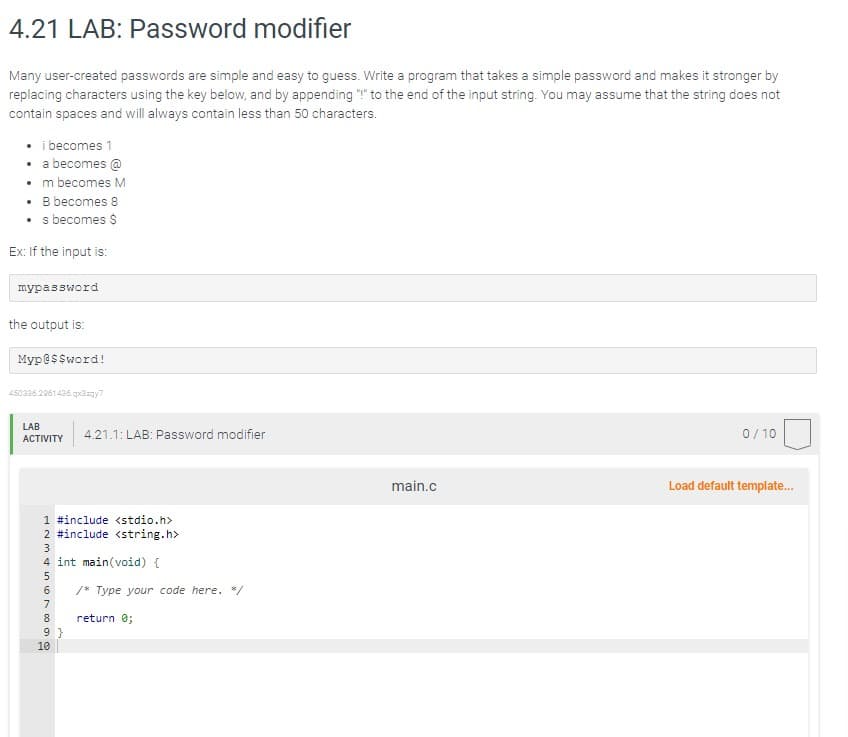
4.21 LAB: Password modifier Many user-created passwords are simple and easy to guess. Write a program that takes a simple password and makes it stronger by replacing characters using the key below, and by appending "!" to the end of the input string. You may assume that the string does not contain spaces and will always contain less than 50 characters. • i becomes 1 • a becomes @ • m becomes M • B becomes 8 • s becomes $ Ex: If the input is: mypassword the output is: Myp@$$word!
Q: How do you think technology and social media affect your social skills and the skills of your peers?…
A: It is widely accepted that technology and social media can have both positive and negative impacts…
Q: What effect, if any, do you believe the internet and globalization have on social cohesion? How can…
A: The globe has undergone a profound transformation due to the "Web and Globalization." The concept of…
Q: People may experience significant inconvenience as a result of a malfunctioning piece of software.…
A: I've included things to look out for in the programme before it's released, as well as things that…
Q: It's no secret that forensics software is used by investigators, but why exactly do they need it?
A: Forensics software is used by investigators to assist in the process of collecting, analyzing, and…
Q: Installing Windows 8 on a gaming machine with integrated video and an empty PCI Express video card…
A: Introduction: Video card: A graphics card (also known as a video card, display card, graphics…
Q: What makes a fiber-coaxial network different from a standard one?
A: What makes a fiber-coaxial network different from a standard one answer in below step.
Q: The definition of real-time operating systems is elucidated with the use of examples. Why should you…
A: The answer is given in the below step
Q: indows 7's setup if you want to join the computer to a domain later? Do you have a time frame in…
A: When setting up Windows 7, you should choose "Work" network location if you plan to join the…
Q: Which
A: Introduction: When setting up a computer running Windows 7, you have the option to choose its…
Q: I need help getting started with a writing assignment on ADTs, abstract data types. Suggested…
A: An Abstract Data Type (ADT) is a high-level description of a collection of data and the operations…
Q: Places where accidents are likely to occur When investigating issues with VLAN trunk formation, you…
A: Use the show interface trunk command to see if the peer-native and local VLANs are compatible. If…
Q: why output is Usage: ./a.out i/r term_number ...Program finished with exit code 1 Press ENTER to…
A: This error occurs because the number of arguments provided is incorrect. The code expects 2…
Q: Can two different devices share the same MAC address? The question is whether or not this will be…
A: MAC:- full form is media access control which is used in communication of network and network…
Q: Which four components of software development are thought to be the most important ones? This is…
A: The study divides the 53 qualities into four groups and emphasizes the most noteworthy traits in…
Q: The This is because it uses is best suited to storing lists of objects that need to be updated,…
A: In Java Collections, Lists are broadly classified into two categories and are as follows Array List…
Q: Implement the following Constructor and member methods as listed below: • public Product(String…
A: java is object-oriented programming language .so all the function and variable which will be going…
Q: Just what are the distinctions between layer 2 and layer 3 switches? Which switch would you choose…
A: Start: What is the difference between layer two and layer three switches? Which switch would you…
Q: Identify and describe the seven levels of organization found in a computer system. Understanding…
A: Microinstructions are low-level control instructions that define a set of datapath control signals.
Q: When referring to subprograms, variables, and other objects in code, which is better to use: fully…
A: Introduction: It is necessary for him to initiate communication with another officer in the sales…
Q: This is syllabus for question in the given picture Course: Data Base Administration Module No. 1…
A: Module No. 1: Introduction to database architectures and database management systems: This module…
Q: Provide a brief background on the evolution of computing.
A: Introduction In this question we asked about the evoluation of computing
Q: We can end unsuccessful searches more quickly if we can presume that the keys in the list have been…
A: Introduction Performing a search in an ordered list is much more efficient than performing a search…
Q: What picture comes to mind when you think of email? Is it probable that a message will reach its…
A: Introduction: is a method of communication ("mailing") amongst electronic device users. Email was…
Q: Is it possible to identify the overarching purpose of software engineering? What, in particular, are…
A: The aim of software engineering may be summed up, and this is accurate.
Q: why output is Usage: ./main exit status 1?
A: I have modified the code so that you can take input and run the program It will prompt you to give…
Q: f this Term.h I need .cpp file of this header file please help me Please make sure they compiles…
A: #include <iostream>#include <string>#include "Date.h" using namespace std; class Term…
Q: Metrics are being used to assess the software quality process and product, which has to be made…
A: Software metric A software metric is a program's quantifiable or countable property. In addition to…
Q: So, what exactly is meant when the term "operating system" is used? Generally speaking, an OS's two…
A: The answer is given below step.
Q: Outlining the characteristics of a real-time OS via illustrations If you're familiar with standard…
A: An operating system is a software platform which provides basic services and manages hardware…
Q: Write a program that has Tracy draw a snowman. Make sure your snowman: • Is made of three gray…
A: Turtle Module : it is an in-built module in Python, which lets the user control a pen(turtle) to…
Q: Create a program that calculates the total cost of a restaurant bill, including tax and tip.…
A: The C# code is given below with output screenshot
Q: Is it feasible to provide more explanation on the four primary advantages that continuous event…
A: Yes it's feasible to provide on the four primary advantages that continuous event simulation offers.
Q: What checks can you do to ensure that each network device has a different MAC address? How about…
A: Each device on a different local network should have the same Media Access Control (MAC) address. If…
Q: What differentiates software engineering from other subfields and areas of engineering are the…
A: Software engineering disciplines: Software engineering, like software architecture, is a metaphor.…
Q: It is possible to describe the distinctions between the Harvard and von Neumann designs as follows:
A: Introduction: Computer architecture refers to the arrangement of the components that comprise a…
Q: In your opinion, how much of a positive impact do you think the internet and other forms of social…
A: The ubiquity of social networks and social media websites is the Internet's most significant social…
Q: Computer Science Problem: Convert the following 32-bit two's complement binary numbers into…
A: (a) First bit is nagtive hence we came to know that number is negative Now , invert all the bits of…
Q: How much should you rely on software service providers for all of your technology needs? What leads…
A: Please find the detailed answer in the following steps.
Q: Which has larger memory addresses, virtual or physical? Why?
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: As a worker in a networking company, describe the information on the general technical skills, as…
A: To succeed in the position of employee at a networking organisation, it is crucial to possess both…
Q: Is it possible, in your opinion, for two network interfaces to share a MAC address? What may be the…
A: Launch: When connecting to a private or public network, a computer employs a network interface. A…
Q: "Free" Yes No Spam Class ents) NoSpam onsider above contingency table listing counts d NoSpam email…
A: A contingency table, also known as a cross-tabulation or cross-tab, is a type of table in statistics…
Q: 4.11 LAB: Number pattern Write a recursive function called print_num_pattern() to output the…
A: Number pattern using recursive function using the python programming language see the below code
Q: As you can see the Ipv4 Cidr block range of Vpc and subnet -1, Which was Created in Aws Console. My…
A: Given that, IPv4 CIDR address for VPC= 10.0.0.0/24 IPv4 CIDR address for subnet 1= 10.0.0.0/25 Total…
Q: What distinguishes remote authentication from local authentication in terms of user identification?…
A: What distinguishes remote authentication from local authentication in terms of user identification?…
Q: why can't output?
A: In this question we will code and check for the output which not working for you Let's code and…
Q: What precisely are these things called triggers? Which function are they meant to serve? How can the…
A: Triggers are SQL procedures that execute automatically when certain commands, including INSERT,…
Q: What is the multifactor identification procedure? What security precautions does it take to guard…
A: Multi factor identification procedure also known as multi-factor Authentication (MFA), is an…
Q: So, what exactly is meant when the term "operating system" is used? Generally speaking, an OS's two…
A: The answer is given below step.
Q: Can you give me a brief rundown of the OS and its main parts? What else can I possibly say?
A: Introduction: Operating systems (OSs) link users to hardware. Operating systems manage files,…
help with code
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

- 21.7 LAB: Login name (Use python) Write a program that creates a login name for a user, given the user's first name, last name, and a four-digit integer as input. Output the login name, which is made up of the first five letters of the last name, followed by the first letter of the first name, and then the last two digits of the number (use the % operator). If the last name has less than five letters, then use all letters of the last name. Ex: If the input is: Michael Jordan 1991 the output is: Your login name: JordaM91 Ex: If the input is: Kanye West 2024 the output is: Your login name: WestK245.21 In Python: A year in the modern Gregorian Calendar consists of 365 days. In reality, the earth takes longer to rotate around the sun. To account for the difference in time, every 4 years, a leap year takes place. A leap year is when a year has 366 days: An extra day, February 29th. The requirements for a given year to be a leap year are: 1) The year must be divisible by 4 2) If the year is a century year (1700, 1800, etc.), the year must be evenly divisible by 400 Some example leap years are 1600, 1712, and 2016. Write a program that takes in a year and determines whether that year is a leap year. Ex: If the input is: 1712 the output is: 1712 is a leap year. Ex: If the input is: 1913 the output is: 1913 is not a leap year. Your program must define and call the following function. The function should return true if the input year is a leap year and false otherwise.def is_leap_year(user_year)Python 3.7.4 Given that add, a function that expects two int parameters and returns their sum, and given that two variables, euro_sales and asia_sales, have already been defined: Write a statement that calls add to compute the sum of euro_sales and asia_sales and that associates this value with a variable named eurasia_sales.
- 12. What is the output of the following program? (2, 3, 6, 8) #include #include #include #include using namespace std; int main() { double x, y; string str; x = 9.0; y = 3.2; cout (sqrt(pow (y, 4))) = " (sqrt(pow (y, 4))) << endl; str = "Predefined functions simplify programming code!"; cout << "Length of str = " << str.length() << endl; return 0; }3.27 LAB: Login name Write a program that creates a login name for a user, given the user's first name, last name, and a four-digit integer as input. Output the login name, which is made up of the first six letters of the first name, followed by the first letter of the last name, an underscore (_), and then the last digit of the number (use the % operator). If the first name has less than six letters, then use all letters of the first name. Ex: If the input is: Michael Jordan 1991 the output is: Your login name: MichaeJ_1 Ex: If the input is: Nicole Smith 2024 the output is: Your login name: NicoleS_45.17 LAB: Output words in a sentence that are at least 4 characters long The starter code reads in user input (assumed to be one or more sentences), and removes the punctuation. Iterate through the list of words and output the words that are more than 3 characters long. Ex: If the input is: Hello, how are you today? the output is: Hello today #provided code import stringuserInput = input() # this creates a mapping which maps each punctuation character to a null string (None)mapping = str.maketrans('', '', string.punctuation) # this removes puncutation from the stringuserInput = userInput.translate(mapping) print('User input without punctuation:', userInput) # split the string into wordswords = userInput.split()print('User input contains the following words: ')print(words)
- 8.16 (Searching for Substrings) Write a program that inputs a line of text and a search string from the keyboard. Using function strstr, locate the first occurrence of the search string in the line of text, and assign the location to variable searchPtr of type char *. If the search string is found, print the remainder of the line of text beginning with the search string. Then, use strstr again to Locate the next occurrence of the search string in the line of text. If a second occurrence is found, print the remainder of the line of text beginning with the second occurrence. [Hint: The second call to strstr should contain searchPtr + 1 as its first argument.] Solve without using pointersQ_4.*. A phrase is a palindrome if, after converting all uppercase letters into lowercase letters and removing all non-alphanumeric characters, it reads the same forward and backward. Alphanumeric characters include letters and numbers. Given a string s, return true if it is a palindrome, or false otherwise. Example 1: Input: s = "A man, a plan, a canal: Panama" Output: true Explanation: "amanaplanacanalpanama" is a palindrome. Example 2: Input: s = "race a car" Output: false Explanation: "raceacar" is not a palindrome..5.28 LAB: Convert to binary - functions Write a program that takes in a positive integer as input, and outputs a string of 1's and 0's representing the integer in binary. For an integer x, the algorithm is: As long as x is greater than 0 Output x % 2 (remainder is either 0 or 1) x = x / 2 Note: The above algorithm outputs the 0's and 1's in reverse order. You will need to write a second function to reverse the string. Ex: If the input is: 6 the output is: 110 Your program must define and call the following two functions. The IntegerToReverseBinary() function should return a string of 1's and 0's representing the integer in binary (in reverse). The ReverseString() function should return a string representing the input string in reverse. string IntegerToReverseBinary(int integerValue)string ReverseString(string userString)
- 7. using c++, If c is a character (e.g. char c = ‘a’), then (int) c is a number between 0 and 255 that represents its ascii value of that character (the ascii value of ‘a’ is 97. Appendix B contains the ascii character set; for example, (int) ‘a’ == 97. Write a function that accepts two characters, c1, and c2, determines whether (int) c1 is greater than (int) c2, and then returns the sum of the ascii values of all the characters between c1 and c2.7.24 LAB: Convert to binary-functions Write a program that takes in a positive integer as input, and outputs a string of 1's and O's representing the integer in binary. For an integer x, the algorithm is As long as x is greater than 0 Output x 2 (remainder is either 0 or 1) x = x // 2 Note: The above algorithm outputs the 0's and 1's in reverse order. You will need to write a second function to reverse the string Ex: If the input is the output is: 110 The program must define and call the following two functions. Define a function named int to reverse_binary() that takes an integer as a parameter and returns a string of 1's and O's representing the integer in binary (in reverse). Define a function named string reverse() that takes an input string as a parameter and returns a string representing the input string in reverse. def int_to_reverse_binary(integer_value) def string reverse(input_string) LAB ACTIVITY 7.24.1: LAB. Convert to binary-functions 0/10 1 # Define your functions here. 2…Python 3.7.4: Assume that C is a variable has been assigned a string value. Write an expression whose value is true if and only if C is what is called a whitespace character. (that is a space or a tab or a newline-- none of which result in ink being printed on paper) When I attempted it myself, MyProgrammingLab said that I "almost certainly should be using or."

