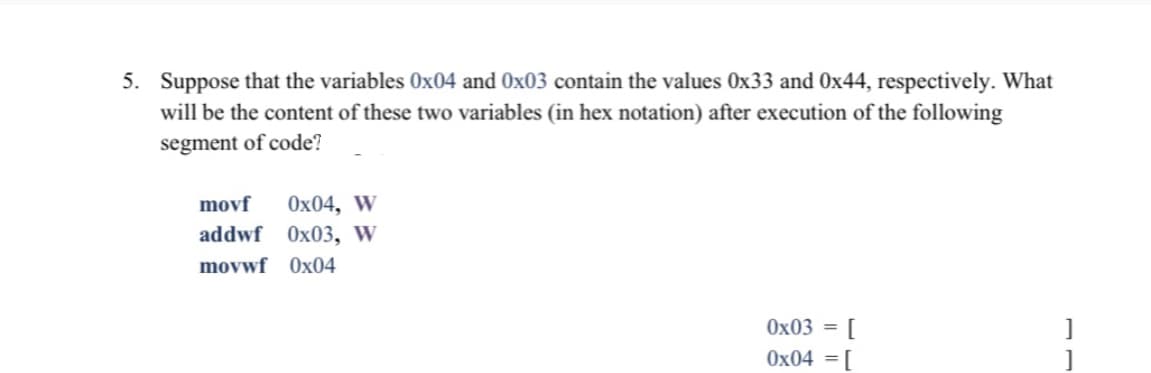
5. Suppose that the variables 0x04 and Ox03 contain the values 0x33 and Ox44, respectively. What will be the content of these two variables (in hex notation) after execution of the following segment of code? Ox04, W addwf 0x03, w movf movwf Ox04 Ox03 = 0x04 = [
Q: Why is it more difficult to break a cipher with a short message?
A: In cryptology, the study of cryptographic calculations, a cypher is a set of steps for encoding and…
Q: The systems analyst is expected to fill four different responsibilities totaling forty (40). What is…
A: System analysts: System analysts are responsible for maintaining and updating the computer systems…
Q: Iverilog: casez and casex Using 4-bits for both input and output. Convert even numbers as its half…
A: According to the question our input and output must be in 4 bit binary and if the passed input is…
Q: b. Z; bz a, Z; az b.b; A a a: A AZIZ a. Use instantaneous descriptions to trace the action of M2…
A:
Q: Draw the flowchart and write a C program that will input a 5 digit number (one time input only).…
A: Here we need to divide a number by 10 to gets its digits and then print the digits.
Q: Make UML Diagram and workflow architecture for integeration between two systems breast cancer clinic…
A: A UML diagram can be useful to corporations and other individuals who want to simplify the…
Q: We're not qualified to talk about how operating systems independently execute processes?
A: The software that connects a user's computer to its hardware is called an operating system (OS).A…
Q: 10. Suppose that the variable ALIVECNT initially contains the value 0x02. What will be the content…
A: Your answer is ready please check the step 2 for solution.
Q: Which of these statements is incorrect: 0 One key is used for encryption and another for decryption…
A: Introduction: key to the public In cryptography, one set of keys was used for encryption, while a…
Q: Describe two problems that current information systems are seeking to tackle
A: Information systems are systems that gather, store, and exchange data among different systems. An…
Q: Describe two issues that modern information systems are trying to address
A: Information systems: Information systems collect, store, and exchange data between various systems.…
Q: Write the unit tests class for the given Java program: public static void main(String[] args) {…
A: Answer:
Q: According to your description of a MANAGEMENT INFORMATION SYSTEM (MIS) that we have studied so far,…
A: A management Information system (MIS) is a computer-based system having software and hardware which…
Q: Examine the five moral aspects of IT systems.
A: Moral Dimensions Five Ethical Aspects of Information Systems The following moral dimensions are…
Q: What does this have to do with Agile versus Waterfall System Development?
A: Waterfall is a more traditional approach to project management, involving a linear flow. Agile, on…
Q: (b) Describe TWO (2) key differences between the activity bar chart and the staff allocation chart.
A:
Q: Explain each of the four levels that make up the TCP/IP abstraction stack.
A: The four abstraction layers consist of the connection layer (lowest layer), Internet layer,…
Q: Create a PowerShell script that generates a Fibonacci series (1,1,2,3,5,8,..) List out the first N…
A: Create a PowerShell script that generates a Fibonacci series (1,1,2,3,5,8,..) List out the first N…
Q: Defintion: What is the purpose of a database audit log? SQL Server uses Extended Events in a way…
A: Introduction: Defintion: What is the purpose of a database audit log? SQL Server uses Extended…
Q: For my C project: Bus ticket reservation. I want to create a function and one txt file for Passenger…
A:
Q: During a data security incident, what is the company's policy on disclosing information?
A: Data security : An outline is a thorough action plan or detailed organization of events. When…
Q: In a distributed database system, how many different kinds of data requests may there be?
A:
Q: What exactly is a spanning tree, and what is an MST? Prim's and Kruskal's algorithms are compared…
A: What is the difference between a spanning tree and MST? Perform an algorithmic comparison and study…
Q: Assign a name to the graphics processing unit.
A: Introduction: A graphics processing unit -GPU is a computer processor specifically designed to…
Q: Discuss how the use of interrupts might assist increase the machine's efficiency and decrease the…
A: The interrupt mechanism allows modules such as I/O or memory to interrupt the CPU's usual…
Q: h to satisfy y
A: In its simplest terms, the risk assessment asks the question: if we don't change our behavior, what…
Q: Is there a difference between a Unix Kernel and a shell in terms of what they do?
A: difference between a Unix Kernel and a shell in terms of what they do? Yes, Kernel it is the core…
Q: Describe the stages of the Waterfall Systems Development paradigm. How does this compare to Agile…
A: Provided: A concise explanation of the Waterfall Systems Development paradigm's steps.What are the…
Q: Why is there a layer for networks if they're already connected?
A: This layer's primary function is to deliver packets from the source to the source of most…
Q: Prove that 2" = o(22n). %3D
A:
Q: Make your own mental picture of how an automated teller machine (ATM) operates.
A: Create your own mental representation of an ATM. Answer: \s. Both credit and bank cards include…
Q: Explain why many IT professionals may disregard project expense management and how this may impact…
A: Define: Cost accounting is normally unbroken lower in IT project management. Most comes are oriented…
Q: symbolic form of the proposition
A: Given :- In the above question , the statements along with the proposition logic mention in the…
Q: Create a Supermarket Inventory System using C++ Include the following: supermarket inventory…
A: Answer:- store.cpp #include <iostream> #include <iostream> #include <fstream>…
Q: What is the difference between computer organization and computer architecture in broad terms?
A: Computer Architecture: It is worried about how equipment parts are associated together to shape a PC…
Q: Try to count the total number of words and characters of given input strings on the command line
A: Answer:
Q: 2.Write a Java program with screenshot output that uses switch statement to offer the user 3 choices…
A: As per the requirement program is developed. Algorithm: Step 1: Write the main() method Step 2:…
Q: What, precisely, sets the von Neumann and Harvard computer designs different from one another, if…
A: The von Neumann and Harvard computer designs primarily describe how the microcontroller is connected…
Q: Solve by using MS Excel find the density at 21.6 degrees
A: LINEAR INTERPOLATION IN EXCEL To perform linear interpolation in Excel, use the FORECAST function…
Q: sub : Computer Networks sub : Computer Networks How does ATM work? Explain through diagram
A: The automated teller machine (ATM) is a type of automatic banking machine (ABM) that enables…
Q: describe the three different types of identity verification. For each of these, provide a discussion…
A: Here, are some identity verification methods 1) Two-Factor Authentication - The two-factor…
Q: Could you describe the two different modes of IPSec?
A: Given: Internet Protocol Security, often known as IPsec, is a protected network protocol suite that…
Q: show how the busy beaver function can be used to create non-computable number
A: Solution: Busy Beaver Function Step 1: Explaining why this function is a non computable. About this…
Q: Discuss whether or not an operating system can survive without system calls. Why and how would you…
A: Operating system: The operating system is not responsible for making system calls. Examining the…
Q: Provide examples of how the following criteria may be rewritten quantitatively. To convey the needs,…
A: A Library system is an enterprise resource system used to track and catalogue the books, items,…
Q: n multimedia to: guide user in navigatir ll of the above menti leliver information fo
A: Text is used in multimedia to: A guide user in navigating through application C. deliver…
Q: Discuss Unit, Integration, and System testing in a brief manner. Where do they diverge?
A: Unit Evaluation Unit Testing is the process of isolating a software module for testing and comparing…
Q: Provide a rundown of the seven most often used topologies.
A: Network Structure: The manner in which computer systems or network devices are linked is referred to…
Q: At the conclusion of the systems analysis phase, you investigated the economic feasibility of the…
A: Solution: When creating a system, there are many phases that must be completed. Each of these…
Q: Why not have a look at the five moral aspects of information systems
A: Answer: The following are the five moral aspects of information systems: 1. Information rights and…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Consider the following C fragment. The program is stopped immediately after the assignment to point.y and we know that &point is 0x0804A010. What would gdb print in response to x/8bx 0x0804A010? (Note: The /8bx means print eight bytes and I did this linux.cs.wwu.edu.) re struct point_st { int x; int y; }; void function() { struct point_st point; point.x = 0x01234567; point.y = 0x89ABCDEF; ... } a. 08040A010: 01 23 45 67 89 AB CD EF b. 08040A010: 67 45 23 01 EF CD AB 89 c. 08040A010: 89 AB CD EF 01 23 45 67 d. 08040A010: EF CD AB 89 67 45 23 01Consider the following code: import pandas as pd df = pd.DataFrame({'state': ['Ohio', 'Ohio', 'Ohio', 'Nevada'], 'year': [2000, 2001, 2002, 2001], 'pop': [1.5, 1.7, 3.6, 2.4]}) Which is one of the following is error? Select one: a. df[1] b. df["state"] c. df.state d. df.loc[1]You are writing code that is equivalent to: X = A / (5 + B) Assume signed bytes and the following first 3 lines of code: mov al,A mov bl,B add bl,5 What is the last one line of code?
- please help me this simpe operation of paython 1. stu = [1, 2, 3, [‘Bob’, 22], [‘Peter’, 21],’Hello world’]stu[1]: stu[3][0]: len(stu):A. The original Caesar cypher shifts each character by one: a becomes b, z becomes a, and so on. Let's make it a bit harder, and allow the shifted value to come from the range 1..25 inclusive. Moreover, let the code preserve the letters' case (lower-case letters will remain lower-case) and all non-alphabetical characters should remain untouched. Your task is to write a program which: asks the user for one line of text to encrypt; asks the user for a shift value (an integer number from the range 1..25 - note: you should force the user to enter a valid shift value (don't give up and don't let bad data fool you!) Test your code using the data we've provided. Test data Sample input: abcxyzABCxyz 123 2 Sample output: cdezabCDEzab 123 Sample input: The die is cast 25 Sample output: Sgd chd hr bzrsYou are writing code that is equivalent to: X = A / (5 + B) Assume signed bytes and the following first 3 lines of code: mov al,A mov bl,B add bl,5 What is the one line of code that will perform the division correctly?
- In <sys/param.h>, MAXPATHLEN is defined to be 1024 bytes.The for()loop here correctly bounds variable i to < 1023, such that when the loop hasended, no byte past npath[1023] may be written with \0. However, since i is alsoincremented in the nested statements here as ++i, it can become equal to 1024,and npath[1024] is past the end of the allocated buffer space.Then a null byte iswritten into npath[1024], overwriting the least significant byte of EBP.This canbe exploited as a off-by-one overflow.The bug was fixed by Which changing the logic?Given an arbitrary cipher text file, please help me write a small C++ program that outputs: 1) the value of the shift, and 2) decrypts the cipher text to plaintext so that only alphabetic letters are changed. Thank you.What does the following program do, assuming a set of integers are stored starting at location x4000 and MASK is used to force the program to branch somewhere?.ORIG x3000LD R0, NUMSLD R2, MASKLOOP LDR R1, R0, #0BRz DONEAND R5, R1, R2BRz LP1BRnzp NEXTLP1 ADD R1, R1, R1STR R1, R0, #0NEXT ADD R0, R0, #1BRnzp LOOPDONE HALTNUMS .FILL x4000MASK .FILL x8000.ENDa. add only positive integers.b. add only negative integers.c. doubles only the positive integers.d. doubles only the negative integers.e. None of the above.
- Suppose we number the bytes in a w-bit word from 0 (least significant) to w/8 – 1 (most significant). Write code for the following C function, which will return an unsigned value in which byte i of argument x has been replaced by byte b: unsigned replace_byte (unsigned x, int i, unsigned char b); Here are some examples showing how the function should work: replace_byte(0x12345678, 2, 0xAB) --> 0x12AB5678 replace_byte(0x12345678, 0, 0xAB) --> 0x123456AB Bit-Level Integer Coding Rules In several of the following problems, we will artificially restrict what programming constructs you can use to help you gain a better understanding of the bit-level, logic, and arithmetic operations of C. In answering these problems, your code must follow these rules: Allowed operations All bit-level and logic operations. Left and right shifts, but only with shift amounts between 0 and w – 1. Addition and subtraction. Equality (==) and inequality (!=) tests. (Some of the problems do not allow…Please write in C program to print out a list of bit strings that can be created by using combination How many bit strings of length 12 containa) exactly three 1s?b) at most three 1s?c) at least three 1s?d) an equal number of 0s and 1s?Early Unix implementations used filenames which were up to 14 characters long. Normally, storing a 14 character string in C would require 15 bytes but to save storage only 14 bytes were used with the terminating NUL character not being stored for filenames which were exactly 14 characters long. Discuss how you would convert this possibly unterminated string into a proper NUL-terminated C string in a char buf[15]. You may use functions from the C standard library

